第3章习题及答案..
第3章计算机网络体系结构(习题参考答案)
第3章计算机网络体系结构三、简答题1. 为什么要采用分层的方法解决计算机的通信问题?通过分层的方法,使得计算机网络复杂的通信处理问题转化成为若干相对较小的层次内的局部问题,对其进行的研究和处理变得相对容易。
2. “各层协议之间存在着某种物理连接,因此可以进行直接的通信。
”这句话对吗?不对。
物理连接只存在于最底层的下面。
各层协议之间只存在着称为“对等层通信”的逻辑连接。
3. 请简要叙述服务与协议之间的区别。
通过协议的规定,下一层可以为上一层提供服务,但是对于上一层的服务用户来说下面的协议是透明的。
协议是存在于对等层之间的,是水平的;服务存在于直接相邻的两个层次之间,是垂直的。
4. 请描述一下通信的两台主机之间通过OSI模型进行数据传输的过程。
发送数据的具体过程为:要进行通信的源用户进程首先将要传输的数据送至应用层并由该层的协议根据协议规范进行处理,为用户数据附加上控制信息后形成应用层协议数据单元再送至表示层;表示层根据本层的协议规范对收到的应用层协议数据单元进行处理,给应用层协议数据单元附加上表示层的控制信息后形成表示层的协议数据单元再将它传送至下一层。
数据按这种方式逐层向下传送直至物理层,最后由物理层实现比特流形式的传送。
当比特流沿着传输介质经过各种传输设备后最终到达了目标系统。
此后,接收数据的具体过程为:按照发送数据的逆过程,比特流从物理层开始逐层向上传送,在每一层都按照该层的协议规范以及数据单元的控制信息完成规定的操作,而后再将本层的控制信息剥离,并将数据部分向上一层传送,依此类推直至最终的、通信的目的用户进程。
5. 请简述虚电路服务的特点。
虚电路服务要求发送分组之前必须建立连接,即虚电路。
之后所有的分组都沿着虚电路依次进行传送。
在所有分组传送完毕后要释放连接。
它可以提供顺序、可靠的分组传输,适用于长报文的通信,一般应用于稳定的专用网络。
6. 请简述无连接服务的特点。
无连接服务无需事先建立连接。
第三章习题解答

第3章 力学基本定律与守恒律 习题及答案1.作用在质量为10 kg 的物体上的力为i t F)210(+=N ,式中t 的单位是s ,(1)求4s 后,这物体的动量和速度的变化.(2)为了使这力的冲量为200 N ·s ,该力应在这物体上作用多久,试就一原来静止的物体和一个具有初速度j 6-m ·s -1的物体,回答这两个问题.解: (1)若物体原来静止,则i t i t t F p t 1401s m kg 56d )210(d -⋅⋅=+==∆⎰⎰,沿x 轴正向,ip I imp v111111s m kg 56s m 6.5--⋅⋅=∆=⋅=∆=∆ 若物体原来具有6-1s m -⋅初速,则⎰⎰+-=+-=-=t tt F v m t m F v m p v m p 000000d )d (,于是⎰∆==-=∆t p t F p p p 0102d,同理, 12v v ∆=∆,12I I=这说明,只要力函数不变,作用时间相同,则不管物体有无初动量,也不管初动量有多大,那么物体获得的动量的增量(亦即冲量)就一定相同,这就是动量定理. (2)同上理,两种情况中的作用时间相同,即⎰+=+=tt t t t I 0210d )210(亦即 0200102=-+t t 解得s 10=t ,(s 20='t 舍去)2.一颗子弹由枪口射出时速率为10s m -⋅v ,当子弹在枪筒内被加速时,它所受的合力为 F =(bt a -)N(b a ,为常数),其中t 以秒为单位:(1)假设子弹运行到枪口处合力刚好为零,试计算子弹走完枪筒全长所需时间;(2)求子弹所受的冲量.(3)求子弹的质量. 解: (1)由题意,子弹到枪口时,有0)(=-=bt a F ,得ba t =(2)子弹所受的冲量⎰-=-=tbt at t bt a I 0221d )(将bat =代入,得 ba I 22=(3)由动量定理可求得子弹的质量202bv a v I m == 3.如图所示,一质量为m 的球,在质量为M 半径为R 的1/4圆弧形滑槽中从静止滑下。
马原,第三章习题及答案
第三章人类社会及其发展规律(课后练习题)一、单项选择题1 .人类社会历史发展的决定力量是( )A .生产方式B .地理条件C .社会意识D .人口因素2 .社会意识相对独立性的最突出表现是它( )A .同社会存在发展的不同步性B .具有历史的继承性C .对社会存在具有能动的反作用D .同社会经济的发展具有不平衡性3 .在生产关系中起决定作用的是( )A .生产资料所有制B .产品的分配和交换C .在生产中人与人的关系D .管理者和生产者的不同地位4 . “手推磨产生的是封建主的社会,蒸汽磨产生的是工业资本家的社会” , 这句话揭示了( )A .生产工具是衡量生产力水平的重要尺度B .科学技术是第一生产力C .社会形态的更替有其一定的顺序性D .物质生产的发展需要建立相应的生产关系5 .十一届三中全会以来,我党制定的一系列正确的路线、方针、政策促进了我国经济的迅猛发展,这说明( )A .经济基础发展的道路是由上层建筑决定的B .上层建筑的发展决定经济基础的发展方向C .上层建筑对经济基础具有积极的能动作用D .社会主义社会的发展不受经济基础决定上层建筑规律的制约6 .一定社会形态的经济基础是( )A .生产力B .该社会的各种生产关系C .政治制度和法律制度D .与一定生产力发展阶段相适应的生产关系的总和7 .上层建筑是指( )A .社会的经济制度B .科学技术C .社会生产关系D .建立在一定社会经济基础之上的意识形态及相应的制度和设施8 .社会形态是( )A .生产力和生产关系的统一B .同生产力发展一定阶段相适应的经济基础和上层建筑的统一体C .社会存在和社会意识的统一D .物质世界和精神世界的统一9 .人类社会发展的一般规律是( )A .生产方式内部的矛盾规律B .生产力和生产关系、经济基础和上层建筑之间的矛盾运动规律C .社会存在和社会意识的矛盾规律D .物质生产和精神生产的矛盾规律10 .阶级斗争对阶级社会发展的推动作用突出表现在( )A .生产力的发展B .生产关系的变革C .社会形态的更替D .科技的进步11 .社会革命根源于( )A .人口太多B .少数英雄人物组织暴动C .先进思想和革命理论的传播D .社会基本矛盾的尖锐化12 .社会主义改革的根本目的在于( )A .改变社会主义制度B .完善社会主义制度C .解放和发展生产力D .实现社会公平13 . “蒸汽、电力和自动纺织机甚至是比巴尔贝斯、拉斯拜尔和布朗基诸位公民更危险万分的革命家。
3. 第三章课后习题及答案
第三章1. (Q1) Suppose the network layer provides the following service. The network layer in the source host accepts a segment of maximum size 1,200 bytes and a destination host address from the transport layer. The network layer then guarantees to deliver the segment to the transport layer at the destination host. Suppose many network application processes can be running at the destination host.a. Design the simplest possible transport-layer protocol that will get application data to thedesired process at the destination host. Assume the operating system in the destination host has assigned a 4-byte port number to each running application process.b. Modify this protocol so that it provides a “return address” to the destination process.c. In your protocols, does the transport layer “have to do anything” in the core of the computernetwork.Answer:a. Call this protocol Simple Transport Protocol (STP). At the sender side, STP accepts from thesending process a chunk of data not exceeding 1196 bytes, a destination host address, and a destination port number. STP adds a four-byte header to each chunk and puts the port number of the destination process in this header. STP then gives the destination host address and the resulting segment to the network layer. The network layer delivers the segment to STP at the destination host. STP then examines the port number in the segment, extracts the data from the segment, and passes the data to the process identified by the port number.b. The segment now has two header fields: a source port field and destination port field. At thesender side, STP accepts a chunk of data not exceeding 1192 bytes, a destination host address,a source port number, and a destination port number. STP creates a segment which contains theapplication data, source port number, and destination port number. It then gives the segment and the destination host address to the network layer. After receiving the segment, STP at the receiving host gives