H3C IPV6之ipsec(ike预共享)典型组网配置案例

组网说明:
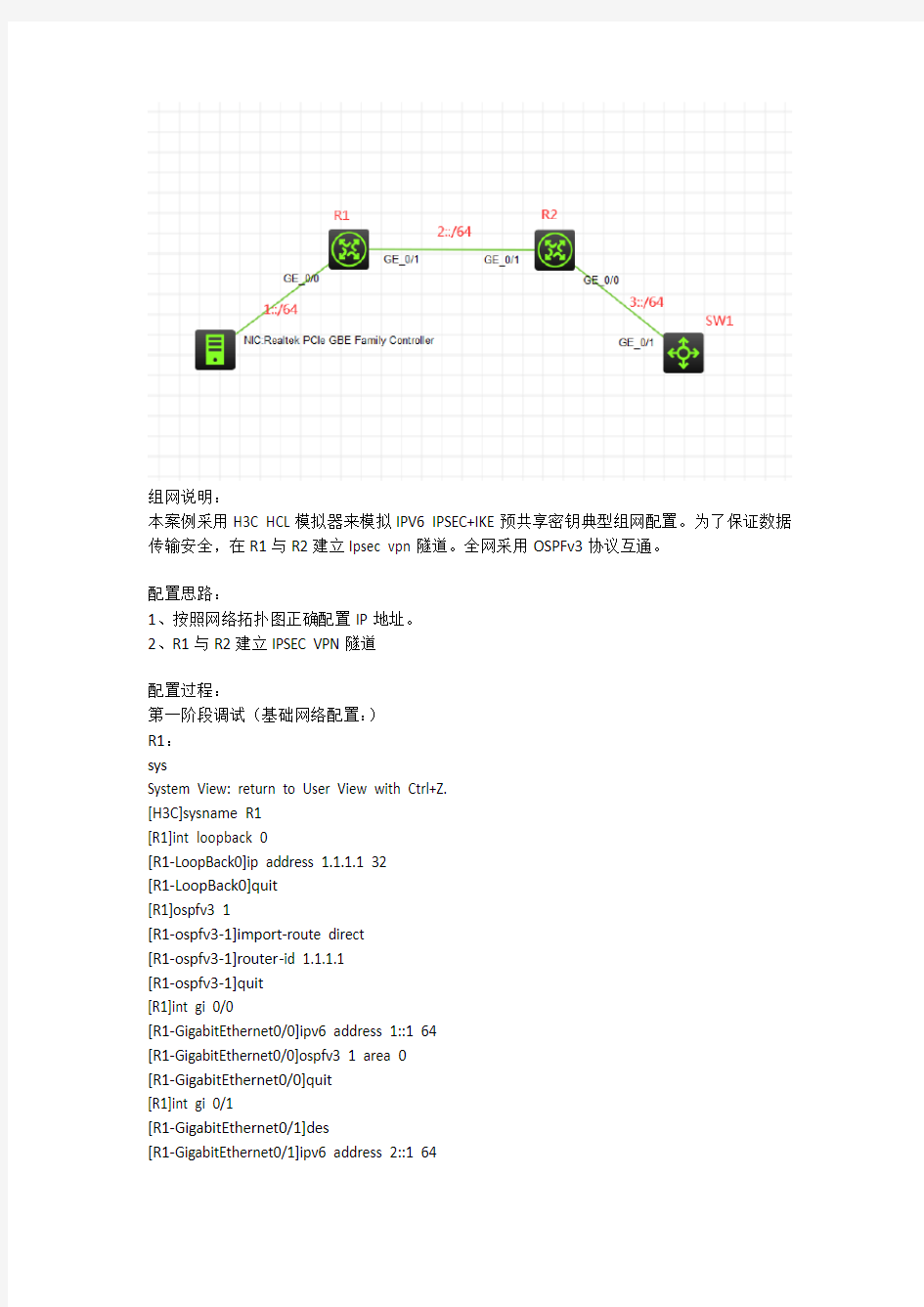
本案例采用H3C HCL模拟器来模拟IPV6 IPSEC+IKE预共享密钥典型组网配置。为了保证数据传输安全,在R1与R2建立Ipsec vpn隧道。全网采用OSPFv3协议互通。
配置思路:
1、按照网络拓扑图正确配置IP地址。
2、R1与R2建立IPSEC VPN隧道
配置过程:
第一阶段调试(基础网络配置:)
R1:
System View: return to User View with Ctrl+Z.
