电子科技大学2015年硕士研究生密码学基础与网络安全考研真题_电子科技大学专业课真题
电子科技大学2015年《825密码学基础与网络安全》考研专业课真题试卷
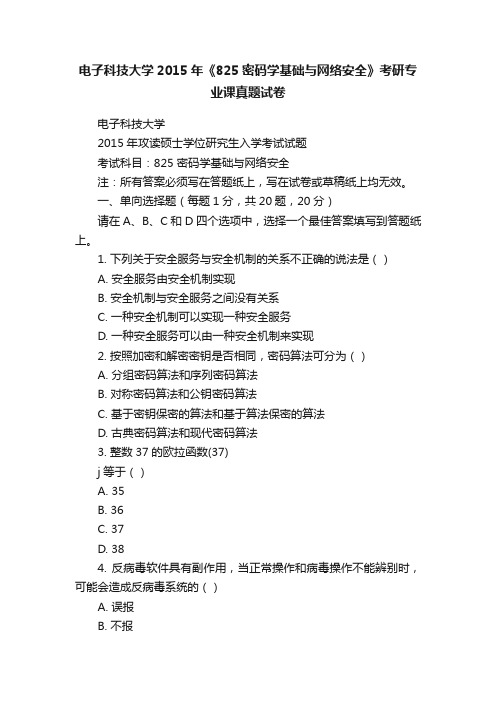
电子科技大学2015年《825密码学基础与网络安全》考研专业课真题试卷电子科技大学2015年攻读硕士学位研究生入学考试试题考试科目:825 密码学基础与网络安全注:所有答案必须写在答题纸上,写在试卷或草稿纸上均无效。
一、单向选择题(每题1分,共20题,20分)请在A、B、C和D四个选项中,选择一个最佳答案填写到答题纸上。
1. 下列关于安全服务与安全机制的关系不正确的说法是()A. 安全服务由安全机制实现B. 安全机制与安全服务之间没有关系C. 一种安全机制可以实现一种安全服务D. 一种安全服务可以由一种安全机制来实现2. 按照加密和解密密钥是否相同,密码算法可分为()A. 分组密码算法和序列密码算法B. 对称密码算法和公钥密码算法C. 基于密钥保密的算法和基于算法保密的算法D. 古典密码算法和现代密码算法3. 整数37的欧拉函数(37)j等于()A. 35B. 36C. 37D. 384. 反病毒软件具有副作用,当正常操作和病毒操作不能辨别时,可能会造成反病毒系统的()A. 误报B. 不报C. 漏报D. 错报5. 7804的后三位数字是()A. 400B. 401C. 402D. 4036. 以下关于美国国防部所提出的PDRR网络安全模型说法正确的是()A. 安全策略(Policy)是PDRR的重要内容B. 依据PDRR模型,增加系统的保护时间可提高系统的安全性C. 依据PDRR模型,增加系统的检测时间可提高系统的安全性D. 依据PDRR模型,应该尽量增加系统暴露时间来提高系统的安全性7. 以下说法不正确的是()A. 非对称加密算法较好地解决了密钥管理问题B. TCP/IP协议在设计之初并未考虑网络安全威胁C. 网络隔离技术不能减少对信息系统的安全威胁D. 安全协议需要使用某种密码算法且须实现一项或多项安全功能8. 下列关于网络地址转换(NAT)正确的说法是()A. NAT与防火墙能协同工作,但与VPN不能协同工作B. NAT与VPN能协同工作,但与防火墙不能协同工作C. NAT与防火墙能协同工作D. NAT与VPN不能协同工作9. 下列关于数字签名说法正确的是()A. 数字签名是不可信的B. 数字签名容易被伪造C. 数字签名容易抵赖D. 数字签名不可改变10. 一般来说,以下哪个不属于设备物理安全的内容()A. 设备防盗B. 设备防毁共7 页第1页。
621英语水平测试-电子科技大学2015硕士入学考试真题
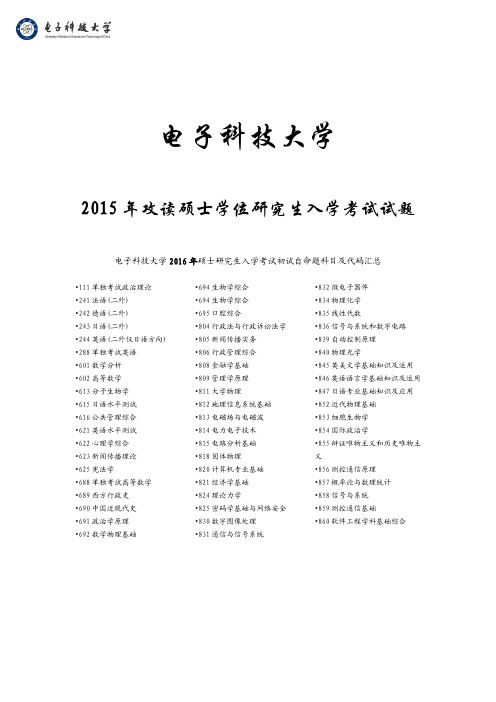
电子科技大学2015年攻读硕士学位研究生入学考试试题电子科技大学2016年硕士研究生入学考试初试自命题科目及代码汇总•111单独考试政治理论•241法语(二外)•242德语(二外)•243日语(二外)•244英语(二外仅日语方向) •288单独考试英语•601数学分析•602高等数学•613分子生物学•615日语水平测试•616公共管理综合•621英语水平测试•622心理学综合•623新闻传播理论•625宪法学•688单独考试高等数学•689西方行政史•690中国近现代史•691政治学原理•692数学物理基础•694生物学综合•694生物学综合•695口腔综合•804行政法与行政诉讼法学•805新闻传播实务•806行政管理综合•808金融学基础•809管理学原理•811大学物理•812地理信息系统基础•813电磁场与电磁波•814电力电子技术•815电路分析基础•818固体物理•820计算机专业基础•821经济学基础•824理论力学•825密码学基础与网络安全•830数字图像处理•831通信与信号系统•832微电子器件•834物理化学•835线性代数•836信号与系统和数字电路•839自动控制原理•840物理光学•845英美文学基础知识及运用•846英语语言学基础知识及运用•847日语专业基础知识及应用•852近代物理基础•853细胞生物学•854国际政治学•855辩证唯物主义和历史唯物主义•856测控通信原理•857概率论与数理统计•858信号与系统•859测控通信基础•860软件工程学科基础综合电子科技大学2015年攻读硕士学位研究生入学考试试题考试科目:621英语水平测试注:无机读卡,所有答案必须写在答题纸上,写在试卷或草稿纸上无效。
Part I Reading Comprehension (40 points)Directions: In this part there are 5 passages, each with some questions or incomplete statements. Read them carefully and then choose from the four suggested answers marked A, B, C and D to answer the questions or complete the statements. Please write your answers on the Answer Sheet.Passage 1Oh no, not Anthony Weiner again.The older generation never gets it. Anthony Weiner, a candidate for mayor of New York, admitted this week to having sent more snaps of himself to a digital acquaintance. As any youngster could have told him, the way to find love is to send photos of your face.Consider Will, a 24-year-old up-and-coming film director in California. He meets potential dates via a smartphone app called Tinder. It finds potential matches who are nearby—your phone always knows where you are—and shows him photos from their Facebook profiles. Will can like or reject each photo. If a woman he likes also likes him, both are alerted and can start chatting.Tinder is quick (you can scroll through dozens of photos in minutes) and spares your blushes (you never know if someone rejects you). Will has already had three romantic encounters and hundreds of matches, he says. Justin Mateen, a co-founder of Tinder, says it has made 100m matches since its launch in September, and led to 50 marriage proposals. He adds: “The app has only really been going for nine months. There could be a baby popping out soon.”Americans are dating longer, which creates opportunities for matchmakers. Some are quite direct.Bang with Friends (BWF), another app, allows users to specify which of their Facebook friends they would like to spend the night with. If both parties feel the same way, BWF notifies them. If not, no one is any the wiser. BWF was booted from Apple’s app store, but that hasn’t stopped it from creating 200,000 pairings since its January launch. BWF’s boss, admits he came up with the concept while “a bit tipsy”.Such apps make it easier to find potential partners, but don’t seem to have turned America into a nation of bed-hoppers. Young women claim to have had a median of 3.6 male intimate friends while young men 6.1 female ones. These figures may be inaccurate—men may exaggerate; women may undercount—but they have not changed much in years.Parents fret that staring at screens all day has made youngsters socially inept face-to-face. A第1 页共12 页survey by two dating sites found that 36-38% of Americans aged 21-34 ask for dates by text message. But when they meet, they must still make their moves in person. Witty joking and a well-placed wink still have their uses.1. It can be summarized from the first three paragraphs that _________.A. we used to judge a potential match by his or her appearanceB. one can find love by sending his photos to a digital acquaintanceC. Anthony Weiner is trying to win more votes from digital friendsD. Tinder will probably replace traditional matchmakers worldwide2. The sixth paragraph is focused on _________.A. the huge success that BWF has achievedB. the serious consequence of digital datingC. the evolution of matchmaking in the U.S.D. the future developments of Facebook3. The last paragraph implies that _________.A. excessive use of apps leaves youngsters socially awkwardB. most young people find love through text messagesC. people in love often move their homes before marriageD. verbal or non-verbal language is still used during dates4. Potential matches found by Tinder are probably _________.A. young, single, and nearbyB. poor, married, but lonelyC. illiterate, retired, but divorcedD. far-away, busy, and happyPassage 2The human body contains enormous quantities of energy. In fact, the average adult has as much energy stored in fat as a one-ton battery. That energy fuels our everyday activities, but what if those actions could in turn run the electronic devices we rely on? Today, innovators around the world are banking on our potential to do just that.Movement produces kinetic energy, which can be converted into power. In the past, devices that turned human kinetic energy into electricity, such as hand-cranked radios, computers and flashlights, involved a person’s full participation. But a growing field is tapping into our energy without our even noticing it.Consider, for example, a health club. With every step you take on a treadmill and with every muscle curl, you turn surplus calories into motion that could drive a generator and produce electricity. The energy from one person’s workout may not be much, but 100 people could contribute significantly to a facility’s power needs.That’s the idea behind the Green Microgym in Portland, Oregon, where machines likes tationary bikes harvest energy during workouts. Pedaling turns a generator, producing electricity that helps to power the building. For now, body energy supplies only a small fraction of the gym’s needs, but the amount should increase as more machines are adapted. “By being extremely energy-efficient and combining human power, solar and someday wind, I believe we’ll be able to be net-zero for electricity sometime this year,” says the gym’s owner, Adam Boesel. His bikes, by the way, aren’t the flirts to put pedal power to work. In some parts of the world, cyclists have been powering safety第2 页共12 页lights for years with devices called bicycle dynamos, which use a generator to create alternating current with every turn of the wheels.Dance clubs are also getting in on the action. In the Netherlands, Rotterdam’s new Club WATT has a floor that harnesses the energy created by the dancers’ steps. For now, it’s just enough to power LED lights in the floor, but in the future, more output is expected from newer technology.5. Using human body energy as power supplies _________.A. requires us to be strongB. is a great new ideaC. proves to be difficultD. is increasingly popular6. It can be learned that the Green Microgym _________.A. is using human, solar and wind power to produce electricityB. is the first to use bikes to harvest human body energyC. will be able to satisfy its power needs by using green energyD. will introduce the technology to other parts of the world7. What is the author’s most likely comment on the application of body energy?A. It is unrealistic at present.B. It has a promising future.C. Its effect is still unknown.D. It depends on the energy cost.Passage 3The first of Laurence Smith’s two weddings was meant to take place in the midwinter snow not far south of the Arctic Circle. The second foresaw balmy blue skies in Palm Springs, California. As it turned out, the guests were greeted by rain and slush in the far north, then by a chill and more rain in the Californian desert.If the weather is capable of surprising him, why should anyone trust Mr. Smith’s forecast for 2050? Because the growing freakiness of weather is precisely his point. Climate change is one of four mega-trends, along with globalization, population growth and surging demand for natural resources, that he thinks will shape the world over the coming decades. The first part of his book The New North: The World in 2050 is a familiar tale of teeming cities, roaring trade, harder-to-get-at oil and rising sea levels.But Mr. Smith comes into his own when he explores the consequences of these trends (climate change especially) for the quarter of the Earth that lies at latitudes above 45°N. A geographer at the University of California, Los Angeles, he specializes in the frozen lands of Russia, Canada, Alaska and Iceland. The region is about to undergo a great transformation.The planet’s warming may be global, but climate-change models predict it will be amplified in the north. Permafrost will melt and settlement patterns will change. Inland, construction will become trickier and ice roads less dependable, so development will gravitate to the coasts. By mid-century the Arctic Ocean may be briefly free of sea ice in September, a boon to shipping. Crops will spread north as seal hunters become farmers.Interest in the region’s vast and increasingly accessible natural resources is already growing, along with the potential for conflict over the rights to these riches. Mr. Smith believes there is every chance that the development of the “new north” will be peaceful, thanks to habits of cooperation and第3 页共12 页an internationally accepted rule book for laying down rights to the seabed. He sees a leading role for the region’s indigenous peoples.By 2050 the answers to some very big questions should be clear: what happens to the north’s massive stocks of carbon in the soil as it defrosts; whether great schemes to channel freshwater from north to south are attempted; how populous, resource-hungry China works with Russia’s emptying, resource-rich Far East. Mr. Smith reckons an area about one and a half times the size of the United States will be habitable, albeit for much of the year still cold and dark. The development of the new north, he thinks, might resemble that of the American West, dotted with settlements formed for mining and trade.Obscuring the view of 2050, however, is a caveat that looms as large as an Arctic iceberg. Mr. Smith sets ground rules that allow him to extrapolate into the future without worrying about disruptions such as game-changing leaps in technology. This is an “informed thought-experiment”rather than a proper prediction. But for anyone curious about the new north—let alone thinking of investing in Arctic derivatives—it is an instructive exercise.8. The word “boon” in the fourth paragraph can be replaced by _________.A. prohibitionB. prosperityC. benefitD. catastrophe9. According to Laurence Smith, the following are all very likely to happen in the future decadesEXCEPT _________.A. The local people in the “new north” will benefit from the climate changeB. The development of the “new north” will be on a peaceful processC. The natural resources in the “new north” will be able to exploitedD. The large amounts of carbon in the “new north” soils will be safely controlled10. What can be inferred from the passage?A. The author takes a skeptical attitude towards Laurence Smith’s predictions of the Arctic.B. The author reckons Laurence Smith is somewhat optimistic in imagining the “new north”C. Laurence Smith did a lot of experiments in combining geographical predictions andeconomic development.D. Laurence Smith shares with the author that the future of the Article depends on ourawareness and actions.11. Which of the following titles is more appropriate for the passage?A. The Arctic: The de-icing ageB. Climate Change: Humankind’s futureC. A Day Dreamer: Laurence Smith’s new writing styleD. 2050: The end of the worldPassage 4The newspaper must provide for the reader the facts, unalloyed, unslanted, objectively selected facts. But in these days of complex news it must provide more; it must supply interpretation, the meaning of the facts. This is the most important assignment confronting American journalism—to make clear to the reader the problems of the day, to make international news as understandable as第4 页共12 页community news, to recognize that there is no longer any such thing (with the possible exception of such scribbling as society and club news) as “local”news, because any event in the international area has a local reaction in manpower draft, in economic strain, in terms, indeed, of our very way of life.There is in journalism a widespread view that when you embark on interpretation, you are entering choppy and dangerous waters, the swirling tides of opinion. This is nonsense.The opponents of interpretation insist that the writer and the editor shall confine himself to the “facts”. This insistence raises two questions: What are the facts? And: Are the bare facts enough?As to the first query. Consider how a so-called “factual” story cones about. The reporter collects, say, fifty facts; out of these fifty, his space allotment being necessarily restricted, he selects the ten, which he considers most important. This is Judgment Number One. Then he or his editor decides which of these ten facts shall constitute the lead of the piece. This is important decision because many readers do not proceed beyond the first paragraph. This is Judgment Number Two. Then the night editor determines whether the article shall be presented on page one, where it has a large impact, or on page twenty-four, where it has little. Judgment Number Three.Thus, in the presentation of a so-called “factual” or “objective” story, at least three judgments are involved. And they are judgments not at all unlike those involved in interpretation, in which reporter and editor, calling upon their general background, and their “news neutralism,” arrive at a conclusion as to the significance of the news.The two areas of judgment, presentation of the news and its interpretation, are both objective rather then subjective processes—as objective, that is, as any human being can be. (Note in passing: even though complete objectivity can never be achieved, nevertheless the ideal must always be the beacon on the murky news channels.) Of an editor is intent on slanting the news, he can do it in other ways and more effectively than by interpretation. He can do it by the selection of those facts that prop up his particular plea. Or he can do it by the pay he gives a story—promoting it to page one or demoting it to page thirty.12. The title that best expresses the ideas of this passage is _________.A. Interpreting the News.B. Choosing Facts.C. Subjective versus Objective Processes.D. Everything Counts.13. Why does the writer of an article select ten out of fifty available facts?A. His editor is prejudiced.B. Space is limited.C. The subject is not important.D. The newspaper is arbitrary.14. What is the least effective way of “slanting” news?A. Placement.B. Concentration.C. InterpretationD. His editor is prejudiced.15. Why should the lead sentence present the most important fact?A. It will influence the reader to continue.B. It will be the best way to write.C. Some readers do not read beyond the first paragraph.D. It will gratify the editor.第5 页共12 页Passage 5One of the most pivotal moments in American literature occurred near the end of the nineteenth century as authors such as a young man named Stephen Crane began to embrace a literary style forged in Europe a bit earlier and which would come to be known as naturalism. Crane was born to parents in the ministry and grew up in a household grounded in religious beliefs and context. Yet, before long, Crane had, for the most part, rejected religion and the idea of divine intervention in favor of a more hands-on approach to the world. As he began to develop as a writer, naturalist themes of man versus nature, the unrelenting power of nature, and an objective view of the world began to dominate his writing. Naturalists attempted to depict the most accurate view of life unadulterated and unobstructed by external commentary or spiritual intervention. Ultimately Crane’s masterful short story The Open Boat stands as one of the most complete and developed works of the naturalist genre.The first apparent element of naturalism in The Open Boat is its subject matter—a shipwreck. Being as true to life as possible is one of the most common goals of a naturalistic writer, and, in this short story, Crane is no exception. It did not come from Crane’s imagination. Rather, it stemmed from his personal experience. As a young war reporter, Crane was on his way from Florida to Cuba when his vesse1, the Commodore, encountered a violent tempest. Within hours, the ship had sunk, leaving a few lucky survivors on a tiny lifeboat to be subjected to the full of nature. Throughout the story Crane depicts scene after scene as if they were snapshots or a shorn film of what the men in the boat were up against. Through his prose, Crane is able to reveal the unadulterated brutal realism manifest in nature itself.As Crane continues with the theme of man versus nature in The Open Boat, the element of pessimism crucial to any naturalistic work, becomes quite apparent. The men are at the mercy of the storms and the seas and cannot do much to save themselves. In this sense, Crane reveals the indifference of nature and the universe in relation to the life or plight of human beings in general. It’s obvious to him that angels will not swoop down and save the unfortunate men. The situation of the shipwreck is ideal because ordinary, everyday people must face an extreme situation from which it is more than likely that they will perish. Crane continually creates a mood of impending doom and the punishing nature of the universe throughout the story. Along the way, he provides little commentary on the situation, forcing readers to place themselves immediately on the boat with the men while enforcing the dark tone of the story. But, even to Crane and most naturalist writers, all is not lost.While Crane’s work The Open Boat is a dark account of a chance situation that turns fatal for many, but not all, of the crew of the Commodore, it also sets forth the main elements of a naturalistic literary work at the turn of the twentieth century. Despite the fact that nature can be unrelenting and compassionless towards humans at any given moment, Crane ultimately shows how individuals still always have the capacity to strive together to overcome hardships and disaster. Furthermore, the accuracy and detail by Crane shun any possibility of a sugarcoated reality and reveals the true ferocity of nature as it is.16. Which of the following can be inferred from the first paragraph about Stephen Crane?第6 页共12 页A. He enjoyed the ministry and listening to preachers.B. He did not enjoy writing when he was young.C. He was rivaled by no other author of his time.D. He was not in tune with the beliefs of his parents.17. Which of the sentences below best expresses the essential information in the underlinedsentence in the first paragraph?A. Naturalists liked to place their own opinions on spirituality in their writing.B. Naturalists placed more emphasis on representing life as it appeared to them.C. Naturalists tried to embody the most precise view of life by looking to religion.D. Naturalists believed the life was obstructed by outside ambition and spirituality.18. According to the second paragraph, The Open Boat is important as a naturalist work because_________.A. it is true account taken from Crane’s own personal experienceB. the story is completely fabricated from Crane’s imaginationC. it is based on a series of events in a shipwreck that Crane heard ofD. it does not attempt to glorify Crane’s heroism against nature19. The author discusses nature in the third paragraph in order to _________.A. show how Crane believes divine power will save humanityB. note that nature itself is stronger than all of humankindC. indicate that nature does not care for strife among peopleD. reveal how it is pessimistic toward life on Earth20. According to the fourth paragraph, the men in the boat are significant because _________.A. they show that by banding together, human beings can surviveB. they represent the ultimate downfall of life according to CraneC. they allow fate to run its course and decide their own futureD. they discount nature and do not take it seriously until the endPart II Structure and Vocabulary (20 points)Directions: Beneath each of the following sentences, there are four choices marked A, B, C and D. Choose the one that best completes the sentence. Please write your answers on the Answer Sheet.21. The general manager usually _________ a question before he gives his answer.A. pondersB. extractsC. imploresD. enlists22. His classmates dislike him for his _________ as he always boasts about his family.A. reclusionB. pomposityC. prideD. austerity23. The writer told several _________ about his colleagues and made everybody laugh.A. legendsB. mythsC. fablesD. anecdotes24. She must have been pretty _____ to fall for such an old trick.A. interestedB. gullibleC. enthusiasticD. shrewd25. This is the ______ piano on which the composer created some of his greatest works.A. trueB. originalC. realD. genuine第7 页共12 页26. A lack of appetite may be ________ of a major mental or physical disorder.A. inquisitiveB. initiativeC. indicativeD. informative27. The self-image controls a person’s attitudes or _________ of what happens to her.A. interpretationsB. approachesC. commitmentsD. simulations28. By the year 2040, Yale University will need over eight acres of land to _________ its library.A. manipulateB. accommodateC. illuminateD. obligate29. If you don’t know where you’ re going in life, you are _________ to wind up somewhere else.A. possibleB. inevitableC. optionalD. liable30. As far as marriage is concerned, it is mutual care and love that _________.A. mountsB. discountsC. countsD. calculates31. If the ten amendments that _________ the Bill of Rights of the US Constitution were a familyof ten children, you wouldn’t want to be the Third.A. includeB. embraceC. compriseD. involve32. The person in custody must, prior to interrogation, be clearly informed that he has the right toremain _________.A. silentB. taciturnC. speechlessD. consent33. The road wound rather _________ into a valley, in which the Pemberley House was situated.A. unprecedentedlyB. abruptlyC. promptlyD. irreversibly34. There is some reason for not giving up my career and _________ a different one.A. taking inB. bringing aboutC. arising fromD. embarking on35. Their house was in close _________ to ours, so we became intimate friends in time.A. vicinityB. contactC. relationD. community36. What all this _________ rhetoric obscured was the lack of hard evidence that violent mediaactually turns children into killers.A. multiculturalB. innovativeC. hyperbolicD. interactive37. A(n) _________ reading approach to reading is a combination of approaches—global, analyticand synthetic—used to suit the convenience of the reader.A. literalB. innovativeC. liberalD. eclectic38. _________ with languages gives you an edge in many jobs and professional opportunities, butis especially valuable in fields such as advertising, business, education and foreign affairs.A. ThresholdB. FacilityC. SpecializationD. Accommodation39. Rather than dictate how I think it ought to work, I would tell my employees to _________something that will work.A. get back toB. get out ofC. come along withD. come up with40. The visitors were impressed by the facilities planned and programmed ________ theirinterrelationships.A. in terms ofB. in aspects ofC. in units ofD. in case ofPart III Cloze (20 points)Directions: Fill in each blank with ONE appropriate word to complete the passage. Please write your answers on the Answer Sheet.第8 页共12 页Passage A:A new report published on November 4th takes a different approach.GlobalWebIndex (GWI), a market-research firm 41 local partners in 32 countries, surveys 170,000 consumers a year and recently began to ask detailed questions about internet use. It 42 China and India in the top three for Facebook users. SimilarWeb, 43 does IP-based analysis, does not even put China in the top ten.One reason for the 44 is that in many developing markets devices are widely shared. Conversely, more than three-quarters of respondents in the GWI report said they used more than one 45 . 46 factor is the spread of virtual private networks (VPNs) and proxy servers, which 47 it possible to surf the web through a foreign server.Once restricted to the tech-literate, these are now common and easy to use. Chinese citizens who want to vault the Great Firewall to use Facebook can do so with a couple of clicks. Foreign fans of the BBC can use the 48 trick to watch its programs via iPlayer, supposedly barred 49 Britain. Since VPNs and proxy servers are clustered in 50 with favorable rules, such as Sweden and the Netherlands, any count of visits to such sites will be skewed. 41. ____________42. ____________43. ____________44. ____________45. ____________46. ____________47. ____________48. ____________49. ____________50. ____________Passage B:Happy hours are not necessarily happy, 51 do they last for an hour, but they have become a part of the ritual of the office worker and businessman.52 weekdays in pubs and bars throughout America, there is the late afternoon happy hour. The time may 53 from place to place, but usually it is held from four to seven. 54 the workday is finished, office workers in large cities and small towns take a relaxing pause and do not go directly home. They head off 55 for the nearest bar or pub to be with friends, co-workers and colleagues. Within minutes the pub is filled to capacity 56 businessmen and secretaries, office clerks and stock executives. They gather 57 the bar like birds around a fountain or forest animals around a watering hole and chat about the trifles of office life or matters more personal. This is their desert garden, the place to relieve the day’s stress at the office.At these happy hours, social binding occurs 58 people who share the same workplace or similar professions. They may chat about each other or talk about a planned project that has 59 to meet a deadline. In this 60 , these places become extensions of the workplace and constitute a good portion of one’s social life. 51. ____________52. ____________53. ____________54. ____________55. ____________56. ____________57. ____________58. ____________59. ____________60. ____________第9 页共12 页Part IV Paraphrasing (20 points)Directions: Paraphrase the underlined parts. Please write your answers on the Answer Sheet.Consult any encyclopedia and you will find Charles Babbage credited with having conceived the first automatic digital computer. (61) Dig deeper, however, and it quickly becomes apparent that Babbage had a lot of help.Others before him had already tried to build calculating contraptions, notably Gottfried Leibniz, a German mathematician. (62) Babbage held regular salons and founded clubs where his ideas were sharpened. And there was also Ada Lovelace, his collaborator and the world’s first computer programmer.The argument against the great man theory of invention is not new. (63) But the main merit of Walter Isaacson’s new book The Innovators is to show that this is particularly true in information technology—despite the customary lionization of many of its pioneers, from Babbage and Alan Turing to Bill Gates and Linus Torvalds.All appear in Mr. Isaacson’s book, which explains its length. Whether their worlds revolved around the computer itself, the microchip, software, the PC, the internet or everything in between—these are all stories that show that invention always has many fathers (and mothers). (64) In fact, those who tried to go it alone tended to fail.(65) Mr. Isaacson thinks geniuses are important but they have to be seen in the context of times they lived in and the people they collaborated with. John von Neumann was a Hungarian-born polymath who worked on the ENIAC, one of the first programmable machines. His name is associated by many with early advances in programming and software architecture. (66) But it was a group of women who were at the forefront of programming, because back then it often involved plugging in wires and throwing switches. “If the ENIAC’s administrators had known how crucial programming would be…they might have been more hesitant to give such an important role to women,” he quotes one of them, Jean Jennings, as saying.(67) The ENIAC also shines a light on another issue: how innovation should best be commercialized. In 1945 von Neumann published a paper summarizing the project’s ideas—making it impossible for others on the team to patent them. The debate over whether innovation is better served by sharing intellectual property or by protecting it has been heated.(68) Mr. Isaacson clearly thinks that innovation is all about getting the mix right, though he doesn’t put it quite that way. If a brilliant leader is too self-involved, as was the case with William Shockley, an American physicist who helped invent the transistor radio, things fall apart. (69) Similarly, teams that lack a willful visionary often falter, as happened after Steve Jobs left Apple. Groups with a wide variety of specialities and experiences do much better than a bunch of left-brainers.The Innovators has not quite lived up to its own advice of getting the mix right. (70) Mr. Isaacson could have dedicated more pages to what he calls “lessons from the journey”, rather than retelling at length stories that other books have already laid out, even if he does give them credit. Then again, just like great technology, a good book doesn’t just emerge from nowhere.第10 页共12 页。
813电磁场与电磁波-电子科技大学2015硕士入学考试真题

电子科技大学2015年攻读硕士学位研究生入学考试试题电子科技大学2016年硕士研究生入学考试初试自命题科目及代码汇总•111单独考试政治理论•241法语(二外)•242德语(二外)•243日语(二外)•244英语(二外仅日语方向) •288单独考试英语•601数学分析•602高等数学•613分子生物学•615日语水平测试•616公共管理综合•621英语水平测试•622心理学综合•623新闻传播理论•625宪法学•688单独考试高等数学•689西方行政史•690中国近现代史•691政治学原理•692数学物理基础•694生物学综合•694生物学综合•695口腔综合•804行政法与行政诉讼法学•805新闻传播实务•806行政管理综合•808金融学基础•809管理学原理•811大学物理•812地理信息系统基础•813电磁场与电磁波•814电力电子技术•815电路分析基础•818固体物理•820计算机专业基础•821经济学基础•824理论力学•825密码学基础与网络安全•830数字图像处理•831通信与信号系统•832微电子器件•834物理化学•835线性代数•836信号与系统和数字电路•839自动控制原理•840物理光学•845英美文学基础知识及运用•846英语语言学基础知识及运用•847日语专业基础知识及应用•852近代物理基础•853细胞生物学•854国际政治学•855辩证唯物主义和历史唯物主义•856测控通信原理•857概率论与数理统计•858信号与系统•859测控通信基础•860软件工程学科基础综合“电磁场与电磁波”试题 共 3 页 第 1 页电子科技大学2015年攻读硕士学位研究生入学考试试题考试科目:813 电磁场与电磁波注:所有答案必须写在答题纸上,做在试卷或草稿纸上无效。
一、填空题(每空2分,共30分)1. 在介电常数02.5e e =的电介质中,已知电场强度23V/m x y z E e x e y e z =++r r r r,则介质中的自由电荷体密度为r = 3C /m 、极化(束缚)电荷体密度为p r = 3C /m 。
电子科技大学(成都)考研历年真题之825密码学基础与网络安全2008--2015年考研真题
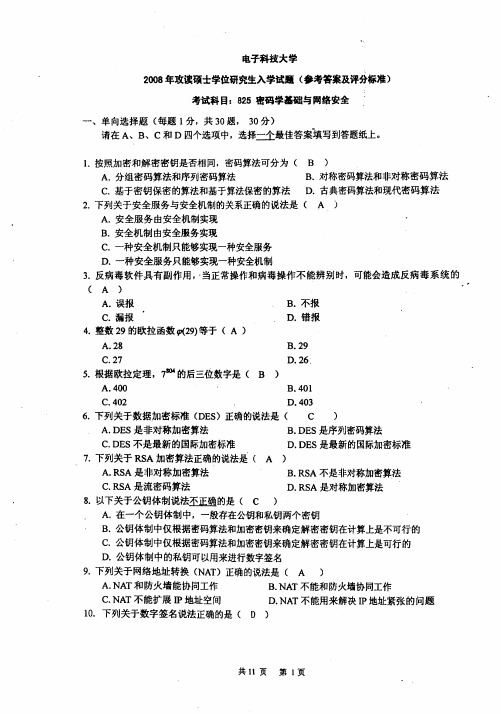
共6 页
第 1页
C. UNIX 文件系统提供了基于组(group)的安全保护机制 D. UNIX 文件系统提供了基于进程和线程的安全保护机制 8. 以下关于入侵检测系统(IDS)的说法正确的是( ) A. 入侵检测系统可分为主机入侵检测系统和网络入侵检测系统 B. 入侵检测系统只能够检测已知攻击 C. 入侵检测系统不能够提供日志功能 D. 网络入侵检测系统(NIDS)不能够保护一个局域网 9. 根据 2013 年 9 月最高人民法院和最高人民检察院关于网络谣言刑案的司法解释, 以下说法 不正确的是( ) A. 捏造损害他人名誉的事实,在信息网络上散布,或者组织、指使人员在信息网络上散 布的行为属于刑法所规定的“捏造事实诽谤他人” 。 B. 将信息网络上涉及他人的原始信息内容篡改为损害他人名誉的事实,在信息网络上散 布,或者组织、指使人员在信息网络上散布的行为属于刑法所规定的“捏造事实诽谤他人” 。 C. 同一诽谤信息实际被点击、浏览次数达到五千次以上,或者被转发次数达到五百次以 上的行为属于刑法所规定的“捏造事实诽谤他人”且属于“严重危害社会秩序和国家利益” 。 D. 利用信息网络诽谤他人,且引发公共秩序混乱的,应当认定为刑法规定的“严重危害 社会秩序和国家利益” 。 10. 以下哪项不属于物理安全威胁?( ) A. 自然灾害 B. 物理攻击 C. 硬件故障 D. 系统安全管理人员培训不够 11. 以下关于身份认证的说法不正确是( ) A. 身份认证是验证者获得对声称者所声称的事实的信任 B. 身份认证有单向和双向认证之分,但一般不能重复两次单向认证来实现双向认证 C. 密码技术和非密码技术都可以用来实现身份认证 D. 只有密码技术才能够用来实现身份认证 12. 关于域(field)的说法正确是( ) A. 域必须满足加法的分配率 B. 域必须满足乘法的分配率 C. 在域中每个元素都有一个加法逆元 D. 在域中每个元素都有一个乘法逆元 13. 以下关于地址解析协议(ARP)说法不正确的是( ) A. 地址解析协议用于 IP 地址和 MAC 地址的解析 B. 地址解析协议包括 ARP 请求和 ARP 应答两种类型的包 C. 由于 ARP 请求是定向传送,所以存在 ARP 欺骗攻击的安全威胁 D. 通过添加静态 ARP 表项到 ARP 地址解析表中可以在一定程度上防止 ARP 欺骗攻击 14. Windows 系统中本地安全管理员(LSA)的任务是 ( ) A. 调用并监视安全警告序列(SAS,一般是 Ctrl+ALt+Del) B. 创建用户的本地访问令牌 C. 提供安全服务相关的应用程序接口(API) D. 管理用户的账户信息(如口令等) 15. Windows 中新技术文件系统(NTFS)的访问控制权限不包括( ) A. 读取权限(Read) B. 执行权限(Execute) C. 改变拥有者权限(Change) D. 拥有者权限(Owner)
电子科技大学【2015 年攻读硕士学位研究生入学考试试题】241专业课真题

.
A. le sien B. la sienne
C. le vôtre
D. la vôtre
18. Je ne veux pas sortir
je suis fatigué.
A. bien que
B.parce que
C. à condition que
me
19. Un Français
cinq fait aujourd’hui partie de ce qu’on appelle le troisième âge.
第4页
共 10 页
D. Nous travaillerons vite avant que ce soit fini.
Section B: 在以下内容中,句子的顺序打乱了。把这些句子重新排序以恢复短文。 (每题 1 分,共 3 分)
8.L’art de réussir une fête 1. Envoyer un plan d’accès détaillé à chaque participant. 2. Donner du rythme à la soirée avec de la musique dès l’apéritif. 3. Organiser un jeu au moment du dessert. 4. Dresser une jolie table avec une belle nappe et des bougies. A. 4 – 2 – 3 – 1 B. 1 – 4 – 2 – 3 C. 2 – 1 – 4 – 3 D. 2 – 4 – 1 – 3
C.d’où
D.par lequel
vin, s’il vous plaît.
A. le
电子科技大学硕士研究生入学考试初试考试大纲(密码学基础与网络安全)

2.4 掌握网络设备隔离技术
2.5 掌握入侵检测技术
2.6 掌握蜜罐技术
第3章 协议安全技术及其应用
3.1 理解安全协议的基本概念
3.2 理解PGP、S/MIME及电子邮件安全
3.3 掌握SSH协议及其应用
3.4 掌握SSL协议及WEB安全
3.5 理解IPSec协议
3.6 理解和掌握Kerberos和X.509协议
6.4 线性移位寄存器序列的周期性(了解)
6.5 线性移位寄存器的序列空间(了解)
6.6 线性移位寄存器序列的极小多项式(理解)
6.7 m序列的伪随机性(了解)
6.8 B-M算法与序列的线性复杂度(了解)
6.9 线性移位寄存器的非线性组合(了解)
第七章数字签名
7.1 基于公钥密码的数字签名(掌握)
7.2 EIGamal签名方案(理解)
一、总体要求
二、内容及比例
第一部分:密码学基础
第一章引言
1.1密码学的发展概况(了解)
1.2密码学的基本概念及其分类(掌握)
第二章古典密码
2.1 古典密码中的基本加密运算(了解)
2.2 几种典型的古典密码体制(了解)
2.3 古典密码的统计分析(了解)
第三章Shannon理论
3.1 密码体制的数学模型(掌握)
电子科技大学硕士研究生入学考试初试考试大纲(密码学基础与网络安全)
考试科目
825密码学基础与网络安全
考试形式
笔试(闭卷)
考试时间
180分钟
考试总分
150分
参考书目
《密码学概论》 Wade Trappe 人民邮电出版社 2004年
《密码编码学与网络安全——原理与实践》(第四版) Stallings 电子工业出版社 2006年
电子科技大学2015年硕士研究生信号与系统考研真题_电子科技大学专业课真题
0
£
n £ M -1 其它n值
,则输出
y[n]
不为
0
的点数最多为___
______________。
2、 已知连续时间线性时不变系统的单位阶跃响应为 s (t ) = e-tu(t) ,则该系统的单位冲击响应
h (t ) 为_________________。 3、 x (t ) 的拉普拉斯变换 X (S ) 存在,且 X (S ) 为有理表达式,在有限的 S 平面内,只存在 4
第1页共4页
三、
(8
分)已知系统的闭式表达为
y
(
t
)
=
ìïEv{x (t
í ïîod
{x
(t
)} )}
x (t ) >0 ,请确定 x(t) £ 0
(1)系统是否为因果系统?
(2)系统是否为稳定系统?
(3)系统是否为线性系统?
(4)系统是否为时不变系统?
( ) 四、(10 分)已知离散时间线性时不变系统的频率响应 H e jw 如图 1 所示,输入信号
第2页共4页
(4) 若要从 y3 (t ) 中恢复出 y2 (t ) ,确定线性时不变系统 h2 (t ) 的频率响应 H2 ( jw)
七、(10 分)已知一个连续时间线性时不变系统是稳定系统,系统的单位冲击响应为偶信号,
系统函数为 H (S ) ,并满足下面条件,确定该系统的系统函数及收敛域。 (1) H (S ) 在有限的 S 平面内只有 4 个极点,没有零点 (2) h (-t ) 的拉普拉斯变换的一个极点为 S = 1 (3) h (t ) e j2t 的拉普拉斯变换的一个极点为 S = 0
2
x [n]
z -1
电子科技大学825密码学基础与网络安全2008-2016年(08-13含答案)考研真题试卷
电子科技大学825密码学基础与网络安全2008-2016年(08-13含答案)考研真题试卷电子科技大学2016年攻读硕士学位研究生入学考试试题考试科目:825 密码学基础与网络安全注:所有答案必须写在答题纸上,写在试卷或草稿纸上均无效。
一、单向选择题(每题1分,共20题,20分)请在A、B、C和D四个选项中,选择一个最佳答案填写到答题纸上。
1.不属于ISO 7498-2和ITU-T X.800规定的安全服务有()A、认证(Authentication)B、访问控制(Access Control)C、加密(Encryption)D、数据完整性(Data Integrity)2. 以下关于VPN说法正确的是()A、VPN指的是用户自己租用线路,和公共网络物理上是完全隔离的、安全的B、VPN指的是用户通过公用网络建立的临时的、逻辑隔离的、安全的连接C、VPN不能做到信息认证和身份认证D、VPN只能提供身份认证、不能提供加密数据的功能3.关于入侵检测系统,下面说法不正确的是()A、由于基于主机的入侵检测系统可以监视一个主机上发生的全部事件,它们能够检测基于网络的入侵检测系统不能检测的攻击B、基于主机的入侵检测系统可以运行在交换网络中C、基于主机的入侵检测系统可以检测针对网络中所有主机的网络扫描D、基于应用的入侵检测系统比起基于主机的入侵检测系统更容易受到攻击,因为应用程序日志并不像操作系统审计追踪日志那样被很好地保护4.防火墙可以防止以下哪类攻击()A、内部网络用户的攻击B、传送已感染病毒的软件和文件C、外部网络用户的IP地址欺骗D、数据驱动型的攻击5.以下关于蜜罐(Honeypot)说法不正确的是()A、蜜罐技术可用来收集攻击信息B、蜜罐技术可用来收集计算机病毒代码C、蜜罐技术可用来诱骗攻击者D、蜜罐技术可用来阻止网络攻击的发生6.假设你向一台远程主机发送特定的数据包,却不想远程主机响应你的数据包,这时你使用的是以下哪一种攻击手段()A、缓冲区溢出B、地址欺骗C、拒绝服务攻击D、暴力攻击共6页第1页。
2014年-2016年电子科技大学820计算机专业基础考研真题试题试卷汇编
) 。
三、 分析计算题(30 分) 1. 某操作系统的 文 件 系统 采 用 混合 索 引分 配 方式,索引 节点 中 包含文 件 的 物 理 结构 数组 iaddr[10]。其中前 7 项 iaddr[0]~iaddr[6]为直接地址,iaddr[7]~iaddr[8]为一次间接地址, iaddr[9]为二次间接地址。系统盘块的大小为 4KB,磁盘的每个扇区大小也为 4KB。描述 磁盘块的数据项需要 4 个字节,其中 1 个字节标示磁盘分区,3 个字节标示物理块。请回 答一下问题: (1) 该文件系统支持的单个文件的最大程度是多少?(8 分) (2) 若某文件 A 的索引节点信息已位于内存, 但其它信息均在磁盘。 现在需要访问文件 A 中第 i 个字节的数据,列举出所有可能的磁盘访问次数,并说明原因。 (6 分) 2. 3 个进程 P0、P1、P2 互斥使用一个仅包含 1 个单元的缓冲区。P0 每次用 produce()生成 1 个正整数,并用 put()送入缓冲区。对于缓冲区中的每个数据,P1 用 get1()取出一次并用 compute1()计算其平方值,P2 用 get2()取出一次并用 compute2()计算其立方值。请用信号 量机制实现进程 P0、P1、P2 之间的同步与互斥关系,并说明所定义信号量的含义,要求 用伪代码描述。 (16 分) 四、 简答题(21 分) 1. 在存储器管理中,什么是重定位?为什么要引入重定位技术?(5 分) 2. 在分页存储管理系统中,页表的主要作用是什么?现代大多数计算机系统都支持非常 大的逻辑地址空间(232~264) ,这给页表设计带来了什么样的新问题,应如何解决。 (5 分) 3. 以从 I/O 设备读入数据为例,请用流程图方式说明程序 I/O、DMA 传输控制的处理过 程。 (6 分) 4. 在哲学家就餐问题中,如果将先拿起左边筷子的哲学家成为左撇子,而将先拿起右边 筷子的哲学家称为右撇子。在同时存在左撇子和右撇子的前提下,我们安排哲学家随 意就座。请问是否可能产生死锁,为什么?(5 分)
2015电子科技大学研究生试卷
效无题院学答内名姓以线封号学密电子科技大学研究生试卷(考试时间:至,共__2_小时)课程名称图论及其应用教师学时60学分教学方式讲授考核日期_2015__年_6__月__26__日成绩考核方式:(学生填写)一.填空题 (每空 3 分,共 15 分)1.不同构的 3 阶简单图的个数为 _____。
2.图 1 中的最小生成树的权值为________。
3.基于图 2 的最优欧拉环游的总权值为__________ 。
4.图 3 中块的个数为_______。
61546321262227433833216图 1图 3图 25.图 4 中强连通分支的个数为________。
图41二.单项选择 (每题 3 分,共 15 分)1.关于图的度序列,下列命题错误的是( ) (A)同构的两个图的度序列相同;(B) 非负整数序列( d1, d2,n, d n ) 是图的度序列当且仅当d i是偶数;i1(C)如果非负整数序列 (d1 , d2 , , d n ) (n 2)是一棵树的度序列,那么序列中至少有两个整数的值为 1;(D). 如果非负整数序列(d1, d2,,d n ) 是简单图的度序列,那么在同构意义下只能确定一个图。
2.关于n阶简单图的邻接矩阵 A (a ij )n n,下列说法错误的是()(A)矩阵 A 的行和等于该行对应顶点的度数;(B)矩阵所有元素之和等于该图边数的 2 倍;(C)不同构的两个图,它们的邻接矩阵特征谱一定不同;(D)非连通图的邻接矩阵一定可以表示为准对角矩阵形式。
3.关于欧拉图,下面说法正确的是()(A)欧拉图存在唯一的欧拉环游;(B)非平凡欧拉图中一定有圈;(C)欧拉图中一定没有割点;(D)度数为偶数的图一定是欧拉图。
4.关于哈密尔顿图,下列命题错误的是()(A)设G是n3的简单图,若其闭包是完全图,则G 是哈密尔顿图;(B)若 n 阶单图的闭包不是完全图,则它一定是非哈密尔顿图;2(C) 若G 是哈密尔顿图,则对于V 的每个非空顶点子集S ,均有(G S) S ;(D)若 G 是n 3的非 H 单图,则 G 度弱于某个C m,n图。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
电子科技大学2015年攻读硕士学位研究生入学考试试题考试科目:825 密码学基础与网络安全注:所有答案必须写在答题纸上,写在试卷或草稿纸上均无效。
一、单向选择题(每题1分,共20题,20分)请在A、B、C和D四个选项中,选择一个最佳答案填写到答题纸上。
1. 下列关于安全服务与安全机制的关系不正确的说法是()A. 安全服务由安全机制实现B. 安全机制与安全服务之间没有关系C. 一种安全机制可以实现一种安全服务D. 一种安全服务可以由一种安全机制来实现2. 按照加密和解密密钥是否相同,密码算法可分为()A. 分组密码算法和序列密码算法B. 对称密码算法和公钥密码算法C. 基于密钥保密的算法和基于算法保密的算法D. 古典密码算法和现代密码算法3. 整数37的欧拉函数(37)j等于()A. 35B. 36C. 37D. 384. 反病毒软件具有副作用,当正常操作和病毒操作不能辨别时,可能会造成反病毒系统的()A. 误报B. 不报C. 漏报D. 错报5. 7804的后三位数字是()A. 400B. 401C. 402D. 4036. 以下关于美国国防部所提出的PDRR网络安全模型说法正确的是()A. 安全策略(Policy)是PDRR的重要内容B. 依据PDRR模型,增加系统的保护时间可提高系统的安全性C. 依据PDRR模型,增加系统的检测时间可提高系统的安全性D. 依据PDRR模型,应该尽量增加系统暴露时间来提高系统的安全性7. 以下说法不正确的是()A. 非对称加密算法较好地解决了密钥管理问题B. TCP/IP协议在设计之初并未考虑网络安全威胁C. 网络隔离技术不能减少对信息系统的安全威胁D. 安全协议需要使用某种密码算法且须实现一项或多项安全功能8. 下列关于网络地址转换(NAT)正确的说法是()A. NAT与防火墙能协同工作,但与VPN不能协同工作B. NAT与VPN能协同工作,但与防火墙不能协同工作C. NAT与防火墙能协同工作D. NAT与VPN不能协同工作9. 下列关于数字签名说法正确的是()A. 数字签名是不可信的B. 数字签名容易被伪造C. 数字签名容易抵赖D. 数字签名不可改变10. 一般来说,以下哪个不属于设备物理安全的内容()A. 设备防盗B. 设备防毁C. 设备电磁辐射抗扰D. 设备外观保护11. 关于电子密码本(ECB)密码操作模式说法正确的是()A. 对每一个明文数据块采用不同的密钥进行加密B. 对每一个明文数据块采用不同的密钥进行解密C. 错误传递仅有一块:出错密文块仅导致对应的明文块错误D. 错误传递有多块:出错密文块将导致多个明文块错误12. 以下关于蜜罐(Honeypot)说法不正确的是()A. 蜜罐技术可用来收集攻击信息B. 蜜罐技术可用来收集计算机病毒代码C. 蜜罐技术可用来诱骗攻击者D. 蜜罐技术可用来阻止网络攻击的发生13. 在以下技术中,不能用作消息认证函数来产生消息认证符的是()A. 消息加密B. 消息认证码(MAC)C. 压缩函数D. 哈希(Hash)函数14. 以下关于IPSec中的密钥管理说法正确的是()A. 互联网络安全关联和密钥管理协议(IAKMP)是IPSec密钥管理的框架B. 因特网密钥交换协议(IKE)是IPSec密钥管理的框架C. Diffie-Hellman密钥交协议是因特网密钥交换协议(IKE)使用的密钥交换协议D. Oakley不是因特网密钥交换协议(IKE)使用的密钥交换协议15. 以下关于防火墙说法正确的是()A、所有防火墙都能够检测网络攻击 B. 所有防火墙都能够检测计算机病毒C. 防火墙能防御内部攻击D. 防火墙能防御外部攻击16. 以下关于入侵防护系统(IPS)的说法不正确的是()A. 入侵防护系统(IPS)可以检测网络攻击行为B. 入侵防护系统(IPS)可以保护一个网络C. 入侵防护系统(IPS)可以阻断检测出的攻击行为D. 入侵防护系统(IPS)可以对计算机病毒进行检测17. 以下关于计算机犯罪(Computer Crime)最准确的说法是()A. 攻击别人的计算机并进而获得信息的行为就是计算机犯罪B. 通过网络攻击获得别人的机密信息一定是计算机犯罪C. 盗窃计算机是计算机犯罪D. 行为人通过计算机操作所实施的危害计算机信息系统(包括内存数据及程序)安全以及其他严重危害社会的并应当处以刑罚的行为18. 可信计算机系统评估准则(TCSEC)是由哪个国家提出来的?()A. 中国B. 英国C. 美国D. 德国19. NP问题的含义是()A. 非确定性图灵机上不能够在多项式时间内得到处理的问题B. 非确定性图灵机上能够在多项式时间内得到处理的问题C. 确定性图灵机上不能够在多项式时间内得到处理的问题D. 确定性图灵机上能够在多项式时间内得到处理的问题20.下面关于TCP协议的说法中,不正确的是()A. TCP协议是传输层的协议B. TCP协议是面向连接的协议C. TCP协议是非面向连接的协议D. TCP协议数据包中不包含源IP地址二、多项选择题(每题2分,共10题,20分)每题有一个或多个正确答案。
请将A、B、C和D四个选中所有正确答案的选项填写到答题纸上。
(注意:多选、少选、错选均不得分)1. 下列哪些方法可以用来防止重放攻击?()A. 挑战-应答机制B. 时戳机制C. 超时-重传机制D. 序列号机制2. 以下关于身份认证的说法不正确的有()A. 身份认证是验证者获得对声称者所声称的事实的信任B. 身份认证有单向和双向认证之分,且可以简单地重复两次单向认证来实现双向认证C. 密码技术和非密码技术都可以用来实现身份认证D. 只有密码技术才能够用来实现身份认证3. 以下关于数据备份说法正确的有()A. 按照备份后数据是否可以更改,数据备份可分为活备份和死备份B. 差分备份只备份上次全备份以来变化了的数据C. 差分备份只备份上次备份以来变化了的数据D. 增量备份只备份上次备份以来变化了的数据4. 以下属于ISO 7498-2和ITU-T X.800规定的安全服务的有()A. 认证(Authentication)B. 访问控制(Access Control)C. 加密(Encryption)D. 数据机密性(Data Confidentiality)5. RFC 1321中以下关于MD5的说法正确的有()A. MD5是一个消息摘要算法标准B. MD5的输入可以为任意长,但其输出是128位C. MD5的输入不能为任意长,但其输出是128位D. MD5算法不论输入多长,都必须进行消息填充6. 美国国家标准学会(ANSI)制订的FIPS PUB 180和180-1中关于SHA-1说法正确的有()A. SHA-1是一个消息摘要算法标准B. SHA-1的输入可以为任意长,但其输出是160位C. SHA-1的输入不能为任意长,但其输出是160位D. SHA-1算法不论输入多长,都必须进行消息填充7. 以下哪些是提高计算机系统可靠性的方法()A. 避错B. 容错C. 硬件冗余D. 软件冗余8. 通常而言,以下哪些是域名解析系统(DNS)潜在的安全威胁()A. DNS劫持攻击B. DNS缓存污染C. DNS拒绝服务攻击D. DNS ID欺骗9. 以下关于跨站脚本攻击(XSS)说法正确的有()A. 跨站脚本攻击包括持久性跨站攻击B. 跨站脚本攻击包括非持久性跨站攻击C. 跨站脚本攻击包括DOM跨站攻击D. 跨站脚本攻击包括拒绝服务跨站攻击10. 在一个密钥管理系统中,可能的密钥类型有()A. 会话密钥B. 主密钥C. 密钥加密密钥D. 随机密钥三、计算选择题(每题5分,共4题, 20分)请在A 、B 、C 和D 四个选项中,选择一个正确答案填写到答题纸上。
1. 在UNIX 系统中,如果用户掩码(umask )为022,则当该用户创建一个文件时,该文件的初始权限是( )A. 754B. 755C. 756D. 7572. 投掷一个有n 面的骰子,有n 个结果,每个结果的概率均为1/n ,则该随机事件的熵为( )A. 2log ()nB. 2log ()n -C. 22log ()nD. 22log ()n - 3. 假如Alice 的RSA 公钥为n=323,e=5,Alice 不小心泄露了私钥d=173。
Alice 将e 换成7,下列哪一个整数可作为相应的私钥d ( )A. 41B. 173C. 247D. 1174. Hill 加密算法123456mod 261198C M æöç÷=ç÷ç÷èø的解密函数(C 表示密文,M 表示明文)是( ) A. 225161921mod 2615131M N æöç÷=ç÷ç÷èø B. 225161724mod 2615131M N æöç÷=ç÷ç÷èøC. 227861724mod 2615131M N æöç÷=ç÷ç÷èøD. 227961724mod 2615131M N æöç÷=ç÷ç÷èø四、简答题(共3题,20分)1. (5分)请简述入侵检测系统(IDS )中误用检测技术(Misuse Detection)和异常检测技术(Anomaly Detection )的含义,并说明入侵检测系统的主要技术指标及其含义。
2. (5分)根据密码分析者可能取得的分析资料不同,可将密码分析(或攻击)分为哪几类?给出这几类攻击的定义。
3.(10分)在某应用系统中,将安全等级划分为绝密(Top Secret )、机密(Secret )和公开(Unclassified )三个等级,其中绝密安全等级最高,公开安全等级最低。
假设该应用系统中有两个主体(S 1和S 2)和三个客体(O 1,O 2和O 3),其中主体S 1的密级为绝密,S 2的密级为机密,客体O 1的密级为绝密,O 2的密级为机密,O 3的密级为公开,请依据访问控制技术的有关原理,回答以下问题:(1)如果按照“不上读,不下写”的访问控制模型,S 1可以对哪些客体进行读和写操作?这样的访问控制模型确保了什么安全属性?(2)如果按照“不下读,不上写”的访问控制模型,S 2可以对哪些客体进行读和写操作?这样的访问控制模型确保了什么安全属性?五、认证协议综合分析题(10分)认证协议是安全协议的一种。
