【期末考试复习】计算机网络英文版
【期末考试复习】计算机网络英文版

【期末考试复习】计算机网络英文版第一章计算机网络概述●Identify the five components of a data communications system.(数据通信系统5个组成部分:报文发送方接受方传输介质协议) message,sender,receiver,transmission medium and protocol.●What are the three criteria necessary for an effective and efficient network?performance, reliability,and security.●What is an internet(互联网)? What is the Internet(因特网)?★ An internet is an interconnection of networks which is a collection of networks connected by internetworking devices such as routers.★The Internet is the name of a specific worldwide network that uses the TCP/IP protocol suite and is the largest internet in the world.第二章数据和信号●Which practical methods are used for analysis of a signal? And which is suitablefor network techniques? 研究电磁信号的方法是哪两种?适用于网络技术的?①Time domain and frequency domain②frequency domain●Why can't any digital signal be transferred with no distortion in communicationtransmission?(数字信号为什么不能无失真传输?)1.Because to receive an exact replica of the digital signal, all of the frequency components must be faithfully through the transmission medium, if certain harmonic cannot transfer successful, the signal we receive will be distorted. However, anymedium transfers signals only within certain frequency ranges, that is, has a limited bandwidth.2.Transmission impairments of signals (attenuation, distortion and noise) always exist, so signal errors unavoidable.●What's the bandwidth(带宽)? Explain briefly what correlation do bandwidth,data rate and cost have in communication process?带宽、数据率、成本之间的关系?The range of frequencies contained in a composite signal is its bandwidth.In networking, we use the term bandwidth in two contexts with two different measuring values: Bandwidth in Hertz is the range of frequencies in a composite signal or the range of frequencies that a channel can pass, usually used to present the performance of analog channels and transmission media. (Another is) Bandwidth in bits per second is the speed of bit transmission in a channel,a link,or even a network, usually used to present the performance of links and communication devices of a network.(课本P84)The greater the transmission bandwidth,the greater the data rate, and the higher the cost.●Q3-3: How can a composite signal be decomposed into its individual frequencies?复位信号如何分解成单独的频率成分?If the composite signal is periodic, we can ues Fourier Series decompose it into a series of signals with discrete frequencies;if the composite signal is nonperiodic, we can ues Fourier Transform decompose it into a combination of sine waves with continuous frequencies.●Q3-4: Name three types of transmission impairment. 三种传输减损?Attenuation, distortion,and noise. 衰减、失真和噪声●Q3-7: What does the Nyquist theorem have to do with communications?奈奎斯特公式在通信中的作用?Estimate the channel capacity of noise-free digital channels, , when the channel is greater than the data rate transmitted on channel capacity, it will be failure due to severe distortion.☆The Nyquist theorem defines the theoretical maximum bit rate of a noiseless channel.●Q3-8: What does the Shannon capacityhave to do with communications?香农容量原理在通信中的作用?Estimate the thermal noise interference channel capacity (theoretical upper limit), the data rate is higher, damage caused by noise will be more serious.☆ The Shannon capacity defines the theoretical highest data rate for noisy channel. 第三章传输介质●Briefly describe the main applications of three types of guided transmissionmedia. 三种重要的有向传输介质的应用总的说:Twisted-pair cable is used for voice and data communications. Coaxial cable is used in cable TV networks and traditional Ethernet LANs. Fiber-optic cable is used in backbone networks, cable TV networks, and Fast Ethernet networks.分别说:twisted-pair cable: 双绞线(广泛用于楼内布线)/doc/5611869427.html,ed as telephone lines to provide voice and data channels –connectingsubscribers to the central telephone office./doc/5611869427.html,ed as DSL (digital subscriber line) loop to provide high-data-rate Internet connection – the so called Family Broad Band./doc/5611869427.html,ed in LANs to provide high-data-rate baseband transmission (10 and 100 Mbps).coaxial cable: 同轴电缆(不用了,目前主要用于有线电视)1.Was widely used in analog telephone networks (10000 voice signals) and in digital telephone networks (data rate up to 600 Mbps).However, it has largely been replaced with fiber-optic cable.2.Was widely used in cable TV networksHowever, cable TV providers replaced most of coax with fiber-optic cable.3.Was widely used in early traditional Ethernet LANs.However, it has been replaced with UTP which has data rate up to 100 Mbps.☆ Now, mainly used for CATVfiber-optic cable: 光纤(广泛用于楼间布线和长途传输)widely used for wirings between buildings or long-distance transmission.such as:1.High-speed backbone networks because its wide bandwidth is cost-effective.2.Cable TV networks use usually a combination of optical fiber and coaxial cable.3.Backbone channels in LANs, CANs and W ANs4.Lightning-proof networks5.Secrecy networks against wiretapping●What types of optical fiber transmission modes are there?Which of them issuitable for long distance transmission?Types:sigal mode and multimode, and the multimode include two types:Step-index and Graded-index.The sigal mode is suitable for long distance transmission.第四章●What is Encoding? Why must encoding be used for data transmission?(1)【什么是编码?】Convert internal data of a sender into line signals suitable for transmission is called encoding.(2)【数据发送时为什么要编码?】1) Electromagnetic signals in information process devices are not allowed transmitting directly over communication lines.2) The signal type of a device differs from the signal type ofa communication line.3) The parameter requirements of device signals differs from the one of line signals.4) Specific requirements in synchronization, efficiency , error control, etc..★Because electromagnetic signals in information process devices are not allowed transmitting directly over communication lines, so encoding must be used for data transmission to converts internal data of a sender into line signals suitable for transmission.2.3.4.机内信号与线路类型不一样;机内信号参数与线路传输的要求不一样;同步、效率、纠错等方面的特殊要求●Which two techniques are used when analog data transmitted by digital signals?Which of them is the most important? Why?用数字信号传输模拟数据常用技术有哪两种?最常用的是?为什么?(1) Pulse Code Modulation(PCM) and Delta Modulation(DM).(2) Pulse Code Modulation(PCM) is the most important.(3) The principal advantage of DM over PCM is the simplicity of its implementation. In general, PCM exhibits better SNR characteristics at the same data rate.●What processes will be involved when analog data are digitized by PCMtechnique?用PCM技术将模拟数据数字化时,要经过哪些处理步骤?Sampling (PAM)---->quantization---->binary encoding---->digital to digital coding●Q4-1 List three techniques of digital-to-digital conversion.They are line coding,block coding and scrambling coding.●Q4-4 Define baseline wandering and its effect on digital transmission.(1)In decoding a digital signal, the receiver calculates a running average of the received signal power. This average is called the baseline.(2)The incoming signal power is evaluated against this baseline to determine the value of the data element.(3)A long string of 0s or 1s can cause a drift in the baseline (baseline wandering) and make it difficult for the receiver to decode correctly.●Q4-5 Define a DC component and its effect on digital transmission.(Define) When the voltage level in a digital signal is constant for a while, the specturm creates very low frequencies(results of Fourier analysis). These frequences around zero,called DC(derect-current) components, that present problems for a system that can not pass low frequencies or a system that uses electricalcoupling.(Effect) DC component means 0/1 parity that can cause base-line wondering. 直流分量的影响不仅仅是基线偏移,还有更重要的原因。
计算机网络英文版习题答案

P63 #5 Consider sending a packet of F bits over a path of Q links. Each link transmits at R bps. The network is lightly loaded so that there are no queuing delays. Propagation delay is negligible.a.Suppose the network is a packet-switched virtual-circuit network. Denote the VC setup time by t s seconds. Suppose the sending layers add a total of h bits of header to the packet. How long does it take to send the file from source to destination?t s+[(F+h)/R]Qb.Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 2h bits of header. How long does it take to send the packet?[(F+2h)/R]Qc.Finally, suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is R bps. Assuming ts setup time and h bits of header appended to the packet, how long does it take to send the packet?t s+(F+h)/RP64 #6 This elementary problem begins to explore propagation delay and transmission delay, two central concepts in data networking. Consider two hosts, A and B, connected by a single link of rate R bps. Suppose that the two hosts are separated by m meters and suppose that the propagation speed along the link is s meters/sec. Host A sends a packet of size L bits to host B.[a] Express the propagation delay, d prop, in terms of m and s.[b] Determine the transmission time of the packet, d trans, in terms of L and R.[c] Ignoring processing and queueing delays, obtain an expression for the end-to-end delay.[d] Suppose Host A begins to transmit the packets at time t=0. At time t=d trans, where is the last bit of the packet?[e] Suppose d prop is greater than d trans. At time t=d trans, where is the first bit of the packet?[f] Suppose d prop is less than d trans. At time t=d trans, where is the first bit of the packet?[g] Suppose s=2.5 x 108, L=100 bits and R=28kbps. Find the distance m so that d prop = d trans.[a] d prop = m/s[b] d trans = L/R[c] end-to-end delay = d prop + d trans=m/s+L/R[d] The beginning position of the link.[e] On the channel between A and B.[f] On the host B.[g] m/s = L/R = > m = sL/R = > m = 892.86 kmP65 #10 Consider the queueing delay in a router buffer. Suppose that all packets are L bits, the transmission rate is R bps, and that N packets simultaneously arrive at the buffer every LN/R seconds. Find the average queueing delay of a packet (in terms of L, R and N). (Hint: The queueing delay for the first packet is zero; for the second packet L/R; for the third packet 2L/R. The Nth packet has already been transmitted when the second batch of packets arrives.)As the Nth packet has already been transmitted when the next batch of packets arrive, we only need to consider the delay for a single batch of packets.Average delay = Total delay / Number of packetsDelay for 1st packet = 0Delay for 2nd packet = L/RDelay for 3rd packet = 2L/R......Delay for Nth packet = (N-1)L/RTotal delay for N packets = (0 + 1 + 2 ... +(N-1) ) * (L/R)Using the formulas for sum of integer series, this can be written as: Total delay for N packets = (N-1) * (N/2) * (L/R)Therefore, average delay for N packets = ((N-1) * L) / 2RP170 #12 What is the difference between persistent HTTP with pipelining and persistent HTTP without pipelinning? Which of the two is used by HTTP/1.1?For the persistent connection without pipelining, the client issues a new request only when the previous has been received. In this case, the client experiences one RTT in order to request and receive each of the referenced objects.For the persistent connection with pipelining, the client issues a request as soon as it encounters a reference. It is possible for only RTT to be expended for all the referenced objects.P170 #14 Telnet into a Web server and send a multiline request message. Include in the request message theIf-modified-since: header line to force a response message with the 304 Not Modified status code.GET/somedir/exp.html HTTP/1.1Host: Connection: closeUser-agent: Mozilla/4.0If-Modified-Since: Thu, 30 May 2007 12:00:00 GMTAccept-language: frP172 #6 Suppose within your web browser you click on a link to obtain a web page. The IP address for the associated URL is not cached in your local host, so a DNS look-up is necessary to obtain the IP address. Suppose that n DNS servers are visited before your host receives the IP address from DNS; the successive visits incur an RTT (Round Trip Time) of RTT1, ... RTTn. Further suppose that the web page associated with the link contains exactly one object, consisting of a small amount of HTTP text. Let RTT0 denote the RTT between the local host and the remote server containing the object. Assuming zero transmission time of the object, how much time elapses from when the client clicks on the link until the client receives the object? (Hint: read pages 90 .. 