Resolution and Binary Decision Diagrams Cannot Simulate Each Other Polynomially
运筹学英汉词汇ABC
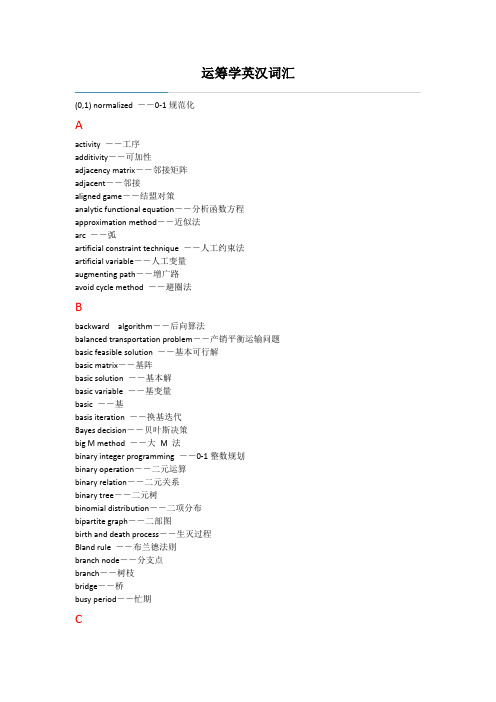
运筹学英汉词汇(0,1) normalized ――0-1规范化Aactivity ――工序additivity――可加性adjacency matrix――邻接矩阵adjacent――邻接aligned game――结盟对策analytic functional equation――分析函数方程approximation method――近似法arc ――弧artificial constraint technique ――人工约束法artificial variable――人工变量augmenting path――增广路avoid cycle method ――避圈法Bbackward algorithm――后向算法balanced transportation problem――产销平衡运输问题basic feasible solution ――基本可行解basic matrix――基阵basic solution ――基本解basic variable ――基变量basic ――基basis iteration ――换基迭代Bayes decision――贝叶斯决策big M method ――大M 法binary integer programming ――0-1整数规划binary operation――二元运算binary relation――二元关系binary tree――二元树binomial distribution――二项分布bipartite graph――二部图birth and death process――生灭过程Bland rule ――布兰德法则branch node――分支点branch――树枝bridge――桥busy period――忙期Ccapacity of system――系统容量capacity――容量Cartesian product――笛卡儿积chain――链characteristic function――特征函数chord――弦circuit――回路coalition structure――联盟结构coalition――联盟combination me――组合法complement of a graph――补图complement of a set――补集complementary of characteristic function――特征函数的互补性complementary slackness condition ――互补松弛条件complementary slackness property――互补松弛性complete bipartite graph――完全二部图complete graph――完全图completely undeterministic decision――完全不确定型决策complexity――计算复杂性congruence method――同余法connected component――连通分支connected graph――连通图connected graph――连通图constraint condition――约束条件constraint function ――约束函数constraint matrix――约束矩阵constraint method――约束法constraint ――约束continuous game――连续对策convex combination――凸组合convex polyhedron ――凸多面体convex set――凸集core――核心corner-point ――顶点(角点)cost coefficient――费用系数cost function――费用函数cost――费用criterion ; test number――检验数critical activity ――关键工序critical path method ――关键路径法(CMP )critical path scheduling ――关键路径cross job ――交叉作业curse of dimensionality――维数灾customer resource――顾客源customer――顾客cut magnitude ――截量cut set ――截集cut vertex――割点cutting plane method ――割平面法cycle ――回路cycling ――循环Ddecision fork――决策结点decision maker决――策者decision process of unfixed step number――不定期决策过程decision process――决策过程decision space――决策空间decision variable――决策变量decision决--策decomposition algorithm――分解算法degenerate basic feasible solution ――退化基本可行解degree――度demand――需求deterministic inventory model――确定贮存模型deterministic type decision――确定型决策diagram method ――图解法dictionary ordered method ――字典序法differential game――微分对策digraph――有向图directed graph――有向图directed tree――有向树disconnected graph――非连通图distance――距离domain――定义域dominate――优超domination of strategies――策略的优超关系domination――优超关系dominion――优超域dual graph――对偶图Dual problem――对偶问题dual simplex algorithm ――对偶单纯形算法dual simplex method――对偶单纯形法dummy activity――虚工序dynamic game――动态对策dynamic programming――动态规划Eearliest finish time――最早可能完工时间earliest start time――最早可能开工时间economic ordering quantity formula――经济定购批量公式edge ――边effective set――有效集efficient solution――有效解efficient variable――有效变量elementary circuit――初级回路elementary path――初级通路elementary ――初等的element――元素empty set――空集entering basic variable ――进基变量equally liability method――等可能性方法equilibrium point――平衡点equipment replacement problem――设备更新问题equipment replacing problem――设备更新问题equivalence