CCNA Security 第四天
信息安全工程师所需证书

信息安全工程师所需证书作为信息安全工程师,以下是一些常见的证书和资格,可以帮助你在这个领域获得认可和提升职业发展:1. CISSP(Certified Information Systems Security Professional)认证,这是国际上最受认可的信息安全专业认证之一,涵盖了广泛的安全领域知识和技能。
2. CISM(Certified Information Security Manager)认证,这是一项专注于信息安全管理的全球性认证,适合那些希望在信息安全领域担任管理职位的人员。
3. CEH(Certified Ethical Hacker)认证,这是一个专注于网络安全和渗透测试的认证,培养了对网络安全漏洞和攻击技术的理解和应对能力。
4. CompTIA Security+认证,这是一个广受欢迎的入门级信息安全认证,涵盖了网络安全、加密、身份验证等基本概念和技能。
5. GIAC(Global Information Assurance Certification)认证,GIAC提供了一系列专业认证,涵盖了各种信息安全领域,包括网络防御、逆向工程、数字取证等。
6. OSCP(Offensive Security Certified Professional)认证,这是一个专注于渗透测试和攻击技术的高级认证,要求通过一系列实践考试来证明技能。
此外,还有许多其他的信息安全认证和培训课程,如ISO 27001、CCNA Security、CISA等,可以根据个人兴趣和职业发展目标选择适合自己的证书。
需要注意的是,证书只是证明你具备一定知识和技能的一种方式,实际上,信息安全领域的知识和技能是不断发展和演变的,持续学习和实践同样重要。
证书只是一个起点,实际工作经验和对最新技术的了解同样重要。
怎样下载网络安全证书

怎样下载网络安全证书网络安全证书是一种由相关机构颁发的证明个人或组织在网络安全领域具备一定知识、技能和能力的证书。
获取网络安全证书可以提升个人或组织在网络安全行业的竞争力,并确保在网络活动中具备一定的保护能力。
下面是下载网络安全证书的步骤。
第一步:确定需要获取的网络安全证书类型网络安全领域有多种不同的证书类型,如CEH(Certified Ethical Hacker),CISSP(Certified Information Systems Security Professional),CISM(Certified Information Security Manager),CCNA Security等。
根据自己的需求和职业规划,选择适合的证书类型。
第二步:了解相关要求和准备材料每种证书都有不同的要求和准备材料,需要提前了解并全面准备。
通常要求参加相关培训课程,并通过笔试或实操考核达到一定的分数或通过率。
还可能需要提交个人简历、推荐信等文件。
第三步:选择合适的培训机构或自学获取网络安全证书通常需要参加培训课程,以帮助学习和准备考试内容。
可以选择线上或线下的培训机构,根据个人情况和时间安排选择合适的培训方式。
如果自学能力强,也可以自学相关内容,但需要确保学习的材料和资源有效且与考试要求相符。
第四步:注册并参加考试在完成培训课程或自学后,需要注册并参加相关考试。
根据证书类型和相关机构的要求,选择合适的考试时间和地点。
通常考试会分为笔试和实操两个部分,根据实际情况做好相应的准备。
第五步:通过考试并获得证书通过合格的考试成绩后,会获得网络安全证书。
证书通常由相关机构发放,上面会有个人或组织的相关信息和证书有效期限,可以作为求职或业务推广的重要凭证。
第六步:持续学习和更新证书网络安全领域变化快速,持有的证书可能需要定期更新。
为了保持竞争力和专业知识的最新状态,需要持续学习和关注网络安全领域的最新动态,并参加合适的培训或考试来更新证书。
CCNA_Security_Packet_Tracer_导师实验说明书_v10
CCNA Security 1.0.1Instructor Packet Tracer ManualThis document is exclusive property of Cisco Systems, Inc. Permission is granted to print and copy this document for non-commercial distribution and exclusiveuse by instructors in the CCNA Security course as part of an official CiscoNetworking Academy Program.PT Activity: Configure Cisco Routers for Syslog, NTP, and SSH OperationsInstructor VersionTopology DiagramAddressing TableLearning Objectives•Configure routers as NTP clients.•Configure routers to update the hardware clock using NTP.•Configure routers to log messages to the syslog server.•Configure routers to timestamp log messages.•Configure local users.•Configure VTY lines to accept SSH connections only.•Configure RSA key pair on SSH server.•Verify SSH connectivity from PC client and router client.IntroductionThe network topology shows three routers. You will configure NTP and Syslog on all routers. You will configure SSH on R3.Network Time Protocol (NTP) allows routers on the network to synchronize their time settings with an NTP server. A group of NTP clients that obtain time and date information from a single source have more consistent time settings and Syslog messages generated can be analyzed more easily. This can help when troubleshooting issues with network problems and attacks. When NTP is implemented in the network, it can be set up to synchronize to a private master clock, or to a publicly available NTP server on the Internet.The NTP Server is the master NTP server in this lab. You will configure the routers to allow the software clock to be synchronized by NTP to the time server. Also, you will configure the routers to periodically update the hardware clock with the time learned from NTP. Otherwise, the hardware clock will tend to gradually lose or gain time (drift) and the software clock and hardware clock may become out of synchronization with each other. The Syslog Server will provide message logging in this lab. You will configure the routers to identify the remote host (Syslog server) that will receive logging messages.You will need to configure timestamp service for logging on the routers. Displaying the correct time and date in Syslog messages is vital when using Syslog to monitor a network. If the correct time and date of a message is not known, it can be difficult to determine what network event caused the message.R2 is an ISP connected to two remote networks: R1 and R3. The local administrator at R3 can perform most router configurations and troubleshooting; however, since R3 is a managed router, the ISP needs access to R3 for occasional troubleshooting or updates. To provide this access in a secure manner, the administrators have agreed to use Secure Shell (SSH).You use the CLI to configure the router to be managed securely using SSH instead of Telnet. SSH is a network protocol that establishes a secure terminal emulation connection to a router or other networking device. SSH encrypts all information that passes over the network link and provides authentication of the remote computer. SSH is rapidly replacing Telnet as the remote login tool of choice for network professionals.The servers have been pre-configured for NTP and Syslog services respectively. NTP will not require authentication. The routers have been pre-configured with the following:•Enable password: ciscoenpa55•Password for vty lines: ciscovtypa55•Static routingTask 1: Configure routers as NTP Clients.S tep 1.T es t C onnectivity•Ping from PC-C to R3.•Ping from R2 to R3.•Telnet from PC-C to R3. Exit the Telnet session.•Telnet from R2 to R3. Exit the Telnet session.S tep 2.C onfigure R1, R2 and R3 as NT P clients.R1(config)# ntp server 192.168.1.5R2(config)# ntp server 192.168.1.5R3(config)# ntp server 192.168.1.5Verify client configuration using the command show ntp status.S tep 3.C onfigure routers to update hardware clock.Configure R1, R2 and R3 to periodically update the hardware clock with the time learned from NTP.R1(config)# ntp update-calendarR2(config)# ntp update-calendarR3(config)# ntp update-calendarVerify that the hardware clock was updated using the command show clock.S tep 4.C onfigure routers to times tamp log mes s ages.Configure timestamp service for logging on the routers.R1(config)# service timestamps log datetime msecR2(config)# service timestamps log datetime msecR3(config)# service timestamps log datetime msecTask 2: Configure routers to log messages to the Syslog Server.S tep 1.C onfigure the routers to identify the remote hos t (S ys log S erver) that will receive logging mes s ages.R1(config)# logging host 192.168.1.6R2(config)# logging host 192.168.1.6R3(config)# logging host 192.168.1.6The router console will display a message that logging has started.S tep 2.Verify logging configuration us ing the command s how logging.S tep 3.E xamine logs of the S ys log s erver.From the Config tab of the Syslog server’s dialogue box, select the Syslog services button. Observe the logging messages received from the routers.Note: Log messages can be generated on the server by executing commands on the router. For example, entering and exiting global configuration mode will generate an informational configuration message.Task 3: Configure R3 to support SSH connections.S tep 1.C onfigure a domain name.Configure a domain name of on R3.R3(config)# ip domain-name S tep 2.C onfigure us ers for login from the S S H client on R3.Create a user ID of SSHadmin with the highest possible privilege level and a secret password ofciscosshpa55.R3(config)# username SSHadmin privilege 15 secret ciscosshpa55S tep 3.C onfigure the incoming VT Y lines on R3.Use the local user accounts for mandatory login and validation. Accept only SSH connections.R3(config)# line vty 0 4R3(config-line)# login localR3(config-line)# transport input sshS tep 4.E ras e exis ting key pairs on R3.Any existing RSA key pairs should be erased on the router.R3(config)#crypto key zeroize rsaNote: If no keys exist, you might receive this message: % No Signature RSA Keys found in configuration.S tep 5.G enerate the R S A encryption key pair for R3.The router uses the RSA key pair for authentication and encryption of transmitted SSH data. Configure the RSA keys with a modulus of 1024. The default is 512, and the range is from 360 to 2048.R3(config)# crypto key generate rsa [Enter]The name for the keys will be: Choose the size of the key modulus in the range of 360 to 2048 for yourGeneral Purpose Keys. Choosing a key modulus greater than 512 may takea few minutes.How many bits in the modulus [512]:1024% Generating 1024 bit RSA keys, keys will be non-exportable...[OK]Note: The command to generate RSA encryption key pairs for R3 in Packet Tracer differs from those used in the lab.S tep 6.Verify the S S H configuration.Use the show ip ssh command to see the current settings. Verify that the authentication timeout and retries are at their default values of 120 and 3.S tep 7.C onfigure S S H timeouts and authentication parameters.The default SSH timeouts and authentication parameters can be altered to be more restrictive. Set the timeout to 90 seconds, the number of authentication retries to 2, and the version to 2.R3(config)# ip ssh time-out 90R3(config)# ip ssh authentication-retries 2R3(config)# ip ssh version 2Issue the show ip ssh command again to confirm that the values have been changed.S tep 8.Attempt to connect to R3 via T elnet from P C-C.Open the Desktop of PC-C. Select the Command Prompt icon. From PC-C, enter the command to connect to R3 via Telnet.PC> telnet 192.168.3.1This connection should fail, since R3 has been configured to accept only SSH connections on the virtual terminal lines.S tep 9.C onnect to R3 us ing S S H on P C-C.Open the Desktop of PC-C. Select the Command Prompt icon. From PC-C, enter the command to connect to R3 via SSH. When prompted for the password, enter the password configured for the administrator ciscosshpa55.PC> ssh –l SSHadmin 192.168.3.1S tep 10.C onnect to R3 us ing S S H on R2.In order to troubleshoot and maintain the R3 router, the administrator at the ISP must use SSH to access the router CLI. From the CLI of R2, enter the command to connect to R3 via SSH version 2 using the SSHadmin user account. When prompted for the password, enter the password configured for the administrator: ciscosshpa55.R2# ssh –v 2 –l SSHadmin 10.2.2.1S tep 11.C heck res ults.Your completion percentage should be 100%. Click Check Results to see feedback and verification of which required components have been completed.PT Activity: Configure AAA Authentication on Cisco Routers Instructor VersionTopology DiagramAddressing TableLearning Objectives•Configure a local user account on R1 and authenticate on the console and VTY lines using local AAA.•Verify local AAA authentication from the R1 console and the PC-A client.•Configure a server-based AAA authentication using TACACS+.•Verify server-based AAA authentication from PC-B client.•Configure a server-based AAA authentication using RADIUS.•Verify server-based AAA authentication from PC-C client.IntroductionThe network topology shows routers R1, R2 and R3. Currently all administrative security is based on knowledge of the enable secret password. Your task is to configure and test local and server-based AAA solutions.You will create a local user account and configure local AAA on router R1 to test the console and VTY logins.•User account: Admin1 and password admin1pa55You will then configure router R2 to support server-based authentication using the TACACS+ protocol. The TACACS+ server has been pre-configured with the following:•Client: R2 using the keyword tacacspa55•User account: Admin2 and password admin2pa55Finally, you will configure router R3 to support server-based authentication using the RADIUS protocol. The RADIUS server has been pre-configured with the following:•Client: R3 using the keyword radiuspa55•User account: Admin3 and password admin3pa55The routers have also been pre-configured with the following:•Enable secret password: ciscoenpa55•RIP version 2Note: The console and VTY lines have not been pre-configured.Task 1: Configure Local AAA Authentication for Console Access on R1S tep 1.T es t connectivity.•Ping from PC-A to PC-B.•Ping from PC-A to PC-C.•Ping from PC-B to PC-C.S tep 2.C onfigure a local us ername on R1.Configure a username of Admin1 and secret password of admin1pa55.R1(config)# username Admin1 password admin1pa55S tep 3.C onfigure local AAA authentication for cons ole acces s on R1.Enable AAA on R1 and configure AAA authentication for console login to use the local database.R1(config)# aaa new-modelR1(config)# aaa authentication login default localS tep 4.C onfigure the line cons ole to us e the defined AAA authentication method.Enable AAA on R1 and configure AAA authentication for console login to use the default method list.R1(config)# line console 0R1(config-line)# login authentication defaultS tep 5.Verify the AAA authentication method.Verify the user EXEC login using the local database.R1(config-line)# end%SYS-5-CONFIG_I: Configured from console by consoleR1# exitR1 con0 is now availablePress RETURN to get started.************ AUTHORIZED ACCESS ONLY *************UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.User Access VerificationUsername: Admin1Password: admin1pa55R1>Task 2: Configure Local AAA Authentication for VTY Lines on R1S tep 1.C onfigure a named lis t AAA authentication method for VT Y lines on R1.Configure a named list called TELNET-LOGIN to authenticate logins using local AAA.R1(config)# aaa authentication login TELNET-LOGIN localS tep 2.C onfigure the VT Y lines to us e the defined AAA authentication method.Configure the VTY lines to use the named AAA method.R1(config)# line vty 0 4R1(config-line)# l ogin authentication TELNET-LOGINR1(config-line)# endS tep 3.Verify the AAA authentication method.Verify the Telnet configuration. From the command prompt of PC-A, Telnet to R1.PC> telnet 192.168.1.1************ AUTHORIZED ACCESS ONLY *************UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.User Access VerificationUsername: Admin1Password: admin1pa55R1>Task 3: Configure Server-Based AAA Authentication Using TACACS+ on R2S tep 1.C onfigure a backup local databas e entry called Admin.For backup purposes, configure a local username of Admin and secret password of adminpa55.R2(config)# username Admin password adminpa55S tep 2.Verify the T AC AC S+ S erver configuration.Select the TACACS+ Server. From the Config tab, click on AAA and notice that there is a Network configuration entry for R2 and a User Setup entry for Admin2.S tep 3.C onfigure the T AC AC S+ s erver s pecifics on R2.Configure the AAA TACACS server IP address and secret key on R2.R2(config)# tacacs-server host 192.168.2.2R2(config)# tacacs-server key tacacspa55S tep 4.C onfigure AAA login authentication for cons ole acces s on R2.Enable AAA on R2 and configure all logins to authenticate using the AAA TACACS+ server and if not available, then use the local database.R2(config)# aaa new-modelR2(config)# aaa authentication login default group tacacs+ localS tep 5.C onfigure the line cons ole to us e the defined AAA authentication method.Configure AAA authentication for console login to use the default AAA authentication method.R2(config)# line console 0R2(config-line)# login authentication defaultS tep 6.Verify the AAA authentication method.Verify the user EXEC login using the AAA TACACS+ server.R2(config-line)# end%SYS-5-CONFIG_I: Configured from console by consoleR2# exitR2 con0 is now availablePress RETURN to get started.************ AUTHORIZED ACCESS ONLY *************UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.User Access VerificationUsername: Admin2Password: admin2pa55R2>CCNA SecurityTask 4: Configure Server-Based AAA Authentication Using RADIUS on R3S tep 1.C onfigure a backup local databas e entry called Admin.For backup purposes, configure a local username of Admin and secret password of adminpa55.R3(config)# username Admin password adminpa55S tep 2.Verify the R ADIUS S erver configuration.Select the RADIUS Server. From the Config tab, click on AAA and notice that there is a Network configuration entry for R3 and a User Setup entry for Admin3.S tep 3.C onfigure the R ADIUS s erver s pecifics on R3.Configure the AAA RADIUS server IP address and secret key on R3.R3(config)# radius-server host 192.168.3.2R3(config)# radius-server key radiuspa55S tep 4.C onfigure AAA login authentication for cons ole acces s on R3.Enable AAA on R3 and configure all logins to authenticate using the AAA RADIUS server and if not available, then use the local database.R3(config)# aaa new-modelR3(config)# aaa authentication login default group radius localS tep 5.C onfigure the line cons ole to us e the defined AAA authentication method.Configure AAA authentication for console login to use the default AAA authentication method.R3(config)# line console 0R3(config-line)# login authentication defaultS tep 6.Verify the AAA authentication method.Verify the user EXEC login using the AAA TACACS+ server.R3(config-line)# end%SYS-5-CONFIG_I: Configured from console by consoleR3# exitR3 con0 is now availablePress RETURN to get started.************ AUTHORIZED ACCESS ONLY *************UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.User Access VerificationUsername: Admin3Password: admin3pa55R3>S tep 7.C heck res ults.Your completion percentage should be 100%. Click Check Results to see feedback and verification of which required components have been completed.PT Activity: Configure IP ACLs to Mitigate AttacksInstructor VersionTopology DiagramAddressing TableObjectives•Verify connectivity among devices before firewall configuration.•Use ACLs to ensure remote access to the routers is available only from management station PC-C.•Configure ACLs on R1 and R3 to mitigate attacks.•Verify ACL functionality.IntroductionAccess to routers R1, R2, and R3 should only be permitted from PC-C, the management station. PC-C is also used for connectivity testing to PC-A, a server providing DNS, SMTP, FTP, and HTTPS services.Standard operating procedure is to apply ACLs on edge routers to mitigate common threats based on source and/or destination IP address. In this activity, you create ACLs on edge routers R1 and R3 to achieve this goal. You then verify ACL functionality from internal and external hosts.The routers have been pre-configured with the following:•Enable password: ciscoenpa55•Password for console: ciscoconpa55•Username for VTY lines: SSHadmin•Password for VTY lines: ciscosshpa55•IP addressing•Static routingTask 1: Verify Basic Network ConnectivityVerify network connectivity prior to configuring the IP ACLs.S tep 1.F rom the P C-C command prompt, ping the P C-A s erver.S tep 2.F rom the P C-C command prompt, S S H to the router R2 L o0 interface. E xit the S S H s es s ion.S tep 3.F rom P C-C, open a web brows er to the P C-A s erver (us ing the IP addres s) to dis play the web page. C los e the brows er on P C-C.S tep 4.F rom the P C-A s erver command prompt, ping P C-C.Task 2: Secure Access to RoutersS tep 1.C onfigure AC L10 to block all remote acces s to the routers except from P C-C.Use the access-list command to create a numbered IP ACL on R1, R2, and R3.R1(config)# access-list 10 permit 192.168.3.3 0.0.0.0R2(config)# access-list 10 permit 192.168.3.3 0.0.0.0R3(config)# access-list 10 permit 192.168.3.3 0.0.0.0S tep 2.Apply AC L 10 to ingres s traffic on the VT Y lines.Use the access-class command to apply the access list to incoming traffic on the VTY lines.R1(config-line)# access-class 10 inR2(config-line)# access-class 10 inR3(config-line)# access-class 10 inS tep 3.Verify exclus ive acces s from management s tation P C-C.SSH to 192.168.2.1 from PC-C (should be successful). SSH to 192.168.2.1 from PC-A (should fail).PC> ssh –l SSHadmin 192.168.2.1Task 3: Create a Numbered IP ACL 100On R3, block all packets containing the source IP address from the following pool of addresses: 127.0.0.0/8, any RFC 1918 private addresses, and any IP multicast address.S tep 1. C onfigure AC L 100 to block all s pecified traffic from the outs ide network.You should also block traffic sourced from your own internal address space if it is not an RFC 1918 address (in this activity, your internal address space is part of the private address space specified in RFC 1918).Use the access-list command to create a numbered IP ACL.R3(config)# access-list 100 deny ip 10.0.0.0 0.255.255.255 anyR3(config)# access-list 100 deny ip 172.16.0.0 0.15.255.255 anyR3(config)# access-list 100 deny ip 192.168.0.0 0.0.255.255 anyR3(config)# access-list 100 deny ip 127.0.0.0 0.255.255.255 anyR3(config)# access-list 100 deny ip 224.0.0.0 15.255.255.255 anyR3(config)# access-list 100 permit ip any anyS tep 2.Apply the AC L to interface S erial 0/0/1.Use the ip access-group command to apply the access list to incoming traffic on interface Serial 0/0/1.R3(config)# interface s0/0/1R3(config-if)# ip access-group 100 inS tep 3.C onfirm that the s pecified traffic entering interface S erial 0/0/1 is dropped.From the PC-C command prompt, ping the PC-A server. The ICMP echo replies are blocked by the ACL since they are sourced from the 192.168.0.0/16 address space.S tep 4.R emove the AC L from interface S erial 0/0/1.Remove the ACL. Otherwise, all traffic from the outside network (being addressed with private source IP addresses) will be denied for the remainder of the PT activity.Use the no ip access-group command to remove the access list from interface Serial 0/0/1.R3(config)# interface s0/0/1R3(config-if)# no ip access-group 100 inTask 4: Create a Numbered IP ACL 110Deny all outbound packets with source address outside the range of internal IP addresses.S tep 1.C onfigure AC L110 to permit only traffic from the ins ide network.Use the access-list command to create a numbered IP ACL.R3(config)# access-list 110 permit ip 192.168.3.0 0.0.0.255 anyS tep 2.Apply the AC L to interface F0/1.Use the ip access-group command to apply the access list to incoming traffic on interface F0/1.R3(config)# interface fa0/1R3(config-if)# ip access-group 110 inTask 5: Create a Numbered IP ACL 120Permit any outside host to access DNS, SMTP, and FTP services on server PC-A, deny any outside host access to HTTPS services on PC-A, and permit PC-C to access R1 via SSH.S tep 1.Verify that P C-C can acces s the P C-A via HT T P S us ing the web brows er.Be sure to disable HTTP and enable HTTPS on server PC-A.S tep 2.C onfigure AC L 120 to s pecifically permit and deny the s pecified traffic.Use the access-list command to create a numbered IP ACL.R1(config)# access-list 120 permit udp any host 192.168.1.3 eq domainR1(config)# access-list 120 permit tcp any host 192.168.1.3 eq smtpR1(config)# access-list 120 permit tcp any host 192.168.1.3 eq ftpR1(config)# access-list 120 deny tcp any host 192.168.1.3 eq 443R1(config)# access-list 120 permit tcp host 192.168.3.3 host 10.1.1.1 eq22S tep 3.Apply the AC L to interface S0/0/0.Use the ip access-group command to apply the access list to incoming traffic on interface S0/0/0.R1(config)# interface s0/0/0R1(config-if)# ip access-group 120 inS tep 4.Verify that P C-C cannot acces s P C-A via HT T P S us ing the web brows er.Task 6: Modify An Existing ACLPermit ICMP echo replies and destination unreachable messages from the outside network (relative to R1); deny all other incoming ICMP packets.S tep 1.Verify that P C-A cannot s ucces s fully ping the loopback interface on R2.S tep 2.Make any neces s ary changes to AC L 120 to permit and deny the s pecified traffic.Use the access-list command to create a numbered IP ACL.R1(config)# access-list 120 permit icmp any any echo-replyR1(config)# access-list 120 permit icmp any any unreachableR1(config)# access-list 120 deny icmp any anyR1(config)# access-list 120 permit ip any anyS tep 3.Verify that P C-A can s ucces s fully ping the loopback interface on R2.S tep 4.C heck res ults.Your completion percentage should be 100%. Click Check Results to see feedback and verification of which required components have been completed.PT Activity: Configuring Context-Based Access Control (CBAC) Instructor VersionTopology DiagramAddressing TableLearning Objectives•Verify connectivity among devices before firewall configuration.•Configure an IOS firewall with CBAC on router R3•Verify CBAC functionality using ping, Telnet, and HTTP.IntroductionContext-Based Access Control (CBAC) is used to create an IOS firewall. In this activity, you will create a basic CBAC configuration on edge router R3. R3 provides access to resources outside of the network for hosts on the inside network. R3 blocks external hosts from accessing internal resources. After the configuration is complete, you will verify firewall functionality from internal and external hosts.The routers have been pre-configured with the following:•Enable password: ciscoenpa55•Password for console: ciscoconpa55•Password for vty lines: ciscovtypa55•IP addressing•Static routing•All switch ports are in VLAN 1 for switches S1 and S3.Task 1: Block Traffic From OutsideS tep 1.Verify B as ic Network C onnectivity.Verify network connectivity prior to configuring the IOS firewall.•From the PC-C command prompt, ping the PC-A server.•From the PC-C command prompt, Telnet to the Router R2 S0/0/1 interface: IP address 10.2.2.2. Exit the Telnet session.•From PC-C, open a web browser to the PC-A server to display the web page. Close the browser on PC-C.•From the PC-A server command prompt, ping PC-C.S tep 2.C onfigure a named IP AC L on R3 to block all traffic originating from the outs ide network.Use the ip access-list extended command to create a named IP ACL.R3(config)# ip access-list extended OUT-INR3(config-ext-nacl)# deny ip any anyR3(config-ext-nacl)# exitS tep 3.Apply the AC L to interface S erial 0/0/1.R3(config)# interface s0/0/1R3(config-if)# ip access-group OUT-IN inS tep 4.C onfirm that traffic entering interface S erial 0/0/1 is dropped.From the PC-C command prompt, ping the PC-A server. The ICMP echo replies are blocked by the ACL. Task 2: Create a CBAC Inspection RuleS tep 1.C reate an ins pection rule to ins pect IC MP, T elnet, and HTT P traffic.R3(config)# ip inspect name IN-OUT-IN icmpR3(config)# ip inspect name IN-OUT-IN telnetR3(config)# ip inspect name IN-OUT-IN httpS tep 2.T urn on time-s tamped logging and C B AC audit trail mes s ages.Use the ip inspect audit-trail command to turn on CBAC audit messages to provide a record of network access through the firewall, including illegitimate access attempts. Enable logging to the syslog server,192.168.1.3, with the logging host command. Make sure that logged messages are timestamped.R3(config)# ip inspect audit-trailR3(config)# service timestamps debug datetime msecR3(config)# logging host 192.168.1.3S tep 3.Apply the ins pection rule to egres s traffic on interface S0/0/1.R3(config-if)# ip inspect IN-OUT-IN outS tep 4.Verify that audit trail mes s ages are being logged on the s ys log s erver.•From PC-C, test connectivity to PC-A with ping, Telnet, and HTTP. Ping and HTTP should be successful. Note that PC-A will reject the Telnet session.•From PC-A, test connectivity to PC-C with ping and Telnet. All should be blocked.•Review the syslog messages on server PC-A: click the Config tab and then click the SYSLOG option.Task 3: Verify Firewall FunctionalityS tep 1.Open a T elnet s es s ion from P C-C to R2.The Telnet should succeed. While the Telnet session is active, issue the command show ip inspect sessions on R3. This command displays the existing sessions that are currently being tracked and inspected by CBAC.R3# show ip inspect sessionsEstablished SessionsSession 100424296 (192.168.3.3:1031)=>(10.1.1.2:23) telnet SIS_OPENExit the Telnet session.S tep 2.F rom P C-C, open a web brows er to the P C-A s erver web page us ing the s erver IP addres s. The HTTP session should succeed. While the HTTP session is active, issue the command show ip inspect sessions on R3.R3# show ip inspect sessionsEstablished SessionsSession 104637440 (192.168.3.3:1032)=>(192.168.1.3:http SIS_OPENNote: If the HTTP session times out before you execute the command on R3, you will have to click the Go button on PC-C to generate a session between PC-C and PC-A.Close the browser on PC-C.。
cisco网络安全认证

cisco网络安全认证Cisco网络安全认证(Cisco Certified Network Associate Security,简称CCNA Security)是由思科公司提供的网络安全认证,主要用于验证网络安全工程师的能力和技能。
它不仅涵盖了网络安全的基本概念和技术,还包括了网络设备的配置和管理。
CCNA Security认证涵盖了诸多的网络安全领域,包括网络威胁防护、VPN技术、防火墙配置、入侵检测与防御、网络访问控制和安全策略等。
通过CCNA Security认证,网络安全工程师可以了解和掌握网络安全的基本原理和技术,能够保护企业网络系统免受各种网络攻击的威胁。
CCNA Security认证的学习过程主要包括学习网络安全的基本理论知识和技术原理,以及学习网络设备的配置和管理。
学员需要了解各类网络攻击和威胁,熟悉网络安全防御的基本方法和技术。
在实践环节中,学员需要通过虚拟实验和实际操作来掌握网络设备的配置和管理,熟练运用各类网络安全工具和软件。
CCNA Security认证对于网络安全工程师来说具有重要意义。
首先,它提供了一个标准化的认证体系,能够证明网络安全工程师具备一定的技术水平和实践能力。
其次,CCNA Security 认证可以帮助网络安全工程师提升自己的职业能力和竞争力,有助于在职场上获得更好的发展机会和职位。
此外,CCNA Security认证还可以增加网络安全工程师在企业中的信任度和影响力,为企业提供更加安全可靠的网络环境。
思科公司作为国际领先的网络技术服务商,其提供的CCNA Security认证具有广泛的应用和认可度。
在日益增多的网络攻击和威胁背景下,网络安全问题越来越受到关注,对网络安全工程师的需求也不断增加。
因此,持有CCNA Security认证的网络安全工程师将在就业市场上具有更大的竞争优势,有望获得更好的职业发展和薪资待遇。
总之,CCNA Security认证是思科公司提供的一项重要的网络安全认证,对于网络安全工程师来说具有重要的意义。
CCNA介绍学习指南教程

CCNA介绍_学习指南教程CCNACCNA证书CCNA认证标志着具备安装、配置、运行中型路由和交换网络,并进行故障排除的能力。
获得CCNA认证的专业人士拥有相应的知识和技能,能够通过广域网与远程站点建立连接,消除基本的安全威胁,了解无线网络接入的要求。
CCNA培训包括(但不限于)以下这些协议的使用:IP、EIGRP、串行线路接口协议、帧中继、RI Pv2、VLAN、以太网和访问控制列表(ACL)。
CCNA徽标CCNA 1-4思科认证网络工程师(CCNA)是思科职业认证的第一步,最低要求为280个学时。
该课程的侧重点是解决在科学、通讯和社会研究等领域的网络应用中的问题。
CCNA考前图解说明学员将学习如何在局域网和广域网(LAN和WAN)的多协议网络中安装和配置思科交换机和路由器,提供一级故障排除服务并改善网络的性能和安全性。
此外,本课程还提供了关于正确应用网络软件工具和保养、维护硬件设备的相关培训。
CCNA面向高中和高中以上程度的学员,包含以下内容:CCNA1-网络基础完成CCNA1课程后,学员将了解以下网络基础知识:网络基础概念以太网技术基础网络模型,七层OSI TCI/IP 网络传输介质,例如铜缆、光纤、无线、IP、寻址、路由。
CCNA2-路由器和路由基础完成CCNA2课程后,学员将了解以下路由器和路由知识:IOS管理路由器配置基础路由协议TCP/IP基本概念访问控制表网络故障排除技能CCNA3-数据交换基础和中间路由完成CCNA3课程后,学员将了解以下数据交换和中间路由知识:VLSM基础RIP第二版OSPF、EIGRP基础交换机配置生成树协议虚拟局域网虚拟中继协议虚拟局域网间路由CCNA4-广域网技术完成CCNA4课程后,学员将了解到以下SAN技术基础知识:扩展IP地址、NAT和PAT DHCP协议ISDN和DDR 帧中继PPP 网络管理协议基础、SNMP行业标准认证CCNA课程将为学员通过CCNA认证奠定基础。
ccer相关的注册证书

ccer相关的注册证书【最新版】目录E 证书的概述E 证书的种类E 证书的获取方式E 证书的作用E 证书的注意事项正文E 证书的概述CCE(Certified Cisco Certification Expert)认证,即思科认证专家认证,是思科系统公司推出的一项网络技术认证。
该认证旨在帮助网络工程师提升技术水平,同时为企业提供一种衡量员工网络技术能力的标准。
CCE 证书是网络工程师在网络技术领域的一块“敲门砖”,能够帮助他们拓宽职业发展道路,提升自身价值。
E 证书的种类CCE 证书分为多个种类,根据不同的网络技术领域,主要可以分为以下几类:(1)路由和交换:涉及网络路由、交换技术等方面的知识,如 CCNA (Cisco Certified Network Associate,思科认证网络工程师)和 CCNP (Cisco Certified Network Professional,思科认证网络专家)等。
(2)安全:主要涉及网络安全领域的知识,如 CCNA Security、CCNP Security 等。
(3)无线:涉及无线网络技术方面的知识,如 CCNA Wireless、CCNPWireless 等。
(4)数据平面:涉及数据平面技术,如 CCNA Data Center、CCNP Data Center 等。
(5)协作:涉及协作技术,如 CCNA Collaboration、CCNP Collaboration 等。
E 证书的获取方式要获得 CCE 证书,需要通过思科系统公司组织的认证考试。
这些考试分为两个层次:笔试和实验。
笔试主要测试考生对相关网络技术领域的理论知识;实验考试则要求考生在实际网络环境中完成指定任务,测试其实践操作能力。
E 证书的作用CCE 证书在网络技术领域具有很高的认可度,能够为持有者带来以下优势:(1)提升个人技能:通过学习和备考,可以帮助网络工程师系统地掌握网络技术知识,提升自身技能水平。
系统运维相关资格证书

系统运维相关资格证书及简介系统运维是信息技术领域的一个重要分支,负责维护和管理计算机系统、服务器、网络和基础设施,以确保其正常运行。
以下是一些与系统运维相关的资格证书以及它们的简介:CompTIA IT Fundamentals(ITF+):简介:CompTIA ITF+认证旨在评估个人对计算机和IT领域的基础知识。
它涵盖了计算机硬件、软件、网络和安全等基础概念。
这是一个入门级证书,适用于那些刚刚开始其IT职业生涯的人员。
CompTIA A+:简介:CompTIA A+是一项广泛认可的证书,旨在衡量IT专业人员的硬件和软件技能。
持有此证书的人可以进行计算机维护、故障排除、操作系统管理和网络设置等工作。
Microsoft Certified:Azure Administrator Associate:简介:这是由微软提供的云计算相关证书,旨在评估Azure云平台的管理员技能。
持有此证书的专业人员可以负责配置、管理和维护Azure基础架构。
Cisco Certified Network Associate(CCNA):简介:CCNA是由思科提供的网络认证,它涵盖了网络配置、管理和故障排除等领域。
持有CCNA证书的人可以在网络管理和运维方面发挥作用。
CompTIA Network+:简介:CompTIA Network+是一项专注于网络技能的认证,涵盖了网络拓扑、协议、安全性和故障排除等主题。
它是一个广泛认可的证书,适用于网络管理和运维人员。
Certified Information Systems Security Professional(CISSP):简介:CISSP是信息安全领域的高级认证,但它也与系统运维相关。
持有此证书的专业人员可以在确保系统和网络安全方面发挥作用。
Certified Information Systems Auditor(CISA):简介:CISA是一个关注信息系统审计和控制的认证。
CCNASecurityChap2答案
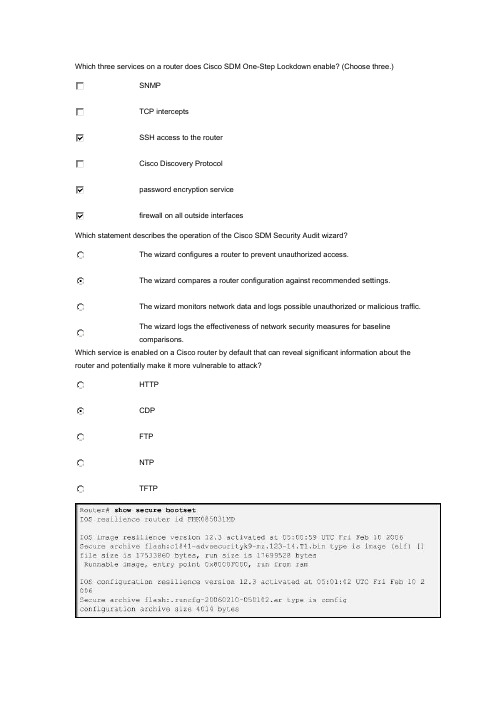
Which three services on a router does Cisco SDM One-Step Lockdown enable? (Choose three.)SNMPTCP interceptsSSH access to the routerCisco Discovery Protocolpassword encryption servicefirewall on all outside interfacesWhich statement describes the operation of the Cisco SDM Security Audit wizard?The wizard configures a router to prevent unauthorized access.The wizard compares a router configuration against recommended settings.The wizard monitors network data and logs possible unauthorized or malicious traffic.The wizard logs the effectiveness of network security measures for baselinecomparisons.Which service is enabled on a Cisco router by default that can reveal significant information about the router and potentially make it more vulnerable to attack?HTTPCDPFTPNTPTFTPRefer to the exhibit. What two facts can be determined from the output? (Choose two.)The Cisco IOS image and configuration files have been properly secured.ROMmon mode will be inaccessible upon entering the privileged EXEC reloadcommand.The Cisco IOS Resilient Configuration feature is enabled.The Cisco IOS Resilient Configuration feature has detected an image versionmismatch.The Cisco IOS configuration files have been erased.An administrator needs to create a user account with custom access to most privileged EXEC commands. Which privilege command is used to create this custom account?privilege exec level 0privilege exec level 1privilege exec level 2privilege exec level 15What is the minimum recommended modulus key length for keys generated to use with SSH?25651276810242048Which three options can be configured by Cisco AutoSecure? (Choose three.)CBACSNMPsyslogsecurity bannerinterface IP addressenable secret passwordWhich three commands are required to restore a primary bootset from a secure archive on a router on which Cisco IOS resilience is enabled? (Choose three.)Restart the router in ROM monitor mode and display the secure bootset Cisco IOS image name using the dir command.Restart the router, enter privileged EXEC mode, and display the secure bootset Cisco IOS image name using the show flash command.Boot the secure bootset Cisco IOS image using the boot command with the filename.Copy the secure bootset Cisco IOS image to flash using the copy IOS-backup-image flash command.Restore the secure configuration file using the copy config-backup flash command.Restore the secure configuration file using the secure boot-config restore filename command.Refer to the exhibit. Routers R1 and R2 are connected via a serial link. One router is configured as the NTP master, and the other is an NTP client. Which two pieces of information can be obtained from the partial output of the show ntp associations detail command on R2? (Choose two.)Both routers are configured to use NTPv2.Router R1 is the master, and R2 is the client.Router R2 is the master, and R1 is the client.The IP address of R1 is 192.168.1.2.The IP address of R2 is 192.168.1.2.What are two characteristics of SNMP community strings? (Choose two.)A vulnerability of SNMPv1, SNMPv2, and SNMPv3 is that they send the communitystrings in plaintext.Commonly known community strings should be used when configuring secure SNMP.If the manager sends one of the correct read-only community strings, it can getinformation and set information in an agent.SNMP read-only community strings can be used to get information from anSNMP-enabled device.SNMP read-write community strings can be used to set information on anSNMP-enabled device.What are three requirements that must be met if an administrator wants to maintain device configurations via secure in-band management? (Choose three.)network devices configured to accommodate SSHa separate network segment connecting all management devicesat least one router acting as a terminal serverencryption of all remote access management trafficconnection to network devices through a production network or the Internetdirect access to the console ports of all network devicesIf AAA is already enabled, which three CLI steps are required to configure a router with a specific view? (Choose three.)assign a secret password to the viewassign commands to the viewassign users who can use the viewassociate the view with the root viewcreate a superview using the parser view view-name commandcreate a view using the parser view view-name commandWhich two characteristics apply to Role-Based CLI Access superviews? (Choose two.)CLI views have passwords, but superviews do not have passwords.Users logged in to a superview can access all commands specified within the associatedCLI views.A single superview can be shared among multiple CLI views.Commands cannot be configured for a specific superview.Deleting a superview deletes all associated CLI views.Refer to the exhibit. Based on the output of the show running-config command, which type of view is SUPPORT?secret view, with a level 5 encrypted passwordroot view, with a level 5 encrypted secret passwordsuperview, containing SHOWVIEW and VERIFYVIEW viewsCLI view, containing SHOWVIEW and VERIFYVIEW commandsRefer to the exhibit. Which statement regarding the JR-Admin account is true?JR-Admin can issue show, ping, and reload commands.JR-Admin can issue ping and reload commands.JR-Admin can issue only ping commands.JR-Admin can issue debug and reload commands.JR-Admin cannot issue any command because the privilege level does not match one ofthose defined.Which recommended security practice prevents attackers from performing password recovery on a Cisco IOS router for the purpose of gaining access to the privileged EXEC mode?Keep a secure copy of the router Cisco IOS image and router configuration file as abackup.Disable all unused ports and interfaces to reduce the number of ways that the router canbe accessed.Configure secure administrative control to ensure that only authorized personnel canaccess the router.Locate the router in a secure locked room that is accessible only to authorized personnel.Provision the router with the maximum amount of memory possible.An administrator defined a local user account with a secret password on router R1 for use with SSH. Which three additional steps are required to configure R1 to accept only encrypted SSH connections? (Choose three.)configure the IP domain name on the routerenable inbound vty Telnet sessionsgenerate the SSH keysconfigure DNS on the routerenable inbound vty SSH sessionsgenerate two-way pre-shared keysBy default, how many seconds of delay between virtual login attempts is invoked when the loginblock-for command is configured?onetwothreefourfiveWhich set of commands are required to create a username of admin, hash the password using MD5, and force the router to access the internal username database when a user attempts to access the console?R1(config)# username admin password Admin01pa55R1(config)# line con 0R1(config-line)# login localR1(config)# username admin password Admin01pa55R1(config)# line con 0R1(config-line)# login internalR1(config)# username admin Admin01pa55 encr md5R1(config)# line con 0R1(config-line)# login localR1(config)# username admin secret Admin01pa55R1(config)# line con 0R1(config-line)# login localR1(config)# username admin secret Admin01pa55R1(config)# line con 0R1(config-line)# login internalWhich three areas of router security must be maintained to secure an edge router at the network perimeter? (Choose three.)physical securityflash securityoperating system securityremote access securityrouter hardeningzone isolationRefer to the exhibit. What two pieces of information can be gathered from the generated message? (Choose two.)This message is a level five notification message.This message appeared because a minor error occurred requiring further investigation.This message appeared because a major error occurred requiring immediate action.This message indicates that service timestamps have been globally enabled.This message indicates that enhanced security was configured on the vty ports.Refer to the exhibit. Which two statements describe the current SDM logging setup? (Choose two.)Buffered logging will be enabled on the router for Logging Level 7 messages.Buffered logging will be enabled on the syslog server for Logging Level 7 messages.All messages with a trap level of 4 and higher (less critical) will be logged.All messages with a trap level of 4 and lower (more critical) will be logged.The router interface IP address that is connected to the syslog server is 192.168.1.3.The syslog server IP address is 192.168.1.3.Refer to the exhibit. What is the significance of secret 5 in the generated output?The ADMIN password is encrypted using DH group 5.The ADMIN password is encrypted via the service password-encryption command.The ADMIN password is hashed using MD5.The ADMIN password is hashed using SHA.Which two operations are required to implement Cisco SDM One-Step Lockdown? (Choosetwo.)Choose the One-Step Lockdown feature.Apply the documented network policies.Deliver the configuration changes to the router.Compare the router configuration against recommended settings.Select the Firewall and ACL task on the SDM Configuration screen.Which statement matches the CLI commands to the SDM wizard that performs similar configuration functions?aaa configuration commands and the SDM Basic Firewall wizardauto secure privileged EXEC command and the SDM One-Step Lockdown wizardclass-maps, policy-maps, and service-policy configuration commands and the SDM IPSwizardsetup privileged EXEC command and the SDM Security Audit wizardWhat are two characteristics of the SDM Security Audit wizard? (Choose two.)It uses interactive dialogs and prompts to implement AAA.It automatically enables Cisco IOS firewall and implements Cisco IOS IPS security configurations to secure the router.It displays a screen with Fix-it check boxes to let you choose which potential security-related configuration changes to implement.It requires users to first identify which router interfaces connect to the inside network and which connect to the outside network.It is initiated from CLI and executes a script in which the managment plane functions and forwarding plane services are tested against known vulnerabilities.。