93)Time to visit DNS servers and get IP address = RTT1 + RTT2 + ... + RTTnTime to establish TCP connection (SYN and SYNACK) = RTT0Time to send HTTP request and receive reply = RTT0Total time = 2 * RTT0 + (RTT1 + RTT2 + ... + RTTn)P171 #16 Suppose Alice with a Web-based e-mail account (such as Yahoo! Mail or Hotmail) sends a message to Bob, who accesses his mail from his mail server using POP3. Discuss how the message gets from Alice’s host to Bob’s host. Be sure to list the series of application-layer protocols that are used to move the message between the two hosts.The series of application-layer protocols: HTTP、SMTP、POP3Suppose that you send an e-mail message whose only data is a Microsoft Excel attachment. What might the header lines (including MIME lines) look like?From:***********To:***********Subject: helloMIME-Version: 1.0Content-Transfer-Encoding: base64Content-Type: Application/MS-ExcelP286 #5 Suppose host A sends two TCP segments back to back to host B over a TCP connection. The first segment has sequence number 90: the second has sequence number 110.a.How much data is in the first segment?a.20 bytesb.Suppose that the first segment is lost but the second segment arrives at B. In the acknowledgement that host B sends to host A, what will be the acknowledgement number?b.ACK90P291 #27 Consider the following plot of TCP window size as a function of time. (reproduced below for you) Assuming TCP Reno is the protocol experiencing the behavior shown above, answer the following questions. In all cases, you should provide a short discussion justifying your answer.a. Identify the intervals of time when TCP slow start is operating.b. Identify the intervals of time when TCP congestion avoidance is operating.c. After the 16th transmission round, is segment loss detected by a tripleduplicate ACK or by a timeout?d. After the 22nd transmission round, is segment loss detected by a triple duplicate ACK or by a timeout?e. What is the initial value of Threshold at the first transmission round?f. What is the value of Threshold at the 18th transmission round?g. What is the value of Threshold at the 24th transmission round?h. During what transmission round is the 70th segment sent?i. Assuming a packet loss is detected after the 26th round by the receipt of a triple duplicate ACK, what will be the values of the congestion-window size and of Threshold?Solution:a.1-6, 23-26b.6-16, 17-22c.a triple duplicate ACKd.timeoute.32f.21g.13h.7i.4, 4P293 #34 Consider sending an object of size O = 100 Kbytes from server to client. Let S = 536 bytes and RTT = 100 msec. suppose the transport protocol uses static windows with window size W. (See Section 3.7.2)a.For a transmission rate of 28 kbps, determine the minimum possible latency. Determine the minimum window size that achieves this latency.b.Repeat (a) for 100 kbps.tency=28.8s W=2tency=8.2s W=4P405 #8 Consider a datagram network using 8-bit host addresses. Suppose a router uses longest prefix matching and has t he following forwarding table:-----------------------------------------------------Prefix Match Interface-----------------------------------------------------00 001 110 211 3-----------------------------------------------------For each of the four interfaces, give the associated range of destination host addresses and the number of addresses in the range.6P407 #15 Consider sending a 3000-byte datagram into a link that has a MTU of 500 bytes. Suppose the original datagram is stamped with the identification number 422. How many fragments are generated? What are their characteristics?there are「2980/480」=7 fragments be generatedP408 #22 Consider the network shown in Problem 21 (reproduced below). Using Dijkstra’s algorithm, and showing your work using a table similar to Table 4.3, do the following:a. Compute the shortest path from s to all network nodesSteps D(t),P(t) D(u),P(u)D(v),P(v)D(w),P(w)D(x),P(x)D(y),P(y)D(z),P(z)0 1,s 4,s ∞∞∞∞∞1 3.t 10,t ∞∞5,t 3,t2 4,u 6,u ∞5,t 3,t3 4,u 6,u ∞5,t4 5,v 7,v 5,v5 6,w 5,v6 6,wPlease fill in the following tables using DV algorithm:For the node Z in the graph shown in the 22nd topic (P408), please fill in the following routing table in the router z about the initial distance-vector Destination node Next hop Current shortest distancevalue-DzS —∞T T 2U —∞V —∞W —∞X —∞Y Y 14Z Z 0following rout-ing table in the node z to update this routing tableDestination node Currentdistance-DyDestination node Current distance-DtS 5 S 1 T 4 T 0 U 2 U 2P493 #7 How big is the MAC address space?The IPv4 address space?The IPv6 address space?MAC address: 6 bytes, MAC address space 2^48IPV4 address: 4 bytes, IPV4 address space 2^32IPV6 address: 16 bytes, IPV6 address space 2^128P494 #4 Consider the 4-bit generator, G, shown in Figure 5.8, and suppose the D has the value 10101010. What is the value of R?G=1001, D=10101010, R=101。
计算机网络英文版——提供给学生部分习题答案

计算机⽹络英⽂版——提供给学⽣部分习题答案Solution of Selected Exercises from the End of Chapter ExercisesChapter 1 - Introduction And Overview1.4 To what aspects of networking does data communications refer?Answer:Data communications refers to the study of low-level mechanisms and technologies used to send information acrossa physical communication medium, such as a wire, radio wave, or light beam.1.5 What is packet-switching, and why is packet switching relevant to the Internet?Answer: Packet switching divides data into small blocks, called packets, and includes an identification of the intended recipient in each packet. Packet switching changed networking in a fundamental way, and provided the basis for the modern Internet. Packet switching allows multiple senders to transmit data over a shared network.1.8 What is a communication protocol? Conceptually, what two aspects of communication does a protocol specify? Answer: A communication protocol refer to a specification for network communication.Major aspects of a protocol are syntax (format) and semantics (meaning) of the protocol.1.9 What is a protocol suite, and what is the advantage of a suite?Answer:protocols are designed in complete, cooperative sets called suites or families, instead of creating each protocol in isolation. Each protocol in a suite handles one aspect of communication; together, the protocols in a suite cover all aspects of communication. The entire suite is designed to allow the protocols to work together efficiently. 1.11 List the layers in the TCP/IP model, and give a brief explanation of each.(See Textbook)1.14 Give a brief explain of the layers in the ISO Open System Interconnection model.(See Textbook)Chapter 3 - Internet Applications And Network Programming3.1 What are the two basic communication paradigms used in the Internet?Answer: There are various approaches, but according to textbook, we can specify them as Stream Paradigm and Message Paradigm.3.2 Give six characteristics of Internet stream communication.(See Textbook)3.3 Give six characteristics of Internet message communication.(See Textbook)3.4 If a sender uses the stream paradigm and always sends 1024 bytes at a time, what size blocks can the Internet deliverto a receiver?Answer: stream paradigm does not provide any guarantees for block sizes, so all depends on individual transfer.3.6 What are the three surprising aspects of the Internet’s message delivery semantics?Answer:The Internet’s message delivery has the followi ng undesirable characteristics:* Messages can be lost* Messages can be duplicated* Messages can be delivered out-of-order3.8 When two applications communicate over the Internet, which one is the server?Answer: T he application that waits for some other applications to contact is called server, and the application that contact other one is called client.3.14 What two identifiers are used to specify a particular server?Answer: A particular server is identified by the following identifiers:* An identifier for the computer on which a server runs (IP Address)* An identifier for a particular service on the computer (Port Number)Chapter 4 - Traditional Internet Applications4.1 What details does an application protocol specify?(See Textbook)4.3 What are the two key aspects of application protocols, and what does each include?(See Textbook)4.6 What are the four parts of a URL, and what punctuation is used to separate the parts?Answer: The URL into four components: a protocol, a computer name, a document name, and parameters. The computer name and protocol port are used to form a connection to the server on which the page resides. And the document name and parameters are used to request a specific page.4.7 What are the four HTTP request types, and when is each used?(See Textbook)4.12 When a user requests an FTP directory listing, how many TCP connections are formed? Explain.Answer: FTP uses two types of connections to perform its functionality, namely* A control connection is reserved for commands. Each time the server needs to download or upload a file, the server opens a new connection.* A data connection is used to transfer files.4.16 List the three types of protocols used with email, and describe each.(See Textbook)4.17 What are the characteristics of SMTP?(See Textbook)4.20 What are the two main email access protocols?Answer: Two major email access protocols are:* Post Office Protocol (POP)* Internet Mail Access Protocol (IMAP)Chapter 6- Information Sources and Signals6.4 State and describe the four fundamental characteristics of a sine wave.(See Textbook)6.9 What is the analog bandwidth of a signal?Answer: Analog bandwidth of signal can be defined as to be the difference between the highest and lowest frequencies of the constituent parts (i.e., the highest and lowest frequencies obtained by Fourier analysis)6.11 Suppose an engineer increases the number of possible signal levels from two to four. How many more bits can be sent in the same amount of time? Explain.Answer: The number of levels that can be represented by n bits is given by 2n . So if number of levels changes from 2→4, it means number of bits goes from 1→2612. What is the definition of baud?Answer: Baud is defined as the number of times that a signal can change per second.6.14 What is the bandwidth of a digital signal? Explain.Answer: According to the definition of analog bandwidth, a digital signal has infinite bandwidth because Fourier analysis of a digital signal produces an infinite set of sine waves with frequencies that grow to infinity.6.18 What is the chief advantage of a Differential Manchester Encoding?Answer: The most important property of differential encoding is that the encoding works correctly even if the two wires carrying the signal are accidentally reversed.6.20 If the maximum frequency audible to a human ear is 20,000 Hz, at what rate must the analog signal from a microphone be sampled when converting it to digital?Answer: The sampling rate = 2 × f max, so the signal should be sampled at 2x20,000 = 40,000 HzChapter 7 - Transmission Media7.2 What are the three energy types used when classifying physical media according to energy used?Answer: Three types of energy used when classifying physical media are electrical, electromechanical (radio), and light7.4 What three types of wiring are used to reduce interference form noise?(See Textbook)7.10 List the three forms of optical fiber, and give the general properties of each.(See Textbook)7.21 What is the relationship between bandwidth, signal levels, and data rate?Answer: If a transmission system uses K possible signal levels and has an anal og bandwidth B, Nyquist’s Theorem states that the maximum data rate in bits per second, D, is: D = 2 B log2K7.22 If two signal levels are used, what is the data rate that can be sent over a coaxial cable that has an analog bandwidthof 6.2 MHz?Answer: Using the D= 2 B log2 K relationship, D = 2*6.2*log22 = 2*6.2*1 = 12.4 Mbps7.24 If a system has an input power level of 9000, and an output power level of 3000, what is the difference when expressed in dB?Answer: Decibel is expressed as 10log10(P out/P in) → 10log10(3,000/9,000) = to be determined by reader7.23 If a system has an average power level of 100, an average noise level of 33.33, and a bandwidth of 100 MHz, whatis the effective limit on channel capacity?Answer: Shannon theorem specify the maximum data rate that could be achieved over a transmission system that experiences noise: C = Blog2 (1 + S/N) = 100,000,000 * log2 (1 + 100/33.33) = 100,000,000 * log24 = 200,000,000 = 200 Mbps7.25 If a telephone system can be created with a signal-to-noise ratio of 40 dB and an analog bandwidth of 3000 Hz, how many bits per second could be transmitted?Answer: First we should convert 40 dB to a real number, namely if 40 = 10 log10S/N→S/N = 10,000 , Using the Shannon’s capacity expression C = B log2(1 + S/N) → C = 3,000 log2 (1+ 10,000) = to be determined by readerCh 8 - Reliability And Channel Coding8.1 List and explain the three main sources of transmission errors.(See Textbook)8.3 In a burst error, how is burst length measured?Answer: For a burst error, the burst size, or length, is defined as the number of bits from the start of the corruption to the end of the corruption.8.4 What is a codeword?Answer: We can define the set of all possible messages to be a set of datawords, and define the set of all possible encoded versions to be a set of codewords. So each possible code sequence is considered to be a codeword.8.8 Compute the Hamming distance for the following pairs: (0000, 0001), (0101, 0001), (1111, 1001), and ( 0001, 1110). (See Textbook)8.11 Generate a RAC parity matrix for a (20, 12) coding of the dataword 100011011111.(See Textbook)8.15 Express the two values in the previous exercise as polynomials.Answer:X10+ X7 + X5 + X3 + XX4+ X2+ 1Ch 9 - Transmission Modes9.1 Describe the difference between serial and parallel transmission.Answer: Transmission modes can be divided into two fundamental categories:* Serial: one bit is sent at a time* Parallel: multiple bits are sent at the same time9.2 What are the advantages of parallel transmission? What is the chief disadvantage?Answer: A parallel mode of transmission has two chief advantages:* High speed: Because it can send N bits at the same time, a parallel interface can operate N times faster than an equivalent serial interface.* Match to underlying hardware: Internally, computer and communication hardware uses parallel circuitry.Thus, a parallel interface matches the internal hardware well.The main disadvantage of parallel transmission is number of cables required, for long distance communication, this is an important consideration.9.4 What is the chief characteristic of asynchronous transmission?Answer:Asynchronous transmission can occur at any time, with an arbitrary delay between the transmission of two data items, it allows the physical medium to be idle for an arbitrary time between two transmissions.Chapter 11 - Multiplexing And Demultiplexing11.2 What are the four basic types of multiplexing?(See Textbook)11.4 What is a guard band?Answer: For proper communication without interference, we should choose a set of carrier frequencies with a gap between them known as a guard band. The guard band reduces or eliminates the possible interference between neighboring carrier signals.11.8 Explain how a range of frequencies can be used to increase data rate.Answer:To increase the overall data rate, a sender divides the frequency range of the channel into K carriers, and sends 1 /K of the data over each carrier.11.12 Suppose N users compete using a statistical TDM system, and suppose the underlying physical transport can sendK bits per second. What is the minimum and maximum data rate that an individual user can experience?Answer: If we neglect the overhead generated by statistical TDM, a system will have two possibilities: * Minimum: If all channels have equal data then the rate will be K/N bps* Maximum: If only one channel active and the others are passive, then rate will be K bpsChapter 13 - Local Area Networks: Packets, Frames, And Topologies13.1 What is circuit switching, and what are its chief characteristics?Answer: The term circuit switching refers to a communication mechanism that establishes a path between a sender and receiver with guaranteed isolation from paths used by other pairs of senders and receivers. The circuit switching has the following main characteristics:* Point-to-point communication* Separate steps for circuit creation, use, and termination* Performance equivalent to an isolated physical path13.3 In a packet switching system, how does a sender transfer a large file?Answer: The packet switching system requires a sender to divide each message into blocks of data that are known as packets . The size of a packet varies; each packet switching technology defines a maximum packet size. So, a large file will be divided into smaller pieces and sent.13.5 What are the characteristics of LANs, MANs, and W ANs?Answer: There are lots of details that can be said and discussed for categorization of network types based on geography, few points are highlighted below:* Local Area Network (LAN): Least expensive; spans a single room or a single building* Metropolitan Area Network (MAN) Medium expense; spans a major city or a metroplex* Wide Area Network (WAN) Most expensive; spans sites in multiple cities13.6 Name the two sublayers of Layer 2 protocols defined by IEEE, and give the purpose of each.Answer: The Layer 2 protocols defined by IEEE defines two sub-layers as mentioned below:* Logical Link Control (LLC) Addressing and demultiplexing* Media Access Control (MAC) Access to shared media13.8 What are the four basic LAN topologies?Answer: The four basic LAN topologies are star, ring, mesh and bus.13.10 In a mesh network, how many connections are required among 20 computers?Answer: The expression to calculate number of connections in a mesh network is given by n (n-1)/2. So for 20 computers then number of connections required will be = 20 (20 – 1)/2 =19013.15 Give a definition of the term frame .Answer: In a packet-switched network, each frame corresponds to a packet processed at data link layer.Chapter 14 - The IEEE MAC Sub-Layer14.1 Explain the three basic approaches used to arbitrate access to a shared medium.(See Textbook)14.3 List the three main types of channelization and the characteristics of each.(See Textbook)14.6 What is a token, and how are tokens used to control network access?Answer: A special control message is called a token. In a token passing system, when no station has any packets to send, the token circulates among all stations continuously. When a station captures the token, it sends its data, and when transmission completed, it releases the token.14.8 Expand the acronym CSMA/CD, and explain each part.Answer: The acronym CSMA/CD stands for Carrier Sense Multi-Access with Collision Detection, which means the following: * Carrier Sense: Instead of allowing a station to transmit whenever a packet becomes ready, Ethernet requires each station to monitor the cable to detect whether another transmission is already in progress.* Multiple Access: The system allows multiple users/hosts to make use of a common/shared media* Collision Detection. A collision can occur if two stations wait for a transmission to stop, find the cable idle, and both start transmitting.14.10 Why does CSMA/CD use a random delay? (Hint: think of many identical computers on a network.)Answer: Randomization is used to avoid having multiple stations transmit simultaneously as soon as the cable is idle.That is, the standard specifies a maximum delay, d, and requires each station to choose a random delay less than d after a collision occurs. In most cases, when two stations each choose a random value, the station that chooses the smallest delay willChapter 15 - Wired LAN Technology (Ethernet And 802.3)15.1 How large is the maximum Ethernet frame, including the CRC?Answer: According to Fig. 15.1 a conventional Ethernet frame has the following fields:* Header: 14 bytes (fixed)* Payload: 46-1500 bytes (there is a minimum frame size because of collision detection)* CRC: 4 bytes (fixed)Accordingly an Ethernet frame will be maximum 1518 bytes and minimum 64 bytes15.3 In an 802.3 Ethernet frame, what is the maximum payload size?Answer: The 802.3 Ethernet makes use of 8-bytes of the original/conventional Ethernet for Logical Link Control / Sub-Network Attachment Point (LLC / SNAP) header instead of extending/increasing the header. This is for sake of backward compatibility. So the maximum pay load is reduced from 1500 bytes to 1492 bytes.15.6 How did a computer attach to a Thicknet Ethernet?Answer: Hardware used with Thicknet was divided into two major parts:* Transceiver: A network interface card (NIC) handled the digital aspects of communication, and a separate electronic device called a transceiver connected to the Ethernet cable and handled carrier detection, conversion of bits into appropriate voltages for transmission, and conversion of incoming signals to bits.* AUI: A physical cable known as an Attachment Unit Interface (AUI) connected a transceiver to a NIC in a computer. A transceiver was usually remote from a computer.15.7 How were computers attached to a Thinnet Ethernet?Answer: Thinnet Ethernet (formally named 10Base2) uses a thinner coaxial cable that was more flexible than Thicknet. The wiring scheme differed dramatically from Thicknet. Instead of using AUI connections between a computer and a transceiver, Thinnet integrates a transceiver directly on the NIC, and runs a coaxial cable from one computer to another.15.8 What is an Ethernet hub, and what wiring is used with a hub?Answer: An electronic device that serves as the central interconnection is known as a hub. Hubs were available in a variety of sizes, with the cost proportional to size. The hubs are becoming old-fashioned, and being replaced with switches.15.3 What category of twisted pair wiring is needed for a 10 Mbps network? 100 Mbps? 1000 Mbps?Answer: The three major categories of Ethernet and their wiring is listed below:* 10 Mbps: 10BaseT (Ethernet) Category 5* 100 Mbps: 100BaseT (Ethernet Fast) Category 5E* 1 Gbps: 1000BaseT (Gigabit Ethernet) Category 6Chapter 20 - Internetworking: Concepts, Architecture, and Protocols20.2 Will the Internet be replaced by a single networking technology? Why or why not?Answer: Incompatibilities make it impossible to form a large network merely by interconnecting the wires among networks. The beauty of the Internet is interconnection of wide range of technologies from various manufacturers.Diversity of the products and solutions is a richness instead of limitation as long as they all adopt the same set of protocols.20.3 What are the two reasons an organization does not use a single router to connect all its networks?Answer:An organization seldom uses a single router to connect all of its networks. There are two major reasons: * Because the router must forward each packet, the processor in a given router is insufficient to handle the traffic passing among an arbitrary number of networks.* Redundancy improves internet reliability. To avoid a single point of failure, protocol software continuously monitors internet connections and instructs routers to send traffic along alternative paths when a network or router fails.20.6 In the 5-layer reference model used with the TCP/IP Internet protocols, what is the purpose of each of the five layers?(See 1.11)Chapter 21- IP: Internet Addressing21.3 In the original classful address scheme, was it possible to determine the class of an address from the address itself? Explain.Answer:Yes, since in the classful addressing scheme initial bit(s) gives indication about the class being used.21.7 If an ISP assigned you a /28 address block, how many computers could you assign an address?Answer: When an organization is assigned /28 CIDR address, it means 28 bits out of 32 bits are fixed, so 32-28 = 4 bits available for user space. So number of users 24-2 = 4, since the all 0s and all 1s address are having special use and can’t be assigned to a user.21.8 If an ISP offers a / 17 address block for N dollars per month and a / 16 address block for 1.5 N dollars per month,which has the cheapest cost per computer?Answer: Number of addresses in /17 block 232-17 = 215Price per address: N /215 = N / 215Number of addresses in /16 block 232-16 = 216Price per address: 1.5N /216 = 0.75N/215 So /16 address block will be cheaper in comparison with the price given for /17 block.21.10 Suppose you are an ISP with a / 24 address block. Explain whether you accommodate a request from a customer who needs addresses for 255 computers. (Hint: consider the special addresses.)Answer: For a/24 address block, number of available addresses will be 232-24 = 28 = 256. However, a suffix with all 0s address is reserved for network ID and a suffix with all 1s address is reserved for broadcast address, so number of addresses that can be assigned to computers/hosts will be 256 -2 = 254.21.11 Suppose you are an ISP that owns a / 22 address block. Show the CIDR allocation you would use to allocateaddress blocks to four customers who need addresses for 60 computers each.Answer: The /22 address block can be assigned as follows:ddd.ddd.ddd.00/26ddd.ddd.ddd.01/26ddd.ddd.ddd.10/26ddd.ddd.ddd.11/26Chapter 22- Datagram Forwarding22.1 What are the two basic communication paradigms that designers consider when designing an internet?Answer:* Connection-oriented service * Connectionless service22.2 How does the Internet design accommodate heterogeneous networks that each have their own packet format?Answer: To overcome heterogeneity, the Internet Protocol defines a packet format that is independent of the underlying hardware. The result is a universal, virtual packet that can be transferred across the underlying hardware intact. The Internet packet format is not tied directly to any hardware. The underlying hardware does not understand or recognize an Internet packet.22.5 What is the maximum length of an IP datagram?In the current version of the Internet Protocol (IP version 4), a datagram can contain at most 64 K (65535) octets, including the header.22.7 If a datagram contains one 8-bit data value and no header options, what values will be found in header fields H.LEN and TOTAL LENGTH?Answer: H. LEN indicated header in 32-quantities, since no options, then this value will be 5. The TOTAL LENGTH indicated the number of bytes in a datagram including the header. This means 5x4 bytes + 1 (8-bits) = 21 bytesChapter 23 - Support Protocols And Technologies23.1 When a router uses a forwarding table to look up a next-hop address, the result is an IP address. What must happenbefore the datagram can be sent?Answer: Each router along the path uses the destination IP address in the datagram to select a next-hop address, encapsulates the datagram in a hardware frame, and transmits the frame across one network. A crucial step of the forwarding process requires a translation: forwarding uses IP addresses, and a frame transmitted across a physical network must contain the MAC address of the next hop.23.2 What term is used to describe the mapping between a protocol address and a hardware address?Answer: Translation from a computer’s IP address to an equivalent hardware address is known as address resolution, and an IP address is said to be resolved to the correct MAC address. The TCP/IP protocol being used for this is called Address Resolution Protocol (ARP). Address resolution is local to a network.23.5 How many octets does an ARP message occupy when used with IP and Ethernet addresses?Answer: According to Fig 23.3 an ARP message has 7-lines of each being 32-bit (4 bytes or octets), therefore,number of octets in an ARP can be determined as 7x4 = 28 octets23.10 What types of addresses are used in layers below ARP?Answer:ARP forms a conceptual boundary in the protocol stack; layers above ARP use IP addresses, and layers below ARP use MAC addresses.23.17 What is the chief difference between BOOTP and DHCP?Answer:The main difference is that the BOOTP protocol required manual administration. So before a computer could use BOOTP to obtain an address, a network administrator had to configure a BOOTP server to know the computer’s I P address. Chapter 24 - The Future IP (IPv6)24.3 List the major features of IPv6, and give a short description of each.(See Textbook)24.4 How large is the smallest IPv6 datagram header?Answer: IPv6 datagram header consists of a base header + zero or more extension header. Since, smallest header is being asked, we assume zero extension header and consider IPv6 will have only base header. If we look at IPv6 header format in Fig. 24.3, it shows that 10x4 bytes = 40 bytes.Chapter 26 - TCP: Reliable Transport Service26.2 List the features of TCP.(See Textbook)26.6 When using a sliding window of size N, how many packets can be sent without requiring a single ACK to be received?Answer: If the size of the window is N, then it means a sender can transmit up to N packets without waiting for an ACK, as long as other controls are in place.26.9 What is the chief cause of packet delay and loss in the Internet?Answer: The main cause of packet delay and loss in the Internet is congestion.Chapter 28 - Network Performance (QoS and DiffServ)28.1 List and describe the three primary measures of network performance.(See Textbook)28.2 Give five types of delay along with an explanation of each.(See Textbook)Chapter 30 - Network Security30.1 List the major security problems on the Internet, and give a short description of each.(See Textbook)30.2 Name the technique used in security attacks.(See Textbook)30.8 List and describe the eight basic security techniques.(See Textbook)。
计算机网络试卷及答案-英文版
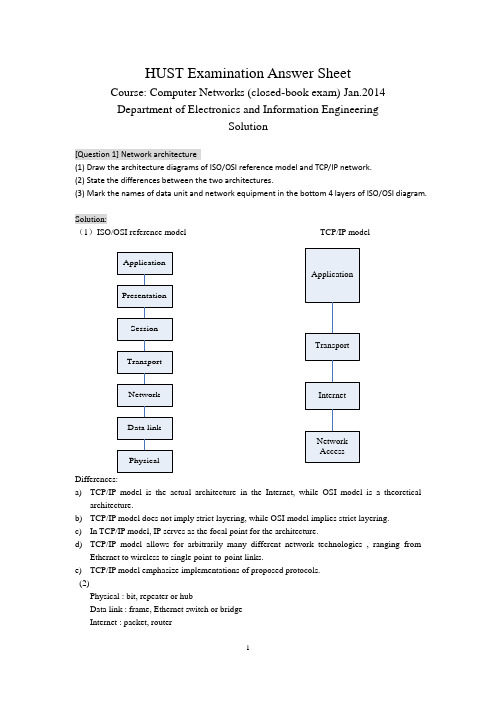
HUST Examination Answer SheetCourse: Computer Networks (closed-book exam) Jan.2014 Department of Electronics and Information EngineeringSolution[Question 1] Network architecture(1) Draw the architecture diagrams of ISO/OSI reference model and TCP/IP network. (2) State the differences between the two architectures.(3) Mark the names of data unit and network equipment in the bottom 4 layers of ISO/OSI diagram.Solution:(1)ISO/OSI reference model TCP/IP modelDifferences:a) TCP/IP model is the actual architecture in the Internet, while OSI model is a theoreticalarchitecture.b) TCP/IP model does not imply strict layering, while OSI model implies strict layering. c) In TCP/IP model, IP serves as the focal point for the architecture.d) TCP/IP model allows for arbitrarily many different network technologies , ranging fromEthernet to wireless to single point-to-point links.e) TCP/IP model emphasize implementations of proposed protocols. (2)Physical : bit, repeater or hubData link : frame, Ethernet switch or bridge Internet : packet, routerTransport : message, gateway[Question 2] Principles of network designSelect ONE of the following principles, tell its main ideas and provide an example. (1) Keep it simple and stupid(2) Complex edge and simple core (3) Smart sender and dumb receiverSolution:(1) KISS: Keep It Simple and StupidIt means that you should make things simple in the designing. One example following it : Ethernet(2) Complex edge and simple coreIt means that the hosts are very complex and have many functions while the nodes are very simple and have few functions.One example following it : The design of router, or the functions of TCP and IP(3) Smart sender and dumb receiverIt means that the function of sender is more complex than that of the receiver, which is help to improve the robustness and performance of communication protocol. One example following it: The flow control of TCP protocol[Question 3] Error detection(1) Tell the main idea of error detection and error correction in communication.(2) Given the CRC polynomial x 4 + x 3 + 1, if the original message is 10110011010, what is the CRC message to send?(3) Suppose the first bit of the message in (2) is inverted due to the noise in transmission. How can the receiver detect it via CRC verification?Solution:(1)1087431()M x x x x x x x =+++++, 43()1C x x x =++. So k=4.a) Multiply M(x) by 2kto get 141211875()T x x x x x x x =+++++,b) Then divide T(x) by C(x) to get the remainder 0000.c) The message that should be transmitted is 101100110100000.(2)The message received is 001100110100000.Divide it by C(x), then the remainder is 1100.So it is not divisible by C(x).So the receiver knows that an error has occurred.(1) What are the essential components to realize reliable transmission?(2) Suppose two computers are communicated via Stop-and-wait protocol. The link bandwidth is 5kbps, and the one-way propagation delay is 20ms. To reach 80% or higher link utilization, what is the minimal frame size for this communication?(3) If it is upgraded to Sliding-Window protocol. To reach the same goal with (2), what is the minimal window size, how many bits are required to describe the frame sequence in window? (Suppose the frame size is 1 or 100Byte)Solution:(1)ACK, and timerActual_throughput = Data / Total_DelayTotal_Delay = RTT + Data / BWLink_Utilization = 100 * Actual_throughput / BWSo: Data/throughput = RTT + Data/BW(BW/throughput - 1) Data = BW*RTTData = BW*RTT/(1/Utilization -1)For the stop-and-wait protocol, for each RTT only one frame is sent,Thus Frame_size = Data = BW*RTT/(1/Utilization - 1) = 5kbps * 40ms / (1/0.8 - 1)= 200 bit / 0.25 = 800 bit = 100 ByteIf the students ignore the data transmission delay, their answer isframe_size = BW*RTT*Utilization = 5000 bit/sec * 40 / 1000 sec * 0.8 = 160 bit = 20 ByteIn this case, at least -2 score.(3)For the sliding-window protocol, in each RTT the data window can be transmitted at most.Thus Window_size = Data = BW*RTT/(1/Utilization - 1) = 5kbps * 40ms / (1/0.8 - 1)= 200 bit / 0.25 = 800 bit = 100 ByteIf the frame size is 100Byte, 1 frames are allowed.To indicate the frames in both sides of sender and receiver, the sequence number should describe 2 frames, thus the [log2(2) ]=1 bitIf the students ignore the data transmission delay, their answer iswindow_size = BW*RTT*Utilization = 5000 bit/sec * 40 / 1000 sec * 0.8 = 160 bit = 20 ByteIf the frame size is 100Byte, 1 frames are allowed.To indicate the frames in both sides of sender and receiver, the sequence number should describe 2 frames, thus the [log2(2) ]=1 bitIn this case, at least -2 score.(1) What is the main idea of CSMA/CD (Carrier Sense Multiple Access/Collision Detection) in traditional Ethernet? Can it be deployed for wireless local network, why?(2) Suppose one traditional Ethernet has 1km cable, the signal propagation speed is 2*105km/s, and the transmission rate is designed to be 100Mbps. What is the minimal frame size to support carrier sensing?Solution:(1) the main idea of CSMA/CD include two parts. One is carrier sensing, which means the node should detect the channel before sending any data. If the node finds the channel is idle, it begins to transmit. Otherwise, the node stop for next round. The second issues is collision detection, which means the node should detect the channel in the duration of its data transmission. If the node finds the channel become busy, or in other word, there is a collision, it should stop transmitting immediately.CSMA/CD cannot be deployed in wireless LAN, because the wireless radio transmitter and receiver can not work in dual mode. The wireless node cannot detect collision when it is transmitting data.(2)the minimal frame should be transmitted throughout the whole traditional Ethernet.Thus t = frame_size / transmit_rate = 2 * cable_length / prop_speed.Frame_size = 100 * 106 bits/sec * 2 * 103 m / (2 * 108)m/sec = 1000 bits = 125 Byte[Question 6] Switched network(1) What are the differences between circuit switching and packet switching?(2) For the following linear topology network, each link has 2ms propagation delay and 4 Mbps bandwidth.A B C DIf we use circuit switching, circuit setup requires a 1KB message to make one round-trip on the path, which incurs a 1ms delay at each switch after the message has been completely received. Then we can send the file as one contiguous bit stream. What is the delay for circuit switching to transmit n-byte from A to D?(3) If we use packet switching in the network of (2), we can break the file into 1KB packets, which has 24byte header and 1000byte payload. The switch takes 1ms process delay after receiving the packet, and then sent it continuously. What is the condition for packet switching to have less delay performance than circuit switching?Solution:(1)(2)T pkt = Packet_Size / Bandwidth = 1 KB / 4Mbps = 1024 *8 / (4 * 106) = 2.048 ms T p = 2 ms, T s = 1 ms,T t = n B / 4MbpsIn circuit switching, Total time duration:D = Singling_Delay + Transmission_Delay = 2 * Packet_Duration + Transmission_Delay = 2 * (T pkt * 2 + T p * 3 + T s * 2 + T pkt ) + (T p * 3 + T t ) = T pkt * 6 + T p * 9 + T s * 4 + T tThus, D = 2.048 * 6 + 2 * 9 + 1 * 4 + n * 8 bits / 4Mbps = 34.288 (ms) + 2n (us)(3)Main ideaThe reliability provided by endhost The reliability provided by thenetwork Information in packet Every packet has its dest-addrin header Every packet has its temp VCIlocally Forwarding action inswitch Every packet was treatedindependentlyThe packets are processed inthe manner of VCPackets received indestinationNot in sequenceIn sequenceT pkt = Packet_Size / Bandwidth = 1 KB / 4Mbps = 1024 *8 / (4 * 106) = 2.048 msT p = 2 ms,T s = 1 ms,T t = 1.024 * n B / 4MbpsIn packet switching, Total time duration:D = Delay_at_Switch * Switch_Num + Delay_at_last_hop= (T p + T pkt +T s)*2 + (T p + T t )= T pkt * 2 + T p * 3 + T s * 2 + T tThus, D = 2.048 * 2 + 2 * 3 + 1 * 2 + 1.024 * n B / 4Mbps= 12.096 (ms) + 2.048 n (us)In order to make34.288 (ms) + 2n (us) > 12.096 (ms) + 2.048 n (us)Thus 22.192(ms) > 0.048 n(us)n < 22.192 * 1000 / 0.048 = 462333 Byte = 451.5 KB[Question 7] Ethernet Switch(1) What are the differences between hub and switch in Ethernet?(2) Suppose one server and nine clients are connected via hub in 10Mbps Ethernet, what is the maximal bandwidth for the client-server connection?(3) If the hub is upgraded to switch, can the client-server connection obtain more bandwidth? if can, how much is it?Solution:(1)hub works in Layer2, it works as the shared media and relays the frames to all the nodes connecting to hub. Switch works in Layer2, it forwards the frames to the specific node according to the destination address embedded in the frame header.(2)the max bandwidth in client-server connection is 10Mbps/(1+9)= 1Mbps(3)the max bandwidth in client-server connection is 10Mbps/9 = 1.1111MbpsAdditional 0.1111 Mbps is obtained for each connection.[Question 8] Router(1) Somebody says that, ``the only difference between switch and router is that they do switch function based on the address in different layers.’’ Is it correct? Why?(2) If we obtain the following information from one router. What kind of routing protocol does itSolution:(1)it is not fully correct. The part talking about the forwarding function is correct, while it is not the only difference. Another but not the last difference is that, router has more functions on control plane, which do routing and find the paths for packets.(2)The routing protocol is RIP.The routing table is:Destination Next hop Interface192.168.1.0/24 * Fa 0/4192.168.2.0/24 * Fa 0/6192.168.10.0/24 192.168.1.1 Fa 0/4192.168.30.0/24 192.168.2.2 Fa 0/6[Question 9] Routing algorithm(1) State the main differences between distance vector routing and link state routing.(2) For the network given in the following figure, provide the steps of forward search in Dijkstra algorithm for node A finding the shortest path to node ESolution:(1) The idea of distance vector routing is to tell the neighbors about the learned topology to all the nodes in the network. The idea of link state routing is to tell all the nodes in network about the neighborhood topology.Step 1 2 3 4 5 6 7 8 9Confirmed (A,0,-) (A,0,-) (A,0,-)(D,2,D)(A,0,-)(D,2,D)(A,0,-)(D,2,D)(B,4,D)(A,0,-)(D,2,D)(B,4,D)(A,0,-)(D,2,D)(B,4,D)(E,6,D)(A,0,-)(D,2,D)(B,4,D)(E,6,D)(A,0,-)(D,2,D)(B,4,D)(E,6,D)(C,7,D)Tentative (B,5,B)(D,2,D)(B,5,B) (B,4,D)(E,7,D)(E,7,D)(E,6,D)(C,8,D)(C,8,D) (C,7,D)A→E A→D→EA→D→B→EA→D→B→E[Question 10] IP address allocationA company has one C class IP address of 200.1.1.*. It has four departments.(1) If each department has less than 25 computers. Provide a kind of IP address allocation. Give the network address, subnet mask, and the available IP address range for each department. (2) If the four departments have 72, 35, 34, 20 computers respectively. Provide the IP address allocation scheme again.Solution:(1)Since each department has less than 25 computers, even considering the additional two more IP address for gateway and broadcast, the 64-computer subnet is enough for them.One IP address allocation scheme is to even divide the 256 IP addresses into 4 subnets, each subnet allows 64 hosts.Another IP address allocation scheme is to even divide the 256 IP addresses into 4 subnets, each subnet allows 32 hosts.(2) Since one of the department has more requirements than 64, then the even distribution scheme[Question 11] TCP protocol(1) Somebody says that, ``because of the reliable transmission service in layer 2, there is no need to provide such service again within TCP protocol in layer 4’’. Is it correct? Why?(2) State the main rules of TCP connection setup according to the following figure. Explain every word and number in the figure.Solution:(1) It is wrong. TCP is based on the un-reliable IP layer, which only provides best effort service. If TCP wants to provide reliable transmission service, it has to realize this by itself.(2)TCP use three hand-shakes to setup the connection.According to the figure, there are two nodes. The sender is with IP address of 192.168.1.163 and the receiver 192.168.1.165 respectively.●At first, the sender send a request ``SYN’’to the receiver to setup the connection. Thismessage is with the sequence number of 424CF1DC;●Secondly, the receiver reply an acknowledgment message ``SYN/ACK’’ to the sender. Thismessage has two sequence numbers. The seq in the ACK is 424CF1DD, which is to confirm the last ``SYN’’ from sender. The seq in the SYN is 30318555, which is a new message from the receiver.●Thirdly, the sender reply an acknowledgment message ``ACK’’ to the receiver. The seq in theACK is 30318556, which is to confirm the last ``SYN’’ from receiver.In the end, both the sender and receiver knows that the other side is ready for this TCP connection.[Question 12] TCP congestion control(1) Both flow control and congestion control in TCP are realized by window based packet control. How can TCP get the window sizes in these two mechanisms?(2) Assume that TCP implements an extension that allows window sizes much larger than 64 KB. Suppose that you are using this extended TCP over a 1Gbps link with a latency of 150ms. TCP packet size is 1KB, and the max receive window is 1 MB. Suppose there is no real congestion and packet loss in transmission. How many RTTs does it take until slow start opens the send window to 1 MB? How long does it take to send the complete file? ( Suppose file size is 10MB )Solution:(1) In flow control, TCP sender knows the window size by the field of advertise-window replied from the receiver. In congestion control, TCP sender learns the window size adaptively by AIMD( Additive Increase and Multiplicative Decrease) mechanism responding to the packet lossevent.(2)When TCP realizes congestion control mechanism, its effective send window size will be min (CongestionWindow, AdvertizedWindow). In original design of TCP header, the field of AdvertizedWindow is 16 bit, which is 216=26*210=64 KB. So the maximum effective window of original TCP sender is 64KB. The assumption of the first sentence in this question relaxes such constraint for TCP.In slow start, the send window starts from w0=1 packet, which is 1 KB. For each RTT after a successful transmission, the window size will be doubled. After i RTT, it will be 2i * w0. Let 2i * 1KB = 1MB, soi = log2(1MB/1KB) = log2(210) = 10.It will take 10 RTTs to reach 1MB send window.Case 1: if the receiver window remains as 1MBIn the first 10 RTTs, total (1 + 2 + 4 + … + 210) * 1KB has been transmitted.Which is (211 - 1) * 1KB = 2 MB - 1 KB, the rest file is 10MB - (2MB - 1KB) = 8MB + 1KBIn the reset transmission, each RTT can only support 1MB transmission.Thus, additional 9 RTTs are required. Total 19 RTT = 19 * 150ms = 2.85 sCase 2: if the receiver window can be changed.Since there is no congestion and loss, the maximum send window will be the bandwidth * delay for this TCP connection.w max= 1G bps * 150ms = 109 * 150 * 10-3= 150 *106 bit = 18.75 * 106 byte = 17.88 MB.So, this 10 MB file can be transferred before reaching w max. In another word, it can be sent in its slow start phase. Assume x RTT is required to send this file, then:(1 + 2 + 4 + … + 2x) * 1KB ≥ 10 MB2 * 2x–1 ≥ 10 * 1024x ≥ log2(10241) – 1 = 12.3Thus x = 13, it will take 13 RTTs to transfer this file. 13RTT = = sTotal delay = 13RTT + Filesize/BW = 13 * 150ms+ 10MB / 1Gbps =1.95 + 0.08 * 1.024^2=2.03 s11。
计算机网络英文复习题
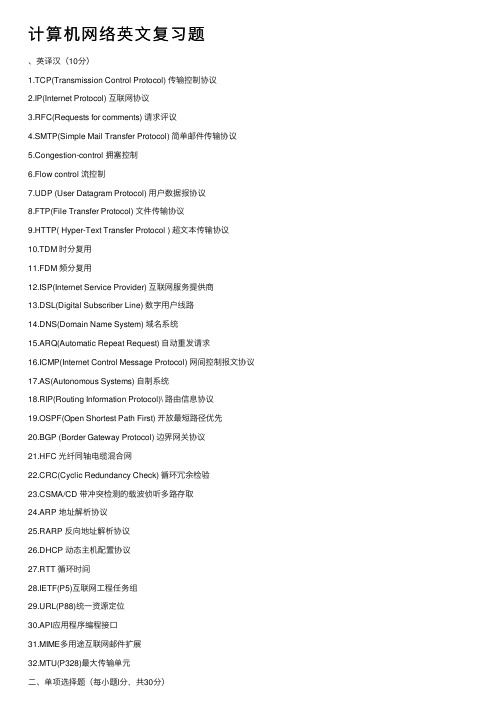
计算机⽹络英⽂复习题、英译汉(10分)1.TCP(Transmission Control Protocol) 传输控制协议2.IP(Internet Protocol) 互联⽹协议3.RFC(Requests for comments) 请求评议4.SMTP(Simple Mail Transfer Protocol) 简单邮件传输协议5.Congestion-control 拥塞控制6.Flow control 流控制7.UDP (User Datagram Protocol) ⽤户数据报协议8.FTP(File Transfer Protocol) ⽂件传输协议9.HTTP( Hyper-Text Transfer Protocol ) 超⽂本传输协议10.TDM 时分复⽤11.FDM 频分复⽤12.ISP(Internet Service Provider) 互联⽹服务提供商13.DSL(Digital Subscriber Line) 数字⽤户线路14.DNS(Domain Name System) 域名系统15.ARQ(Automatic Repeat Request) ⾃动重发请求16.ICMP(Internet Control Message Protocol) ⽹间控制报⽂协议17.AS(Autonomous Systems) ⾃制系统18.RIP(Routing Information Protocol)\ 路由信息协议19.OSPF(Open Shortest Path First) 开放最短路径优先20.BGP (Border Gateway Protocol) 边界⽹关协议21.HFC 光纤同轴电缆混合⽹22.CRC(Cyclic Redundancy Check) 循环冗余检验23.CSMA/CD 带冲突检测的载波侦听多路存取24.ARP 地址解析协议25.RARP 反向地址解析协议26.DHCP 动态主机配置协议27.RTT 循环时间28.IETF(P5)互联⽹⼯程任务组29.URL(P88)统⼀资源定位30.API应⽤程序编程接⼝31.MIME多⽤途互联⽹邮件扩展1. DSL divides the communication link between the home and the ISP into three nonoverlapping frequency bands, a upstream channel is in _A_________.A)50 kHz to 1MHz band B) 1MHz to 2MHz bandC)4 kHz to 50kHz band D) 0 to 4kHz band2. As a data packet moves from the upper to the lower layers, headers are A .A) Added; B) subtracted; C) rearranged; D) modified3. What is the main function of the network layer? DA) node-to-node delivery; B) process-to-process message deliveryC) synchronization; D) updating and maintenance of routingtables4. Which of the following is the default mask for the address 168.0.46.201? BA) 255.0.0.0; B) 255.255.0.0; C) 255.255.255.0; D) 255.255.255.2555.A router reads theaddress on a packet to determine the next hop. AA) IP ; B) MAC; C) source; D)ARP6 .Which device can’t isolates the departme ntal collision domains. AA) Hub; B) switch; C) router; D) A and B7. Input port of a router don’t perform ____D____ functions.A) the physical layer functions B) the data link layer functionsC) lookup and forwarding function D) network management8. HTTP has a mechanism that allows a cache to verify that its objects are up to date. The mechanism is DA) persistent connections B) cookies C) Web Caching D) conditional GET9. A protocol layer can be implemented in ___D_____.A) software B) hardware C) a combination of the software and hardware D) All of the above10. A protocol has three important factors, they are_A______.A)syntax, semantics, order B) syntax, semantics, layerC)syntax, semantics, packet D) syntax , layer, packet11. There are two broad classes of packet-switched networks: datagram networks and virtual-circuit networks. The virtual-circuit networks forward packets in their switches use ___D___.A) MAC addresses B) IP addressesC) e-mail addresses D) virtual-circuit numbers12. TCP service model doesn’t provide ___D_______service.A) reliable transport service B) flow control serviceC) congestion-control service D) guarantee a minimum transmission rate service.13. Usually elastic applications don’t include____B______.A) Electronic mail B) Internet telephony14. A user who uses a user agent on his local PC receives his mail sited in a mail server by using _B___ protocol.A)SMTP B) POP3C)SNMP D) FTP15. Considering sliding-window protocol, if the size of the transmitted window is N and the size of the receiving window is 1,the protocol is BA) stop-and-wait protocol B) Go-Back-N protocolC) selective Repeat protocol D) alternating-bit protocol16. which IP address is effective___B______.A) 202,131,45,61 B) 126.0.0.1C) 192.268.0.2 D) 290.25.135.1217. if IP address is 202.130.191.33, subnet mask is 255.255.255.0,then subnet prefix is__D_____A) 202.130.0.0 B) 202.0.0.0C) 202.130.191.33 D)202.130.191.018.The command Ping s implemented with __B______messagesA) DNS B) ICMPC) IGMP D) RIP19. Which layer-function is mostly implemented in an adapter? __A________A) physical layer and link layer B) network layer and transport layerC)physical layer and network layer D) transport layer and application layer20. If a user brings his computer from Chengdu to Peking, and accesses Internet again. Now, __B_____ of his computer needs to be changed.A) MAC address B) IP addressC) e-mail address D) user address1. .traceroute is implemented with __B____messages.A) DNS B) ICMPC) ARP D) RIP2.A router reads the A address on a packet to determine the next hop.A. IP ;B. MAC;C. source;D.ARP3. There are two broad classes of packet-switched networks: datagram networks andvirtual-circuit networks. The virtual-circuit networks forward packets in their switches use ___D___.A) MAC addresses B) IP addressesC) e-mail addresses D) virtual-circuit numbersA) device interfaces with same subnet part of IP addressB) can’t physically reach each other without intervening a router.C)all of the devices on a given subnet having the same subnet address.D)A portion of an interface’s IP address must be determined by the subnet to which it is connected.5. if IP address is 102.100.100.32, subnet mask is 255.255.240.0,then subnet prefix is___A___A) 102.100.96.0 B) 102.100.0.0C) 102.100.48.0 D) 102.100.112.06 If a user brings his computer from chengdu to beijing, and accesses Internet again. Now,___B__ of his computer needs to be changed.A) MAC address B) IP addressC) e-mail address D) user address7.I nput port of a router don’t perform ____D___ functions.A) the physical layer functions B) the data link layer functionsC) lookup and forwarding function D) network management8.switching fabric is at the heart of a router, switching can be accomplished in a number of ways, donit include_D_A)Switching via memory B)Switching via crossbarC)Switching via a bus D) Switching via buffer9.if a host wants to emit a datagram to all hosts on the same subnet, then the datagram’s destination IP address is ___B__A)255.255.255.0 B) 255.255.255.255C)255.255.255.254 D) 127.0.0.110.The advantage of Circuit switching does not include________.A) small transmission delay B)small Processing costC) high link utilization D)no limited to format of message1.an ARP query sent to __A__A) local network B) all over the Internet.2. .packet-switching technologies that use virtual circuitsinclude__B___:A) X.25, ATM, IP B) X.25, ATM, frame relay.C) IPX, IP, ATM D) IPX, IP, TCP3. In Internet, _D_ protocol is used to report error and provide the information forun-normal cases.A) IP B) TCP C)UDP D) ICMP1.A is a Circuit-switched network.B. Datagram networkC. InternetD. virtual circuit network2.The store-and-forward delay is DA. processing delayB. queuing delayC. propagation delayD. transmission delay3.Which is not the function of connection-oriented service? DA. flow controlB. congestion controlC. error correctionD. reliabledata transfer4.The IP protocol lies in CA. application layerB. transport layerC. network layerD. link layer5.Which of the following is the PDU for application layer __B___A.datagram;B. message;C. frame;D.segment6.bandwidth is described in _B__A) Bytes per second B) Bits per secondC) megabits per millisecond D) centimeters7.A user who uses a user agent on his local PC receives his mail sited in a mail server by using __A__ protocol.A)SMTP B) POP3C)SNMP D) FTP8.As a data packet moves from the lower to the upper layers, headers are B.A)Added; B. subtracted; C. rearranged; D. modified三、填空题(每空1分,共22分 (注意:所有填空题不能写中⽂,否则中⽂答案对的情况1. link-layer address is variously called a LAN address, a MAC address, or a physical address.2 In the layered architecture of computer networking, n layer is the user of n-1 layer and the service provider of n+1 layer.A) n B) n+3 C) n+1 D) n-1四、判断题(每⼩题1分,共10分)1.√The services of TCP’s reliable data transfer founded on the services of theunreliable data transfer.2.√Any protocol that performs handshaking between the communication entitiesbefore transferring data is a connection-oriented service.3.× HOL blocking occur in output ports of router.4.√Socket is globally unique.5.√SMTP require multimedia data to be ASCII encoded before transfer.6.×The transmission delay is a function of the distance between the two routers.7.×IP address is associated with the host or router. SO one device only have one IPaddress.8. √In packet-switched networks, a session’s messages use the resources on demand, and Internet makes its best effort to deliver packets in a timely manner.9. ×UDP is a kind of unreliable transmission layer protocol, so there is not any checksum field in UDP datagram header.10.√Forwarding table is configured by both Intra and Inter-AS routing algorithmIP is a kind of reliable transmission protocol. F8.Forwarding table is configured by both Intra and Inter-AS routing algorithm.T9.Distance vector routing protocol use lsa to advertise the network which router10.RIP and OSPF are Intra-AS routing protocols T11.Packet switching is suitable for real-time services, and offers better sharing ofbandwidth than circuit switching F五、计算题(28 points)1.C onsider the following network. With the indicated link costs, use Dijkstra’s shortest-path algorithm to compute the shortest path from X to all network nodes.2 Given: an organization has been assigned the network number 198.1.1.0/24 and it needs todefine six subnets. The largest subnet is required to support 25 hosts. Please:●Defining the subnet mask; (2分) 27bits or 255.255.255.224●Defining each of the subnet numbers; which are starting from 0# (4分)198.1.1.0/27 198.1.1.32/27 198.1.1.64/27 198.1.1.96/27 198.1.1.128/27 198.1.1.160/27 198.1.1.192/27 198.1.1.224/27●Defining the subnet 2#’s broadcast address.(2分) 198.1.1.95/27Defining host addresses scope for subnet 2#. (2分) 198.1.1.65/27--198.1.1.94/273. Consider sending a 3,000-byte datagram into a link that has an MTU of 1500bytes.Suppose the original datagram is stamped with the identification number 422 .Assuming a 20-byte IP header,How many fragments are generated? What are their characteristics?(10分)。
计算机网络英文题库附答案chater
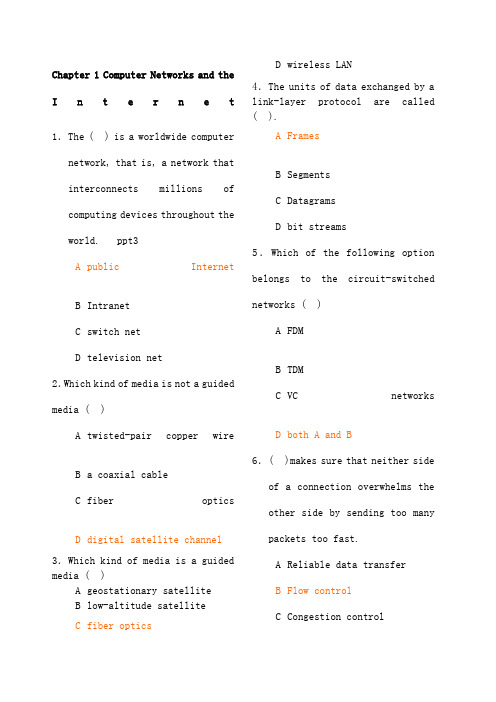
Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computernetwork, that is, a network that interconnectsmillionsofcomputing devices throughout theworld. ppt3 A public InternetB IntranetC switch netD television net2.Which kind of media is not a guidedmedia ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following optionbelongs to the circuit-switchednetworks ( )A FDMB TDMC VCnetworksD both A and B 6.( )makes sure that neither sideof a connection overwhelms theother side by sending too manypackets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch mustreceive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagramnetworksandvirtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, and virtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, and virtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuit networks use VC. numbers to forward packets toward their destination.D datagram networks use VC. numbers and virtual-circuit networks use destination addresses to forward packetstoward their destination.9.In the following options, which one is not a guided media ( )A twisted-pairwireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet ’s headerB wait to transmit the packet onto the linkC determine where to direct thepacketD check bit-error in the packet 11.In the following four descriptions, which one is correct ( )A The traffic intensity must begreater than 1.B The fraction of lost packetsincreases as the trafficintensity decreases.C If the traffic intensity isclose to zero, the averagequeuing delay will be close tozero.D If the traffic intensity isclose to one, the averagequeuing delay will be close toone.12.The Internet’s network layer is responsible for movingnetwork-layer packets known as( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layersare called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes ofpacket-switched networks: ( )networks and virtual-circuitnetworks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be looselyclassified into threecategories: residential access,company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue,R is the transmission rate, and all packets consist of L bits, then thetraffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR /aB La /RC Ra /LD LR /a 17.A 2B 1C 0D -118.In the Internet, the equivalentconcept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics 20.End systems access to the Internet through its ( ). A modemsB protocolsC ISPD sockets21.End systems, packet switches,and other pieces of the Internet, run ( ) that control thesending and receiving ofinformation within theInternet.A programsB processesC applicationsD protocols22.There are many private networks,such as many corporate andgovernment networks, whosehosts cannot exchange messages with hosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) runningon its end systems to exchangedata with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionlessunreliable service and ()service.A flowcontrolB connection-oriented reliableC congestion controlD TCP25.It defines the format and theorder of messages exchangedbetween two or morecommunicating entities, as wellas the actions taken on thetransmission and/or receipt ofa message or other event. Thesentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol ( )A the format of messagesexchanged between two or morecommunicating entitiesB the order of messagesexchanged between two or morecommunicating entitiesC the actions taken on thetransmission of a message orother eventD the transmission signals aredigital signals or analogsignals27.In the following options, which is defined in protocol ( )A the actions taken on thetransmission and/or receiptof a message or other event B the objects exchanged between communicating entities C the content in the exchangedmessagesD the location of the hosts28.In the following options, whichdoes not belong to the network edge( )A end systemsB routersC clientsD servers29.In the following options, whichbelongs to the network core ( )A end systemsB routersC clientsD servers30.In the following options, whichis not the bundled with theInternet’sconnection-oriented service( )A reliable data transferB guarantee of thetransmission timeC flow controlD congestion-control31.An application can rely on theconnection to deliver all of itsdata without error and in theproper order. The sentencedescribes ( ). A flow controlB congestion-controlC reliable datatransferD connection-oriented service 32.It makes sure that neither sideof a connection overwhelms theother side by sending too manypackets too fast. The sentence describes ( ). A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internetfrom entering a state of gridlock. When a packet switchbecomes congested, its bufferscan overflow and packet loss canoccur. The sentence describes( ).A flowcontrolB congestion-controlC connection-oriented serviceD reliable data transfer 34.TheInternet ’sconnection-oriented service has aname, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet ’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP( )A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP( )A InternetphoneB video conferencingC streamingmultimediaD telnet39.There are two fundamentalapproaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resourcesneeded along a path to provide for communication between the end system are reserved for theduration of the communicationsession.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’smessages use the resources ondemand, and as a consequence,may have to wait for access tocommunication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, foreach link used by the end-to-endconnection, the connection gets( ) of the link’s bandwidthfor the duration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rateof a circuit is equal to theframe rate multiplied by thenumber of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch mustreceive the entire packetbefore it can begin to transmitthe first bit of the packet ontothe outbound link.A Queuing delayB Store-and-forwardtransmissionC Packet lossD Propagation45.The network that forwardspackets according to host destination addresses is called( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwardspackets according tovirtual-circuit numbers iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, whichis not a kind of access network( )A residentialaccessB company accessC wirelessaccessD local access48.Suppose there is exactly onepacket switch between a sendinghost and a receiving host. The transmission rates between thesending host and the switch and between the switch and the receiving host are R 1 and R 2,respectively. Assuming that theswitch uses store-and-forwardpacket switching, what is thetotal end-to-end delay to senda packet of length L (Ignorequeuing delay, propagationdelay, and processing delay.) ( ) A L /R 1+L /R 2B L /R 1C L /R 2D none of the above49.The time required to examine thepacket ’s header and determinewhere to direct the packet ispart of the ( ). A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagatefrom the beginning of the linkto the next router is ( ). A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of3000bits over a path of 5 links. Eachlink transmits at 1000bps. Queuingdelays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is apacket-switched virtual circuitnetwork. VC setup time is seconds.Suppose the sending layers add atotal of 500 bits of header to eachpacket. How long does it take to sendthe file from source to destination(2).Suppose the network is a packet-switched datagram networkand a connectionless service is used.Now suppose each packet has 200 bitsof header. How long does it take tosend the file(3).Suppose that the network is acircuit-switched network. Furthersuppose that the transmission rate of the circuit between source anddestination is 200bps. Assumingsetup time and 200 bits of header appended to the packet, how longdoes it take to send the packetS olution:(1).t=5*(3000+500)/1000+=( 2).t=5*(3000+200)/1000=16s( 3).t=(3000+200)/200+=。
《计算机网络》期末复习资料
家庭的外貌英语作文My Family's Appearance。
My family is a typical Chinese family with five members. My parents are both in their 50s, and they have three children. I am the youngest one, and my two elder sisters are both married and have their own families.My father is a tall and strong man with a round faceand a pair of big eyes. He has a full head of black hair, which is a little bit curly. He always wears a pair of glasses, which makes him look more intellectual. He likesto wear casual clothes, such as T-shirts and jeans, which are comfortable and easy to move in.My mother is a kind and gentle lady with a slim figure and a beautiful face. She has long black hair, which she always wears in a bun. She has a pair of big eyes, whichare always full of love and warmth. She likes to wear dresses and skirts, which make her look elegant andfeminine.My eldest sister is a tall and slim woman with a cheerful personality. She has a long face and a pair of bright eyes. She has short hair, which she likes to stylein different ways. She likes to wear fashionable clothes, such as high heels and tight dresses, which make her look sexy and confident.My second sister is a short and plump woman with a sweet smile. She has a round face and a pair of cute dimples. She has long hair, which she always wears in a ponytail. She likes to wear casual clothes, such as T-shirts and shorts, which are comfortable and easy to wear.As for me, I am a medium-sized girl with a lively personality. I have a round face and a pair of big eyes. I have long hair, which I like to wear in different styles. I like to wear comfortable clothes, such as T-shirts and jeans, which are easy to move in.In conclusion, my family members have differentappearances, but we all love each other and get along well. We are a happy and harmonious family.。
计算机网络英语期末复习试题及答案

《计算机网络英语》期末复习试题及答案一选择题1.A ( ) protocol is used to move a datagram over an individual link.A application-layerB transport-layerC network-layerD link-layer2.The units of data exchanged by a link-layer protocol are called ( ).A datagramsB framesC segmentsD messages3.Which of the following protocols is not a link-layer protocol? ( )A EthernetB PPPC HDLCD IP4.In the following four descriptions, which one is not correct? ( )A link-layer protocol has the node-to-node job of moving network-layer datagrams over a single link in the path.B The services provided by the link-layer protocols may be different.C A datagram must be handled by the same link-layer protocols on the different links in the path.D The actions taken by a link-layer protocol when sending and receiving frames include error detection, flow control and random access.5.Which of the following services can not offered by a link-layer protocol? ( )A congestion controlB Link AccessC Error controlD Framing6.( ) protocol serves to coordinate the frame transmissions of the many nodes when multiple nodes share a single broadcast link.A ARPB MACC ICMPD DNS7.In the following four descriptions about the adapter, which one is not correct? ( )A The adapter is also called as NIC.B The adapter is a semi-autonomous unit.C The main components of an adapter are bus interface and the link interface.D The adapter can provide all the link-layer services.8.Consider CRC error checking approach, the four bit generator G is 1011, and suppose that the data D is 10101010, then the value of R is( ).A 010B 100C 011D 1109.In the following four descriptions about random access protocol, which one is not correct? ( )A In slotted ALOHA, nodes can transmit at random time.B In pure ALOHA, if a frame experiences a collision, the node will immediately retransmit it with probability p.C The maximum efficiency of a slotted ALOHA is higher than a pure ALOHA.D In CSMA/CD, one node listens to the channel before transmitting.10.In the following descriptions about MAC address, which one is not correct? ( )A The MAC address is the address of one node’s adapter.B No two adapters have the same MAC address.C The MAC address doesn’t change no matter where the adapter goes.D MAC address has a hierarchical structure.11.The ARP protocol can translate ( ) into ( ). ( )A host name, IP addressB host name, MAC addressC IP address, MAC addressD broadcast address, IP address12.The value of Preamble field in Ethernet frame structure is ( )A 10101010 10101010……10101010 11111111B 10101011 10101011……10101011 10101011C 10101010 10101010……10101010 10101011D 10101010 10101010……10101010 1010101013.There are four steps in DHCP, the DHCP server can complete ( ).A DHCP server discoveryB DHCP server offersC DHCP requestD DHCP response14.In CSMA/CD, the adapter waits some time and then returns to sensing the channel. In the following four times, which one is impossible? ( )A 0 bit timesB 512 bit timesC 1024 bit timesD 1028 bit times15.The most common Ethernet technologies are 10BaseT and 100BaseT. “10” and “100”indicate( ).A the maximum length between two adaptersB the minimum length between two adaptersC the transmission rate of the channelD the transmission rate of the node16.The principal components of PPP include but not( ).A framingB physical-control protocolC link-layer protocolD network-layer protocol17.In the following four options, which service can not be provided by switch? ( )A filteringB self-learningC forwardingD optimal routing18.In the following four services, which one was be required in PPP? ( )A packet framingB error detectionC error correctionD multiple types of link19.The ability to determine the interfaces to which a frame should be directed, and then directing the frame to those interfaces is( ).A filteringB forwardingC self-learningD optimal routing20.In ( ) transmission(s), the nodes at both ends of a link may transmit packets at the same time.A full-duplexB half-duplexC single-duplexD both full-duplex and half-duplex21.Consider the data D is 01110010001, if use even parity checking approach, the parity bit is( ①), if use odd parity checking approach, the parity bit is( ②). ( )A ①0 ②1B ①0 ②0C ①1 ②1D ①1 ②022.In the following four descriptions about parity checks, which one is correct? ( )A Single-bit parity can detect all errors.B Single-bit parity can correct one errors.C Two-dimensional parity not only can detect a single bit error, but also can correct that error.D Two-dimensional parity not only can detect any combination of two errors, but also can correct them.23.MAC address is ( ) bits long.A 32B 48C 128D 6424.Wireless LAN using protocol ( ).A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.1125.The following protocols are belonging to multiple access protocols except for ( ).A channel partitioning protocolsB routing protocolsC random access protocolsD taking-turns protocols26.Which of the following is not belonging to channel partitioning protocols? ( )A CSMAB FDMC CDMAD TDM27.In the following four descriptions about CSMA/CD, which one is not correct? ( )A A node listens to the channel before transmitting.B If someone else begins talking at the same time, stop talking.C A transmitting node listens to the channel while it is transmitting.D With CSMA/CD, the collisions can be avoided completely.28.( ) provides a mechanism for nodes to translate IP addresses to link-layer address.A IPB ARPC RARPD DNS29.A MAC address is a ( )address.A physical-layerB application-layerC link-layerD network-layer30.Which of the following is correct? ( )A No two adapters have the same MAC address.B MAC broadcast address is FF-FF-FF-FF-FF-FF.C A portable computer with an Ethernet card always has the same MAC address, no matter where the computer goes.D All of the above31.In the following four descriptions, which one is not correct? ( )A ARP resolves an IP address to a MAC address.B DNS resolves hostnames to IP addresses.C DNS resolves hostnames for hosts anywhere in the Internet.D ARP resolves IP addresses for nodes anywhere in the Internet.32.In the LAN, ( )protocol dynamically assign IP addresses to hosts.A DNSB ARPC DHCPD IP33.DHCP protocol is a four-step process: ①DHCP request. ②DHCP ACK. ③DHCP server discovery. ④DHCP server offer(s). The correct sequence is ( )A ①②③④B ③②①④C ③④①②D ①④③②34.In the Ethernet frame structure, the CRC field is ( )bytes.A 2B 4C 8D 3235.In the Ethernet frame structure, the Data field carries the ( ).A IP datagramB segmentC frameD message36.In the following four descriptions, which one is not correct? ( )A Ethernet uses baseband transmission.B All of the Ethernet technologies provide connection-oriented reliable service to the network layer.C The Ethernet 10Base2 technology uses a thin coaxial cable for the bus.D The Ethernet 10BaseT technology uses a star topology.37.Ethernet’s multiple access protocol is ( ).A CDMAB CSMA/CDC slotted ALOHAD token-passing protocol38.In the following four descriptions about CSMA/CD, which one is not correct? ( )A An adapter may begin to transmit at any time.B An adapter never transmits a frame when it senses that some other adapter is transmitting.C A transmitting adapter aborts its transmission as soon as it detects that another adapter is also transmitting.D An adapter retransmits when it detects a collision.39.Which of the following descriptions about CSMA/CD is correct? ( )A No slots are used.B It uses carrier sensing.C It uses collision detection.D All of the above.40.The Ethernet 10BaseT technology uses( )as its physical media.A fiber opticsB twisted-pair copper wireC coaxial cableD satellite radio channel41.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( )meters.A 100B 200C 500D 1042.A ( )is a physical-layer device that acts on individual bits rather than on frames.A switchB hubC routerD gateway43.A hub is a ( )device that acts on individual bits rather than on frames.A physical-layerB link-layerC network-layerD ransport-layer44.A switch is a( )device that acts on frame.A physical-layerB link-layerC network-layerD transport-layer45.In the following four descriptions, which one is not correct? ( )A Switches can interconnect different LAN technologies.B Hubs can interconnect different LAN technologies.C There is no limit to how large a LAN can be when switches are used to interconnect LAN segments.D There is restriction on the maximum allowable number of nodes in a collision domain when hubs are used to interconnect LAN segments.46.The ability to determine whether a frame should be forwarded to some interface or should just be dropped is ( ).A filteringB forwardingC self-learningD optimal routing47.Which of the following devices is not a plug and play device? ( )A hubB routerC switchD repeater48.Which of the following devices is not cut-through device? ( )A hubB routerC switchD repeater49.In the following four descriptions, which one is not correct? ( )A Switches do not offer any protection against broadcast storms.B Routers provide firewall protection against layer-2 broadcast storms.C Both switches and routers are plug and play devices.D A router is a layer-3 packet switch, a switch is a layer-2 packet switch.50.Which device has the same collision domain? ( )A HubB SwitchC RouterD Bridge51.IEEE802.2 protocol belong to ( )layerA networkB MACC LLCD physical52.IEEE802.11 protocol defines ( )rules.A Ethernet BusB wireless WANC wireless LAND Token Bus53.In data link-layer, which protocol is used to share bandwidth? ( )A SMTPB ICMPC ARPD CSMA/CD54.When two or more nodes on the LAN segments transmit at the same time, there will be a collision and all of the transmitting nodes well enter exponential back-off, that is all of the LAN segments belong to the same( ).A collision domainB switchC bridgeD hub55.