the application process the application data and the source port number.c. No, the transport layer does not have to do anything in the core; the transport layer “lives” inthe end systems.2. (Q2) Consider a planet where everyone belongs to a family of six, every family lives in its own house, each house has a unique address, and each person in a given house has a unique name. Suppose this planet has a mail service that delivers letters form source house to destination house. The mail service requires that (i) the letter be in an envelope and that (ii) the address of the destination house (and nothing more ) be clearly written on the envelope. Suppose each family has a delegate family member who collects and distributes letters for the other family members. The letters do not necessarily provide any indication of the recipients of the letters.a. Using the solution to Problem Q1 above as inspiration, describe a protocol that thedelegates can use to deliver letters from a sending family member to a receiving family member.b. In your protocol, does the mail service ever have to open the envelope and examine theletter in order to provide its service.Answer:a.For sending a letter, the family member is required to give the delegate the letter itself, theaddress of the destination house, and the name of the recipient. The delegate clearly writes the recipient’s name on the top of the letter. The delegate then puts the letter in an e nvelope and writes the address of the destination house on the envelope. The delegate then gives the letter to the planet’s mail service. At the receiving side, the delegate receives the letter from the mail service, takes the letter out of the envelope, and takes note of the recipient name written at the top of the letter. The delegate than gives the letter to the family member with this name.b.No, the mail service does not have to open the envelope; it only examines the address on theenvelope.3. (Q3) Describe why an application developer might choose to run an application over UDP rather than TCP.Answer:An application developer may not want its application to use TCP’s congestion control, which can throttle the application’s sending rate at times of congestion. Often, designers of IP telephony and IP videoconference applications choose to run their applications over UDP because they want to avoid TCP’s congestion control. Also, some applications do not need the reliable data transfer provided by TCP.4. (P1) Suppose Client A initiates a Telnet session with Server S. At about the same time, Client B also initiates a Telnet session with Server S. Provide possible source and destination port numbers fora. The segment sent from A to B.b. The segment sent from B to S.c. The segment sent from S to A.d. The segment sent from S to B.e. If A and B are different hosts, is it possible that the source port number in the segment fromA to S is the same as that fromB to S?f. How about if they are the same host?Yes.f No.5. (P2) Consider Figure 3.5 What are the source and destination port values in the segmentsflowing form the server back to the clients’ processes? What are the IP addresses in the network-layer datagrams carrying the transport-layer segments?Answer:Suppose the IP addresses of the hosts A, B, and C are a, b, c, respectively. (Note that a,b,c aredistinct.)To host A: Source port =80, source IP address = b, dest port = 26145, dest IP address = a To host C, left process: Source port =80, source IP address = b, dest port = 7532, dest IP address = cTo host C, right process: Source port =80, source IP address = b, dest port = 26145, dest IP address = c6. (P3) UDP and TCP use 1s complement for their checksums. Suppose you have the followingthree 8-bit bytes: 01101010, 01001111, 01110011. What is the 1s complement of the sum of these 8-bit bytes? (Note that although UDP and TCP use 16-bit words in computing the checksum, for this problem you are being asked to consider 8-bit sums.) Show all work. Why is it that UDP takes the 1s complement of the sum; that is , why not just sue the sum? With the 1s complement scheme, how does the receiver detect errors? Is it possible that a 1-bit error will go undetected? How about a 2-bit error?Answer:One's complement = 1 1 1 0 1 1 1 0.To detect errors, the receiver adds the four words (the three original words and the checksum). If the sum contains a zero, the receiver knows there has been an error. All one-bit errors will be detected, but two-bit errors can be undetected (e.g., if the last digit of the first word is converted to a 0 and the last digit of the second word is converted to a 1).7. (P4) Suppose that the UDP receiver computes the Internet checksum for the received UDPsegment and finds that it matches the value carried in the checksum field. Can the receiver be absolutely certain that no bit errors have occurred? Explain.Answer:No, the receiver cannot be absolutely certain that no bit errors have occurred. This is because of the manner in which the checksum for the packet is calculated. If the corresponding bits (that would be added together) of two 16-bit words in the packet were 0 and 1 then even if these get flipped to 1 and 0 respectively, the sum still remains the same. Hence, the 1s complement the receiver calculates will also be the same. This means the checksum will verify even if there was transmission error.8. (P5) a. Suppose you have the following 2 bytes: 01001010 and 01111001. What is the 1scomplement of sum of these 2 bytes?b. Suppose you have the following 2 bytes: 11110101 and 01101110. What is the 1s complement of sum of these 2 bytes?c. For the bytes in part (a), give an example where one bit is flipped in each of the 2 bytesand yet the 1s complement doesn’t change.0 1 0 1 0 1 0 1 + 0 1 1 1 0 0 0 0 1 1 0 0 0 1 0 1 1 1 0 0 0 1 0 1 + 0 1 0 0 1 1 0 0 0 0 0 1 0 0 0 1Answer:a. Adding the two bytes gives 10011101. Taking the one’s complement gives 01100010b. Adding the two bytes gives 00011110; the one’s complement gives 11100001.c. first byte = 00110101 ; second byte = 01101000.9. (P6) Consider our motivation for correcting protocol rdt2.1. Show that the receiver, shown inthe figure on the following page, when operating with the sender show in Figure 3.11, can lead the sender and receiver to enter into a deadlock state, where each is waiting for an event that will never occur.Answer:Suppose the sender is in state “Wait for call 1 from above” and the receiver (the receiver shown in the homework problem) is in state “Wait for 1 from below.” The sender sends a packet with sequence number 1, and transitions to “Wait for ACK or NAK 1,” waiting for an ACK or NAK. Suppose now the receiver receives the packet with sequence number 1 correctly, sends an ACK, and transitions to state “Wait for 0 from below,” waiting for a data packet with sequence number 0. However, the ACK is corrupted. When the rdt2.1 sender gets the corrupted ACK, it resends the packet with sequence number 1. However, the receiver is waiting for a packet with sequence number 0 and (as shown in the home work problem) always sends a NAK when it doesn't get a packet with sequence number 0. Hence the sender will always be sending a packet with sequence number 1, and the receiver will always be NAKing that packet. Neither will progress forward from that state.10. (P7) Draw the FSM for the receiver side of protocol rdt3.0Answer:The sender side of protocol rdt3.0 differs from the sender side of protocol 2.2 in that timeouts have been added. We have seen that the introduction of timeouts adds the possibility of duplicate packets into the sender-to-receiver data stream. However, the receiver in protocol rdt.2.2 can already handle duplicate packets. (Receiver-side duplicates in rdt 2.2 would arise if the receiver sent an ACK that was lost, and the sender then retransmitted the old data). Hence the receiver in protocol rdt2.2 will also work as the receiver in protocol rdt 3.0.11. (P8) In protocol rdt3.0, the ACK packets flowing from the receiver to the sender do not havesequence numbers (although they do have an ACK field that contains the sequence number of the packet they are acknowledging). Why is it that our ACK packets do not require sequence numbers?Answer:To best Answer this question, consider why we needed sequence numbers in the first place. We saw that the sender needs sequence numbers so that the receiver can tell if a data packet is a duplicate of an already received data packet. In the case of ACKs, the sender does not need this info (i.e., a sequence number on an ACK) to tell detect a duplicate ACK. A duplicate ACK is obvious to the rdt3.0 receiver, since when it has received the original ACK it transitioned to the next state. The duplicate ACK is not the ACK that the sender needs and hence is ignored by the rdt3.0 sender.12. (P9) Give a trace of the operation of protocol rdt3.0 when data packets and acknowledgmentpackets are garbled. Your trace should be similar to that used in Figure 3.16Answer:Suppose the protocol has been in operation for some time. The sender is in state “Wait for call fro m above” (top left hand corner) and the receiver is in state “Wait for 0 from below”. The scenarios for corrupted data and corrupted ACK are shown in Figure 1.13. (P10) Consider a channel that can lose packets but has a maximum delay that is known.Modify protocol rdt2.1 to include sender timeout and retransmit. Informally argue whyyour protocol can communicate correctly over this channel.Answer:Here, we add a timer, whose value is greater than the known round-trip propagation delay. We add a timeout event to the “Wait for ACK or NAK0” and “Wait for ACK or NAK1” states. If the timeout event occurs, the most recently transmitted packet is retransmitted. Let us see why this protocol will still work with the rdt2.1 receiver.• Suppose the timeout is caused by a lost data packet, i.e., a packet on the senderto- receiver channel. In this case, the receiver never received the previous transmission and, from the receiver's viewpoint, if the timeout retransmission is received, it look exactly the same as if the original transmission is being received.• Suppose now that an ACK is lost. The receiver will eventually retransmit the packet on atimeout. But a retransmission is exactly the same action that is take if an ACK is garbled. Thus the sender's reaction is the same with a loss, as with a garbled ACK. The rdt 2.1 receiver can already handle the case of a garbled ACK.14. (P11) Consider the rdt3.0 protocol. Draw a diagram showing that if the network connectionbetween the sender and receiver can reorder messages (that is, that two messagespropagating in the medium between the sender and receiver can be reordered), thenthe alternating-bit protocol will not work correctly (make sure you clearly identify thesense in which it will not work correctly). Your diagram should have the sender on theleft and the receiver on the right, with the time axis running down the page, showingdata (D) and acknowledgement (A) message exchange. Make sure you indicate thesequence number associated with any data or acknowledgement segment.Answer:15. (P12) The sender side of rdt3.0 simply ignores (that is, takes no action on) all received packetsthat are either in error or have the wrong value in the ack-num field of anacknowledgement packet. Suppose that in such circumstances, rdt3.0 were simply toretransmit the current data packet . Would the protocol still work? (hint: Consider whatwould happen if there were only bit errors; there are no packet losses but prematuretimeout can occur. Consider how many times the nth packet is sent, in the limit as napproaches infinity.)Answer:The protocol would still work, since a retransmission would be what would happen if the packet received with errors has actually been lost (and from the receiver standpoint, it never knows which of these events, if either, will occur). To get at the more subtle issue behind this question, one has to allow for premature timeouts to occur. In this case, if each extra copy of the packet is ACKed and each received extra ACK causes another extra copy of the current packet to be sent, the number of times packet n is sent will increase without bound as n approaches infinity.16. (P13) Consider a reliable data transfer protocol that uses only negative acknowledgements.Suppose the sender sends data only infrequently. Would a NAK-only protocol bepreferable to a protocol that uses ACKs? Why? Now suppose the sender has a lot ofdata to send and the end to end connection experiences few losses. In this second case ,would a NAK-only protocol be preferable to a protocol that uses ACKs? Why?Answer:In a NAK only protocol, the loss of packet x is only detected by the receiver when packetx+1 is received. That is, the receivers receives x-1 and then x+1, only when x+1 is received does the receiver realize that x was missed. If there is a long delay between the transmission of x and the transmission of x+1, then it will be a long time until x can be recovered, under a NAK only protocol.On the other hand, if data is being sent often, then recovery under a NAK-only scheme could happen quickly. Moreover, if errors are infrequent, then NAKs are only occasionally sent (when needed), and ACK are never sent – a significant reduction in feedback in the NAK-only case over the ACK-only case.17. (P14) Consider the cross-country example shown in Figure 3.17. How big would the windowsize have to be for the channel utilization to be greater than 80 percent?Answer:It takes 8 microseconds (or 0.008 milliseconds) to send a packet. in order for the sender to be busy 90 percent of the time, we must have util = 0.9 = (0.008n) / 30.016 or n approximately 3377 packets.18. (P15) Consider a scenario in which Host A wants to simultaneously send packets to Host Band C. A is connected to B and C via a broadcast channel—a packet sent by A is carriedby the channel to both B and C. Suppose that the broadcast channel connecting A, B,and C can independently lose and corrupt packets (and so, for example, a packet sentfrom A might be correctly received by B, but not by C). Design a stop-and-wait-likeerror-control protocol for reliable transferring packets from A to B and C, such that Awill not get new data from the upper layer until it knows that B and C have correctlyreceived the current packet. Give FSM descriptions of A and C. (Hint: The FSM for Bshould be essentially be same as for C.) Also, give a description of the packet format(s)used.Answer:In our solution, the sender will wait until it receives an ACK for a pair of messages (seqnum and seqnum+1) before moving on to the next pair of messages. Data packets have a data field and carry a two-bit sequence number. That is, the valid sequence numbers are 0, 1, 2, and 3. (Note: you should think about why a 1-bit sequence number space of 0, 1 only would not work in the solution below.) ACK messages carry the sequence number of the data packet they are acknowledging.The FSM for the sender and receiver are shown in Figure 2. Note that the sender state records whether (i) no ACKs have been received for the current pair, (ii) an ACK for seqnum (only) has been received, or an ACK for seqnum+1 (only) has been received. In this figure, we assume that theseqnum is initially 0, and that the sender has sent the first two data messages (to get things going).A timeline trace for the sender and receiver recovering from a lost packet is shown below:Sender Receivermake pair (0,1)send packet 0Packet 0 dropssend packet 1receive packet 1buffer packet 1send ACK 1receive ACK 1(timeout)resend packet 0receive packet 0deliver pair (0,1)send ACK 0receive ACK 019. (P16) Consider a scenario in which Host A and Host B want to send messages to Host C. HostsA and C are connected by a channel that can lose and corrupt (but not reorder)message.Hosts B and C are connected by another channel (independent of the channelconnecting A and C) with the same properties. The transport layer at Host C shouldalternate in delivering messages from A and B to the layer above (that is, it should firstdeliver the data from a packet from A, then the data from a packet from B, and so on).Design a stop-and-wait-like error-control protocol for reliable transferring packets fromA toB and C, with alternating delivery atC as described above. Give FSM descriptionsof A and C. (Hint: The FSM for B should be essentially be same as for A.) Also, give adescription of the packet format(s) used.Answer:This problem is a variation on the simple stop and wait protocol (rdt3.0). Because the channel may lose messages and because the sender may resend a message that one of the receivers has already received (either because of a premature timeout or because the other receiver has yet to receive the data correctly), sequence numbers are needed. As in rdt3.0, a 0-bit sequence number will suffice here.The sender and receiver FSM are shown in Figure 3. In this problem, the sender state indicates whether the sender has received an ACK from B (only), from C (only) or from neither C nor B. The receiver state indicates which sequence number the receiver is waiting for.20. (P17) In the generic SR protocol that we studied in Section 3.4.4, the sender transmits amessage as soon as it is available (if it is in the window) without waiting for anacknowledgment. Suppose now that we want an SR protocol that sends messages twoat a time. That is , the sender will send a pair of messages and will send the next pairof messages only when it knows that both messages in the first pair have been receivercorrectly.Suppose that the channel may lose messages but will not corrupt or reorder messages.Design an error-control protocol for the unidirectional reliable transfer of messages.Give an FSM description of the sender and receiver. Describe the format of the packetssent between sender and receiver, and vice versa. If you use any procedure calls otherthan those in Section 3.4(for example, udt_send(), start_timer(), rdt_rcv(), and soon) ,clearly state their actions. Give an example (a timeline trace of sender and receiver)showing how your protocol recovers from a lost packet.Answer:21. (P18) Consider the GBN protocol with a sender window size of 3 and a sequence numberrange of 1024. Suppose that at time t, the next in-order packet that the receiver isexpecting has a sequence number of k. Assume that the medium does not reordermessages. Answer the following questions:a. What are the possible sets of sequence number inside the sender’s window at timet? Justify your Answer.b .What are all possible values of the ACK field in all possible messages currentlypropagating back to the sender at time t? Justify your Answer.Answer:a.Here we have a window size of N=3. Suppose the receiver has received packet k-1, and hasACKed that and all other preceeding packets. If all of these ACK's have been received by sender, then sender's window is [k, k+N-1]. Suppose next that none of the ACKs have been received at the sender. In this second case, the sender's window contains k-1 and the N packets up to and including k-1. The sender's window is thus [k- N,k-1]. By these arguments, the senders window is of size 3 and begins somewhere in the range [k-N,k].b.If the receiver is waiting for packet k, then it has received (and ACKed) packet k-1 and the N-1packets before that. If none of those N ACKs have been yet received by the sender, then ACKmessages with values of [k-N,k-1] may still be propagating back. Because the sender has sent packets [k-N, k-1], it must be the case that the sender has already received an ACK for k-N-1.Once the receiver has sent an ACK for k-N-1 it will never send an ACK that is less that k-N-1.Thus the range of in-flight ACK values can range from k-N-1 to k-1.22. (P19) Answer true or false to the following questions and briefly justify your Answer.a. With the SR protocol, it is possible for the sender to receive an ACK for a packet thatfalls outside of its current window.b. With CBN, it is possible for the sender to receiver an ACK for a packet that fallsoutside of its current window.c. The alternating-bit protocol is the same as the SR protocol with a sender and receiverwindow size of 1.d. The alternating-bit protocol is the same as the GBN protocol with a sender andreceiver window size of 1.Answer:a.True. Suppose the sender has a window size of 3 and sends packets 1, 2, 3 at t0 . At t1 (t1 > t0)the receiver ACKS 1, 2, 3. At t2 (t2 > t1) the sender times out and resends 1, 2, 3. At t3 the receiver receives the duplicates and re-acknowledges 1, 2, 3. At t4 the sender receives the ACKs that the receiver sent at t1 and advances its window to 4, 5, 6. At t5 the sender receives the ACKs 1, 2, 3 the receiver sent at t2 . These ACKs are outside its window.b.True. By essentially the same scenario as in (a).c.True.d.True. Note that with a window size of 1, SR, GBN, and the alternating bit protocol arefunctionally equivalent. The window size of 1 precludes the possibility of out-of-order packets (within the window). A cumulative ACK is just an ordinary ACK in this situation, since it can only refer to the single packet within the window.23. (Q4) Why is it that voice and video traffic is often sent over TCP rather than UDP in today’sInternet. (Hint: The Answer we are looking for has nothing to do with TCP’s congestion-control mechanism. )Answer:Since most firewalls are configured to block UDP traffic, using TCP for video and voice traffic lets the traffic though the firewalls24. (Q5) Is it possible for an application to enjoy reliable data transfer even when the applicationruns over UDP? If so, how?Answer:Yes. The application developer can put reliable data transfer into the application layer protocol. This would require a significant amount of work and debugging, however.25. (Q6) Consider a TCP connection between Host A and Host B. Suppose that the TCP segmentstraveling form Host A to Host B have source port number x and destination portnumber y. What are the source and destination port number for the segments travelingform Host B to Host A?Answer:Source port number y and destination port number x.26. (P20) Suppose we have two network entities, A and B. B has a supply of data messages thatwill be sent to A according to the following conventions. When A gets a request fromthe layer above to get the next data (D) message from B, A must send a request (R)message to B on the A-to-B channel. Only when B receives an R message can it send adata (D) message back to A on the B-to-A channel. A should deliver exactly one copy ofeach D message to the layer above. R message can be lost (but not corrupted) in the A-to-B channel; D messages, once sent, are always delivered correctly. The delay alongboth channels is unknown and variable.Design(give an FSM description of) a protocol that incorporates the appropriatemechanisms to compensate for the loss-prone A-to-B channel and implementsmessage passing to the layer above at entity A, as discussed above. Use only thosemechanisms that are absolutely necessary.Answer:Because the A-to-B channel can lose request messages, A will need to timeout and retransmit its request messages (to be able to recover from loss). Because the channel delays are variable and unknown, it is possible that A will send duplicate requests (i.e., resend a request message that has already been received by B). To be able to detect duplicate request messages, the protocol will use sequence numbers. A 1-bit sequence number will suffice for a stop-and-wait type of request/response protocol.A (the requestor) has 4 states:• “Wait for Request 0 from above.” Here the requestor is waiting for a call from above to request a unit of data. When it receives a request from above, it sends a request message, R0, to B, starts a timer and make s a transition to the “Wait for D0” state. When in the “Wait for Request 0 from above” state, A ign ores anything it receives from B.• “Wait for D0”. Here the requestor is waiting for a D0 data message from B. A timer is always running in this state. If the timer expires, A sends another R0 message, restarts the timer and remains in this state. If a D0 message is received from B, A stops the time and transits to the “Wait for Request 1 from above” state. If A receives a D1 data message while in this state, it is ignored.• “Wait for Request 1 from above.” Here the requestor is again waiting for a call from above to request a unit of data. When it receives a request from above, it sends a request message, R1, to B, starts a timer and makes a transition to the “Wait for D1” state. When in the “Wait for Request 1 from above” state, A ignores anything it receives from B.• “Wait for D1”. Here the requestor is waiting for a D1 data message from B. A timer is always running in this state. If the timer expires, A sends another R1 message, restarts the timer and remains in this state. If a D1 message is received from B, A stops the timer and transits to the “Wait for Request 0 from above” state. If A receives a D0 data message while in this state, it is ignored.The data supplier (B) has only two states:。
第3章 本量利练习题(答案版)
第3章本量利分析一、单项选择题:1、生产单一品种产品企业,保本销售额=( B )A. 保本销售量×单位利润B. 固定成本总额÷贡献边际率C. 固定成本总额÷(单价一单位变动成本)D. 固定成本总额÷综合贡献边际率E. 固定成本总额÷贡献边际2、生产多品种产品企业测算综合保本销售额=固定成本总额÷( D )A.单位贡献边际B.贡献边际率C.单价一单位变动成本D.加权平均贡献毛益率3、某企业只生产一种产品,单价6元,单位变动生产成本4元,单位销售和管理变动成本0.5元,销量为500件,则其产品贡献边际为( B )元A.650B.750C.850D.9504、下属因素中导致保本销售量下降的是( D )A.销售量上升B.产品单价下降C.固定成本上升D.产品单位变动成本下降5、在变动成本法下,其利润表所提供的中间指标是( A )A.贡献边际B.营业利润C.营业毛利D.期间成本6、在下列指标中,可据以判断企业经营安全程度的指标是( C )A.保本量B.贡献边际C.保本作业率D.保本额7、保本作业率与安全边际率之间的关系是( D )A.两者相等B.前者一般大于后者C.后者一般大于前者D.两者之和等于18、销售量不变,保本点越高,则能实现的利润( A )A.越小B.不变C.越大D.不一定9、销售量不变,单价单独变动时,会使安全边际( C )A.不变B.不一定变动C.同方向变动D.反方向变动10、下列因素单独变动时,不对实现目标利润的销售量产生影响的是( D )A.单价B.目标利润C.成本水平D.销售量二、多项选择题:1、安全边际率=( AC )A.安全边际量÷实际销售量B.保本销售量÷实际销售量C.安全边际额÷实际销售额D.保本销售额÷实际销售额E.安全边际量÷安全边际额2、从传统式保本图得知( CE )A.保本点右边,成本大于收入,是亏损区B.销售量一定的情况下,保本点越高,盈利区越大C.实际销售量超过保本点销售量部分即是安全边际D.在其他因素不变的情况,保本点越低,盈利面积越小E.安全边际越大,盈利面积越大3、贡献边际率的计算公式可表示为(ABDE )A.1-变动成本率B.贡献边际/销售收入C.固定成本/保本销售量D.固定成本/保本销售额E.单位贡献边际/单价4、在盈亏临界图中,盈亏临界点的位置取决于( ABD )等因素。
第三章习题解答及参考答案
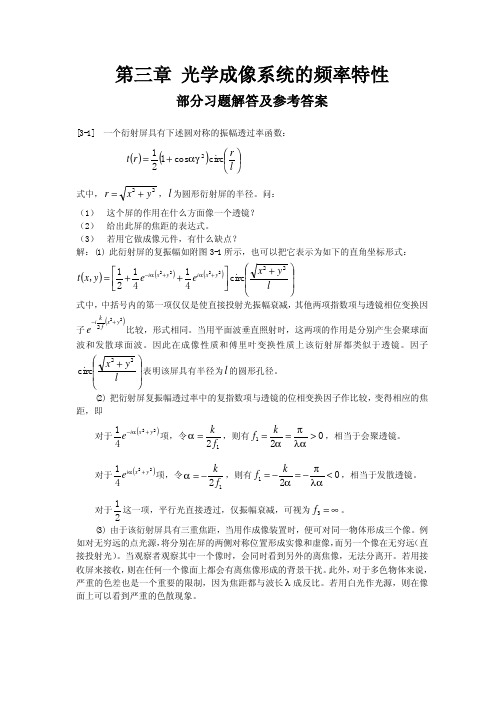
(
)
①
2 式中 m 为整数。令 u = αr ,显然上式是 u 的周期函数,周期为 2π ,故可展开成傅里 ∞ 1 1 + sgn (cos u ) = ∑ Cn e inu 2 2 n = −∞
叶级数:
其中,
Cn =
1 2π
∫
π 2
−π 2
e −inu du =
sin (nπ 2) nπ
②
遂有:
∞ 1 1 sin (nπ 2 ) inαr 2 e + sgn cos αr 2 = ∑ 2 2 nπ n= −∞
②
σ ( f x ,0 ) 2λd i =1− f x = 1− f x f0 σ0 l
l l ≤ λd i f x ≤ (见附图3 - 4(b)) 4 2
2 1 l l σ ( f x ,0 ) = (l − λd i f x ) l − = − λd i l f x 2 2 2
λd ;两个一级分量与中央亮斑 L
附图 3-2
习题[3-2]图示
附图 3-3
归一化强度分布
[3-3]
将面积为 10 mm × 10 mm 的透射物体置于一傅里叶变换透镜的前焦面上作频谱分析。
用波长 λ = 0.5 µ m 的单色平面波垂直照明,要求在频谱面上测得的强度在频率 140 线/mm 以下能准确代表物体的功率谱。并要求频率为 140 线/mm 与 20 线/mm 在频谱面上的间隔为 30mm,问该透镜的焦距和口径各为多少? 解:取面积为10mm ×10mm 的透射物体的对角线方向为 x 轴。因要求在 140 线/mm 以下的 空间频率成分不受到有限孔径的渐晕效应的影响,故透镜的口径 D 应满足条件:
第3章 数组(习题答案及解析)

习题3 参考答案一、选择题3.1 C 分析:本题考查程序和数组的基本概念。
3.2 A 分析:字符串比较大小是以第1个不相同字符的大小为标准的,跟长度没有关系,B选项不正确;字符串比较大小除了使用库函数strcn3()以外,就只能靠自己写代码来实现了,而不能通过关系运算符来比较大小。
因为字符串在表达式中相当于const char*,即常字符指针,代表的是字符串的首地址,关系运算符会将两个字符串的首地址值比较大小,这是毫无意义的。
C选项不正确。
C语言中只有字符串常量而没有字符串变量,D选项描述不正确;空串的长度为0,而以空格打头的字符串的长度至少为1,因此A选项是正确。
3.3 A 分析:如果第一维的长度没有指定,则定义的同时需要完成初始化,否则不知道分配多大的内存空间给它,所以选项B、C错误;二维数组a[2][3]中只有两个元素,都是一维数组,一维下标最大只能是a[1],所以选项D错误;若完成初始化的二维数组,第一维的长度没有指定,则第一维的大小按如下规则确定:若初值个数能被第二维大小整除,所得的商就是第一维的大小,若不能整除,则所得的商加1作为第一维的大小,所以选项A相当于:double a[1][3] = {6};其中a[0][0]=6,其他元素赋值0,选项A正确,答案为A。
3.4 D 分析:本题考察的知识点是:字符串常量。
在C语言中,字符串常量是以双引号括起来的字符序列。
因此B选项和C选项不正确。
字符序列中可包含一些转义字符,转义字符都是以"\"开头的。
A选项中包含了三个"\",前两个(\\)代表了一个"\"字符,后面一个和"""一起(\")被看作一个""",所以该字符串缺少一个结束的""",因此不正确。
D选项的两个"""之间没有任何字符,代表的是一个空串,是合法的字符串常量,因此D选项正确。
3第三章 弹性理论(习题及答案)

第三章弹性理论思考与练习一、选择题1.计算需求弹性的弹性系数的一般公式是( )。
A.需求量与价格之比B.需求量变动的百分比除以价格变动的百分比C.需求量变动的绝对值除以价格变动的绝对值D.价格变动的百分比除以需求量变动的百分比2.某种商品的价格变动10%,需求量变动20%。
则它的弹性系数为( )。
A.10%B.30%C.1/2D.23.如果一种商品的需求的价格弹性为2,价格由1元上升到1.02元会导致需求量( )。
A.增加4%B.增加2%C.减少4%D.减少2%4.如果一种商品的需求的价格弹性为0.5,价格由l元上升到1.04元会导致需求量( )。
A.增加4%B.增加2%C.减少4%D.减少2%5.如果需求的价格弹性为1/3,价格上升30%时,需求量将( )。
A.增加10%B.减少10%C.增加90%D.减少90%6.如果一种商品的价格上升时,需求量完全没有下降,那么该商品的需求( )。
A.完全有弹性B.完全无弹性C.富有弹性D.缺乏弹性7.如果一种商品的价格变动5%,需求量因此变动5%.那么该商品的需求( )。
A.富有弹性B.缺乏弹性C.无弹性D.单位弹性8.如果( ),我们就说一种商品的需求缺乏弹性。
A.需求量变化百分比大于价格变化百分比B.需求量变化百分比小于价格变化百分比C.需求变化大于价格变化D.价格变化大于需求变化9.如果一种商品的需求缺乏弹性,其弹性系数( )。
A.大于1B.大于0小于1C.等于1D.为010.如果一种商品的需求缺乏弹性,商品价格上升5%将使( )。
A.需求量的增加超过5%B.需求量的增加小于5%C.需求量的减少超过5%D.需求量的减少小于5%参考答案1.B;2.D;3.C;4.D;5.B;6.B;7.D;8.B;9.B;10.D二、判断题1.同一条线性需求曲线上不同点的弹性系数是不同的。
( )2.需求的价格弹性为零意味着需求曲线是一条水平线。
( )3.当某种产品的价格上升8%,而需求量减少7%时。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
是多大?⑵ XL为何值时,开关S闭合前的电流最大,是多少? 3.4.3 有一R、L、C 串联电路, R =100Ω、L = 200mH、 C = 20μF。⑴把它接在工频220V 交流电路中时,求其电流、有功 功率、无功功率、视在功率及功率因数,画出相量图,其为感性 负载还是容性负载?⑵把它接在U = 220V, f = 500Hz交流电路中 时,求其电流、有功功率、无功功率、视在功率及功率因数,画 出相量图,其为感性负载还是容性负载?
图3.12.3 习题3.4.2
图3.12.4 习题3.4.5
3.4.4 有一既含电阻又含有电容的负载, 其中R =100Ω, C = 31.85μF。由工频交流电供电,其电流为I = 2A。两根导线的 总电阻、总电感分别为Rl=1 Ω、L l= 6.37mH 。⑴试求输电线路 上的电压降、负载的端电压及电源的电压,并画出相量图;⑵求 电源的有功功率、无功功率、视在功率及功率因数。 3.4.5 如图3.12.4 所示,U = 220V, f = 50Hz ,R =100Ω, XL =100Ω。⑴求开关闭合前,电路中的总电流、有功功率、无功 功率、视在功率及功率因数;⑵若 XC = 300Ω,求开关闭合后, 电路中的总电流、有功功率、无功功率、视在功率及功率因数; ⑶比较并联电容器后,总电流,有功功率、无功功率、视在功率 及功率因数的变化。 3.4.6 如图3.12.5 所示 Z1 2、Z2 j10、Z3 (40 j30)、
I1 530 A 。试计算 I 2 、 I3、 U。
3.4.7 如图3.12.6 所示,U = 220V, R =XC ,总电压 U 与总 电流 I 相位相同,求 U L、 UC。
图3.12.5 习题3.4.6
图3.12.6 习题3.4.7
3.5.1 有两台单相交流电动机,并联在工频220V 的交流电 路中。已知 P1N=1kW , cosφ1= 0.8, P2N = 2kW, cosφ2 = 0.6。 ⑴求电路的总电流、总有功功率、总无功功率、总视在功率。 ⑵若将电路功率因数提高到cosφ3 = 0.9,需并联多大的电容器? 3.5.2 如图3.12.7 所示的荧光灯电路,U = 220V , f = 50Hz , 灯管两端的电压为U L =100V ,电路中的电流为I = 0.4A,镇流 器的功率 Pl =7W 。求⑴灯管与镇流器的电阻 RL 、Rl和电感L; ⑵灯管的有功功率 PL 、电路的总有功功率P 及功率因数;⑶若 是电路的功率因数提高到 cosφ1 = 0.95,需并联上多大的电容器? 电路中的总电流降到多少安?
习题
45 3.1.1 已知交流电流的频率为 f 50Hz ,初相位 有效值 I 10 A 。⑴写出其瞬时值表达式;⑵画出其三角函数 曲线。
3.1.2 电压表达式 u 220 2 sin(314t 60 ) ,⑴计算其最大 值Um 、有效值U; ⑵计算其周期T、频率f、角频率ω; ⑶计算
3.5.3 在U = 220V, f = 50Hz 的电源上,接有一感性负载额 定功率及功率因数分别等于PN = 30kW,cosφ= 0.4。⑴求负载的 电流、无功功率、视在功率及功率因数;⑵若使电路中的总电 流降至200A ,应并联上多大的电容器?此时电路中的功载的UN =110V, P N = 264W, cosφN = 0.6,把它接在工频220V的交流电路中时,开关打到a、b、c点, 分别串联多大的L、C、R ,才能使负载工作在额定状态?
图3.12.1 习题3.3.1
图3.12.2 习题3.4.1
3.4.1 在3.12.2中,已知 R=XL=XC=50Ω,负载电阻RL=50Ω, 试分别计算电源电压分别为工频、直流220V 两种情况下,各支路 的电流及各支路上RL上的有功功率。
3.4.2 在图3.12.3中,已知 U 220V、R 300、X L 400
3.2.1 用复数法求电流 i1 10 2 sin t, i2 10 2 sin(t 120 ) i3 10 2 sin(t 240 ) 的和,并画出它们的相量图。
3.2.2 用复数法求电压 u1 220 2 sin t,u2 220 2 sin(t 120 ) 的差,并画出它们的相量图。 3.3.1 在图3.12.1中,电阻 R=100Ω,电感L=318.5mH,电容 C=31.8uF,接于220V的交流电路中。计算当频率分别为50Hz、 500Hz 两种情况下,开关S合向abc时,各支路的电流。
图3.12.7 习题3.5.2
图3.12.8 习题3.5.4
3.5.5 一单相感性负载,主要技术参数 UN = 220V PN= 2kW , cosφN = 0.5,⑴若在其两端并联上一个C =100μF电容器,电路的 功率因数是多少?⑵如果想使电路中的电流降到最小,此时电路 中的电流为多大? 3.5.6 如图3.12.9 所示, Z1 为一感性负载,把它接在工频 220V 的交流电路中时, P1 = 800W, cosφ1 = 0.6 。开关闭合后, 电路中的有功功率增加了75W ,无功功率减少了300var。试求 电路中的总电流I 及 Z2 , Z2 是感性负载还是容性负载?
初相位ψ,并画出其三角函数曲线。
3.1.3 电流 i1 20 2 sin(314t 60 ) ,i2 5 2 sin(314t 30 ) ⑴画出它们的三角函数曲线,在曲线上标出它们的相位差;⑵指 出它们的超前滞后的关系;⑶写出它们的相量表达式,并求它们 的和 i i1 i2
图3.12.9 习题3.5.6
U 2200 V、C 100uF、R 50、 3.6.1 如图3.12.10 所示, L 60mH 求⑴工频下的电流 I (2)频率为何值时,电流最小, 等于多少?