[H3C]sysname R1
[R1]int loopback 0
[R1-LoopBack0]ip address 1.1.1.1 32
[R1-LoopBack0]quit
[R1]ospfv3 1
[R1-ospfv3-1]import-route direct
[R1-ospfv3-1]router-id 1.1.1.1
[R1-ospfv3-1]quit
[R1]int gi 0/0
[R1-GigabitEthernet0/0]ipv6 address 1::1 64
[R1-GigabitEthernet0/0]ospfv3 1 area 0
[R1-GigabitEthernet0/0]quit
[R1]int gi 0/1
[R1-GigabitEthernet0/1]des
[R1-GigabitEthernet0/1]ipv6 address 2::1 64
[R1-GigabitEthernet0/1]ospfv3 1 area 0
[R1-GigabitEthernet0/1]quit
R2:
System View: return to User View with Ctrl+Z. [H3C]sysname R2
[R2]int loopback 0
[R2-LoopBack0]ip address 2.2.2.2 32
[R2-LoopBack0]quit
[R2]ospfv3 1
[R2-ospfv3-1]router-id 2.2.2.2
[R2-ospfv3-1]import-route direct
[R2-ospfv3-1]quit
[R2]int gi 0/1
[R2-GigabitEthernet0/1]des
[R2-GigabitEthernet0/1]quit
[R2]int gi 0/0
[R2-GigabitEthernet0/0]des
[R2-GigabitEthernet0/0]quit
SW1:
System View: return to User View with Ctrl+Z. [H3C]sysname SW1
[SW1]int loopback 0
[SW1-LoopBack0]ip address 3.3.3.3 32
[SW1-LoopBack0]quit
[SW1]ospfv3 1
[SW1-ospfv3-1]import-route direct
[SW1-ospfv3-1]router-id 3.3.3.3
[SW1-ospfv3-1]quit
[SW1]int gi 1/0/1
[SW1-GigabitEthernet1/0/1]port link-mode route [SW1-GigabitEthernet1/0/1]des
第一阶段测试:
物理机填写IP地址:
物理机能PING通SW1:
第二阶段调试(IPSEC预共享密钥关键配置点):
R1:
[R1]acl ipv6 advanced 3000
[R1-acl-ipv6-adv-3000]rule 0 permit ipv6 source 1::/64 destination 3::/64 [R1-acl-ipv6-adv-3000]quit
[R1]ike keychain james
[R1-ike-keychain-james]pre-shared-key address ipv6 2::2 64 key simple james [R1-ike-keychain-james]quit
[R1]ike proposal 1
[R1-ike-proposal-1]quit
[R1]ike profile james
[R1-ike-profile-james]keychain james
[R1-ike-profile-james]proposal 1
[R1-ike-profile-james]match remote identity address ipv6 2::2 64
[R1-ike-profile-james]local-identity address ipv6 2::1
[R1-ike-profile-james]quit
[R1]ipsec transform-set james
[R1-ipsec-transform-set-james]protocol esp
[R1-ipsec-transform-set-james]encapsulation-mode tunnel
[R1-ipsec-transform-set-james]esp authentication-algorithm md5
[R1-ipsec-transform-set-james]esp encryption-algorithm des-cbc
[R1-ipsec-transform-set-james]quit
[R1]ipsec ipv6-policy james 1 isakmp
[R1-ipsec-ipv6-policy-isakmp-james-1]security acl ipv6 3000
[R1-ipsec-ipv6-policy-isakmp-james-1]ike-profile james
[R1-ipsec-ipv6-policy-isakmp-james-1]transform-set james
[R1-ipsec-ipv6-policy-isakmp-james-1]remote-address ipv6 2::2
[R1-ipsec-ipv6-policy-isakmp-james-1]quit
[R1]int gi 0/1
[R1-GigabitEthernet0/1]ipsec apply ipv6-policy james
[R1-GigabitEthernet0/1]quit
R2:
[R2]acl ipv6 advanced 3000
[R2-acl-ipv6-adv-3000]rule 0 permit ipv6 source 3::/64 destination 1::/64 [R2-acl-ipv6-adv-3000]quit
[R2]ike keychain james
[R2-ike-keychain-james]pre-shared-key address ipv6 2::1 key simple james [R2-ike-keychain-james]quit
[R2]ike proposal 1
[R2-ike-proposal-1]quit
[R2]ike profile james
[R2-ike-profile-james]keychain james
[R2-ike-profile-james]proposal 1
[R2-ike-profile-james]local-identity address ipv6 2::1
[R2-ike-profile-james]match remote identity address ipv6 2::1 64
[R2-ike-profile-james]quit
[R2]ipsec transform-set james
[R2-ipsec-transform-set-james]protocol esp
[R2-ipsec-transform-set-james]encapsulation-mode tunnel
[R2-ipsec-transform-set-james]esp authentication-algorithm md5 [R2-ipsec-transform-set-james]esp encryption-algorithm des-cbc [R2-ipsec-transform-set-james]quit
[R2]ipsec ipv6-policy james 1 isakmp
[R2-ipsec-ipv6-policy-isakmp-james-1]security acl ipv6 3000
[R2-ipsec-ipv6-policy-isakmp-james-1]transform-set james
[R2-ipsec-ipv6-policy-isakmp-james-1]ike-profile james
[R2-ipsec-ipv6-policy-isakmp-james-1]remote-address ipv6 2::1 [R2-ipsec-ipv6-policy-isakmp-james-1]quit
[R2]int gi 0/1
[R2-GigabitEthernet0/1]ipsec apply ipv6-policy james
[R2-GigabitEthernet0/1]quit
第二阶段测试:
查看R1的IPSEC显示信息:
