计算机网络英文试题
计算机网络英文题库(附答案)chapter5

Chapter 5 The Link Layer and Local Area Network1.A ( ) protocol is used to move a datagram over an individual link.A application-layerB transport-layerC network-layerD link-layer2.The units of data exchanged by a link-layer protocol are called ( ).A datagramsB framesC segmentsD messages3.Which of the following protocols is not a link-layer protocol? ( )A EthernetB PPPC HDLCD IP4.In the following four descriptions, which one is not correct? ( )A link-layer protocol has the node-to-node job of moving network-layer datagrams over a single link in the path.B The services provided by the link-layer protocols may be different.C A datagram must be handled by the same link-layer protocols on the different links in the path.D The actions taken by a link-layer protocol when sending and receiving frames include error detection, flow control and random access.5.Which of the following services can not offered by a link-layer protocol? ( )A congestion controlB Link AccessC Error controlD Framing6.( ) protocol serves to coordinate the frame transmissions of the many nodes when multiple nodes share a single broadcast link.A ARPB MACC ICMPD DNS7.In the following four descriptions about the adapter, which one is not correct? ( )A The adapter is also called as NIC.B The adapter is a semi-autonomous unit.C The main components of an adapter are bus interface and the link interface.D The adapter can provide all the link-layer services.8.Consider CRC error checking approach, the four bit generator G is 1011, and suppose that the data D is 10101010, then the value of R is( ).A 010B 100C 011D 1109.In the following four descriptions about random access protocol, which one is not correct? ( )A I n slotted ALOHA, nodes can transmit at random time.B I n pure ALOHA, if a frame experiences a collision, the node will immediately retransmit it with probability p.C T he maximum efficiency of a slotted ALOHA is higher than a pure ALOHA.D I n CSMA/CD, one node listens to the channel before transmitting.10.In the following descriptions about MAC address, which one is not correct? ( )A T he MAC address is the address of one node’s adapter.B N o two adapters have the same MAC address.C T he MAC address doesn’t change no matter where the adapter goes.D M AC address has a hierarchical structure.11.The ARP protocol can translate ( ) into ( ). ( )A h ost name, IP addressB h ost name, MAC addressC I P address, MAC addressD broadcast address, IP address12.The value of Preamble field in Ethernet frame structure is ( )A 10101010 10101010……10101010 11111111B 10101011 10101011……10101011 10101011C 10101010 10101010……10101010 10101011D 10101010 10101010……10101010 1010101013.There are four steps in DHCP, the DHCP server can complete ( ).A DHCP server discoveryB DHCP server offersC DHCP requestD DHCP response14.In CSMA/CD, the adapter waits some time and then returns to sensing the channel. In the following four times, which one is impossible? ( )A 0 bit timesB 512 bit timesC 1024 bit timesD 1028 bit times15.The most common Ethernet technologies are 10BaseT and 100BaseT. “10” and “100” indicate( ).A the maximum length between two adaptersB the minimum length between two adaptersC the transmission rate of the channelD the transmission rate of the node16.The principal components of PPP include but not( ).A framingB physical-control protocolC link-layer protocolD network-layer protocol17.In the following four options, which service can not be provided by switch? ( )A filteringB self-learningC forwardingD optimal routing18.In the following four services, which one was be required in PPP? ( )A packet framingB error detectionC error correctionD multiple types of link19.The ability to determine the interfaces to which a frame should be directed, and then directing the frame to those interfaces is( ).A filteringB forwardingC self-learningD optimal routing20.In ( ) transmission(s), the nodes at both ends of a link may transmit packets at the same time.A full-duplexB half-duplexC single-duplexD both full-duplex and half-duplex21.Consider the data D is 01110010001, if use even parity checking approach, the parity bit is( ① ), if use odd parity checking approach, the parity bit is( ② ). ( )A ①0 ②1B ①0 ②0C ①1 ②1D ①1 ②022.In the following four descriptions about parity checks, which one is correct? ( )A Single-bit parity can detect all errors.B Single-bit parity can correct one errors.C Two-dimensional parity not only can detect a single bit error, but also can correct that error.D Two-dimensional parity not only can detect any combination of two errors, but also can correct them.23.MAC address is ( ) bits long.A 32B 48C 128D 6424.Wireless LAN using protocol ( ).A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.1125.The following protocols are belonging to multiple access protocols except for ( ).A channel partitioning protocolsB routing protocolsC random access protocolsD taking-turns protocols26.Which of the following is not belonging to channel partitioning protocols? ( )A CSMAB FDMC CDMAD TDM27.In the following four descriptions about CSMA/CD, which one is not correct? ( )A A node listens to the channel before transmitting.B If someone else begins talking at the same time, stop talking.C A transmitting node listens to the channel while it is transmitting.D With CSMA/CD, the collisions can be avoided completely.28.( ) provides a mechanism for nodes to translate IP addresses to link-layer address.A IPB ARPC RARPD DNS29.A MAC address is a ( )address.A physical-layerB application-layerC link-layerD network-layer30.Which of the following is correct? ( )A No two adapters have the same MAC address.B MAC broadcast address is FF-FF-FF-FF-FF-FF.C A portable computer with an Ethernet card always has the same MAC address, no matter where the computer goes.D All of the above31.In the following four descriptions, which one is not correct? ( )A ARP resolves an IP address to a MAC address.B DNS resolves hostnames to IP addresses.C DNS resolves hostnames for hosts anywhere in the Internet.D ARP resolves IP addresses for nodes anywhere in the Internet.32.In the LAN, ( )protocol dynamically assign IP addresses to hosts.A DNSB ARPC DHCPD IP33.DHCP protocol is a four-step process: ①DHCP request. ②DHCP ACK. ③DHCP server discovery. ④DHCP server offer(s). The correct sequence is ( )A ①②③④B ③②①④C ③④①②D ①④③②34.In the Ethernet frame structure, the CRC field is ( )bytes.A 2B 4C 8D 3235.In the Ethernet frame structure, the Data field carries the ( ).A IP datagramB segmentC frameD message36.In the following four descriptions, which one is not correct? ( )A Ethernet uses baseband transmission.B All of the Ethernet technologies provide connection-oriented reliable service to the network layer.C The Ethernet 10Base2 technology uses a thin coaxial cable for the bus.D The Ethernet 10BaseT technology uses a star topology.37.Ethernet’s multiple access protocol is ( ).A CDMAB CSMA/CDC slotted ALOHAD token-passing protocol38.In the following four descriptions about CSMA/CD, which one is not correct? ( )A An adapter may begin to transmit at any time.B An adapter never transmits a frame when it senses that some other adapter is transmitting.C A transmitting adapter aborts its transmission as soon as it detects that another adapter is also transmitting.D An adapter retransmits when it detects a collision.39.Which of the following descriptions about CSMA/CD is correct? ( )A No slots are used.B It uses carrier sensing.C It uses collision detection.D All of the above.40.The Ethernet 10BaseT technology uses( )as its physical media.A fiber opticsB twisted-pair copper wireC coaxial cableD satellite radio channel41.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( )meters.A 100B 200C 500D 1042.A ( )is a physical-layer device that acts on individual bits rather than on frames.A switchB hubC routerD gateway43.A hub is a ( )device that acts on individual bits rather than on frames.A physical-layerB link-layerC network-layerD ransport-layer44.A switch is a( )device that acts on frame.A physical-layerB link-layerC network-layerD transport-layer45.In the following four descriptions, which one is not correct? ( )A Switches can interconnect different LAN technologies.B Hubs can interconnect different LAN technologies.C There is no limit to how large a LAN can be when switches are used to interconnect LAN segments.D There is restriction on the maximum allowable number of nodes in a collision domain when hubs are used to interconnect LAN segments.46.The ability to determine whether a frame should be forwarded to some interface or should just be dropped is ( ).A f ilteringB f orwardingC s elf-learningD o ptimal routing47.Which of the following devices is not a plug and play device? ( )A hubB routerC switchD repeater48.Which of the following devices is not cut-through device? ( )A hubB routerC switchD repeater49.In the following four descriptions, which one is not correct? ( )A Switches do not offer any protection against broadcast storms.B Routers provide firewall protection against layer-2 broadcast storms.C Both switches and routers are plug and play devices.D A router is a layer-3 packet switch, a switch is a layer-2 packet switch. 50.Which device has the same collision domain? ( )A HubB SwitchC RouterD Bridge51.IEEE802.2 protocol belong to ( )layerA networkB MACC LLCD physical52.IEEE802.11 protocol defines ( )rules.A Ethernet BusB wireless WANC wireless LAND Token Bus53.In data link-layer, which protocol is used to share bandwidth? ( )A SMTPB ICMPC ARPD CSMA/CD54.When two or more nodes on the LAN segments transmit at the same time, there will be a collision and all of the transmitting nodes well enter exponential back-off, that is all of the LAN segments belong to the same( ).A collision domainB switchC bridgeD hub55.( )allows different nodes to transmit simultaneously and yet have their respective receivers correctly receive a sender’s encoded data bits.A CDMAB CSMAC CSMA/CDD CSMA/CA56.Because there are both network-layer addresses (for example, Internet IP addresses) and link-layer addresses (that is, LAN addresses), there is a need totranslate between them. For the Internet, this is the job of ( ).A RIPB OSPFC ARPD IP57.PPP defines a special control escape byte, ( ). If the flag sequence, 01111110 appears anywhere in the frame, except in the flag field, PPP precedes that instance of the flag pattern with the control escape byte.A 01111110B 01111101C 10011001D 1011111058.The device ( ) can isolate collision domains for each of the LAN segment.A modemB switchC hubD NIC59.In the following four descriptions about PPP, which one is not correct? ( )A PPP is required to detect and correct errors.B PPP is not required to deliver frames to the link receiver in the same order in which they were sent by the link sender.C PPP need only operate over links that have a single sender and a single receiver.D PPP is not required to provide flow control.60.In the PPP data frame, the( ) field tells the PPP receivers the upper-layer protocol to which the received encapsulated data belongs.A flagB controlC protocolD checksum61.PPP’s link-control protocols (LCP) accomplish ( ).A initializing the PPP linkB maintaining the PPP linkC taking down the PPP linkD all of the above62.The PPP link always begins in the ( ) state and ends in the ( ) state. ( )A open, terminatingB open, deadC dead, deadD dead, terminating63.For( ) links that have a single sender at one end of the link and a single receiver at the other end of the link.A point-to-pointB broadcastC multicastD all of the above64.With ( )transmission, the nodes at both ends of a link may transmit packets at the same time.A half-duplexB full-duplexC simplex(单工)D synchronous65.With ( ) transmission, a node can not both transmit and receive at the same time.A half-duplexB full-duplexC simplex(单工)D synchronous66.Which of the following functions can’t be implemented in the NIC? ( )A encapsulation and decapsulationB error detectionC multiple access protocolD routing67.Which of the following four descriptions is wrong? ( )A The bus interface of an adapter is responsible for communication with the adapter’s parent node.B The link interface of an adapter is responsible for implementing the link-layer protocol.C The bus interface may provide error detection, random access functions.D The main components of an adapter are the bus interface and the link interface. 68.For odd parity schemes, which of the following is correct? ( )A 011010001B 111000110C 110101110D 00011011069.( )divides time into time frames and further divides each time frame into N time slots.A FDMB TMDC CDMAD CSMA70.With CDMA, each node is assigned a different ( )A codeB time slotC frequencyD link71.Which of the following four descriptions about random access protocol is not correct? ( )A A transmission node transmits at the full rate of the channelB When a collision happens, each node involved in the collision retransmits at once.C Both slotted ALOHA and CSMA/CD are random access protocols.D With random access protocol, there may be empty slots.72.PPP defines a special control escape byte 01111101. If the data is b1b201111110b3b4b5, the value is( )after byte stuffing.A b1b20111110101111110b3b4b5B b1b20111111001111101b3b4b5C b5b4b30111111001111101b2b1D b5b4b30111110101111110b2b173.MAC address is in ( ) of the computer.A RAMB NICC hard diskD cache74.Which of the following is wrong? ( )A ARP table is configured by a system administratorB ARP table is built automaticallyC ARP table is dynamicD ARP table maps IP addresses to MAC addresses75.NIC works in ( )layer.A physicalB linkC networkD transport76.In LAN, if UTP is used, the common connector is( ).A AUIB BNCC RJ-45D NNI77.The modem’s function(s) is(are) ( ).A translates digital signal into analog signalB translates analog signal into digital signalC both translates analog signal into digital signal and translates digital signal into analog signalD translates one kind of digital signal into another digital signal78.( )defines Token-Ring protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.279.( )defines Token-Bus protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.280.( ) defines CSMA/CD protocol.A IEEE 802.3B IEEE 802.4C IEEE 802.5D IEEE 802.281.The computer network that concentrated in a geographical area, such as in a building or on a university campus, is ( )A a LANB a MANC a WAND the Internet82.The MAC address is ( ) bits long.A 32B 48C 128D 25683.Which of the following four descriptions about MAC addresses is wrong? ( )A a MAC address is burned into the adapter’s ROMB No two adapters have the same addressC An adapter’s MAC address is dynamicD A MAC address is a link-layer address84.Which of the following four descriptions about DHCP is correct? ( )A DHCP is C/S architectureB DHCP uses TCP as its underlying transport protocolC The IP address offered by a DHCP server is valid foreverD The DHCP server will offer the same IP address to a host when the host requests an IP address85.The ( )field permits Ethernet to multiplex network-layer protocols.A preambleB typeC CRCD destination MAC address86.For 10BaseT, the maximum length of the connection between an adapter and the hub is ( ) meters.A 50B 100C 200D 50087.An entry in the switch table contains the following information excepts for ( )A the MAC address of a nodeB the switch interface that leads towards the nodeC the time at which the entry for the node was placed in the tableD the IP address of a node88.Consider the 4-bit generator , G is 1001, and suppose that D has the value 101110000. What is the value of R?89.Consider the following graph of the network. Suppose Host A will send a datagram to Host B, Host A run OICQ on port 4000, Host B run OICQ on port 8000. All of ARP tables are up to date. Enumerate all the steps when message “Hello” is sent from host A to host B.。
《计算机网络》考题(英文选择题)

《计算机⽹络》考题(英⽂选择题)Computer Networks – Exam1 Short questionsFor each question, please circle a single best answer.1.In the CSMA/CD protocol, what condition on the transmission delay T trans and thepropagation delay T prop has to be satisfied to guarantee that a node always detects a collision?A. T trans > T propB. T trans > 2T prop CORRECTC. T trans < T propD. 2T trans < T prop2.Alice and Bob communicate in an alphabet that has L letters. They use a monoalphabeticsubstitution cipher with key K. Assume that Trudy obtains a plaintext m and thecorresponding ciphertext c. Under what conditions can Trudy recover the key K completely?A. m contains at least 1-L unique letters. CORRECTB. Lm≥.C. Km≥.D. m is not empty.3.The WiMaX protocol:A. provides the maximum available data rate over a wireless channel.B. uses unlicensed spectrum, such as WiFi.C. provides a mechanism for scheduling. CORRECTD. All of the above options are correct.4.Two hosts simultaneously send data through a link of capacity 1Mbps. Host A generates datawith a rate of 1Mbps and uses TCP. Host B uses UDP and transmits a 100bytes packet every 1ms. Which host will obtain higher throughput?A. Host A.B. Host B. CORRECTC. They obtain roughly the same throughput.D. They experience congestion collapse and negligible throughput.5.What is the theoretical upper-bound on the number of simultaneous TCP/IPv4 connectionsthat a host with a single IP address can handle? (Ignore memory limitations.)B. 232C. 264CORRECTD. unlimited6.Host A sends a TCP segment (Seq = 43, ACK = 103), to which host B replies with a TCP segment (Seq = 103, ACK = 57). The payload of the first TCP segment isA. 14 bytes long. CORRECTB. 43 bytes long.C. 46 bytes long.D. 57 bytes long.E. 60 bytes long.7.The Distance-Vector algorithm is not:A. iterative.B. asynchronous.C. distributed.D. used in RIP.E. None of the above. CORRECT8.Longest prefix matching is used:A. in routers to know on which link interface to forward packets. CORRECTB. in classless addressing to use the address space more efficiently than in classful addressing.C. by NAT to increase the available address space in home networks.D. to assign subnet masks.E. None of the above.9.An authoritative DNS server knows a top-level domain server via:A. hostname.B. IP address. CORRECTC. canonical hostname.D. alias.E. domain.10.A user requests aWeb page that consists of some text and 3 images. The browser’s cache is empty. For this page, the client’s browser:A. sends 1 http request message and receives 1 http response messages.B. sends 1 http request message and receives 3 http response messages.C. sends 1 http request message and receives 4 http response messages.D. sends 3 http request messages and receives 3 http response messages.11.What is the advantage of using a layered model of networking?A. Simplified the networkB. For the purpose of standardizationC. Divides the complexity of internetworking into discrete, more easily learned operation subsetsD. All of the above CORRECT12.What is the name of protocol data unit(PDU)at the network layer of the OSI reference model?A. TransportB. FrameC. Packet CORRECTD. Segment13.Which is true when a broadcast is sent out in an Ethernet 802.3 LAN?A. The broadcast is sent only to the default gateway.B. The broadcast is sent only to the destination hardware address in the broadcast.C. The broadcast is sent to all devices in the collision domain. CORRECTD. The broadcast is sent to all devices in the broadcast domain.14.Segmentation of a data stream happens at which layer of the OSI model?A.PhysicalB.Data Link/doc/ee7d8dd65022aaea998f0fd2.html workD.Transport CORRECT15.Which of following international standard defines for Fast Ethernet?A.IEEE 802.3B.IEEE 802.3zC.IEEE 802.3u CORRECTD.IEEE 802.3ae16.What does the Data Link layer use to find hosts on a local network?A.Logical network addressesB.Port numbersC.Hardware addresses CORRECTD.Default gateways17.What were the key reasons the ISO released the OSI model?A.To allow companies to charge more for their equipmentB.To help vendors create interoperable network devices CORRECTC.To help vendors create and sell specialized software and hardware18.What is used at the Transport layer to stop a receiving host’s buffer from overflowing?A.SegmentationB.PacketsC.AcknowledgmentsD.Flow control CORRECT19.When data is encapsulated, which is the correct order?A.Data,frame,packet,segment,bitB.Segment,data,packet,frame,bitC.Data,segment,packet,frame,bit CORRECTD.Data,segment,frame,packet,bit20.What does the term“Base”indicate in 100Base-TX?A.The maximum distanceB.The type of wiring usedC.A LAN switch method using half duplexD.A signaling method for communication on the network CORRECT21.What is the maximum distance of 100Base-T?A.100 feetB.1000 feetC.100 meters CORRECTD.1000 meters22.Which of the following would describe a transport layer connection that would ensure reliable delivery?A.RoutingB.Acknowledgments CORRECTC.SwitchingD.System authentication23.Which of the following is not considered a reason for LAN congestion?A.Low bandwidthB.Too many users in a broadcast domainC.Broadcast stormsD.Routers CORRECT24.Which of the following are two basic types of dynamic routing?A.Static and defaultB.TCP and UDP exchangeD.None of the above25.If your LAN network is currently congested and you are using only hubs in your network,what would be the BEST solution to decrease congestion on your network?A.Cascade your hubs.B.Replace your hubs with switches. CORRECTC.Replace your hubs with routers.D.Add faster hubs.26.What technology is a used by most switches to resolve topology loops and ensure that data flows properly through a single network path?A.RIPB.STP CORRECTC.IGRPD.Store-and-forward27.Which of the following is one of the characteristics of IP?A.reliable and connectionlessB.unreliable and connectionless CORRECTC.reliable and connection-orientedD.unreliable and connection-oriented28.What is the valid host range for subnet 172.16.10.16(Mask 255.255.255.240)?A.172.16.10.20 through 172.16.10.22B.172.16.10.16 through 172.16.10.23C.172.16.10.17 through 172.16.10.31D.172.16.10.17 through 172.16.10.30 CORRECT29.What range of addresses can be used in the first octet of a Class B network address?A.1–126B.128–190C.128–191 CORRECTD.129–19230.Which of the following is not true?A.IP is connectionless and provides routing.B.ARP is used to find an IP address of a host. CORRECTC.UDP is connectionless.D.TCP is connection oriented.31.Which class of IP address provides a maximum of only 254 host addresses per network ID?B.Class BC.Class C CORRECTD.Class D32.Which protocol tool use ICMP?A.TelnetB.Ping CORRECTC.ARPD.FTP33.Which of the following is an IEEE standard for frame tagging?A.802.1XB.802.3ZC.802.1QD.802.3U CORRECT34.A client will use____to send emails to mail-server.A.POP3B.SMTP CORRECTC.TELNETD.FTP35.Which protocol used in PPP allows multiple Network layer protocols to be used during a connection?A.LCPB.NCP CORRECTC.HDLCD.X.2536.When too many packets are present in the subnet, performance degrades. What is this situation called?A.dead lockB.congestion CORRECT/doc/ee7d8dd65022aaea998f0fd2.html work fault/doc/ee7d8dd65022aaea998f0fd2.html work busy37.Which language can be used to realize the client-side dynamic web page generation?A.CGIB.ASP CORRECTC.JavaScript38.The two-wire connections between each subs criber’s telephone and the end office are known in the trade as the____.A.trunkB.local loopC.linkD.switch CORRECT39.When web page is transmitted over SSL, the protocol used is_____.A.HTTPB.SHTTPC.HTTPS CORRECTD.SSL40.Nyquist proved that if an arbitrary signal has been run through a low-pass filter of bandwidthH, the filtered signal can be completely reconstructed by making only_____(exact)samples per secondA.HB.0.5HC.2H CORRECTD.4H41.To convert a binary message to an ASCII message in email system, we can useencoding, which break up groups of 24 bits into four 6-bit units, with each unit being sent asa legal ASCII character. (Ref in page 262)A.base64 CORRECTB.quoted-printableC.SMTPD.POP342.A CRC generator polynomial is G(x)=X8+X5+X2+l.How many bits will the checksum be?A.7B.8 CORRECTC.9D.1043.If the length of sequence is 4 bits, the maximum sending window size should be____.A.13B.14C.15 CORRECTD.1644.In 802.11, to solve the_______station problem and the hidden station problem,we can useA. faultB.mobileC.exposed CORRECTD.wireless45.If the congestion window size is 20KB, and the receive window size is 30KB,what is themaximum bytes can the TCP entity transmit?A.20KB CORRECTB.30KBC.50KBD.10KB46.Port numbers below________are called well-known ports and are reserved for standardservices.A.256B.1024 CORRECTC.4096D.100047.________, which are overlay networks on top of public networks but with most of theproperties of private network.A.PBXB.VPN CORRECTC.CDMA 1XD.GPRS48.The problem of running out of IP addresses is not a theoretical problem that might occur atsome point in the distant future. Some people felt that a quick fix was needed for the short term. This quick fix came in the form of____________________.A.IP6B.DHCPC.RARPD.NAT CORRECT49.Public-key algorithms have the property that_______keys are used for encryption anddecryption and that the decryption key cannot be derived from the encryption key.These properties make it possible to publish the public key.A.one timeB.randomC.same50.The main public-key algorithm is___________which derives its strength from the fact that itis very difficult to factor large numbers.A.DESB.AESC.MD5D.RSA CORRECT51.Various schemes have been devised for digital signatures, using both symmetric-key and________-key algorithms.A.public CORRECTB.privateC.one timeD.one way52.Often, authentication is needed but secrecy is not, based on the idea of a one-way hashfunction that takes an arbitrarily long piece of plaintext and from it computes a fixed-length bit string. This hash function, MD, often called a________.A.message digest CORRECTB.packet-switchedC.message-detectD.mini data53.URL(Uniform Resource Locator)have three parts: the________, the DNS name of themachine on which the page is located, and a local name uniquely indicating the specific page.A.protocol CORRECTB.addressC.port number/doc/ee7d8dd65022aaea998f0fd2.html54.HTTP1.1, which supports________connections. With them, it is possible to establish a TCPconnection, send a request and get a response, and then additional requests and get additional response.A.one timeB.persistent CORRECTC.stop and waitD.one-way55._______, when it is used, a bad frame that is received is discarded, but the good framesreceived after it are buffered.A.selective repeatD.stop and wait56.How does the FDM multiplexing schemes work like?A.each user having exclusive possession of some band CORRECTB.each user take turns, periodically getting the entire bandwidth for a litter burst of timeC.each user transmit over the entire frequency spectrum all the time with different codingD.each user transmit over a shared fiber using different wavelength57.When we use a modem, which use 16 phases signal to modulation, then how much can we get the maximum data rate in a 2400 baud channel(in noiseless channel)?A.400bpsB.2400bpsC.9.6kbps CORRECTD.14.4kbps58.______is a small java program that has been compiled into binary instruction running in JVM, and can be embedded into HTML pages, interpreted by JVM-capable browsers.A.JavaScriptB.JavaBeanC.Applet CORRECTD.JSP59.Which of the following best describes the function of the OSI reference model’s transport layer?A.It sends data by using flow control CORRECTB.It provides the best path for deliveryC.It determines network addressesD.It provides error-correcting60.What is the most efficient subnet mask to use on point-to-point WAN links?A.255.255.255.0B.255.255.255.224C.255.255.255.252 CORRECTD.255.255.255.248*************************61.Given the cutoff frequency is 3000Hz, the bit rate b=9600 bits/s, then the time required to send 8 bits 1 bit at a time will be 8/b sec, so the number of the highest harmonic passed through isA. 1C. 2.5D. 2062.If two codewords are a Hamming distance 2d+1 apart, it will require single-bit errorsto convert one into the other. Error-correcting can be done while bit-errors are atmost .A.2d, d+1B. 2d, dC.2 d+1, d CORRECTD. None of the above63.For sliding window protocol using go back N, supposing the sender window’s size is 16, then at most frames may be outstanding at any instant.A. 0B. 1C. 15 CORRECTD. 1664.If the physical line is poor, which of the following protocols may be work better?A. Stop-and -WaitB. One-Bit Sliding Window ProtocolC. Sliding Window Protocol Using Go Back ND. Sliding Window Protocol Using Selective Repeat CORRECT65.Services provided by Ethernet are unreliable. If the destination station receive a error data frame, it 。
计算机网络双语试题及答案
计算机网络双语试题及答案一、选择题(共20题,每题2分,共40分)1. 当使用HTTP协议进行通信时,下列哪个是无连接的协议?A. TCPB. IPC. UDPD. FTP2. 在计算机网络中,IP地址的作用是什么?A. 标识主机在网络中的唯一地址B. 实现数据的可靠传输C. 进行主机之间的通信D. 提供远程访问服务3. 下列哪个不属于网络拓扑结构的类型?A. 总线型拓扑B. 环形拓扑C. 星型拓扑D. 布线型拓扑4. 在TCP/IP协议中,下列哪个协议用于将IP地址转换为物理地址?B. DHCPC. FTPD. ICMP5. 在计算机网络中,HTTP和HTTPS协议之间的区别是?A. HTTP使用明文传输,HTTPS使用加密传输B. HTTP使用UDP传输,HTTPS使用TCP传输C. HTTP使用IP地址,HTTPS使用域名D. HTTP使用GET请求,HTTPS使用POST请求6. 某计算机的IP地址是192.168.0.1,子网掩码是255.255.255.0,那么该计算机所在的网络号是?A. 192.168.0B. 192.168.0.1C. 192.168.0.255D. 192.168.0.07. 在计算机网络中,下列哪个协议用于将域名解析为IP地址?A. DNSB. FTPC. DHCP8. 在TCP/IP协议中,下列哪个协议用于控制数据传输的可靠性?A. ICMPB. UDPC. FTPD. TCP9. 在计算机网络中,什么是反向代理服务器(Reverse Proxy Server)?A. 将外部网络请求转发给内部服务器的服务器B. 将内部网络请求转发给外部服务器的服务器C. 将HTTP请求转发给HTTPS服务器的服务器D. 将HTTPS请求转发给HTTP服务器的服务器10. 在计算机网络中,下列哪个协议用于电子邮件的发送和接收?A. SMTPB. POP3C. HTTPD. FTP11. 在计算机网络中,下列哪个协议用于文件传输?B. SMTPC. UDPD. TCP12. 以下哪个不是IPv6地址的特点?A. 128位长度B. 冒号分隔的十六进制C. 有固定的网络号和主机号D. 全球唯一的地址13. 在计算机网络中,下列哪个技术不属于无线局域网技术?A. Wi-FiB. BluetoothC. NFCD. 4G14. 在网络中,下列哪个设备用于将不同网段的数据转发到目的主机?A. 集线器B. 路由器D. 网关15. 下列哪个网络拓扑结构具有较高的可容错性和可拓展性?A. 星型拓扑B. 总线型拓扑C. 环形拓扑D. 树型拓扑16. 在计算机网络中,下列哪个协议用于互联网上的主机进行网络配置?A. DHCPB. DNSC. HTTPD. FTP17. 在TCP/IP协议中,下列哪个协议用于检测并纠正数据传输中的错误?A. TCPB. ARPC. ICMPD. UDP18. 下列哪个是网络安全的常见攻击方式之一?A. DDoS攻击B. 数据库攻击C. 剪贴板攻击D. 社会工程学攻击19. 下列哪个不是局域网(LAN)的特点?A. 覆盖范围较小B. 速度较快C. 价格较高D. 结构较简单20. 在计算机网络中,下列哪个协议用于向局域网中的所有主机广播消息?A. UDPB. TCPC. DHCPD. ICMP二、问答题(共5题,每题10分,共50分)1. 请简要介绍HTTP协议的工作原理。
计算机网络试卷及答案-英文版
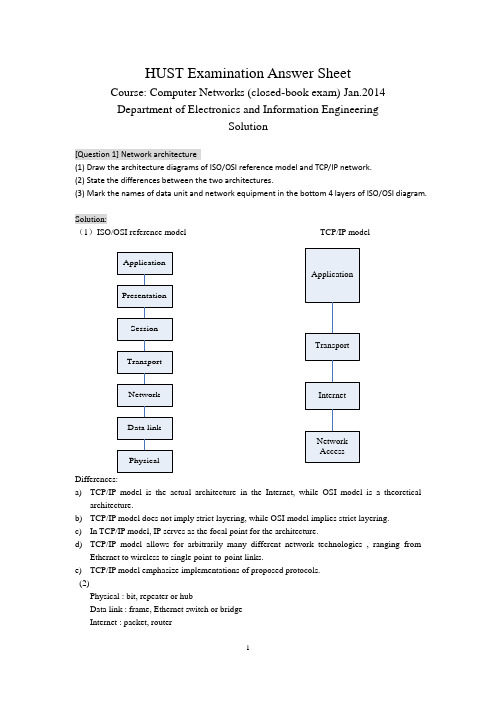
HUST Examination Answer SheetCourse: Computer Networks (closed-book exam) Jan.2014 Department of Electronics and Information EngineeringSolution[Question 1] Network architecture(1) Draw the architecture diagrams of ISO/OSI reference model and TCP/IP network. (2) State the differences between the two architectures.(3) Mark the names of data unit and network equipment in the bottom 4 layers of ISO/OSI diagram.Solution:(1)ISO/OSI reference model TCP/IP modelDifferences:a) TCP/IP model is the actual architecture in the Internet, while OSI model is a theoreticalarchitecture.b) TCP/IP model does not imply strict layering, while OSI model implies strict layering. c) In TCP/IP model, IP serves as the focal point for the architecture.d) TCP/IP model allows for arbitrarily many different network technologies , ranging fromEthernet to wireless to single point-to-point links.e) TCP/IP model emphasize implementations of proposed protocols. (2)Physical : bit, repeater or hubData link : frame, Ethernet switch or bridge Internet : packet, routerTransport : message, gateway[Question 2] Principles of network designSelect ONE of the following principles, tell its main ideas and provide an example. (1) Keep it simple and stupid(2) Complex edge and simple core (3) Smart sender and dumb receiverSolution:(1) KISS: Keep It Simple and StupidIt means that you should make things simple in the designing. One example following it : Ethernet(2) Complex edge and simple coreIt means that the hosts are very complex and have many functions while the nodes are very simple and have few functions.One example following it : The design of router, or the functions of TCP and IP(3) Smart sender and dumb receiverIt means that the function of sender is more complex than that of the receiver, which is help to improve the robustness and performance of communication protocol. One example following it: The flow control of TCP protocol[Question 3] Error detection(1) Tell the main idea of error detection and error correction in communication.(2) Given the CRC polynomial x 4 + x 3 + 1, if the original message is 10110011010, what is the CRC message to send?(3) Suppose the first bit of the message in (2) is inverted due to the noise in transmission. How can the receiver detect it via CRC verification?Solution:(1)1087431()M x x x x x x x =+++++, 43()1C x x x =++. So k=4.a) Multiply M(x) by 2kto get 141211875()T x x x x x x x =+++++,b) Then divide T(x) by C(x) to get the remainder 0000.c) The message that should be transmitted is 101100110100000.(2)The message received is 001100110100000.Divide it by C(x), then the remainder is 1100.So it is not divisible by C(x).So the receiver knows that an error has occurred.(1) What are the essential components to realize reliable transmission?(2) Suppose two computers are communicated via Stop-and-wait protocol. The link bandwidth is 5kbps, and the one-way propagation delay is 20ms. To reach 80% or higher link utilization, what is the minimal frame size for this communication?(3) If it is upgraded to Sliding-Window protocol. To reach the same goal with (2), what is the minimal window size, how many bits are required to describe the frame sequence in window? (Suppose the frame size is 1 or 100Byte)Solution:(1)ACK, and timerActual_throughput = Data / Total_DelayTotal_Delay = RTT + Data / BWLink_Utilization = 100 * Actual_throughput / BWSo: Data/throughput = RTT + Data/BW(BW/throughput - 1) Data = BW*RTTData = BW*RTT/(1/Utilization -1)For the stop-and-wait protocol, for each RTT only one frame is sent,Thus Frame_size = Data = BW*RTT/(1/Utilization - 1) = 5kbps * 40ms / (1/0.8 - 1)= 200 bit / 0.25 = 800 bit = 100 ByteIf the students ignore the data transmission delay, their answer isframe_size = BW*RTT*Utilization = 5000 bit/sec * 40 / 1000 sec * 0.8 = 160 bit = 20 ByteIn this case, at least -2 score.(3)For the sliding-window protocol, in each RTT the data window can be transmitted at most.Thus Window_size = Data = BW*RTT/(1/Utilization - 1) = 5kbps * 40ms / (1/0.8 - 1)= 200 bit / 0.25 = 800 bit = 100 ByteIf the frame size is 100Byte, 1 frames are allowed.To indicate the frames in both sides of sender and receiver, the sequence number should describe 2 frames, thus the [log2(2) ]=1 bitIf the students ignore the data transmission delay, their answer iswindow_size = BW*RTT*Utilization = 5000 bit/sec * 40 / 1000 sec * 0.8 = 160 bit = 20 ByteIf the frame size is 100Byte, 1 frames are allowed.To indicate the frames in both sides of sender and receiver, the sequence number should describe 2 frames, thus the [log2(2) ]=1 bitIn this case, at least -2 score.(1) What is the main idea of CSMA/CD (Carrier Sense Multiple Access/Collision Detection) in traditional Ethernet? Can it be deployed for wireless local network, why?(2) Suppose one traditional Ethernet has 1km cable, the signal propagation speed is 2*105km/s, and the transmission rate is designed to be 100Mbps. What is the minimal frame size to support carrier sensing?Solution:(1) the main idea of CSMA/CD include two parts. One is carrier sensing, which means the node should detect the channel before sending any data. If the node finds the channel is idle, it begins to transmit. Otherwise, the node stop for next round. The second issues is collision detection, which means the node should detect the channel in the duration of its data transmission. If the node finds the channel become busy, or in other word, there is a collision, it should stop transmitting immediately.CSMA/CD cannot be deployed in wireless LAN, because the wireless radio transmitter and receiver can not work in dual mode. The wireless node cannot detect collision when it is transmitting data.(2)the minimal frame should be transmitted throughout the whole traditional Ethernet.Thus t = frame_size / transmit_rate = 2 * cable_length / prop_speed.Frame_size = 100 * 106 bits/sec * 2 * 103 m / (2 * 108)m/sec = 1000 bits = 125 Byte[Question 6] Switched network(1) What are the differences between circuit switching and packet switching?(2) For the following linear topology network, each link has 2ms propagation delay and 4 Mbps bandwidth.A B C DIf we use circuit switching, circuit setup requires a 1KB message to make one round-trip on the path, which incurs a 1ms delay at each switch after the message has been completely received. Then we can send the file as one contiguous bit stream. What is the delay for circuit switching to transmit n-byte from A to D?(3) If we use packet switching in the network of (2), we can break the file into 1KB packets, which has 24byte header and 1000byte payload. The switch takes 1ms process delay after receiving the packet, and then sent it continuously. What is the condition for packet switching to have less delay performance than circuit switching?Solution:(1)(2)T pkt = Packet_Size / Bandwidth = 1 KB / 4Mbps = 1024 *8 / (4 * 106) = 2.048 ms T p = 2 ms, T s = 1 ms,T t = n B / 4MbpsIn circuit switching, Total time duration:D = Singling_Delay + Transmission_Delay = 2 * Packet_Duration + Transmission_Delay = 2 * (T pkt * 2 + T p * 3 + T s * 2 + T pkt ) + (T p * 3 + T t ) = T pkt * 6 + T p * 9 + T s * 4 + T tThus, D = 2.048 * 6 + 2 * 9 + 1 * 4 + n * 8 bits / 4Mbps = 34.288 (ms) + 2n (us)(3)Main ideaThe reliability provided by endhost The reliability provided by thenetwork Information in packet Every packet has its dest-addrin header Every packet has its temp VCIlocally Forwarding action inswitch Every packet was treatedindependentlyThe packets are processed inthe manner of VCPackets received indestinationNot in sequenceIn sequenceT pkt = Packet_Size / Bandwidth = 1 KB / 4Mbps = 1024 *8 / (4 * 106) = 2.048 msT p = 2 ms,T s = 1 ms,T t = 1.024 * n B / 4MbpsIn packet switching, Total time duration:D = Delay_at_Switch * Switch_Num + Delay_at_last_hop= (T p + T pkt +T s)*2 + (T p + T t )= T pkt * 2 + T p * 3 + T s * 2 + T tThus, D = 2.048 * 2 + 2 * 3 + 1 * 2 + 1.024 * n B / 4Mbps= 12.096 (ms) + 2.048 n (us)In order to make34.288 (ms) + 2n (us) > 12.096 (ms) + 2.048 n (us)Thus 22.192(ms) > 0.048 n(us)n < 22.192 * 1000 / 0.048 = 462333 Byte = 451.5 KB[Question 7] Ethernet Switch(1) What are the differences between hub and switch in Ethernet?(2) Suppose one server and nine clients are connected via hub in 10Mbps Ethernet, what is the maximal bandwidth for the client-server connection?(3) If the hub is upgraded to switch, can the client-server connection obtain more bandwidth? if can, how much is it?Solution:(1)hub works in Layer2, it works as the shared media and relays the frames to all the nodes connecting to hub. Switch works in Layer2, it forwards the frames to the specific node according to the destination address embedded in the frame header.(2)the max bandwidth in client-server connection is 10Mbps/(1+9)= 1Mbps(3)the max bandwidth in client-server connection is 10Mbps/9 = 1.1111MbpsAdditional 0.1111 Mbps is obtained for each connection.[Question 8] Router(1) Somebody says that, ``the only difference between switch and router is that they do switch function based on the address in different layers.’’ Is it correct? Why?(2) If we obtain the following information from one router. What kind of routing protocol does itSolution:(1)it is not fully correct. The part talking about the forwarding function is correct, while it is not the only difference. Another but not the last difference is that, router has more functions on control plane, which do routing and find the paths for packets.(2)The routing protocol is RIP.The routing table is:Destination Next hop Interface192.168.1.0/24 * Fa 0/4192.168.2.0/24 * Fa 0/6192.168.10.0/24 192.168.1.1 Fa 0/4192.168.30.0/24 192.168.2.2 Fa 0/6[Question 9] Routing algorithm(1) State the main differences between distance vector routing and link state routing.(2) For the network given in the following figure, provide the steps of forward search in Dijkstra algorithm for node A finding the shortest path to node ESolution:(1) The idea of distance vector routing is to tell the neighbors about the learned topology to all the nodes in the network. The idea of link state routing is to tell all the nodes in network about the neighborhood topology.Step 1 2 3 4 5 6 7 8 9Confirmed (A,0,-) (A,0,-) (A,0,-)(D,2,D)(A,0,-)(D,2,D)(A,0,-)(D,2,D)(B,4,D)(A,0,-)(D,2,D)(B,4,D)(A,0,-)(D,2,D)(B,4,D)(E,6,D)(A,0,-)(D,2,D)(B,4,D)(E,6,D)(A,0,-)(D,2,D)(B,4,D)(E,6,D)(C,7,D)Tentative (B,5,B)(D,2,D)(B,5,B) (B,4,D)(E,7,D)(E,7,D)(E,6,D)(C,8,D)(C,8,D) (C,7,D)A→E A→D→EA→D→B→EA→D→B→E[Question 10] IP address allocationA company has one C class IP address of 200.1.1.*. It has four departments.(1) If each department has less than 25 computers. Provide a kind of IP address allocation. Give the network address, subnet mask, and the available IP address range for each department. (2) If the four departments have 72, 35, 34, 20 computers respectively. Provide the IP address allocation scheme again.Solution:(1)Since each department has less than 25 computers, even considering the additional two more IP address for gateway and broadcast, the 64-computer subnet is enough for them.One IP address allocation scheme is to even divide the 256 IP addresses into 4 subnets, each subnet allows 64 hosts.Another IP address allocation scheme is to even divide the 256 IP addresses into 4 subnets, each subnet allows 32 hosts.(2) Since one of the department has more requirements than 64, then the even distribution scheme[Question 11] TCP protocol(1) Somebody says that, ``because of the reliable transmission service in layer 2, there is no need to provide such service again within TCP protocol in layer 4’’. Is it correct? Why?(2) State the main rules of TCP connection setup according to the following figure. Explain every word and number in the figure.Solution:(1) It is wrong. TCP is based on the un-reliable IP layer, which only provides best effort service. If TCP wants to provide reliable transmission service, it has to realize this by itself.(2)TCP use three hand-shakes to setup the connection.According to the figure, there are two nodes. The sender is with IP address of 192.168.1.163 and the receiver 192.168.1.165 respectively.●At first, the sender send a request ``SYN’’to the receiver to setup the connection. Thismessage is with the sequence number of 424CF1DC;●Secondly, the receiver reply an acknowledgment message ``SYN/ACK’’ to the sender. Thismessage has two sequence numbers. The seq in the ACK is 424CF1DD, which is to confirm the last ``SYN’’ from sender. The seq in the SYN is 30318555, which is a new message from the receiver.●Thirdly, the sender reply an acknowledgment message ``ACK’’ to the receiver. The seq in theACK is 30318556, which is to confirm the last ``SYN’’ from receiver.In the end, both the sender and receiver knows that the other side is ready for this TCP connection.[Question 12] TCP congestion control(1) Both flow control and congestion control in TCP are realized by window based packet control. How can TCP get the window sizes in these two mechanisms?(2) Assume that TCP implements an extension that allows window sizes much larger than 64 KB. Suppose that you are using this extended TCP over a 1Gbps link with a latency of 150ms. TCP packet size is 1KB, and the max receive window is 1 MB. Suppose there is no real congestion and packet loss in transmission. How many RTTs does it take until slow start opens the send window to 1 MB? How long does it take to send the complete file? ( Suppose file size is 10MB )Solution:(1) In flow control, TCP sender knows the window size by the field of advertise-window replied from the receiver. In congestion control, TCP sender learns the window size adaptively by AIMD( Additive Increase and Multiplicative Decrease) mechanism responding to the packet lossevent.(2)When TCP realizes congestion control mechanism, its effective send window size will be min (CongestionWindow, AdvertizedWindow). In original design of TCP header, the field of AdvertizedWindow is 16 bit, which is 216=26*210=64 KB. So the maximum effective window of original TCP sender is 64KB. The assumption of the first sentence in this question relaxes such constraint for TCP.In slow start, the send window starts from w0=1 packet, which is 1 KB. For each RTT after a successful transmission, the window size will be doubled. After i RTT, it will be 2i * w0. Let 2i * 1KB = 1MB, soi = log2(1MB/1KB) = log2(210) = 10.It will take 10 RTTs to reach 1MB send window.Case 1: if the receiver window remains as 1MBIn the first 10 RTTs, total (1 + 2 + 4 + … + 210) * 1KB has been transmitted.Which is (211 - 1) * 1KB = 2 MB - 1 KB, the rest file is 10MB - (2MB - 1KB) = 8MB + 1KBIn the reset transmission, each RTT can only support 1MB transmission.Thus, additional 9 RTTs are required. Total 19 RTT = 19 * 150ms = 2.85 sCase 2: if the receiver window can be changed.Since there is no congestion and loss, the maximum send window will be the bandwidth * delay for this TCP connection.w max= 1G bps * 150ms = 109 * 150 * 10-3= 150 *106 bit = 18.75 * 106 byte = 17.88 MB.So, this 10 MB file can be transferred before reaching w max. In another word, it can be sent in its slow start phase. Assume x RTT is required to send this file, then:(1 + 2 + 4 + … + 2x) * 1KB ≥ 10 MB2 * 2x–1 ≥ 10 * 1024x ≥ log2(10241) – 1 = 12.3Thus x = 13, it will take 13 RTTs to transfer this file. 13RTT = = sTotal delay = 13RTT + Filesize/BW = 13 * 150ms+ 10MB / 1Gbps =1.95 + 0.08 * 1.024^2=2.03 s11。
计算机网络英文复习题
计算机⽹络英⽂复习题、英译汉(10分)1.TCP(Transmission Control Protocol) 传输控制协议2.IP(Internet Protocol) 互联⽹协议3.RFC(Requests for comments) 请求评议4.SMTP(Simple Mail Transfer Protocol) 简单邮件传输协议5.Congestion-control 拥塞控制6.Flow control 流控制7.UDP (User Datagram Protocol) ⽤户数据报协议8.FTP(File Transfer Protocol) ⽂件传输协议9.HTTP( Hyper-Text Transfer Protocol ) 超⽂本传输协议10.TDM 时分复⽤11.FDM 频分复⽤12.ISP(Internet Service Provider) 互联⽹服务提供商13.DSL(Digital Subscriber Line) 数字⽤户线路14.DNS(Domain Name System) 域名系统15.ARQ(Automatic Repeat Request) ⾃动重发请求16.ICMP(Internet Control Message Protocol) ⽹间控制报⽂协议17.AS(Autonomous Systems) ⾃制系统18.RIP(Routing Information Protocol)\ 路由信息协议19.OSPF(Open Shortest Path First) 开放最短路径优先20.BGP (Border Gateway Protocol) 边界⽹关协议21.HFC 光纤同轴电缆混合⽹22.CRC(Cyclic Redundancy Check) 循环冗余检验23.CSMA/CD 带冲突检测的载波侦听多路存取24.ARP 地址解析协议25.RARP 反向地址解析协议26.DHCP 动态主机配置协议27.RTT 循环时间28.IETF(P5)互联⽹⼯程任务组29.URL(P88)统⼀资源定位30.API应⽤程序编程接⼝31.MIME多⽤途互联⽹邮件扩展1. DSL divides the communication link between the home and the ISP into three nonoverlapping frequency bands, a upstream channel is in _A_________.A)50 kHz to 1MHz band B) 1MHz to 2MHz bandC)4 kHz to 50kHz band D) 0 to 4kHz band2. As a data packet moves from the upper to the lower layers, headers are A .A) Added; B) subtracted; C) rearranged; D) modified3. What is the main function of the network layer? DA) node-to-node delivery; B) process-to-process message deliveryC) synchronization; D) updating and maintenance of routingtables4. Which of the following is the default mask for the address 168.0.46.201? BA) 255.0.0.0; B) 255.255.0.0; C) 255.255.255.0; D) 255.255.255.2555.A router reads theaddress on a packet to determine the next hop. AA) IP ; B) MAC; C) source; D)ARP6 .Which device can’t isolates the departme ntal collision domains. AA) Hub; B) switch; C) router; D) A and B7. Input port of a router don’t perform ____D____ functions.A) the physical layer functions B) the data link layer functionsC) lookup and forwarding function D) network management8. HTTP has a mechanism that allows a cache to verify that its objects are up to date. The mechanism is DA) persistent connections B) cookies C) Web Caching D) conditional GET9. A protocol layer can be implemented in ___D_____.A) software B) hardware C) a combination of the software and hardware D) All of the above10. A protocol has three important factors, they are_A______.A)syntax, semantics, order B) syntax, semantics, layerC)syntax, semantics, packet D) syntax , layer, packet11. There are two broad classes of packet-switched networks: datagram networks and virtual-circuit networks. The virtual-circuit networks forward packets in their switches use ___D___.A) MAC addresses B) IP addressesC) e-mail addresses D) virtual-circuit numbers12. TCP service model doesn’t provide ___D_______service.A) reliable transport service B) flow control serviceC) congestion-control service D) guarantee a minimum transmission rate service.13. Usually elastic applications don’t include____B______.A) Electronic mail B) Internet telephony14. A user who uses a user agent on his local PC receives his mail sited in a mail server by using _B___ protocol.A)SMTP B) POP3C)SNMP D) FTP15. Considering sliding-window protocol, if the size of the transmitted window is N and the size of the receiving window is 1,the protocol is BA) stop-and-wait protocol B) Go-Back-N protocolC) selective Repeat protocol D) alternating-bit protocol16. which IP address is effective___B______.A) 202,131,45,61 B) 126.0.0.1C) 192.268.0.2 D) 290.25.135.1217. if IP address is 202.130.191.33, subnet mask is 255.255.255.0,then subnet prefix is__D_____A) 202.130.0.0 B) 202.0.0.0C) 202.130.191.33 D)202.130.191.018.The command Ping s implemented with __B______messagesA) DNS B) ICMPC) IGMP D) RIP19. Which layer-function is mostly implemented in an adapter? __A________A) physical layer and link layer B) network layer and transport layerC)physical layer and network layer D) transport layer and application layer20. If a user brings his computer from Chengdu to Peking, and accesses Internet again. Now, __B_____ of his computer needs to be changed.A) MAC address B) IP addressC) e-mail address D) user address1. .traceroute is implemented with __B____messages.A) DNS B) ICMPC) ARP D) RIP2.A router reads the A address on a packet to determine the next hop.A. IP ;B. MAC;C. source;D.ARP3. There are two broad classes of packet-switched networks: datagram networks andvirtual-circuit networks. The virtual-circuit networks forward packets in their switches use ___D___.A) MAC addresses B) IP addressesC) e-mail addresses D) virtual-circuit numbersA) device interfaces with same subnet part of IP addressB) can’t physically reach each other without intervening a router.C)all of the devices on a given subnet having the same subnet address.D)A portion of an interface’s IP address must be determined by the subnet to which it is connected.5. if IP address is 102.100.100.32, subnet mask is 255.255.240.0,then subnet prefix is___A___A) 102.100.96.0 B) 102.100.0.0C) 102.100.48.0 D) 102.100.112.06 If a user brings his computer from chengdu to beijing, and accesses Internet again. Now,___B__ of his computer needs to be changed.A) MAC address B) IP addressC) e-mail address D) user address7.I nput port of a router don’t perform ____D___ functions.A) the physical layer functions B) the data link layer functionsC) lookup and forwarding function D) network management8.switching fabric is at the heart of a router, switching can be accomplished in a number of ways, donit include_D_A)Switching via memory B)Switching via crossbarC)Switching via a bus D) Switching via buffer9.if a host wants to emit a datagram to all hosts on the same subnet, then the datagram’s destination IP address is ___B__A)255.255.255.0 B) 255.255.255.255C)255.255.255.254 D) 127.0.0.110.The advantage of Circuit switching does not include________.A) small transmission delay B)small Processing costC) high link utilization D)no limited to format of message1.an ARP query sent to __A__A) local network B) all over the Internet.2. .packet-switching technologies that use virtual circuitsinclude__B___:A) X.25, ATM, IP B) X.25, ATM, frame relay.C) IPX, IP, ATM D) IPX, IP, TCP3. In Internet, _D_ protocol is used to report error and provide the information forun-normal cases.A) IP B) TCP C)UDP D) ICMP1.A is a Circuit-switched network.B. Datagram networkC. InternetD. virtual circuit network2.The store-and-forward delay is DA. processing delayB. queuing delayC. propagation delayD. transmission delay3.Which is not the function of connection-oriented service? DA. flow controlB. congestion controlC. error correctionD. reliabledata transfer4.The IP protocol lies in CA. application layerB. transport layerC. network layerD. link layer5.Which of the following is the PDU for application layer __B___A.datagram;B. message;C. frame;D.segment6.bandwidth is described in _B__A) Bytes per second B) Bits per secondC) megabits per millisecond D) centimeters7.A user who uses a user agent on his local PC receives his mail sited in a mail server by using __A__ protocol.A)SMTP B) POP3C)SNMP D) FTP8.As a data packet moves from the lower to the upper layers, headers are B.A)Added; B. subtracted; C. rearranged; D. modified三、填空题(每空1分,共22分 (注意:所有填空题不能写中⽂,否则中⽂答案对的情况1. link-layer address is variously called a LAN address, a MAC address, or a physical address.2 In the layered architecture of computer networking, n layer is the user of n-1 layer and the service provider of n+1 layer.A) n B) n+3 C) n+1 D) n-1四、判断题(每⼩题1分,共10分)1.√The services of TCP’s reliable data transfer founded on the services of theunreliable data transfer.2.√Any protocol that performs handshaking between the communication entitiesbefore transferring data is a connection-oriented service.3.× HOL blocking occur in output ports of router.4.√Socket is globally unique.5.√SMTP require multimedia data to be ASCII encoded before transfer.6.×The transmission delay is a function of the distance between the two routers.7.×IP address is associated with the host or router. SO one device only have one IPaddress.8. √In packet-switched networks, a session’s messages use the resources on demand, and Internet makes its best effort to deliver packets in a timely manner.9. ×UDP is a kind of unreliable transmission layer protocol, so there is not any checksum field in UDP datagram header.10.√Forwarding table is configured by both Intra and Inter-AS routing algorithmIP is a kind of reliable transmission protocol. F8.Forwarding table is configured by both Intra and Inter-AS routing algorithm.T9.Distance vector routing protocol use lsa to advertise the network which router10.RIP and OSPF are Intra-AS routing protocols T11.Packet switching is suitable for real-time services, and offers better sharing ofbandwidth than circuit switching F五、计算题(28 points)1.C onsider the following network. With the indicated link costs, use Dijkstra’s shortest-path algorithm to compute the shortest path from X to all network nodes.2 Given: an organization has been assigned the network number 198.1.1.0/24 and it needs todefine six subnets. The largest subnet is required to support 25 hosts. Please:●Defining the subnet mask; (2分) 27bits or 255.255.255.224●Defining each of the subnet numbers; which are starting from 0# (4分)198.1.1.0/27 198.1.1.32/27 198.1.1.64/27 198.1.1.96/27 198.1.1.128/27 198.1.1.160/27 198.1.1.192/27 198.1.1.224/27●Defining the subnet 2#’s broadcast address.(2分) 198.1.1.95/27Defining host addresses scope for subnet 2#. (2分) 198.1.1.65/27--198.1.1.94/273. Consider sending a 3,000-byte datagram into a link that has an MTU of 1500bytes.Suppose the original datagram is stamped with the identification number 422 .Assuming a 20-byte IP header,How many fragments are generated? What are their characteristics?(10分)。
计算机网络英文题库附答案chater
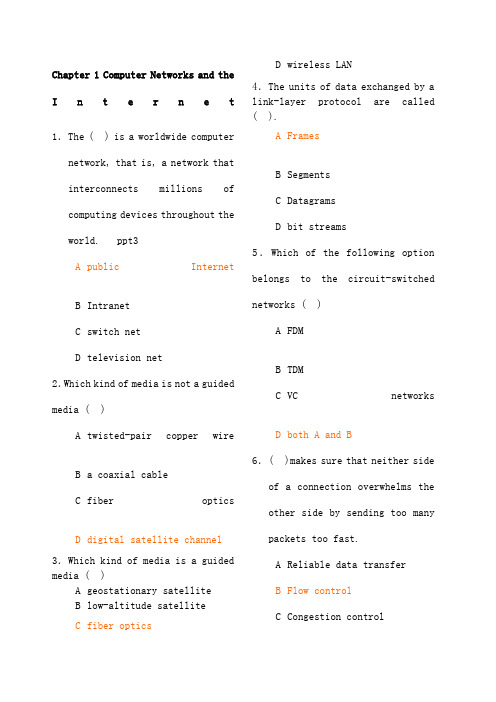
Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computernetwork, that is, a network that interconnectsmillionsofcomputing devices throughout theworld. ppt3 A public InternetB IntranetC switch netD television net2.Which kind of media is not a guidedmedia ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following optionbelongs to the circuit-switchednetworks ( )A FDMB TDMC VCnetworksD both A and B 6.( )makes sure that neither sideof a connection overwhelms theother side by sending too manypackets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch mustreceive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagramnetworksandvirtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, and virtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, and virtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuit networks use VC. numbers to forward packets toward their destination.D datagram networks use VC. numbers and virtual-circuit networks use destination addresses to forward packetstoward their destination.9.In the following options, which one is not a guided media ( )A twisted-pairwireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet ’s headerB wait to transmit the packet onto the linkC determine where to direct thepacketD check bit-error in the packet 11.In the following four descriptions, which one is correct ( )A The traffic intensity must begreater than 1.B The fraction of lost packetsincreases as the trafficintensity decreases.C If the traffic intensity isclose to zero, the averagequeuing delay will be close tozero.D If the traffic intensity isclose to one, the averagequeuing delay will be close toone.12.The Internet’s network layer is responsible for movingnetwork-layer packets known as( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layersare called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes ofpacket-switched networks: ( )networks and virtual-circuitnetworks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be looselyclassified into threecategories: residential access,company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue,R is the transmission rate, and all packets consist of L bits, then thetraffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR /aB La /RC Ra /LD LR /a 17.A 2B 1C 0D -118.In the Internet, the equivalentconcept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics 20.End systems access to the Internet through its ( ). A modemsB protocolsC ISPD sockets21.End systems, packet switches,and other pieces of the Internet, run ( ) that control thesending and receiving ofinformation within theInternet.A programsB processesC applicationsD protocols22.There are many private networks,such as many corporate andgovernment networks, whosehosts cannot exchange messages with hosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) runningon its end systems to exchangedata with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionlessunreliable service and ()service.A flowcontrolB connection-oriented reliableC congestion controlD TCP25.It defines the format and theorder of messages exchangedbetween two or morecommunicating entities, as wellas the actions taken on thetransmission and/or receipt ofa message or other event. Thesentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol ( )A the format of messagesexchanged between two or morecommunicating entitiesB the order of messagesexchanged between two or morecommunicating entitiesC the actions taken on thetransmission of a message orother eventD the transmission signals aredigital signals or analogsignals27.In the following options, which is defined in protocol ( )A the actions taken on thetransmission and/or receiptof a message or other event B the objects exchanged between communicating entities C the content in the exchangedmessagesD the location of the hosts28.In the following options, whichdoes not belong to the network edge( )A end systemsB routersC clientsD servers29.In the following options, whichbelongs to the network core ( )A end systemsB routersC clientsD servers30.In the following options, whichis not the bundled with theInternet’sconnection-oriented service( )A reliable data transferB guarantee of thetransmission timeC flow controlD congestion-control31.An application can rely on theconnection to deliver all of itsdata without error and in theproper order. The sentencedescribes ( ). A flow controlB congestion-controlC reliable datatransferD connection-oriented service 32.It makes sure that neither sideof a connection overwhelms theother side by sending too manypackets too fast. The sentence describes ( ). A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internetfrom entering a state of gridlock. When a packet switchbecomes congested, its bufferscan overflow and packet loss canoccur. The sentence describes( ).A flowcontrolB congestion-controlC connection-oriented serviceD reliable data transfer 34.TheInternet ’sconnection-oriented service has aname, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet ’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP( )A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP( )A InternetphoneB video conferencingC streamingmultimediaD telnet39.There are two fundamentalapproaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resourcesneeded along a path to provide for communication between the end system are reserved for theduration of the communicationsession.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’smessages use the resources ondemand, and as a consequence,may have to wait for access tocommunication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, foreach link used by the end-to-endconnection, the connection gets( ) of the link’s bandwidthfor the duration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rateof a circuit is equal to theframe rate multiplied by thenumber of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch mustreceive the entire packetbefore it can begin to transmitthe first bit of the packet ontothe outbound link.A Queuing delayB Store-and-forwardtransmissionC Packet lossD Propagation45.The network that forwardspackets according to host destination addresses is called( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwardspackets according tovirtual-circuit numbers iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, whichis not a kind of access network( )A residentialaccessB company accessC wirelessaccessD local access48.Suppose there is exactly onepacket switch between a sendinghost and a receiving host. The transmission rates between thesending host and the switch and between the switch and the receiving host are R 1 and R 2,respectively. Assuming that theswitch uses store-and-forwardpacket switching, what is thetotal end-to-end delay to senda packet of length L (Ignorequeuing delay, propagationdelay, and processing delay.) ( ) A L /R 1+L /R 2B L /R 1C L /R 2D none of the above49.The time required to examine thepacket ’s header and determinewhere to direct the packet ispart of the ( ). A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagatefrom the beginning of the linkto the next router is ( ). A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of3000bits over a path of 5 links. Eachlink transmits at 1000bps. Queuingdelays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is apacket-switched virtual circuitnetwork. VC setup time is seconds.Suppose the sending layers add atotal of 500 bits of header to eachpacket. How long does it take to sendthe file from source to destination(2).Suppose the network is a packet-switched datagram networkand a connectionless service is used.Now suppose each packet has 200 bitsof header. How long does it take tosend the file(3).Suppose that the network is acircuit-switched network. Furthersuppose that the transmission rate of the circuit between source anddestination is 200bps. Assumingsetup time and 200 bits of header appended to the packet, how longdoes it take to send the packetS olution:(1).t=5*(3000+500)/1000+=( 2).t=5*(3000+200)/1000=16s( 3).t=(3000+200)/200+=。
最新计算机网络英文题库(附答案)chapter1word版本

Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world.ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media? ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media? ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks? ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, andvirtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, andvirtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuitnetworks use VC. numbers to forward packets toward theirdestination.D datagram networks use VC. numbers and virtual-circuit networksuse destination addresses to forward packets toward their destination. 9.In the following options, which one is not a guided media? ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct? ( )A The traffic intensity must be greater than 1.B The fraction of lost packets increases as the traffic intensitydecreases.C If the traffic intensity is close to zero, the average queuing delaywill be close to zero.D If the traffic intensity is close to one, the average queuing delaywill be close to one.12.The Internet’s network layer is responsible for moving network-layer packets known as ( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuit networks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access, company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR/aB La/RC Ra/LD LR/a17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that control the sending and receiving of information within theInternet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks, whose hosts cannot exchange messages withhosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionless unreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messages exchanged between two or more communicating entities, as well as the actions taken on thetransmission and/or receipt of a message or other event. The sentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol? ( )A the format of messages exchanged between two or morecommunicating entitiesB the order of messages exchanged between two or morecommunicating entitiesC the actions taken on the transmission of a message or other eventD the transmission signals are digital signals or analog signals 27.In the following options, which is defined in protocol? ( )A the actions taken on the transmission and/or receipt of a message orother eventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge? ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core? ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’s connection-oriented service? ( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from entering a state of gridlock. When a packet switch becomes congested, its buffers can overflow and packet loss can occur. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP?( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP?( )A SMTPB internet telephoneC FTPD HTTP 38.In the following options, which does not use UDP?( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration of the communication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’s messages use the resources on demand, and as a consequence, may have to wait for access to communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of thelink’s bandwidth for the duration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by the number of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packets according to host destination addresses is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packets according to virtual-circuit numbers is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network?( )A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and the receiving host are R1 and R2,respectively. Assuming that the switch uses store-and-forward packetswitching, what is the total end-to-end delay to send a packet of length L? (Ignore queuing delay, propagation delay, and processing delay.)( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine the packet’s header and determine where to direct the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is ( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 200 bits of header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is 200bps. Assuming 0.02s setup time and 200 bits of header appended to the packet, how long does it take to send the packet?Solution: (1). t=5*(3000+500)/1 000+0.1=17.6s(2). t=5*(3000+200)/1 000=16s(3). t=(3000+200)/200+0.02=16.02s 相对压力一般指表压,是测量系统相对于大气压的压力值。
计算机网络英文题库(附答案)chapter1(推荐文档)

Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world.ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media? ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media? ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks? ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, andvirtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, andvirtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuitnetworks use VC. numbers to forward packets toward theirdestination.D datagram networks use VC. numbers and virtual-circuit networksuse destination addresses to forward packets toward their destination. 9.In the following options, which one is not a guided media? ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct? ( )A The traffic intensity must be greater than 1.B The fraction of lost packets increases as the traffic intensitydecreases.C If the traffic intensity is close to zero, the average queuing delaywill be close to zero.D If the traffic intensity is close to one, the average queuing delaywill be close to one.12.The Internet’s network layer is responsible for moving network-layer packets known as ( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuit networks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access, company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR/aB La/RC Ra/LD LR/a17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that control the sending and receiving of information within theInternet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks, whose hosts cannot exchange messages withhosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionless unreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messages exchanged between two or more communicating entities, as well as the actions taken on thetransmission and/or receipt of a message or other event. The sentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol? ( )A the format of messages exchanged between two or morecommunicating entitiesB the order of messages exchanged between two or morecommunicating entitiesC the actions taken on the transmission of a message or other eventD the transmission signals are digital signals or analog signals 27.In the following options, which is defined in protocol? ( )A the actions taken on the transmission and/or receipt of a message orother eventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge? ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core? ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’s connection-oriented service? ( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from entering a state of gridlock. When a packet switch becomes congested, its buffers can overflow and packet loss can occur. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP?( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP?( )A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP?( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching 40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration of the communication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’s messages use the resources on demand, and as a consequence, may have to wait for access to communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of thelink’s bandwidth for the duration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by the number of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packets according to host destination addresses is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packets according to virtual-circuit numbers is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network?( )A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and the receiving host are R1 and R2,respectively. Assuming that the switch uses store-and-forward packetswitching, what is the total end-to-end delay to send a packet of length L? (Ignore queuing delay, propagation delay, and processing delay.)( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine the packet’s header and determine where to direct the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is ( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 200 bits of header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is 200bps. Assuming 0.02s setup time and 200 bits of header appended to the packet, how long does it take to send the packet?Solution: (1). t=5*(3000+500)/1 000+0.1=17.6s(2). t=5*(3000+200)/1 000=16s(3). t=(3000+200)/20 0+0.02=16.02s。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
Computer Network Test Paper1.Who invented IP and some related Internet protocols? Ba)Vinton Cerf and Bob Metcalfeb)Vinton Cerf and Robert Kahnc)Bob Metcalfe and Ivan Sutherlandd)Bob Metcalfe and David Clark2.In the OSI reference model,3.The upper layers of the OSI model are, in correct order Ba)Session, application, presentationb)Session, presentation, applicationc)Session, application, presentation, physicald)Application, presentation, session4.The lower layers of the OSI model are, in correct order Da)physical, system, network, logicalb)physical, logical, network, systemc)physical, transport, network, data linkd)physical, data link, network, transport5.The Internet Protocol (IP) generally corresponds to which OSI layer? Aa)Network (layer three)b)Transport (layer four)c)Data link (layer two)d)Session (layer five)6.MTU stands for Ca)Minimum Transfer Unitb)Minimum Transmission Unitc)Maximum Transmission Unitd)Maximum Transfer Unit7.What layer of the OSI model is designed to perform error detection functions?Ba)Physicalb)Data linkc)Networkd)transport8.Which of these network devices primarily functions at the OSI Network layer(layer 3)? Ca)Switchb)Gatewayc)Routerd)All of the above9.What is the size of today’s standard (IPv4) IP address? Aa) 4 bytes (32 bits)b)12 bytes (96 bits)c)15 bytes (120 bits)d)16 bytes (128 bits)10.What is the size of the next-generation (IPv6) IP address?a) 4 bytes (32 bits)b)12 bytes (96 bits)c)15 bytes (120 bits)d)16 bytes (128 bits)11.Which of the following higher-level protocols runs over IP? Da)FTPb)HTTPc)SMTPd)All of the above12.Which of the following IPv4 addresses is the loopback address? Ca)0.0.0.0b)10.0.0.1c)127.0.0.1d)255.255.255.25513.Which of the following IPv6 addresses is the loopback address? Ba)0::0b)0::1c)127::0d)127::114.The length of an IP datagram header can vary depending on the options used. Whatis the smallest possible IP header size? Ba)16 bytesb)20 bytesc)24 bytesd)60 bytes15.The source IP address for an IPv4 datagram is stored where in the header?Ca)2nd longword (bytes 5-8)b)3rd longword (bytes 9-12)c)4rd longword (bytes 13-16)d)5rd longword (bytes 17-20)16.The destination IP address for an IPv4 datagram is stored where in the header?Da)2nd longword (bytes 5-8)b)3rd longword (bytes 9-12)c)4rd longword (bytes 13-16)d)5rd longword (bytes 17-20)17.The header length field in an IPv4 datagram contains the size of an IP headermeasured in number of Ca)Bitsb)Bytesc)Longwords (4 bytes)d)None of the above18.Can IP run over any other physical networks besides Ethernet? Da)No (and IP does not run over Ethernet)b)Noc)Yes (but IP does not run over Ethernet)d)Yes19.What function does Address Resolution Protocol (ARP) perform? Aa)Converts IP addresses to Ethernet addressesb)Automatically assigns IP addresses to computersc)Prevents two computers from using the same IP addressd)None of the above20.What mechanism does ARP use to resolve IP addresses? Ba)Mathematical formulab)Lookup tablec)Central web sited)Random number generator21.Which utility program is designed to report whether a networked computer isresponding at a given IP address, and how long these responses take? Ba)tracerouteb)pingc)ttcpd)netstate22.which of these shell commands supplies the IP address of a computer running theLinux operating system? Ba)ipconfigb)ifconfigc)linuxconfd)none of the above23.Which of the following technologies manage the conversion between IP addressesand host names? Ba)BGPb)DNSc)ARPd)All of the above24.CIDR stands for Da)Class-based Internet Domain Routingb)Careful Inter-Domain Routingc)Constant Internet Domain Routingd)Classless Inter-Domain Routing25.In CIDR notation, which of the following networks contains host 192.168.14.2?Ba)192.168.10.0/22b)192.168.11.0/21c)192.168.12.0/23d)192.168.13.0/2426.Which central authority is responsible for allocating IP addresses on theInternet? Ba)IETFb)IANAc)IEEEd)None of the above27.The IP delivery service is Ca)Reliable, connection-orientedb)Non-routablec)Unreliable, connectionlessd)None of the above28.TCP stands for Aa)Transmission Control Protocolb)Trivial Connection Protocolc)Traffic Control Protocold)Telephony Connection Protocol29.UDP stands for Ca)Universal Data Protocolb)Unreliable Datagram Protocolc)User Datagram Protocold)Ultimate Data Protocol30.Both TCP and UDP belong to which layer of the OSI mode? Ba)Sessionb)Transportc)Networkd)Data Link31.UDP offers which of the following benefits relative to TCP? Aa)UDP consumes fewer computer resources by not maintaining connection stateb)UDP supports a self-regulating “throttle” feature that prevents networksaturationc)UDP guarantees that Individual packets of a transmission will arrive “inorder”d)None of the above32.What is the maximum recommended length of twisted-pair Ethernet cables used inhome or business networks? Ba)10 metersb)100 metersc)1000 metersd)Other33.On Ethernet LANs, the Ethernet address is also known as the Ba)IP addressb)MAC addressc)Virtual addressd)Other34.How long is a MAC address? Ba) 4 bytesb) 6 bytesc)8 bytesd)10 bytes35.What is the basic unit of Ethernet traffic? Ba)Fileb)Framec)Packetd)Stream36.CSMA/CD stands for Aa)Carrier Sense Multiple Access with Collision Detectionb)Collision Sense Multiple Access with Carrier Detectionc)Carrier Single-Multiple Access with Collision Detectiond)Collision Single-Multiple Access with Carrier Detection37.Which of the following is a routing protocol?a)ARPb)DNSc)BGPd)SMTP38.Which of the following algorithm has the so called count-to-infinity problem?Ca)Flooding algorithmb)Link-state algorithmc)Distance vector algorithmd)None of the above39.Which of the following algorithm does BGP use? Ca)Flooding algorithmb)Link-state algorithmc)Distance vector algorithmd)None of the above40.Which of the following protocol does ICMP run over? Ca)TCPb)UDPc)IPd)Ethernet41.Which of the following describes the TCP connection establishing mechanism?Ca)One-way-handshakeb)Two-way-handshakec)Three-way-handshaked)Four-way-handshake。