( )allows different nodes to transmit simultaneously and yet have their respective receivers correctly receive a sender’s encoded data bits.A CDMAB CSMAC CSMA/CDD CSMA/CA56.Because there are both network-layer addresses (for example, Internet IP addresses) and link-layer addresses (that is, LAN addresses), there is a need to translate between them. Forthe Internet, this is the job of ( ).A RIPB OSPFC ARPD IP57.PPP defines a special control escape byte, ( ). If the flag sequence, 01111110 appears anywhere in the frame, except in the flag field, PPP precedes that instance of the flag pattern with the control escape byte.A 01111110B 01111101C 10011001D 1011111058.The device ( ) can isolate collision domains for each of the LAN segment.A modemB switchC hubD NIC59.In the following four descriptions about PPP, which one is not correct? ( )A PPP is required to detect and correct errors.B PPP is not required to deliver frames to the link receiver in the same order in which they were sent by the link sender.C PPP need only operate over links that have a single sender and a single receiver.D PPP is not required to provide flow control.60.In the PPP data frame, the( ) field tells the PPP receivers the upper-layer protocol to which the received encapsulated data belongs.A flagB controlC protocolD checksum61.PPP’s link-control protocols (LCP) accomplish ( ).A initializing the PPP linkB maintaining the PPP linkC taking down the PPP linkD all of the above62.The PPP link always begins in the ( ) state and ends in the ( ) state. ( )A open, terminatingB open, deadC dead, deadD dead, terminating63.For( ) links that have a single sender at one end of the link and a single receiver at the other end of the link.A point-to-pointB broadcastC multicastD all of the above64.With ( )transmission, the nodes at both ends of a link may transmit packets at the same time.A half-duplexB full-duplexC simplex(单工)D synchronous65.With ( ) transmission, a node can not both transmit and receive at the same time.A half-duplexB full-duplexC simplex(单工)D synchronous66.Which of the following functions can’t be implemented in the NIC? ( )A encapsulation and decapsulationB error detectionC multiple access protocolD routing67.Which of the following four descriptions is wrong? ( )A The bus interface of an adapter is responsible for communication with the adapter’s parent node.B The link interface of an adapter is responsible for implementing the link-layer protocol.C The bus interface may provide error detection, random access functions.D The main components of an adapter are the bus interface and the link interface. 68.For odd parity schemes, which of the following is correct? ( )A 011010001B 111000110C 110101110D 00011011069.( )divides time into time frames and further divides each time frame into N time slots.A FDMB TMDC CDMAD CSMA70.With CDMA, each node is assigned a different ( )A codeB time slotC frequencyD link71.Which of the following four descriptions about random access protocol is not correct? ( )A A transmission node transmits at the full rate of the channelB When a collision happens, each node involved in the collision retransmits at once.C Both slotted ALOHA and CSMA/CD are random access protocols.D With random access protocol, there may be empty slots.72.PPP defines a special control escape byte 01111101. If the data is b1b201111110b3b4b5, the value is( )after byte stuffing.A b1b20111110101111110b3b4b5B b1b20111111001111101b3b4b5C b5b4b30111111001111101b2b1D b5b4b30111110101111110b2b173.MAC address is in ( ) of the computer.A RAMB NICC hard diskD cache74.Which of the following is wrong? ( )A ARP table is configured by a system administratorB ARP table is built automaticallyC ARP table is dynamicD ARP table maps IP addresses to MAC addresses75.NIC works in ( )layer.A physicalB linkC networkD transport76.In LAN, if UTP is used, the common connector is( ).A AUIB BNCC RJ-45D NNI77.The modem’s function(s) is(are) ( ).A translates digital signal into analog signalB translates analog signal into digital signalC both translates analog signal into digital signal and translates digital signal into analog signalD translates one kind of digital signal into another digital signal78.( )defines Token-Ring protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.279.( )defines Token-Bus protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.280.( ) defines CSMA/CD protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.281.The computer network that concentrated in a geographical area, such as in a building or on a university campus, is ( )A a LANB a MANC a WAND the Internet82.The MAC address is ( ) bits long.A 32B 48C 128D 25683.Which of the following four descriptions about MAC addresses is wrong? ( )A a MAC address is burned into the adapter’s ROMB No two adapters have the same addressC An adapter’s MAC address is dynamicD A MAC address is a link-layer address84.Which of the following four descriptions about DHCP is correct? ( )A DHCP is C/S architectureB DHCP uses TCP as its underlying transport protocolC The IP address offered by a DHCP server is valid foreverD The DHCP server will offer the same IP address to a host when the host requests an IP address85.The ( )field permits Ethernet to multiplex network-layer protocols.A preambleB typeC CRCD destination MAC address86.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( ) meters.A 50B 100C 200D 50087.An entry in the switch table contains the following information excepts for ( )A the MAC address of a nodeB the switch interface that leads towards the nodeC the time at which the entry for the node was placed in the tableD the IP address of a node二、阅读理解The central processing unit (CPU) is the heart of the computer systems. Among other things, its configuration determines whether a computer is fast or slow in relation to other computers. The CPU is the most complex computer system component, responsible for directing most of the computer system activities based on the instructions provided. As one computer generation has evolved to the next, the physical size of the CPU has often become smaller and smaller, while its speed and capacity have increased tremendously. Indeed, these changes have resulted in microcomputers that are small enough to fit on your desk or your lap.The CPU comprises the control unit and the arithmetic / logic unit (ALU).The control unit is responsible for directing and coordinating most of the computer systems activities. It determines the movement of electronic signals between main memory and the arithmetic/logic unit, as well as the control signals between the CPU and input/output devices. The ALU performs all the arithmetic and logical (comparison) functions — that is, it adds, subtracts, multiplies, divides, and does comparisons. These comparisons, which are basically “less than”, “greater than”, and “equal to”, can be combined into several common expressions, such as “greater than or equal to”. The objective of most instructions that use comparisons is to determine which instruction should be executed next.Tell whether the following statements are true(T) or false(F) according to the passage A.(根据上文的内容判断下列句子的正误)1. With the development of computer, the physical size of the CPU has often become bigger and bigger. ( )2. The movement of electronic signals between main memory and the ALU as well as the control signal between the CPU and input /output devices are controlled by the control unit of the CPU. ( )3. The CPU comprises the control unit and memory. ( )4. The control unit performs all the arithmetic and logical (comparison) functions5. The central processing unit (CPU) is the heart of the computer systems. ( )三、翻译下面的文章。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
第一章计算机网络概述第二章数据和信号第三章传输介质第四章●What is Encoding? Why must encoding be used for data transmission?(1)【什么是编码?】Convert internal data of a sender into line signals suitable for transmission is called encoding.(2)【数据发送时为什么要编码?】1) Electromagnetic signals in information process devices are not allowed transmitting directly over communication lines.2) The signal type of a device differs from the signal type of a communication line.3) The parameter requirements of device signals differs from the one of line signals.4) Specific requirements in synchronization, efficiency , error control, etc..★Because electromagnetic signals in information process devices are not allowed transmitting directly over communication lines, so encoding must be used for data transmission to converts internal data of a sender into line signals suitable for transmission.2.3.4.机内信号与线路类型不一样;机内信号参数与线路传输的要求不一样;同步、效率、纠错等方面的特殊要求●Which two techniques are used when analog data transmitted by digital signals?Which of them is the most important? Why?用数字信号传输模拟数据常用技术有哪两种?最常用的是?为什么?(1) Pulse Code Modulation(PCM) and Delta Modulation(DM).(2) Pulse Code Modulation(PCM) is the most important.(3) The principal advantage of DM over PCM is the simplicity of its implementation. In general, PCM exhibits better SNR characteristics at the same data rate.●What processes will be involved when analog data are digitized by PCMtechnique?用PCM技术将模拟数据数字化时,要经过哪些处理步骤?Sampling (PAM)---->quantization---->binary encoding---->digital to digital coding●Q4-1 List three techniques of digital-to-digital conversion.●Q4-4 Define baseline wandering and its effect on digital transmission.(1)In decoding a digital signal, the receiver calculates a running average of the received signal power. This average is called the baseline.(2)The incoming signal power is evaluated against this baseline to determine the value of the data element.(3)A long string of 0s or 1s can cause a drift in the baseline (baseline wandering) and make it difficult for the receiver to decode correctly.●Q4-5 Define a DC component and its effect on digital transmission.(Define) When the voltage level in a digital signal is constant for a while, the specturm creates very low frequencies(results of Fourier analysis). These frequences around zero,called DC(derect-current) components, that present problems for a system that can not pass low frequencies or a system that uses electrical coupling.(Effect) DC component means 0/1 parity that can cause base-line wondering. 直流分量的影响不仅仅是基线偏移,还有更重要的原因。
看看教材和课件,或看看原书作业答案。
第五章●Which modulation techniques are used in analog transmission? Which of themis the most susceptible to noise? Which of them is the mechanism commonly used in all modern modems.1.Amplitude shift keying ( ASK)Frequency shift keying ( FSK )Phase shift keying ( PSK)Quadrature Amplitude Modulation(QAM)2.The most susceptible to noise of the four digital-to-analog conversion techniques is ASK.3.The mechanism commonly used in all modern modems of them is QAM.●Q5-1 Define analog transmission.●Q5-2 Define carrier signal and explain its role in analog transmission.(Define) A sender produces an analog signal as fundamental wave to carry digital signals. The fundamental wave is called carrier signal.(explain) Digital data are converted into modulated signals through changing one or more of three characteristics of a carrier signal: amplitude, frequency and phase.Most familiar application is for transmitting digital data through the public telephone network via a modem.(A carrier is a single-frequency signal that has one if its characteristic (amplitude, frequency, or phase) changed to represent the baseband signal.【In analog transmission, the sending device produces a high frequency analog signal that acts as a base for the information signals (data). The base signal is called the carrier signal. It is to represent the baseband signal.】)●Q5-3 Definne digital-to-analog conversion.Digital-to-analog conversion is the process of changing one of the characteristics of an analog signal based on the information in digital data. It is also called modulation of a digital signal. The baseband digital signal representing the digital data modulations the carrier to create a broadband analog signal.●Q5-4 Which of characteristics of an analog signal are changed to represent thedigital signal in each of the following digital-analog conversions?a.ASK changes the amplitude of the carrier.b.FSK changes the frequency of the carrier.c.PSK changes the phase of the carrier.d.QAM changes both the amplitude and phase of the carrier.QAM is the most efficient of these options and is the mechanism commonly used in all modern modems.●Q5-5 Which of the four digital-to-analog conversion techniques(ASK,FSK,PSKor QAM) is the most susceptible to noise?Defend your answer.(Answer) The most susceptible to noise of the four digital-to-analog conversion techniques is ASK.(Define) Noise usually affects the amplitude; therefore, ASK is the modulation technique most affected by noise than phase or frequency.第六章●Which of the four multiplexing techniques is (are) suitable for analog channels?Which of them is (are) suitable for digital channels? (See P181 Questions Q6-3) Frequency-division and wavelength-division multiplexing are suitable for analogchannelsSynchronous time-division multiplexing and asynchronous time-divisionmultiplexing are suitable for digital channels.●Which of the four multiplexing techniques is (are) suitable for electricallinks? Which of them is (are) suitable for optical links?Frequency-division , Synchronous time-division and asynchronous time-division multiplexingare suitable forelectrical links .Wavelength-division multiplexing is suitable for optical links.光传输信道都属于模拟信道,而时分复用只适用于数字信道。
