计算机网络英文题库(附答案)chapter1
计算机网络第一章客观题

计算机网络第一章客观题Computer NetworksChapter 1(答案见末尾)1.1 In the following options, which does not define in protocol? ( )A the format of messages exchanged between two or more communicating entitiesB the order of messages exchanged between two or more communicating entitiesC the actions taken on the transmission of a message or other eventD the transmission signals are digital signals or analog signals1.2 In the following options, which is defined in protocol? ( )A the actions taken on the transmission and/or receipt of a message or other eventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts1.3 An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service1.4 The Internet’s connection-oriented service has a name, it is ( ).B UDPC TCP/IPD IP1.5 The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP1.6 Which of the following nodes belongs to the network core?A. a Web ServerB. a Host with Win2003 ServerC. a Router with NAT serviceD. a Supernode on Skype Network1.7 In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers1.8 In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics1.9 End systems access to the Internet through its ( ).A modemsB protocolsD sockets1.10 In the following options, which belongs to the network core? ( )A end systemsB routersC clientsD servers1.11 End systems, packet switches, and other pieces of the Internet, run ( ) that control the sending and receiving of information within the Internet.A programsB processesC applicationsD protocols1.12 The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications1.13 The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol1.14 The lower layers of the OSI model are, in correct orderA. physical, system, network, logicalB. physical, logical, network, systemC. physical, transport, network, data linkD. physical, data link, network, transport1.15 The Internet Protocol (IP) generally corresponds to which OSI layer?A. Network (layer three)B. Transport (layer four)C. Data link (layer two)D. Session (layer five)1.16 What layer of the OSI model is designed to perform error detection functions?A. PhysicalB. Data linkC. NetworkD. transport1.17 Which of the following protocol layers is not explicitly part of the Internet Protocol Stack? _________A. application layerB. session layerC. data link layerD. transport layer1.18 The 5-PDU is called___A. messageB. segmentC. datagramD. frame1.19 The Int ernet’s network layer is responsible for moving network-layer packets known as ( ) from one host to another.A frameB datagramC segmentD message1.20 Transport-layer packets are called:A. messageB. segmentC. datagramD. frame1.21 The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams1.22 There are two fundamental approaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching1.23 Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, and virtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, and virtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuit networks use VC. numbers to forward packets toward their destination.D datagram networks use VC. numbers and virtual-circuit networks use destination addresses to forward packets toward their destination.1.24 ( ) means that the switch must receive the entire packetbefore it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM1.25 In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration of the communication session.A packet-switchedB data-switchedC circuit-switchedD message-switched1.26 In ( ) networks, the resources are not reserved; a session’s messages use the resources on demand, and as a consequence, may have to wait for access to communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched1.27 In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of the link’s bandwidth for the duration of the connection.A a fraction 1/nB allC 1/2D n times1.28 For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by thenumber of bits in a slot.A CDMAB packet-switched networkC TDMD FDM1.29 The network that forwards packets according to host destination addresses is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram1.30 The network that forwards packets according to virtual-circuit numbers is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram1.31 The time required to propagate from the beginning of the link to the next router is ( ).A queuing delayB processing delayC propagation delayD transmission delay1.32 Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet1.33 In the following four descriptions, which one is correct? ( )A The traffic intensity must be greater than 1.B The fraction of lost packets increases as the traffic intensity decreases.C If the traffic intensity is close to zero, the average queuing delay will be close to zero.D If the traffic intensity is close to one, the average queuing delay will be close to one.1.34 Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( ),A LR/aB La/RC Ra/LD LR/a1.35 Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and the receiving host are R1 and R2, respectively. Assuming that the switch uses store-and-forward packet switching, what is the total end-to-end delay to send a packet of length L? (Ignore queuing delay, propagation delay, and processing delay.) ( )A L/R1+L/R2B L/R1C L/R2D none of the above1.36 We are sending a 30 Mbit MP3 file from a source host to a destination host. Suppose there is only one link between source and destination and the link has a transmission rate of 10 Mbps. Assume that the propagation speed is 2 * 108 meters/sec, and the distance between source and destination is 10,000 km.Also suppose that message switching is used, with the message consisting of the entire MP3 file. How many bits will the source have transmitted when the first bit arrives at the destination?A. 1 bitB. 30,000,000 bitsC. 500,000 bitsD. none of the above1.37 In the following entries, which is not a kind of access network?( )A residential accessB company accessC wireless accessD local access1.38 The following technologies may be used for residential access, exceptA. HFCB. DSLC. Dial-up modemD. FDDI1.39 Which kind of media is not a guided media? ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel1.40 在OSI 参考模型中,直接为会话层提供服务的是____。
强烈推荐计算机网络英文试题库(附答案)chapter.doc
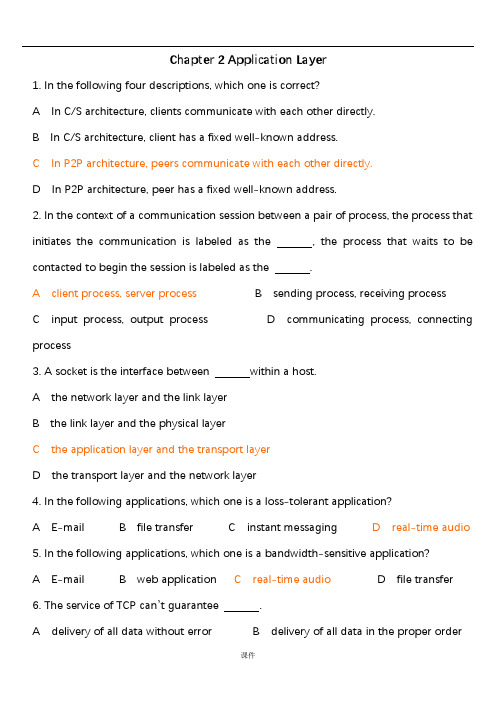
Chapter 2 Application Layer1. In the following four descriptions, which one is correct?A In C/S architecture, clients communicate with each other directly.B In C/S architecture, client has a fixed well-known address.C In P2P architecture, peers communicate with each other directly.D In P2P architecture, peer has a fixed well-known address.2. In the context of a communication session between a pair of process, the process that initiates the communication is labeled as the , the process that waits to be contacted to begin the session is labeled as the .A client process, server processB sending process, receiving processC input process, output processD communicating process, connecting process3. A socket is the interface between within a host.A the network layer and the link layerB the link layer and the physical layerC the application layer and the transport layerD the transport layer and the network layer4. In the following applications, which one is a loss-tolerant application?A E-mailB file transferC instant messagingD real-time audio5. In the following applications, which one is a bandwidth-sensitive application?A E-mailB web applicationC real-time audioD file transfer6. The service of TCP can’t guarantee .A delivery of all data without errorB delivery of all data in the proper orderC the rate of deliveryD congestion control7. In the following applications, which one uses UDP?A E-mailB web applicationC file transferD DNS8. In the following descriptions about HTTP, which one is not correct?A HTTP uses non-persistent connections in its default mode.B HTTP uses TCP as its underlying transport protocol.C HTTP is a stateless protocol.D HTTP is client-server architecture.9. Suppose a web page consists of a base HTML file, 5 JEPG images and a java applet, and also suppose HTTP uses persistent connection without pipelining, the total response time is .A 2RTTB 8RTTC 12 RTTD 14RTT10. In HTTP response message, if the requested HTTP protocol version is not supported, the status code is .A 200B 301C 400D 5051~5CACDC6~10CDABD11. The port number of web application is .A 25B 20C 80D 5312. A network entity that satisfies HTTP requests on the behalf of an origin web server is .A server farmB server stackC proxy serverD edge server13. In the following descriptions about persistent connection, which one is not correct?A The server leaves the TCP connection open after sending a response.B Each TCP connection is closed after the server sending one object.C There are two versions of persistent connection: without pipelining and with pipelining.D The default mode of HTTP uses persistent connection with pipelining.14. FTP uses two parallel TCP connections to transfer a file, there are .A control connection and data connectionB receiving connection and sending connectionC client connection and sever connectionD program connection and process connection15. In the following descriptions about FTP, which one is correct?A FTP is p2p architecture.B FTP sends its control information out-of-band.C FTP uses persistent connection.D FTP is a stateless protocol.16.In the commands of FTP,which one does not have parameter?A USERB PASSC LISTD STOR17. The Internet mail system has three components which they are .A user agent, SMTP, POP3B SMTP, POP3, IMAPC user agent, SMTP, IMAPD user agent, SMTP, mail server18. If the status code in HTTP response message is 404, it means .A Request succeeded.B The requested document doesn’t exit on this server.C This is a generic error code indicating that the request could not be understood bythe server.D Requested object has been permanently mover.19. Comparison HTTP with SMTP, the correct is .A HTTP is a push protocol, and SMTP is a pull protocol.B In the default mode, both of them use persistent connection.C HTTP places all of the message’s objects into one message, and SMTP sends every object one by one.D HTTP requires each message to be in 7-bit ASCII format, and SMTP doesn’t impose this restriction.20. The headers in the MIME message must include except .A FromB Content-typeC Content-transfer-encodingD MIME version11~15CCBAB16~20DDBBD21. In the following protocol, which one is stateless?A POP3B SMTPC FTPD IMAP22. DNS means .A Data Name SystemB Data National SystemC Domain Name SystemD Domain National System23. There are three classes of DNS server except .A Root DNS serverB Local DNS serverC TLD server D Authoritative DNS server24. DNS provides some services except .A Host aliasingB Mail server aliasingC Load distributionD A single point of failure25.There are three architectures for locating content in P2P file sharing,KaZaA uses.A Centralized Directory(Napster)B Query Flooding(Gnutella)C Exploiting Heterogeneity(p141)D Incentive Priorities26.There are three architectures for locating content in P2P file sharing,Napster uses.A Centralized Directory(p137)B Query FloodingC Exploiting HeterogeneityD Incentive Priorities27.The following architectures in P2P file sharing,which is an overlay network?A Centralized DirectoryB Query Flooding(p139)C Exploiting HeterogeneityD Incentive Priorities28. The time it takes for a small packet to travel from client to server and then back to the client is .A round-travel timeB next-hop timeC round-trip timeD prefix-matching time29. Suppose A ( with a Web-based e-mail account ) sends a message to B ( who accesses his mail server using POP3), which application-layer protocol is not used?A HTTPB SMTPC POP3D IMAP30. In the four following options, which protocol is included in Mail Access Protocol?A SMTPB DHCPC IMAPD FTP31. In FTP commands, is used to send user password to the server.A UserB PassC RetrD Stor32. The function of the additional header field in MIME Content-Type is .A to convert the message body to its origin non-ASCII formB to determine what actions it should take on message bodyC to send an E-mail to the receiving user agentD to indicate what type the message is33. In the four following options, which application is organized as hybrid of C/S and P2P architecture?A E-mailB OICQC File transferD Web application34.In the four following options,which is not a centralized DNS design’s problem?A a single point of failureB traffic volumeC distant centralized databaseD slow(maintenance)35.In the following options, from the application developer’s perspective, which is not correct?A the network architecture is fixedB the network architecture provides a specific set of services to applicationsC the application architecture is designed by the physical devicesD the application architecture dictates how the application is organized over the various end systems36. There are three predominant architectures used in modern network applications, which one is not included?A the client-server architectureB the P2P architectureC a hybrid of the client-server and P2P architectureD a hybrid of the client-server and browser-server architecture37. In the following options about C/S architecture, which is not correct?A In C/S architecture, there is an always-on host, called the server.B In C/S architecture, there is an always-on host, called the client.C The server has a fixed, well-known address, called IP address.D Clients do not directly communicate with each other.38.are often used to create a powerful virtual server in C/S architecture.A PeersB Server farmC server stackD local server39. A process sends messages into, and receives messages from, the network through its .A socketB programC clientD peer40. Which one is not defined by an application-layer protocol?A the types of messages exchangedB the syntax of various message typesC the semantics of the fieldsD rules for determining when and how to translate the socket41. HTTP can use two types of connections, which are .A persistent and non-persistent connectionB connection with pipelining and without pipeliningC TCP and UDPD parallel and serial connection42. takes for a small packet to travel from client to server and then back to the client.A RDTB thresholdC RTTD overhead43. The default mode of HTTP uses .A non-persistent connection with pipeliningB non-persistent connection without pipeliningC persistent connection with pipeliningD persistent connection without pipelining44. In HTTP request messages, the request line has three fields, there are .A the method field, the URL field and the HTTP version fieldB the method, the connection and URL fieldC the user-agent, the method and HTTP version fieldD the user-agent, the URL and the HTTP version field45. In the header lines of HTTP request message, if the field of Connection is close, it specifies .A the host on which object residesB what type of the user agentC that the browser wants the server to close the connection after sending the requested objectD which language can the browser receive46. In HTTP response message, if the status code is 404, it means .A request succeeded and the information is returned in the responseB requested object has been permanently movedC the requested HTTP protocol version is not supported by the serverD the requested document does not exist on this server47. is a network entity that satisfies HTTP requests on the behalf of an origin Web server.A proxy serverB local serverC DNS serverD Web server48. In the following four options about web cache, which one is not correct?A A web cache is both a server and a client at the same time.B A web cache is purchased and installed by an ISP.C A web cache can raise the response time for a client request.D A web cache can reduce traffic on an institution’s access link to the Internet.49. The request message in the conditional GET must include the header line.A Last-ModifiedB Last-ReferencedC If-Modified-SinceD If –Referenced-Since50. FTP uses two parallel connections to transfer a file, they are .A TCP and UDP connectionB connection with pipelining and without pipeliningC control an data connectionD client-server and browser-server connection51. In FTP commands, which one is used to ask the server to send back a list of all files in the current remote directory?A USERB PASSC LISTD RETR52. In the Internet mail system, allow users to read, reply to, forward, save and compose message.A User agentsB mail serversC SMTPD TCP53. The two key MIME headers for supporting multimedia are .A Content-Type and MIME-VersionB Content-Type and Content-Transfer-EncodingC Content-Transfer-Encoding and MIME-VersionD MIME-Version and MIME-Type54. For Internet mail, the mail access protocol is used to .A transfer mail from the recipient’s mail server to the recipient’s user agentB transfer mail from the sender’s mail server to the recipient’s mail serverC translate the mail from the sender’s mail serverD translate the mail into the recipient’s mail server55. POP3 progresses through three phases, which they are .A authorization, translation and transactionB authorization, translation and updateC authorization, transaction and updateD translation, transaction and update56. In the following four services, which one can not provide by DNS?A Host aliasingB Mail server aliasingC translate hostname to IP addressesD translate MAC addresses to IP addresses57. There are three classes of DNS servers, there are .A root DNS server, top-level domain DNS server and local DNS serverB root DNS server, top-level domain DNS server and authoritative DNS serverC root DNS server, local DNS server and authoritative DNS serverD root DNS server, local DNS server and top-level domain DNS server58. In the following four options about POP3, which one is not correct?A The user agent employed only three commands: List, Retr and QuitB The server does not carry state information across POP3 sessionsC The port number is 110D The POP3 protocol does not provide any means for a user to create remote folders and assign messages to folders.59.A resource record in DNS distributed database is a four-tuple,which field can be ign ored?(p132)A Name B Value C Type D TTL60.In the following four options about DNSresource record,which one is correct?A The meaning of Name and Value depend on Type.B The meaning of Value and Type depend on Name.C If Type=A,then Name is a domain and Value is the IP address for the hostname.D If Type=MX,then Name is domain and Value is the IP address for the hostname.61.In the following four options about DNS messages,which one is not correct?A There are only two kinds of DNS message.(p133)B Both query and reply message have the same format.C The header section in DNS message has12bytes.D The authority section contains the resource records for the same that was originally q ueried.62.In DNS message,contains information about the query that is being made.(p133)A authority sectionB question sectionC answer sectionD additional section63.There are three techniques are employed in most any P2P file-sharing systems,which one is not include?(p144)A Request queuingB incentive prioritiesC parallel downloadingD Response queui ng64. In the following four options about P2P file-sharing, which one is not correct?A P2P file-sharing is highly scalable.B P2P file-sharing relies on P2P architecture.C The means for locating content in different P2P file-sharing are different.D P2P file-sharing systems not only share MP3s,but also videos, software, documents and images.65.In MIME header lines,specifies the name of the SMTP server that sent the messag e(from),the name of the SMTP server that received the message(by),and the time an which the receiving server received the message.A ReceivedB FromC ToD MIME-Version66. If the header line Connection is close, it means that the client wants .A persistent connection with pipeliningB persistent connection without pipeliningC nonpersistent connectionD not connection67. In HTTP request message, the entity body is empty with the method, but is used with the method.A GET, POSTB POST,GETC GET, HEAD D POST, HEAD68. In HTTP response message, if the Date: header ;one indicates the time Fri. 08 Aug. 2008 12:00:00 GMT, the Last-Modified: header line can not be .A Fri. 08 Aug. 2008 11:00:00 GMTB Fri. 08 Aug. 2008 11:30:00 GMTC Fri. 08 Aug. 2008 12:00:00 GMTD Fri. 08 Aug. 2008 12:30:00 GMT69. In the following four options, which one is not the part of cookie technology?A Cookie header lines in the HTTP response message and request message.B One cookie header file kept on the user’s end system and managed by the user’s browser.C A network entity that satisfies HTTP requests on the behalf of an origin Web server.D A back-end database at the Web site70. On-top of stateless HTTP, can be used to create a user session layer.A proxy serverB Web cacheC cookieD socket71. Processes communicate with each other by reading from and writing to .A programsB threadsC socketsD channels72. In the following four options about network architecture, which one is not correct?A The network architecture is fixed.B The network architecture provides a specific set of services to application.C The network architecture is designed by application developer.D The network architecture dictates how the application is organized over special server.73. In Client-Server architecture, the clients visit the server’s through .A client’s socketB client’s IP addressC server’s socketD server’s IP address74. can be thought of as a program that is running within end system.A processB threadC socketD context75. API means .A Application Program InterfaceB Application Process InterfaceC Appellation Program InterfaceD Appellation Process Interface76. One host can be running many network applications, so the system assigns them differentto distinguish each other.A IP addressB port numberC hostnameD section77. In the following four applications, which one is both bandwith-sensitive and require tight timing constraints?A real-time audioB file transferC E-mailD Web documents78. The port number of the Web server is .A 25B 20C 80D 808079. The port number of the mail server is .A 25B 20C 80D 808080. Look the URL /rjxy/index.html, the object’s path name is .A B /rjxyC /rjxy/index.htmlD index.html81. Each URL has components, they are .A transport protocol and object’s path nameB host name and object’s path nameC transport protocol and host nameD client name and server name1. Consider an HTTP client will request a WEB page from a WEB server. Suppose the URL of the page is /somedepartment /somedir/exp.html. The client does not want to use persistent connections and want to receive French version of the object. The user agent is Windows NT 5.1. Give the request message according to the given format.Request line:Header lines:2. Telnet into a Web server and send a multiline request message. Include in the request message the If-modified-since: header line to force a response message with the 304 Not Modified status code.Solution:Request line:Header lines:3. Suppose within you Web browser you click on a link to obtain a Web page. The IPaddress for the associated URL is not cached in your local host, so a DNS look-up is necessary to obtain the IP address. Suppose that n DNS servers are visited before your host receives the IP address from DNS; the successive visits incur an RTT of RTT1,…,RTT n. Further suppose that the Web page associated with the link contains exactly one object, consisting of a small HTML text. Let RTT0 denote the RTT between the local host and the server containing the object. Assuming zero transmission time of the object, how much time elapses from when the client clicks on the link until the client receives the object?5. Suppose that you send an e-mail message whose only data is a microsoft excell attachment. What might the header lines (including MIME lines) look like?。
计算机网络英文——提供给学生部分习题答案
Solution of Selected Exercises from the End of Chapter ExercisesChapter 1 - Introduction And Overview1.4 To what aspects of networking does data communications refer? Answer: Data communications refers to the study of low-level mechanisms and technologies used to send information across a physical communication medium, such as a wire, radio wave, or light beam.b5E2RGbCAP1.5 What is packet-switching, and why is packet switching relevant tothe Internet?Answer: Packet switching divides data into small blocks, called packets, and includes an identification of the intended recipient in each packet. Packet switching changed networking in a fundamental way, and provided the basis for the modern Internet. Packet switching allows multiple senders to transmit data over a shared network. p1EanqFDPw1.8 What is a communication protocol? Conceptually, what two aspects ofcommunication does a protocol specify?Answer: A communication protocol refer to a specification for network communication.Major aspects of a protocol are syntax (format> and semantics (meaning> of the protocol. DXDiTa9E3d1.9 What is a protocol suite, and what is the advantage of a suite? Answer:protocols are designed in complete, cooperative sets called suites or families, instead of creating each protocol in isolation.Each protocol in a suite handles oneaspect of communication。
计算机网络英文试题库(附答案)chapter

.Chapter 2 Application Layer1. In the following four descriptions, which one is correct?A In C/S architecture, clients communicate with each other directly.B In C/S architecture, client has a fixed well-known address.C In P2P architecture, peers communicate with each other directly.D In P2P architecture, peer has a fixed well-known address.2.In the context of a communication session between a pair of process, theprocess that initiates the communication is labeled as the,the process that waits to be contacted to begin the session is labeled as the.A client process, server processB sending process, receivingprocessC input process,output processD communicating process, connecting process3.A socket is the interface between within a host.A the network layer and the link layerB the link layer and the physical layerC the application layer and the transport layerD the transport layer and the network layer4. In the following applications, which one is a loss-tolerant application?A E-mailB file transferC instant messagingD real-time audio5. In the following applications, which one is a bandwidth-sensitive application?.A E-mailB web applicationC real-time audioD file transfer6. The service of TCP can’tguarantee.A delivery of all data without errorB delivery of all data in theproper orderC the rate of deliveryD congestion control7. In the following applications, which one uses UDP?A E-mailB web applicationC file transferD DNS8.In the following descriptions about HTTP, which one is not correct?A HTTP uses non-persistent connections in its default mode.B HTTP uses TCP as its underlying transport protocol.C HTTP is a stateless protocol.D HTTP is client-server architecture.9.Suppose a web page consists of a base HTML file, 5 JEPG images and a java applet, and also suppose HTTP uses persistent connection without pipelining,the total response time is.A 2RTTB 8RTTC 12 RTTD 14RTT10. In HTTP response message, if the requested HTTP protocol version is not supported, the status code is.A 200B 301C 400D 5051~5 CACDC6~10 CDABD11. The port number of web application is.A25B20C80D5312. A network entity that satisfies HTTP requests on the behalf of an originweb server is.A server farmB server stackC proxy serverD edge server13. In the following descriptions about persistent connection, which one is not correct?A The server leaves the TCP connection open after sending a response.B Each TCP connection is closed after the server sending one object.C There are two versions of persistent connection: without pipelining and with pipelining.D The default mode of HTTP uses persistent connection with pipelining.14. FTP uses two parallel TCPconnections to transfer a file, there are.A control connection and data connectionB receiving connection and sending connectionC client connection and sever connectionD program connection and process connection15. In the following descriptions about FTP, which one is correct?A FTP is p2p architecture.B FTP sends its control informationout-of-band.C FTP uses persistent connection.D FTP is a stateless protocol.16. In the commandsof FTP, which one does not have parameter?A USERB PASSC LISTD STOR17. The Internet mail system has three components which they are.A user agent, SMTP, POP3B SMTP, POP3, IMAPC user agent, SMTP, IMAPD user agent, SMTP, mail server18. If the status code in HTTP response message is 404, it means.A Request succeeded.B The requested document doesn’texit on this server.C This is a generic error code indicating that the request could not be understood by the server.D Requested object has been permanently mover.19. Comparison HTTP with SMTP, the correct is.A HTTP is a push protocol, and SMTP is a pull protocol.B In the default mode, both of them use persistent connection.C HTTP places all of the message ’s objects into one message, and SMTP sendsevery object one by one.D HTTP requires each messageto be in 7-bit ASCII format,and SMTPdoesn’t impose this restriction.20. The headers in the MIME message must include except.A FromB Content-typeC Content-transfer-encodingD MIME version11~15CCBAB16~20 DDBBD21. In the following protocol, which one is stateless?A POP3B SMTPC FTPD IMAP22. DNS means.A Data Name SystemB Data National SystemC Domain Name SystemD Domain National System23. There are three classes of DNS server except.A Root DNS serverB Local DNS serverC TLD server D Authoritative DNS server24. DNS provides some services except.A Host aliasingB Mail server aliasingC Load distributionD A single point of failure25. There are three architectures for locating content in P2Pfile sharing,KaZaA uses.A Centralized Directory(Napster)B Query Flooding(Gnutella)C Exploiting Heterogeneity (p141)D Incentive Priorities26. There are three architectures for locating content in P2Pfile sharing, Napst er uses.A Centralized Directory (p137)B Query FloodingC Exploiting HeterogeneityD Incentive Priorities27. The following architectures in P2Pfile sharing, which is an overlay network?A Centralized DirectoryB Query Flooding(p139)C Exploiting HeterogeneityD Incentive Priorities28. The time it takes for a small packet to travel from client to server andthen back to the client is.A round-travel timeB next-hop timeC round-trip timeD prefix-matching time29.Suppose A ( with a Web-based e-mail account ) sends a message to B ( who accesses his mail server using POP3), which application-layer protocol is not used?A HTTPB SMTPC POP3D IMAP30.In the four following options, which protocol is included in Mail Access Protocol?A SMTPB DHCPC IMAPD FTP31. In FTP commands,is used to send user password to the server.A UserB PassC RetrD Stor32. The function of the additional header field in MIMEContent-Type is.A to convert the message body to its origin non-ASCII formB to determine what actions it should take on message bodyC to send an E-mail to the receiving user agentD to indicate what type the message is33.In the four following options, which application is organized as hybrid ofC/S and P2P architecture?A E-mailB OICQC File transferD Web application34. In the four following options, which is not a centralized DNSdesign ’s problem ?A a single point of failureB traffic volumeC distant centralized databaseD slow(maintenance)35. In the following options, from the application developer’s perspective, which is not correct?A the network architecture is fixedB the network architecture provides a specific set of services to applicationsC the application architecture is designed by the physical devicesD the application architecture dictates how the application is organized over the various end systems36. There are three predominant architectures used in modern network applications, which one is not included?A the client-server architectureB the P2P architectureC a hybrid of the client-server and P2P architectureD a hybrid of the client-server and browser-server architecture37.In the following options about C/S architecture, which is not correct?A In C/S architecture, there is an always-on host, called the server.B In C/S architecture, there is an always-on host, called the client.C The server has a fixed, well-known address, called IP address.D Clients do not directly communicate with each other.38.are often used to create a powerful virtual server in C/S architecture.A PeersB Server farmC server stackD local server39. A process sends messages into, and receives messages from, the network through its.A socketB programC clientD peer40.Which one is not defined by an application-layer protocol?A the types of messages exchangedB the syntax of various message typesC the semantics of the fieldsD rules for determining when and how to translate the socket41. HTTP can use two types of connections, which are.A persistent and non-persistent connectionB connection with pipelining and without pipeliningC TCP and UDPD parallel and serial connection42.takes for a small packet to travel from client to server and thenback to the client.A RDTB thresholdC RTTD overhead43. The default mode of HTTP uses.A non-persistent connection with pipeliningB non-persistent connection without pipeliningC persistent connection with pipeliningD persistent connection without pipelining44. In HTTP request messages, the request line has three fields,there are.A the method field, the URL field and the HTTP version fieldB the method, the connection and URL fieldC the user-agent, the method and HTTP version fieldD the user-agent, the URL and the HTTP version field45. In the header lines of HTTP request message, if the field of Connection isclose, it specifies.A the host on which object residesB what type of the user agentC that the browser wants the server to close the connection after sendingthe requested objectD which language can the browser receive46. In HTTP response message, if the status code is 404, it means.A request succeeded and the information is returned in the responseB requested object has been permanently movedC the requested HTTP protocol version is not supported by the serverD the requested document does not exist on this server47.is a network entity that satisfies HTTP requests on the behalfof an origin Web server.A proxy serverB local serverC DNS serverD Web server48. In the following four options about web cache, which one is not correct?A A web cache is both a server and a client at the same time.B A web cache is purchased and installed by an ISP.C A web cache can raise the response time for a client request.D A web cache can reduce traffic on an institution’s access link to the Internet.49. The request message in the conditional GET must include the headerline.A Last-ModifiedB Last-ReferencedC If-Modified-SinceD If–Referenced-Since50. FTP uses two parallel connections to transfer a file, they are.A TCP and UDP connectionB connection with pipelining and without pipeliningC control an data connectionD client-server and browser-server connection51.In FTP commands, which one is used to ask the server to send back alist of all files in the current remote directory?A USERB PASSC LISTD RETR52. In the Internet mail system,allow users to read, reply to, forward, save and compose message.A User agentsB mail serversC SMTPD TCP53. The two key MIME headers for supporting multimedia are.A Content-Type and MIME-VersionB Content-Type and Content-Transfer-EncodingC Content-Transfer-Encoding and MIME-VersionD MIME-Version and MIME-Type54. For Internet mail, the mail access protocol is used to.A transfer mail from the recipient ’s mail server to the recipient’s user agentB transfer mail from the sender’s mail server to the recipient’s mail serverC translate the mail from the sender’s mail serverD translate the mail into the recipient’s mail server55. POP3 progresses through three phases, which they are.A authorization, translation and transactionB authorization, translation and updateC authorization, transaction and updateD translation, transaction and update56. In the following four services, which one can not provide by DNS?A Host aliasingB Mail server aliasingC translate hostname to IP addressesD translate MAC addresses to IP addresses57. There are three classes of DNS servers, there are.A root DNS server, top-level domain DNS server and local DNS serverB root DNS server, top-level domain DNS server and authoritative DNS serverC root DNS server, local DNS server and authoritative DNS serverD root DNS server, local DNS server and top-level domain DNS server58.In the following four options about POP3, which one is not correct?A The user agent employed only three commands: List, Retr and QuitB The server does not carry state information across POP3 sessionsC The port number is 110D The POP3 protocol does not provide any means for a user to createremote folders and assign messages to folders.59. A resource record in DNSdistributed database is a four-tuple,which field ca n be ignored?(p132) A Name B Value C Type D TTL60. In the following four options about DNSresource record, which one is correct?A The meaning of Nameand Value depend on Type.B The meaning of Value and Type depend on Name.C If Type=A, then Nameis a domain and Value is the IP address for the hostname.D If Type=MX,then Nameis domain and Value is the IP address for the hostname.61.In the following four options about DNSmessages, which one is not correct?A There are only two kinds of DNSmessage.(p133)B Both query and reply messagehave the sameformat.C The header section in DNSmessagehas 12 bytes.D The authority section contains the resource records for the samethat wasorigi nally queried.62.In DNSmessage,contains information about the query that is being made.(p 133)A authority sectionB question sectionC answer sectionD additional sec tion63.There are three techniques are employed in most any P2Pfile-sharing systems, which one is not include?(p144)A Request queuingB incentive prioritiesC parallel downloadingD Responseq ueuing64. In the following four options about P2P file-sharing, which one isnot correct?A P2P file-sharing is highly scalable.B P2P file-sharing relies on P2P architecture.C The means for locating content in different P2P file-sharing are different.D P2P file-sharing systems not only share MP3s,but also videos, software,documents and images.65.In MIMEheader lines,specifies the nameof the SMTPserver that sent the m essage (from),the nameof the SMTPserver that received the message(by), and the time an which t he receiving server received the message.A ReceivedB FromC ToD MIME-Version66.If the header line Connection is close, it means that the client wants.A persistent connection with pipeliningB persistent connection without pipeliningC nonpersistent connectionD not connection67. In HTTP request message, the entity body is empty with the method,but is used with the method.A GET, POSTB POST,GETC GET, HEAD D POST, HEAD68. In HTTP response message, if the Date: header ;one indicates the time Fri.08 Aug. 2008 12:00:00 GMT, the Last-Modified: header line can not be.A Fri. 08 Aug. 2008 11:00:00 GMTB Fri. 08 Aug. 2008 11:30:00GMTC Fri. 08 Aug. 2008 12:00:00 GMTD Fri. 08 Aug. 2008 12:30:00 GMT69. In the following four options,which one is not the part of cookie technology?A Cookie header lines in the HTTP response message and request message.B One cookie header file kept on the user ’s end system and managedby the user ’s browser.C A network entity that satisfies HTTPrequests on the behalf of an origin Web server.D A back-end database at the Web site70. On-top of stateless HTTP,can be used to create a user session layer.A proxy serverB Web cacheC cookieD socket71. Processes communicate with each other by reading from and writing to.A programsB threadsC socketsD channels72.In the following four options about network architecture, which one isnot correct?A The network architecture is fixed.B The network architecture provides a specific set of services to application.C The network architecture is designed by application developer.D The network architecture dictates how the application is organized overspecial server.73. In Client-Server architecture,the clients visit the server ’s through.A client’s socketB client’s IP addressC server’s socketD server’s IP address74.can be thought of as a program that is running within end system.A processB threadC socketD context75. API means.A Application Program InterfaceB Application Process InterfaceC Appellation Program InterfaceD Appellation Process Interface76.One host can be running many network applications, so the system assignsthem differentto distinguish each other.A IP addressB port numberC hostnameD section77.In the following four applications, which one is both bandwith-sensitive and require tight timing constraints?A real-time audioB file transferC E-mailD Webdocuments78.The port number of the Web server is.A 25B 20C 80D 808079.The port number of the mail server is.A 25B 20C 80D 808080.Look the URL/rjxy/index.html,the object ’s path nameis.A B /rjxyC /rjxy/index.htmlD index.html81. Each URL has components, they are.A transport protocol and object’s path nameB host name and object’s path nameC transport protocol and host nameD client name and server name1. Consider an HTTP client will request a WEB page from a WEB server. Supposethe URLof the page is /somedepartment /somedir/exp.html. The client does not want to use persistent connections and want to receive Frenchversion of the object. The user agent is WindowsNT 5.1. Give the request message according to the given format.Request line:Header lines:.2.Telnet into a Web server and send a multiline request message. Includein the request message the If-modified-since: header line to force aresponse message with the 304 Not Modified status code.Solution:Request line:Header lines:3.Suppose within you Web browser you click on a link to obtain a Web page. The.look-up is necessary to obtain the IP address. Suppose that n DNS servers arevisited before your host receives the IP address from DNS; the successive visits incur an RTT of RTT, ⋯, RTT. Further suppose that the Webpage associated with1nthe link contains exactly one object,consisting of a small HTML text.Let RTT0 denote the RTT between the local host and the server containing the object.Assuming zero transmission time of the object, how much time elapses from whenthe client clicks on the link until the client receives the object?5. Suppose that you send an e-mail message whose only data is a microsoft excell attachment. What might the header lines (including MIME lines) look like?。
计算机网络双语试题及答案
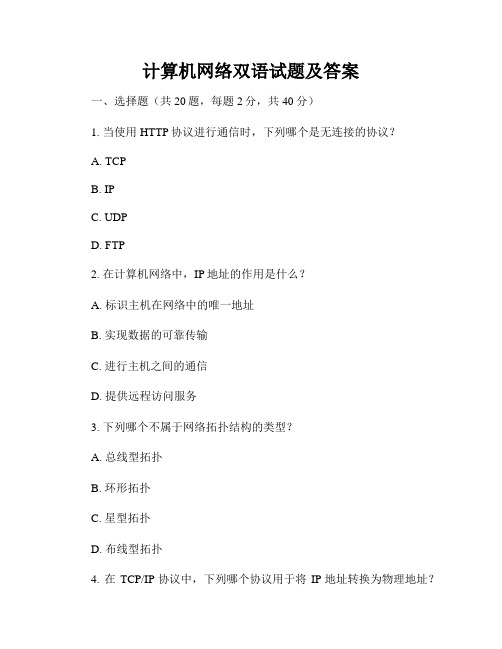
计算机网络双语试题及答案一、选择题(共20题,每题2分,共40分)1. 当使用HTTP协议进行通信时,下列哪个是无连接的协议?A. TCPB. IPC. UDPD. FTP2. 在计算机网络中,IP地址的作用是什么?A. 标识主机在网络中的唯一地址B. 实现数据的可靠传输C. 进行主机之间的通信D. 提供远程访问服务3. 下列哪个不属于网络拓扑结构的类型?A. 总线型拓扑B. 环形拓扑C. 星型拓扑D. 布线型拓扑4. 在TCP/IP协议中,下列哪个协议用于将IP地址转换为物理地址?B. DHCPC. FTPD. ICMP5. 在计算机网络中,HTTP和HTTPS协议之间的区别是?A. HTTP使用明文传输,HTTPS使用加密传输B. HTTP使用UDP传输,HTTPS使用TCP传输C. HTTP使用IP地址,HTTPS使用域名D. HTTP使用GET请求,HTTPS使用POST请求6. 某计算机的IP地址是192.168.0.1,子网掩码是255.255.255.0,那么该计算机所在的网络号是?A. 192.168.0B. 192.168.0.1C. 192.168.0.255D. 192.168.0.07. 在计算机网络中,下列哪个协议用于将域名解析为IP地址?A. DNSB. FTPC. DHCP8. 在TCP/IP协议中,下列哪个协议用于控制数据传输的可靠性?A. ICMPB. UDPC. FTPD. TCP9. 在计算机网络中,什么是反向代理服务器(Reverse Proxy Server)?A. 将外部网络请求转发给内部服务器的服务器B. 将内部网络请求转发给外部服务器的服务器C. 将HTTP请求转发给HTTPS服务器的服务器D. 将HTTPS请求转发给HTTP服务器的服务器10. 在计算机网络中,下列哪个协议用于电子邮件的发送和接收?A. SMTPB. POP3C. HTTPD. FTP11. 在计算机网络中,下列哪个协议用于文件传输?B. SMTPC. UDPD. TCP12. 以下哪个不是IPv6地址的特点?A. 128位长度B. 冒号分隔的十六进制C. 有固定的网络号和主机号D. 全球唯一的地址13. 在计算机网络中,下列哪个技术不属于无线局域网技术?A. Wi-FiB. BluetoothC. NFCD. 4G14. 在网络中,下列哪个设备用于将不同网段的数据转发到目的主机?A. 集线器B. 路由器D. 网关15. 下列哪个网络拓扑结构具有较高的可容错性和可拓展性?A. 星型拓扑B. 总线型拓扑C. 环形拓扑D. 树型拓扑16. 在计算机网络中,下列哪个协议用于互联网上的主机进行网络配置?A. DHCPB. DNSC. HTTPD. FTP17. 在TCP/IP协议中,下列哪个协议用于检测并纠正数据传输中的错误?A. TCPB. ARPC. ICMPD. UDP18. 下列哪个是网络安全的常见攻击方式之一?A. DDoS攻击B. 数据库攻击C. 剪贴板攻击D. 社会工程学攻击19. 下列哪个不是局域网(LAN)的特点?A. 覆盖范围较小B. 速度较快C. 价格较高D. 结构较简单20. 在计算机网络中,下列哪个协议用于向局域网中的所有主机广播消息?A. UDPB. TCPC. DHCPD. ICMP二、问答题(共5题,每题10分,共50分)1. 请简要介绍HTTP协议的工作原理。
计算机网络英文版——提供给学生部分习题答案

计算机⽹络英⽂版——提供给学⽣部分习题答案Solution of Selected Exercises from the End of Chapter ExercisesChapter 1 - Introduction And Overview1.4 To what aspects of networking does data communications refer?Answer:Data communications refers to the study of low-level mechanisms and technologies used to send information acrossa physical communication medium, such as a wire, radio wave, or light beam.1.5 What is packet-switching, and why is packet switching relevant to the Internet?Answer: Packet switching divides data into small blocks, called packets, and includes an identification of the intended recipient in each packet. Packet switching changed networking in a fundamental way, and provided the basis for the modern Internet. Packet switching allows multiple senders to transmit data over a shared network.1.8 What is a communication protocol? Conceptually, what two aspects of communication does a protocol specify? Answer: A communication protocol refer to a specification for network communication.Major aspects of a protocol are syntax (format) and semantics (meaning) of the protocol.1.9 What is a protocol suite, and what is the advantage of a suite?Answer:protocols are designed in complete, cooperative sets called suites or families, instead of creating each protocol in isolation. Each protocol in a suite handles one aspect of communication; together, the protocols in a suite cover all aspects of communication. The entire suite is designed to allow the protocols to work together efficiently. 1.11 List the layers in the TCP/IP model, and give a brief explanation of each.(See Textbook)1.14 Give a brief explain of the layers in the ISO Open System Interconnection model.(See Textbook)Chapter 3 - Internet Applications And Network Programming3.1 What are the two basic communication paradigms used in the Internet?Answer: There are various approaches, but according to textbook, we can specify them as Stream Paradigm and Message Paradigm.3.2 Give six characteristics of Internet stream communication.(See Textbook)3.3 Give six characteristics of Internet message communication.(See Textbook)3.4 If a sender uses the stream paradigm and always sends 1024 bytes at a time, what size blocks can the Internet deliverto a receiver?Answer: stream paradigm does not provide any guarantees for block sizes, so all depends on individual transfer.3.6 What are the three surprising aspects of the Internet’s message delivery semantics?Answer:The Internet’s message delivery has the followi ng undesirable characteristics:* Messages can be lost* Messages can be duplicated* Messages can be delivered out-of-order3.8 When two applications communicate over the Internet, which one is the server?Answer: T he application that waits for some other applications to contact is called server, and the application that contact other one is called client.3.14 What two identifiers are used to specify a particular server?Answer: A particular server is identified by the following identifiers:* An identifier for the computer on which a server runs (IP Address)* An identifier for a particular service on the computer (Port Number)Chapter 4 - Traditional Internet Applications4.1 What details does an application protocol specify?(See Textbook)4.3 What are the two key aspects of application protocols, and what does each include?(See Textbook)4.6 What are the four parts of a URL, and what punctuation is used to separate the parts?Answer: The URL into four components: a protocol, a computer name, a document name, and parameters. The computer name and protocol port are used to form a connection to the server on which the page resides. And the document name and parameters are used to request a specific page.4.7 What are the four HTTP request types, and when is each used?(See Textbook)4.12 When a user requests an FTP directory listing, how many TCP connections are formed? Explain.Answer: FTP uses two types of connections to perform its functionality, namely* A control connection is reserved for commands. Each time the server needs to download or upload a file, the server opens a new connection.* A data connection is used to transfer files.4.16 List the three types of protocols used with email, and describe each.(See Textbook)4.17 What are the characteristics of SMTP?(See Textbook)4.20 What are the two main email access protocols?Answer: Two major email access protocols are:* Post Office Protocol (POP)* Internet Mail Access Protocol (IMAP)Chapter 6- Information Sources and Signals6.4 State and describe the four fundamental characteristics of a sine wave.(See Textbook)6.9 What is the analog bandwidth of a signal?Answer: Analog bandwidth of signal can be defined as to be the difference between the highest and lowest frequencies of the constituent parts (i.e., the highest and lowest frequencies obtained by Fourier analysis)6.11 Suppose an engineer increases the number of possible signal levels from two to four. How many more bits can be sent in the same amount of time? Explain.Answer: The number of levels that can be represented by n bits is given by 2n . So if number of levels changes from 2→4, it means number of bits goes from 1→2612. What is the definition of baud?Answer: Baud is defined as the number of times that a signal can change per second.6.14 What is the bandwidth of a digital signal? Explain.Answer: According to the definition of analog bandwidth, a digital signal has infinite bandwidth because Fourier analysis of a digital signal produces an infinite set of sine waves with frequencies that grow to infinity.6.18 What is the chief advantage of a Differential Manchester Encoding?Answer: The most important property of differential encoding is that the encoding works correctly even if the two wires carrying the signal are accidentally reversed.6.20 If the maximum frequency audible to a human ear is 20,000 Hz, at what rate must the analog signal from a microphone be sampled when converting it to digital?Answer: The sampling rate = 2 × f max, so the signal should be sampled at 2x20,000 = 40,000 HzChapter 7 - Transmission Media7.2 What are the three energy types used when classifying physical media according to energy used?Answer: Three types of energy used when classifying physical media are electrical, electromechanical (radio), and light7.4 What three types of wiring are used to reduce interference form noise?(See Textbook)7.10 List the three forms of optical fiber, and give the general properties of each.(See Textbook)7.21 What is the relationship between bandwidth, signal levels, and data rate?Answer: If a transmission system uses K possible signal levels and has an anal og bandwidth B, Nyquist’s Theorem states that the maximum data rate in bits per second, D, is: D = 2 B log2K7.22 If two signal levels are used, what is the data rate that can be sent over a coaxial cable that has an analog bandwidthof 6.2 MHz?Answer: Using the D= 2 B log2 K relationship, D = 2*6.2*log22 = 2*6.2*1 = 12.4 Mbps7.24 If a system has an input power level of 9000, and an output power level of 3000, what is the difference when expressed in dB?Answer: Decibel is expressed as 10log10(P out/P in) → 10log10(3,000/9,000) = to be determined by reader7.23 If a system has an average power level of 100, an average noise level of 33.33, and a bandwidth of 100 MHz, whatis the effective limit on channel capacity?Answer: Shannon theorem specify the maximum data rate that could be achieved over a transmission system that experiences noise: C = Blog2 (1 + S/N) = 100,000,000 * log2 (1 + 100/33.33) = 100,000,000 * log24 = 200,000,000 = 200 Mbps7.25 If a telephone system can be created with a signal-to-noise ratio of 40 dB and an analog bandwidth of 3000 Hz, how many bits per second could be transmitted?Answer: First we should convert 40 dB to a real number, namely if 40 = 10 log10S/N→S/N = 10,000 , Using the Shannon’s capacity expression C = B log2(1 + S/N) → C = 3,000 log2 (1+ 10,000) = to be determined by readerCh 8 - Reliability And Channel Coding8.1 List and explain the three main sources of transmission errors.(See Textbook)8.3 In a burst error, how is burst length measured?Answer: For a burst error, the burst size, or length, is defined as the number of bits from the start of the corruption to the end of the corruption.8.4 What is a codeword?Answer: We can define the set of all possible messages to be a set of datawords, and define the set of all possible encoded versions to be a set of codewords. So each possible code sequence is considered to be a codeword.8.8 Compute the Hamming distance for the following pairs: (0000, 0001), (0101, 0001), (1111, 1001), and ( 0001, 1110). (See Textbook)8.11 Generate a RAC parity matrix for a (20, 12) coding of the dataword 100011011111.(See Textbook)8.15 Express the two values in the previous exercise as polynomials.Answer:X10+ X7 + X5 + X3 + XX4+ X2+ 1Ch 9 - Transmission Modes9.1 Describe the difference between serial and parallel transmission.Answer: Transmission modes can be divided into two fundamental categories:* Serial: one bit is sent at a time* Parallel: multiple bits are sent at the same time9.2 What are the advantages of parallel transmission? What is the chief disadvantage?Answer: A parallel mode of transmission has two chief advantages:* High speed: Because it can send N bits at the same time, a parallel interface can operate N times faster than an equivalent serial interface.* Match to underlying hardware: Internally, computer and communication hardware uses parallel circuitry.Thus, a parallel interface matches the internal hardware well.The main disadvantage of parallel transmission is number of cables required, for long distance communication, this is an important consideration.9.4 What is the chief characteristic of asynchronous transmission?Answer:Asynchronous transmission can occur at any time, with an arbitrary delay between the transmission of two data items, it allows the physical medium to be idle for an arbitrary time between two transmissions.Chapter 11 - Multiplexing And Demultiplexing11.2 What are the four basic types of multiplexing?(See Textbook)11.4 What is a guard band?Answer: For proper communication without interference, we should choose a set of carrier frequencies with a gap between them known as a guard band. The guard band reduces or eliminates the possible interference between neighboring carrier signals.11.8 Explain how a range of frequencies can be used to increase data rate.Answer:To increase the overall data rate, a sender divides the frequency range of the channel into K carriers, and sends 1 /K of the data over each carrier.11.12 Suppose N users compete using a statistical TDM system, and suppose the underlying physical transport can sendK bits per second. What is the minimum and maximum data rate that an individual user can experience?Answer: If we neglect the overhead generated by statistical TDM, a system will have two possibilities: * Minimum: If all channels have equal data then the rate will be K/N bps* Maximum: If only one channel active and the others are passive, then rate will be K bpsChapter 13 - Local Area Networks: Packets, Frames, And Topologies13.1 What is circuit switching, and what are its chief characteristics?Answer: The term circuit switching refers to a communication mechanism that establishes a path between a sender and receiver with guaranteed isolation from paths used by other pairs of senders and receivers. The circuit switching has the following main characteristics:* Point-to-point communication* Separate steps for circuit creation, use, and termination* Performance equivalent to an isolated physical path13.3 In a packet switching system, how does a sender transfer a large file?Answer: The packet switching system requires a sender to divide each message into blocks of data that are known as packets . The size of a packet varies; each packet switching technology defines a maximum packet size. So, a large file will be divided into smaller pieces and sent.13.5 What are the characteristics of LANs, MANs, and W ANs?Answer: There are lots of details that can be said and discussed for categorization of network types based on geography, few points are highlighted below:* Local Area Network (LAN): Least expensive; spans a single room or a single building* Metropolitan Area Network (MAN) Medium expense; spans a major city or a metroplex* Wide Area Network (WAN) Most expensive; spans sites in multiple cities13.6 Name the two sublayers of Layer 2 protocols defined by IEEE, and give the purpose of each.Answer: The Layer 2 protocols defined by IEEE defines two sub-layers as mentioned below:* Logical Link Control (LLC) Addressing and demultiplexing* Media Access Control (MAC) Access to shared media13.8 What are the four basic LAN topologies?Answer: The four basic LAN topologies are star, ring, mesh and bus.13.10 In a mesh network, how many connections are required among 20 computers?Answer: The expression to calculate number of connections in a mesh network is given by n (n-1)/2. So for 20 computers then number of connections required will be = 20 (20 – 1)/2 =19013.15 Give a definition of the term frame .Answer: In a packet-switched network, each frame corresponds to a packet processed at data link layer.Chapter 14 - The IEEE MAC Sub-Layer14.1 Explain the three basic approaches used to arbitrate access to a shared medium.(See Textbook)14.3 List the three main types of channelization and the characteristics of each.(See Textbook)14.6 What is a token, and how are tokens used to control network access?Answer: A special control message is called a token. In a token passing system, when no station has any packets to send, the token circulates among all stations continuously. When a station captures the token, it sends its data, and when transmission completed, it releases the token.14.8 Expand the acronym CSMA/CD, and explain each part.Answer: The acronym CSMA/CD stands for Carrier Sense Multi-Access with Collision Detection, which means the following: * Carrier Sense: Instead of allowing a station to transmit whenever a packet becomes ready, Ethernet requires each station to monitor the cable to detect whether another transmission is already in progress.* Multiple Access: The system allows multiple users/hosts to make use of a common/shared media* Collision Detection. A collision can occur if two stations wait for a transmission to stop, find the cable idle, and both start transmitting.14.10 Why does CSMA/CD use a random delay? (Hint: think of many identical computers on a network.)Answer: Randomization is used to avoid having multiple stations transmit simultaneously as soon as the cable is idle.That is, the standard specifies a maximum delay, d, and requires each station to choose a random delay less than d after a collision occurs. In most cases, when two stations each choose a random value, the station that chooses the smallest delay willChapter 15 - Wired LAN Technology (Ethernet And 802.3)15.1 How large is the maximum Ethernet frame, including the CRC?Answer: According to Fig. 15.1 a conventional Ethernet frame has the following fields:* Header: 14 bytes (fixed)* Payload: 46-1500 bytes (there is a minimum frame size because of collision detection)* CRC: 4 bytes (fixed)Accordingly an Ethernet frame will be maximum 1518 bytes and minimum 64 bytes15.3 In an 802.3 Ethernet frame, what is the maximum payload size?Answer: The 802.3 Ethernet makes use of 8-bytes of the original/conventional Ethernet for Logical Link Control / Sub-Network Attachment Point (LLC / SNAP) header instead of extending/increasing the header. This is for sake of backward compatibility. So the maximum pay load is reduced from 1500 bytes to 1492 bytes.15.6 How did a computer attach to a Thicknet Ethernet?Answer: Hardware used with Thicknet was divided into two major parts:* Transceiver: A network interface card (NIC) handled the digital aspects of communication, and a separate electronic device called a transceiver connected to the Ethernet cable and handled carrier detection, conversion of bits into appropriate voltages for transmission, and conversion of incoming signals to bits.* AUI: A physical cable known as an Attachment Unit Interface (AUI) connected a transceiver to a NIC in a computer. A transceiver was usually remote from a computer.15.7 How were computers attached to a Thinnet Ethernet?Answer: Thinnet Ethernet (formally named 10Base2) uses a thinner coaxial cable that was more flexible than Thicknet. The wiring scheme differed dramatically from Thicknet. Instead of using AUI connections between a computer and a transceiver, Thinnet integrates a transceiver directly on the NIC, and runs a coaxial cable from one computer to another.15.8 What is an Ethernet hub, and what wiring is used with a hub?Answer: An electronic device that serves as the central interconnection is known as a hub. Hubs were available in a variety of sizes, with the cost proportional to size. The hubs are becoming old-fashioned, and being replaced with switches.15.3 What category of twisted pair wiring is needed for a 10 Mbps network? 100 Mbps? 1000 Mbps?Answer: The three major categories of Ethernet and their wiring is listed below:* 10 Mbps: 10BaseT (Ethernet) Category 5* 100 Mbps: 100BaseT (Ethernet Fast) Category 5E* 1 Gbps: 1000BaseT (Gigabit Ethernet) Category 6Chapter 20 - Internetworking: Concepts, Architecture, and Protocols20.2 Will the Internet be replaced by a single networking technology? Why or why not?Answer: Incompatibilities make it impossible to form a large network merely by interconnecting the wires among networks. The beauty of the Internet is interconnection of wide range of technologies from various manufacturers.Diversity of the products and solutions is a richness instead of limitation as long as they all adopt the same set of protocols.20.3 What are the two reasons an organization does not use a single router to connect all its networks?Answer:An organization seldom uses a single router to connect all of its networks. There are two major reasons: * Because the router must forward each packet, the processor in a given router is insufficient to handle the traffic passing among an arbitrary number of networks.* Redundancy improves internet reliability. To avoid a single point of failure, protocol software continuously monitors internet connections and instructs routers to send traffic along alternative paths when a network or router fails.20.6 In the 5-layer reference model used with the TCP/IP Internet protocols, what is the purpose of each of the five layers?(See 1.11)Chapter 21- IP: Internet Addressing21.3 In the original classful address scheme, was it possible to determine the class of an address from the address itself? Explain.Answer:Yes, since in the classful addressing scheme initial bit(s) gives indication about the class being used.21.7 If an ISP assigned you a /28 address block, how many computers could you assign an address?Answer: When an organization is assigned /28 CIDR address, it means 28 bits out of 32 bits are fixed, so 32-28 = 4 bits available for user space. So number of users 24-2 = 4, since the all 0s and all 1s address are having special use and can’t be assigned to a user.21.8 If an ISP offers a / 17 address block for N dollars per month and a / 16 address block for 1.5 N dollars per month,which has the cheapest cost per computer?Answer: Number of addresses in /17 block 232-17 = 215Price per address: N /215 = N / 215Number of addresses in /16 block 232-16 = 216Price per address: 1.5N /216 = 0.75N/215 So /16 address block will be cheaper in comparison with the price given for /17 block.21.10 Suppose you are an ISP with a / 24 address block. Explain whether you accommodate a request from a customer who needs addresses for 255 computers. (Hint: consider the special addresses.)Answer: For a/24 address block, number of available addresses will be 232-24 = 28 = 256. However, a suffix with all 0s address is reserved for network ID and a suffix with all 1s address is reserved for broadcast address, so number of addresses that can be assigned to computers/hosts will be 256 -2 = 254.21.11 Suppose you are an ISP that owns a / 22 address block. Show the CIDR allocation you would use to allocateaddress blocks to four customers who need addresses for 60 computers each.Answer: The /22 address block can be assigned as follows:ddd.ddd.ddd.00/26ddd.ddd.ddd.01/26ddd.ddd.ddd.10/26ddd.ddd.ddd.11/26Chapter 22- Datagram Forwarding22.1 What are the two basic communication paradigms that designers consider when designing an internet?Answer:* Connection-oriented service * Connectionless service22.2 How does the Internet design accommodate heterogeneous networks that each have their own packet format?Answer: To overcome heterogeneity, the Internet Protocol defines a packet format that is independent of the underlying hardware. The result is a universal, virtual packet that can be transferred across the underlying hardware intact. The Internet packet format is not tied directly to any hardware. The underlying hardware does not understand or recognize an Internet packet.22.5 What is the maximum length of an IP datagram?In the current version of the Internet Protocol (IP version 4), a datagram can contain at most 64 K (65535) octets, including the header.22.7 If a datagram contains one 8-bit data value and no header options, what values will be found in header fields H.LEN and TOTAL LENGTH?Answer: H. LEN indicated header in 32-quantities, since no options, then this value will be 5. The TOTAL LENGTH indicated the number of bytes in a datagram including the header. This means 5x4 bytes + 1 (8-bits) = 21 bytesChapter 23 - Support Protocols And Technologies23.1 When a router uses a forwarding table to look up a next-hop address, the result is an IP address. What must happenbefore the datagram can be sent?Answer: Each router along the path uses the destination IP address in the datagram to select a next-hop address, encapsulates the datagram in a hardware frame, and transmits the frame across one network. A crucial step of the forwarding process requires a translation: forwarding uses IP addresses, and a frame transmitted across a physical network must contain the MAC address of the next hop.23.2 What term is used to describe the mapping between a protocol address and a hardware address?Answer: Translation from a computer’s IP address to an equivalent hardware address is known as address resolution, and an IP address is said to be resolved to the correct MAC address. The TCP/IP protocol being used for this is called Address Resolution Protocol (ARP). Address resolution is local to a network.23.5 How many octets does an ARP message occupy when used with IP and Ethernet addresses?Answer: According to Fig 23.3 an ARP message has 7-lines of each being 32-bit (4 bytes or octets), therefore,number of octets in an ARP can be determined as 7x4 = 28 octets23.10 What types of addresses are used in layers below ARP?Answer:ARP forms a conceptual boundary in the protocol stack; layers above ARP use IP addresses, and layers below ARP use MAC addresses.23.17 What is the chief difference between BOOTP and DHCP?Answer:The main difference is that the BOOTP protocol required manual administration. So before a computer could use BOOTP to obtain an address, a network administrator had to configure a BOOTP server to know the computer’s I P address. Chapter 24 - The Future IP (IPv6)24.3 List the major features of IPv6, and give a short description of each.(See Textbook)24.4 How large is the smallest IPv6 datagram header?Answer: IPv6 datagram header consists of a base header + zero or more extension header. Since, smallest header is being asked, we assume zero extension header and consider IPv6 will have only base header. If we look at IPv6 header format in Fig. 24.3, it shows that 10x4 bytes = 40 bytes.Chapter 26 - TCP: Reliable Transport Service26.2 List the features of TCP.(See Textbook)26.6 When using a sliding window of size N, how many packets can be sent without requiring a single ACK to be received?Answer: If the size of the window is N, then it means a sender can transmit up to N packets without waiting for an ACK, as long as other controls are in place.26.9 What is the chief cause of packet delay and loss in the Internet?Answer: The main cause of packet delay and loss in the Internet is congestion.Chapter 28 - Network Performance (QoS and DiffServ)28.1 List and describe the three primary measures of network performance.(See Textbook)28.2 Give five types of delay along with an explanation of each.(See Textbook)Chapter 30 - Network Security30.1 List the major security problems on the Internet, and give a short description of each.(See Textbook)30.2 Name the technique used in security attacks.(See Textbook)30.8 List and describe the eight basic security techniques.(See Textbook)。
计算机网络试卷及答案-英文版
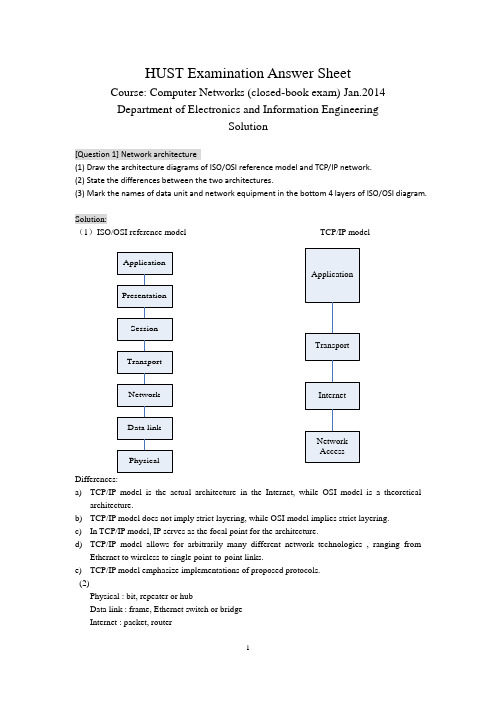
HUST Examination Answer SheetCourse: Computer Networks (closed-book exam) Jan.2014 Department of Electronics and Information EngineeringSolution[Question 1] Network architecture(1) Draw the architecture diagrams of ISO/OSI reference model and TCP/IP network. (2) State the differences between the two architectures.(3) Mark the names of data unit and network equipment in the bottom 4 layers of ISO/OSI diagram.Solution:(1)ISO/OSI reference model TCP/IP modelDifferences:a) TCP/IP model is the actual architecture in the Internet, while OSI model is a theoreticalarchitecture.b) TCP/IP model does not imply strict layering, while OSI model implies strict layering. c) In TCP/IP model, IP serves as the focal point for the architecture.d) TCP/IP model allows for arbitrarily many different network technologies , ranging fromEthernet to wireless to single point-to-point links.e) TCP/IP model emphasize implementations of proposed protocols. (2)Physical : bit, repeater or hubData link : frame, Ethernet switch or bridge Internet : packet, routerTransport : message, gateway[Question 2] Principles of network designSelect ONE of the following principles, tell its main ideas and provide an example. (1) Keep it simple and stupid(2) Complex edge and simple core (3) Smart sender and dumb receiverSolution:(1) KISS: Keep It Simple and StupidIt means that you should make things simple in the designing. One example following it : Ethernet(2) Complex edge and simple coreIt means that the hosts are very complex and have many functions while the nodes are very simple and have few functions.One example following it : The design of router, or the functions of TCP and IP(3) Smart sender and dumb receiverIt means that the function of sender is more complex than that of the receiver, which is help to improve the robustness and performance of communication protocol. One example following it: The flow control of TCP protocol[Question 3] Error detection(1) Tell the main idea of error detection and error correction in communication.(2) Given the CRC polynomial x 4 + x 3 + 1, if the original message is 10110011010, what is the CRC message to send?(3) Suppose the first bit of the message in (2) is inverted due to the noise in transmission. How can the receiver detect it via CRC verification?Solution:(1)1087431()M x x x x x x x =+++++, 43()1C x x x =++. So k=4.a) Multiply M(x) by 2kto get 141211875()T x x x x x x x =+++++,b) Then divide T(x) by C(x) to get the remainder 0000.c) The message that should be transmitted is 101100110100000.(2)The message received is 001100110100000.Divide it by C(x), then the remainder is 1100.So it is not divisible by C(x).So the receiver knows that an error has occurred.(1) What are the essential components to realize reliable transmission?(2) Suppose two computers are communicated via Stop-and-wait protocol. The link bandwidth is 5kbps, and the one-way propagation delay is 20ms. To reach 80% or higher link utilization, what is the minimal frame size for this communication?(3) If it is upgraded to Sliding-Window protocol. To reach the same goal with (2), what is the minimal window size, how many bits are required to describe the frame sequence in window? (Suppose the frame size is 1 or 100Byte)Solution:(1)ACK, and timerActual_throughput = Data / Total_DelayTotal_Delay = RTT + Data / BWLink_Utilization = 100 * Actual_throughput / BWSo: Data/throughput = RTT + Data/BW(BW/throughput - 1) Data = BW*RTTData = BW*RTT/(1/Utilization -1)For the stop-and-wait protocol, for each RTT only one frame is sent,Thus Frame_size = Data = BW*RTT/(1/Utilization - 1) = 5kbps * 40ms / (1/0.8 - 1)= 200 bit / 0.25 = 800 bit = 100 ByteIf the students ignore the data transmission delay, their answer isframe_size = BW*RTT*Utilization = 5000 bit/sec * 40 / 1000 sec * 0.8 = 160 bit = 20 ByteIn this case, at least -2 score.(3)For the sliding-window protocol, in each RTT the data window can be transmitted at most.Thus Window_size = Data = BW*RTT/(1/Utilization - 1) = 5kbps * 40ms / (1/0.8 - 1)= 200 bit / 0.25 = 800 bit = 100 ByteIf the frame size is 100Byte, 1 frames are allowed.To indicate the frames in both sides of sender and receiver, the sequence number should describe 2 frames, thus the [log2(2) ]=1 bitIf the students ignore the data transmission delay, their answer iswindow_size = BW*RTT*Utilization = 5000 bit/sec * 40 / 1000 sec * 0.8 = 160 bit = 20 ByteIf the frame size is 100Byte, 1 frames are allowed.To indicate the frames in both sides of sender and receiver, the sequence number should describe 2 frames, thus the [log2(2) ]=1 bitIn this case, at least -2 score.(1) What is the main idea of CSMA/CD (Carrier Sense Multiple Access/Collision Detection) in traditional Ethernet? Can it be deployed for wireless local network, why?(2) Suppose one traditional Ethernet has 1km cable, the signal propagation speed is 2*105km/s, and the transmission rate is designed to be 100Mbps. What is the minimal frame size to support carrier sensing?Solution:(1) the main idea of CSMA/CD include two parts. One is carrier sensing, which means the node should detect the channel before sending any data. If the node finds the channel is idle, it begins to transmit. Otherwise, the node stop for next round. The second issues is collision detection, which means the node should detect the channel in the duration of its data transmission. If the node finds the channel become busy, or in other word, there is a collision, it should stop transmitting immediately.CSMA/CD cannot be deployed in wireless LAN, because the wireless radio transmitter and receiver can not work in dual mode. The wireless node cannot detect collision when it is transmitting data.(2)the minimal frame should be transmitted throughout the whole traditional Ethernet.Thus t = frame_size / transmit_rate = 2 * cable_length / prop_speed.Frame_size = 100 * 106 bits/sec * 2 * 103 m / (2 * 108)m/sec = 1000 bits = 125 Byte[Question 6] Switched network(1) What are the differences between circuit switching and packet switching?(2) For the following linear topology network, each link has 2ms propagation delay and 4 Mbps bandwidth.A B C DIf we use circuit switching, circuit setup requires a 1KB message to make one round-trip on the path, which incurs a 1ms delay at each switch after the message has been completely received. Then we can send the file as one contiguous bit stream. What is the delay for circuit switching to transmit n-byte from A to D?(3) If we use packet switching in the network of (2), we can break the file into 1KB packets, which has 24byte header and 1000byte payload. The switch takes 1ms process delay after receiving the packet, and then sent it continuously. What is the condition for packet switching to have less delay performance than circuit switching?Solution:(1)(2)T pkt = Packet_Size / Bandwidth = 1 KB / 4Mbps = 1024 *8 / (4 * 106) = 2.048 ms T p = 2 ms, T s = 1 ms,T t = n B / 4MbpsIn circuit switching, Total time duration:D = Singling_Delay + Transmission_Delay = 2 * Packet_Duration + Transmission_Delay = 2 * (T pkt * 2 + T p * 3 + T s * 2 + T pkt ) + (T p * 3 + T t ) = T pkt * 6 + T p * 9 + T s * 4 + T tThus, D = 2.048 * 6 + 2 * 9 + 1 * 4 + n * 8 bits / 4Mbps = 34.288 (ms) + 2n (us)(3)Main ideaThe reliability provided by endhost The reliability provided by thenetwork Information in packet Every packet has its dest-addrin header Every packet has its temp VCIlocally Forwarding action inswitch Every packet was treatedindependentlyThe packets are processed inthe manner of VCPackets received indestinationNot in sequenceIn sequenceT pkt = Packet_Size / Bandwidth = 1 KB / 4Mbps = 1024 *8 / (4 * 106) = 2.048 msT p = 2 ms,T s = 1 ms,T t = 1.024 * n B / 4MbpsIn packet switching, Total time duration:D = Delay_at_Switch * Switch_Num + Delay_at_last_hop= (T p + T pkt +T s)*2 + (T p + T t )= T pkt * 2 + T p * 3 + T s * 2 + T tThus, D = 2.048 * 2 + 2 * 3 + 1 * 2 + 1.024 * n B / 4Mbps= 12.096 (ms) + 2.048 n (us)In order to make34.288 (ms) + 2n (us) > 12.096 (ms) + 2.048 n (us)Thus 22.192(ms) > 0.048 n(us)n < 22.192 * 1000 / 0.048 = 462333 Byte = 451.5 KB[Question 7] Ethernet Switch(1) What are the differences between hub and switch in Ethernet?(2) Suppose one server and nine clients are connected via hub in 10Mbps Ethernet, what is the maximal bandwidth for the client-server connection?(3) If the hub is upgraded to switch, can the client-server connection obtain more bandwidth? if can, how much is it?Solution:(1)hub works in Layer2, it works as the shared media and relays the frames to all the nodes connecting to hub. Switch works in Layer2, it forwards the frames to the specific node according to the destination address embedded in the frame header.(2)the max bandwidth in client-server connection is 10Mbps/(1+9)= 1Mbps(3)the max bandwidth in client-server connection is 10Mbps/9 = 1.1111MbpsAdditional 0.1111 Mbps is obtained for each connection.[Question 8] Router(1) Somebody says that, ``the only difference between switch and router is that they do switch function based on the address in different layers.’’ Is it correct? Why?(2) If we obtain the following information from one router. What kind of routing protocol does itSolution:(1)it is not fully correct. The part talking about the forwarding function is correct, while it is not the only difference. Another but not the last difference is that, router has more functions on control plane, which do routing and find the paths for packets.(2)The routing protocol is RIP.The routing table is:Destination Next hop Interface192.168.1.0/24 * Fa 0/4192.168.2.0/24 * Fa 0/6192.168.10.0/24 192.168.1.1 Fa 0/4192.168.30.0/24 192.168.2.2 Fa 0/6[Question 9] Routing algorithm(1) State the main differences between distance vector routing and link state routing.(2) For the network given in the following figure, provide the steps of forward search in Dijkstra algorithm for node A finding the shortest path to node ESolution:(1) The idea of distance vector routing is to tell the neighbors about the learned topology to all the nodes in the network. The idea of link state routing is to tell all the nodes in network about the neighborhood topology.Step 1 2 3 4 5 6 7 8 9Confirmed (A,0,-) (A,0,-) (A,0,-)(D,2,D)(A,0,-)(D,2,D)(A,0,-)(D,2,D)(B,4,D)(A,0,-)(D,2,D)(B,4,D)(A,0,-)(D,2,D)(B,4,D)(E,6,D)(A,0,-)(D,2,D)(B,4,D)(E,6,D)(A,0,-)(D,2,D)(B,4,D)(E,6,D)(C,7,D)Tentative (B,5,B)(D,2,D)(B,5,B) (B,4,D)(E,7,D)(E,7,D)(E,6,D)(C,8,D)(C,8,D) (C,7,D)A→E A→D→EA→D→B→EA→D→B→E[Question 10] IP address allocationA company has one C class IP address of 200.1.1.*. It has four departments.(1) If each department has less than 25 computers. Provide a kind of IP address allocation. Give the network address, subnet mask, and the available IP address range for each department. (2) If the four departments have 72, 35, 34, 20 computers respectively. Provide the IP address allocation scheme again.Solution:(1)Since each department has less than 25 computers, even considering the additional two more IP address for gateway and broadcast, the 64-computer subnet is enough for them.One IP address allocation scheme is to even divide the 256 IP addresses into 4 subnets, each subnet allows 64 hosts.Another IP address allocation scheme is to even divide the 256 IP addresses into 4 subnets, each subnet allows 32 hosts.(2) Since one of the department has more requirements than 64, then the even distribution scheme[Question 11] TCP protocol(1) Somebody says that, ``because of the reliable transmission service in layer 2, there is no need to provide such service again within TCP protocol in layer 4’’. Is it correct? Why?(2) State the main rules of TCP connection setup according to the following figure. Explain every word and number in the figure.Solution:(1) It is wrong. TCP is based on the un-reliable IP layer, which only provides best effort service. If TCP wants to provide reliable transmission service, it has to realize this by itself.(2)TCP use three hand-shakes to setup the connection.According to the figure, there are two nodes. The sender is with IP address of 192.168.1.163 and the receiver 192.168.1.165 respectively.●At first, the sender send a request ``SYN’’to the receiver to setup the connection. Thismessage is with the sequence number of 424CF1DC;●Secondly, the receiver reply an acknowledgment message ``SYN/ACK’’ to the sender. Thismessage has two sequence numbers. The seq in the ACK is 424CF1DD, which is to confirm the last ``SYN’’ from sender. The seq in the SYN is 30318555, which is a new message from the receiver.●Thirdly, the sender reply an acknowledgment message ``ACK’’ to the receiver. The seq in theACK is 30318556, which is to confirm the last ``SYN’’ from receiver.In the end, both the sender and receiver knows that the other side is ready for this TCP connection.[Question 12] TCP congestion control(1) Both flow control and congestion control in TCP are realized by window based packet control. How can TCP get the window sizes in these two mechanisms?(2) Assume that TCP implements an extension that allows window sizes much larger than 64 KB. Suppose that you are using this extended TCP over a 1Gbps link with a latency of 150ms. TCP packet size is 1KB, and the max receive window is 1 MB. Suppose there is no real congestion and packet loss in transmission. How many RTTs does it take until slow start opens the send window to 1 MB? How long does it take to send the complete file? ( Suppose file size is 10MB )Solution:(1) In flow control, TCP sender knows the window size by the field of advertise-window replied from the receiver. In congestion control, TCP sender learns the window size adaptively by AIMD( Additive Increase and Multiplicative Decrease) mechanism responding to the packet lossevent.(2)When TCP realizes congestion control mechanism, its effective send window size will be min (CongestionWindow, AdvertizedWindow). In original design of TCP header, the field of AdvertizedWindow is 16 bit, which is 216=26*210=64 KB. So the maximum effective window of original TCP sender is 64KB. The assumption of the first sentence in this question relaxes such constraint for TCP.In slow start, the send window starts from w0=1 packet, which is 1 KB. For each RTT after a successful transmission, the window size will be doubled. After i RTT, it will be 2i * w0. Let 2i * 1KB = 1MB, soi = log2(1MB/1KB) = log2(210) = 10.It will take 10 RTTs to reach 1MB send window.Case 1: if the receiver window remains as 1MBIn the first 10 RTTs, total (1 + 2 + 4 + … + 210) * 1KB has been transmitted.Which is (211 - 1) * 1KB = 2 MB - 1 KB, the rest file is 10MB - (2MB - 1KB) = 8MB + 1KBIn the reset transmission, each RTT can only support 1MB transmission.Thus, additional 9 RTTs are required. Total 19 RTT = 19 * 150ms = 2.85 sCase 2: if the receiver window can be changed.Since there is no congestion and loss, the maximum send window will be the bandwidth * delay for this TCP connection.w max= 1G bps * 150ms = 109 * 150 * 10-3= 150 *106 bit = 18.75 * 106 byte = 17.88 MB.So, this 10 MB file can be transferred before reaching w max. In another word, it can be sent in its slow start phase. Assume x RTT is required to send this file, then:(1 + 2 + 4 + … + 2x) * 1KB ≥ 10 MB2 * 2x–1 ≥ 10 * 1024x ≥ log2(10241) – 1 = 12.3Thus x = 13, it will take 13 RTTs to transfer this file. 13RTT = = sTotal delay = 13RTT + Filesize/BW = 13 * 150ms+ 10MB / 1Gbps =1.95 + 0.08 * 1.024^2=2.03 s11。
计算机网络英文题库附答案chater
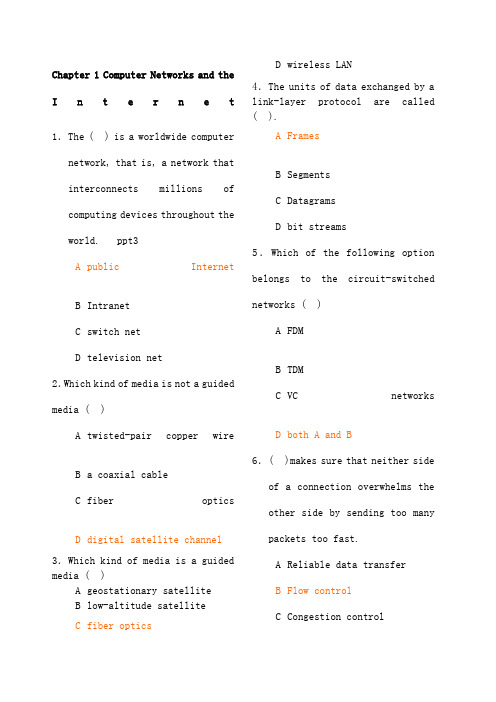
Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computernetwork, that is, a network that interconnectsmillionsofcomputing devices throughout theworld. ppt3 A public InternetB IntranetC switch netD television net2.Which kind of media is not a guidedmedia ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following optionbelongs to the circuit-switchednetworks ( )A FDMB TDMC VCnetworksD both A and B 6.( )makes sure that neither sideof a connection overwhelms theother side by sending too manypackets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch mustreceive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagramnetworksandvirtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, and virtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, and virtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuit networks use VC. numbers to forward packets toward their destination.D datagram networks use VC. numbers and virtual-circuit networks use destination addresses to forward packetstoward their destination.9.In the following options, which one is not a guided media ( )A twisted-pairwireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet ’s headerB wait to transmit the packet onto the linkC determine where to direct thepacketD check bit-error in the packet 11.In the following four descriptions, which one is correct ( )A The traffic intensity must begreater than 1.B The fraction of lost packetsincreases as the trafficintensity decreases.C If the traffic intensity isclose to zero, the averagequeuing delay will be close tozero.D If the traffic intensity isclose to one, the averagequeuing delay will be close toone.12.The Internet’s network layer is responsible for movingnetwork-layer packets known as( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layersare called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes ofpacket-switched networks: ( )networks and virtual-circuitnetworks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be looselyclassified into threecategories: residential access,company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue,R is the transmission rate, and all packets consist of L bits, then thetraffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR /aB La /RC Ra /LD LR /a 17.A 2B 1C 0D -118.In the Internet, the equivalentconcept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics 20.End systems access to the Internet through its ( ). A modemsB protocolsC ISPD sockets21.End systems, packet switches,and other pieces of the Internet, run ( ) that control thesending and receiving ofinformation within theInternet.A programsB processesC applicationsD protocols22.There are many private networks,such as many corporate andgovernment networks, whosehosts cannot exchange messages with hosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) runningon its end systems to exchangedata with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionlessunreliable service and ()service.A flowcontrolB connection-oriented reliableC congestion controlD TCP25.It defines the format and theorder of messages exchangedbetween two or morecommunicating entities, as wellas the actions taken on thetransmission and/or receipt ofa message or other event. Thesentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol ( )A the format of messagesexchanged between two or morecommunicating entitiesB the order of messagesexchanged between two or morecommunicating entitiesC the actions taken on thetransmission of a message orother eventD the transmission signals aredigital signals or analogsignals27.In the following options, which is defined in protocol ( )A the actions taken on thetransmission and/or receiptof a message or other event B the objects exchanged between communicating entities C the content in the exchangedmessagesD the location of the hosts28.In the following options, whichdoes not belong to the network edge( )A end systemsB routersC clientsD servers29.In the following options, whichbelongs to the network core ( )A end systemsB routersC clientsD servers30.In the following options, whichis not the bundled with theInternet’sconnection-oriented service( )A reliable data transferB guarantee of thetransmission timeC flow controlD congestion-control31.An application can rely on theconnection to deliver all of itsdata without error and in theproper order. The sentencedescribes ( ). A flow controlB congestion-controlC reliable datatransferD connection-oriented service 32.It makes sure that neither sideof a connection overwhelms theother side by sending too manypackets too fast. The sentence describes ( ). A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internetfrom entering a state of gridlock. When a packet switchbecomes congested, its bufferscan overflow and packet loss canoccur. The sentence describes( ).A flowcontrolB congestion-controlC connection-oriented serviceD reliable data transfer 34.TheInternet ’sconnection-oriented service has aname, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet ’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP( )A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP( )A InternetphoneB video conferencingC streamingmultimediaD telnet39.There are two fundamentalapproaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching40.In ( ) networks, the resourcesneeded along a path to provide for communication between the end system are reserved for theduration of the communicationsession.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’smessages use the resources ondemand, and as a consequence,may have to wait for access tocommunication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, foreach link used by the end-to-endconnection, the connection gets( ) of the link’s bandwidthfor the duration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rateof a circuit is equal to theframe rate multiplied by thenumber of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch mustreceive the entire packetbefore it can begin to transmitthe first bit of the packet ontothe outbound link.A Queuing delayB Store-and-forwardtransmissionC Packet lossD Propagation45.The network that forwardspackets according to host destination addresses is called( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwardspackets according tovirtual-circuit numbers iscalled ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, whichis not a kind of access network( )A residentialaccessB company accessC wirelessaccessD local access48.Suppose there is exactly onepacket switch between a sendinghost and a receiving host. The transmission rates between thesending host and the switch and between the switch and the receiving host are R 1 and R 2,respectively. Assuming that theswitch uses store-and-forwardpacket switching, what is thetotal end-to-end delay to senda packet of length L (Ignorequeuing delay, propagationdelay, and processing delay.) ( ) A L /R 1+L /R 2B L /R 1C L /R 2D none of the above49.The time required to examine thepacket ’s header and determinewhere to direct the packet ispart of the ( ). A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagatefrom the beginning of the linkto the next router is ( ). A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of3000bits over a path of 5 links. Eachlink transmits at 1000bps. Queuingdelays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is apacket-switched virtual circuitnetwork. VC setup time is seconds.Suppose the sending layers add atotal of 500 bits of header to eachpacket. How long does it take to sendthe file from source to destination(2).Suppose the network is a packet-switched datagram networkand a connectionless service is used.Now suppose each packet has 200 bitsof header. How long does it take tosend the file(3).Suppose that the network is acircuit-switched network. Furthersuppose that the transmission rate of the circuit between source anddestination is 200bps. Assumingsetup time and 200 bits of header appended to the packet, how longdoes it take to send the packetS olution:(1).t=5*(3000+500)/1000+=( 2).t=5*(3000+200)/1000=16s( 3).t=(3000+200)/200+=。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
Chapter 1 Computer Networks and the Internet1.The ( ) is a worldwide computer network, that is, a network that interconnects millions of computing devices throughout the world.ppt3A public InternetB IntranetC switch netD television net2.Which kind of media is not a guided media? ( )A twisted-pair copper wireB a coaxial cableC fiber opticsD digital satellite channel3.Which kind of media is a guided media? ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN4.The units of data exchanged by a link-layer protocol are called ( ).A FramesB SegmentsC DatagramsD bit streams5.Which of the following option belongs to the circuit-switched networks? ( )A FDMB TDMC VC networksD both A and B6.( )makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast.A Reliable data transferB Flow controlC Congestion controlD Handshaking procedure7.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Store-and-forward transmissionB FDMC End-to-end connectionD TDM8.Datagram networks and virtual-circuit networks differ in that ( ).A datagram networks are circuit-switched networks, andvirtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, andvirtual-circuit networks are circuit-switched networks.C datagram networks use destination addresses and virtual-circuitnetworks use VC. numbers to forward packets toward theirdestination.D datagram networks use VC. numbers and virtual-circuit networksuse destination addresses to forward packets toward their destination. 9.In the following options, which one is not a guided media? ( )A twisted-pair wireB fiber opticsC coaxial cableD satellite10.Processing delay does not include the time to ( ).A examine the packet’s headerB wait to transmit the packet onto the linkC determine where to direct the packetD check bit-error in the packet11.In the following four descriptions, which one is correct? ( )A The traffic intensity must be greater than 1.B The fraction of lost packets increases as the traffic intensitydecreases.C If the traffic intensity is close to zero, the average queuing delaywill be close to zero.D If the traffic intensity is close to one, the average queuing delaywill be close to one.12.The Internet’s network layer is responsible for moving network-layer packets known as ( ) from one host to another.A frameB datagramC segmentD message13.The protocols of various layers are called ( ).A the protocol stackB TCP/IPC ISPD network protocol14.There are two classes of packet-switched networks: ( ) networks and virtual-circuit networks.A datagramB circuit-switchedC televisionD telephone15.Access networks can be loosely classified into three categories: residential access, company access and ( ) access.A cabledB wirelessC campusD city areaQuestion 16~17Suppose, a is the average rate at which packets arrive at the queue, R is the transmission rate, and all packets consist of L bits, then the traffic intensity is ( 16 ), and it should no greater than ( 17 ).16. A LR/aB La/RC Ra/LD LR/a17.A 2B 1C 0D -118.In the Internet, the equivalent concept to end systems is ( ).A hostsB serversC clientsD routers19.In the Internet, end systems are connected together by ( ).A copper wireB coaxial cableC communication linksD fiber optics20.End systems access to the Internet through its ( ).A modemsB protocolsC ISPD sockets21.End systems, packet switches, and other pieces of the Internet, run ( ) that control the sending and receiving of information within theInternet.A programsB processesC applicationsD protocols22.There are many private networks, such as many corporate and government networks, whose hosts cannot exchange messages withhosts outside of the private network. These private networks are often referred to as ( ).A internetsB LANC intranetsD WAN23.The internet allows ( ) running on its end systems to exchange data with each other.A clients applicationsB server applicationsC P2P applicationsD distributed applications24.The Internet provides two services to its distributed applications: a connectionless unreliable service and () service.A flow controlB connection-oriented reliableC congestion controlD TCP25.It defines the format and the order of messages exchanged between two or more communicating entities, as well as the actions taken on thetransmission and/or receipt of a message or other event. The sentence describes ( ).A InternetB protocolC intranetD network26.In the following options, which does not define in protocol? ( )A the format of messages exchanged between two or morecommunicating entitiesB the order of messages exchanged between two or morecommunicating entitiesC the actions taken on the transmission of a message or other eventD the transmission signals are digital signals or analog signals 27.In the following options, which is defined in protocol? ( )A the actions taken on the transmission and/or receipt of a message orother eventB the objects exchanged between communicating entitiesC the content in the exchanged messagesD the location of the hosts28.In the following options, which does not belong to the network edge? ( )A end systemsB routersC clientsD servers29.In the following options, which belongs to the network core? ( )A end systemsB routersC clientsD servers30.In the following options, which is not the bundled with the Internet’s connection-oriented service? ( )A reliable data transferB guarantee of the transmission timeC flow controlD congestion-control31.An application can rely on the connection to deliver all of its data without error and in the proper order. The sentence describes ( ).A flow controlB congestion-controlC reliable data transferD connection-oriented service32.It makes sure that neither side of a connection overwhelms the other side by sending too many packets too fast. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer33.It helps prevent the Internet from entering a state of gridlock. When a packet switch becomes congested, its buffers can overflow and packet loss can occur. The sentence describes ( ).A flow controlB congestion-controlC connection-oriented serviceD reliable data transfer34.The Internet’s connection-oriented service has a name, it is ( ).A TCPB UDPC TCP/IPD IP35.In the following options, which service does not be provided to an application by TCP?( )A reliable transportB flow controlC video conferencingD congestion control36.The Internet’s connectionless service is called ( ).A TCPB UDPC TCP/IPD IP37.In the following options, which does not use TCP?( )A SMTPB internet telephoneC FTPD HTTP38.In the following options, which does not use UDP?( )A Internet phoneB video conferencingC streaming multimediaD telnet39.There are two fundamental approaches to building a network core, ( ) and packet switching.A electrical current switchingB circuit switchingC data switchingD message switching 40.In ( ) networks, the resources needed along a path to provide for communication between the end system are reserved for the duration of the communication session.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In ( ) networks, the resources are not reserved; a session’s messages use the resources on demand, and as a consequence, may have to wait for access to communication link.A packet-switchedB data-switchedC circuit-switchedD message-switched42.In a circuit-switched network, if each link has n circuits, for each link used by the end-to-end connection, the connection gets ( ) of thelink’s bandwidth for the duration of the connection.A a fraction 1/nB allC 1/2D n times43.For ( ), the transmission rate of a circuit is equal to the frame rate multiplied by the number of bits in a slot.A CDMAB packet-switched networkC TDMD FDM44.( ) means that the switch must receive the entire packet before it can begin to transmit the first bit of the packet onto the outbound link.A Queuing delayB Store-and-forward transmissionC Packet lossD Propagation45.The network that forwards packets according to host destination addresses is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram46.The network that forwards packets according to virtual-circuit numbers is called ( ) network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.In the following entries, which is not a kind of access network?( )A residential accessB company accessC wireless accessD local access48.Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and the receiving host are R1 and R2,respectively. Assuming that the switch uses store-and-forward packetswitching, what is the total end-to-end delay to send a packet of length L? (Ignore queuing delay, propagation delay, and processing delay.)( )A L/R1+L/R2B L/R1C L/R2D none of the above49.The time required to examine the packet’s header and determine where to direct the packet is part of the ( ).A queuing delayB processing delayC propagation delayD transmission delay50.The time required to propagate from the beginning of the link to the next router is ( ).A queuing delayB processing delayC propagation delayD transmission delay51.Consider sending a packet of 3000bits over a path of 5 links. Each link transmits at 1000bps. Queuing delays, propagation delay and processing delay are negligible. (6 points)(1).Suppose the network is a packet-switched virtual circuit network. VC setup time is 0.1 seconds. Suppose the sending layers add a total of 500 bits of header to each packet. How long does it take to send the file from source to destination?(2).Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 200 bits of header. How long does it take to send the file?(3).Suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is 200bps. Assuming 0.02s setup time and 200 bits of header appended to the packet, how long does it take to send the packet?Solution: (1). t=5*(3000+500)/1 000+0.1=17.6s(2). t=5*(3000+200)/1 000=16s(3). t=(3000+200)/20 0+0.02=16.02s。