relation――等价关系equivalence――等价Erlang distribution――爱尔朗分布Euler circuit――欧拉回路Euler formula――欧拉公式Euler graph――欧拉图Euler path――欧拉通路event――事项expected value criterion――期望值准则expected value of queue length――平均排队长expected value of sojourn time――平均逗留时间expected value of team length――平均队长expected value of waiting time――平均等待时间exponential distribution――指数分布external stability――外部稳定性Ffeasible basis ――可行基feasible flow――可行流feasible point――可行点feasible region ――可行域feasible set in decision space――决策空间上的可行集feasible solution――可行解final fork――结局结点final solution――最终解finite set――有限集合flow――流following activity ――紧后工序forest――森林forward algorithm――前向算法free variable ――自由变量function iterative method――函数迭代法functional basic equation――基本函数方程function――函数fundamental circuit――基本回路fundamental cut-set――基本割集fundamental system of cut-sets――基本割集系统fundamental system of cut-sets――基本回路系统Ggame phenomenon――对策现象game theory――对策论game――对策generator――生成元geometric distribution――几何分布goal programming――目标规划graph theory――图论graph――图HHamilton circuit――哈密顿回路Hamilton graph――哈密顿图Hamilton path――哈密顿通路Hasse diagram――哈斯图hitchock method ――表上作业法hybrid method――混合法Iideal point――理想点idle period――闲期implicit enumeration method――隐枚举法in equilibrium――平衡incidence matrix――关联矩阵incident――关联indegree――入度indifference curve――无差异曲线indifference surface――无差异曲面induced subgraph――导出子图infinite set――无限集合initial basic feasible solution ――初始基本可行解initial basis ――初始基input process――输入过程Integer programming ――整数规划inventory policy―v存贮策略inventory problem―v货物存储问题inverse order method――逆序解法inverse transition method――逆转换法isolated vertex――孤立点isomorphism――同构Kkernel――核knapsack problem ――背包问题Llabeling method ――标号法latest finish time――最迟必须完工时间leaf――树叶least core――最小核心least element――最小元least spanning tree――最小生成树leaving basic variable ――出基变量lexicographic order――字典序lexicographic rule――字典序lexicographically positive――按字典序正linear multiobjective programming――线性多目标规划Linear Programming Model――线性规划模型Linear Programming――线性规划local noninferior solution――局部非劣解loop method――闭回路loop――圈loop――自环(环)loss system――损失制Mmarginal rate of substitution――边际替代率Marquart decision process――马尔可夫决策过程matching problem――匹配问题matching――匹配mathematical programming――数学规划matrix form ――矩阵形式matrix game――矩阵对策maximum element――最大元maximum flow――最大流maximum matching――最大匹配middle square method――平方取中法minimal regret value method――最小后悔值法minimum-cost flow――最小费用流mixed expansion――混合扩充mixed integer programming ――混合整数规划mixed Integer programming――混合整数规划mixed Integer ――混合整数规划mixed situation――混合局势mixed strategy set――混合策略集mixed strategy――混合策略mixed system――混合制most likely estimate――最可能时间multigraph――多重图multiobjective programming――多目标规划multiobjective simplex algorithm――多目标单纯形算法multiple optimal solutions ――多个最优解multistage decision problem――多阶段决策问题multistep decision process――多阶段决策过程Nn- person cooperative game ――n人合作对策n- person noncooperative game――n人非合作对策n probability distribution of customer arrive――顾客到达的n 概率分布natural state――自然状态nature state probability――自然状态概率negative deviational variables――负偏差变量negative exponential distribution――负指数分布network――网络newsboy problem――报童问题no solutions ――无解node――节点non-aligned game――不结盟对策nonbasic variable ――非基变量nondegenerate basic feasible solution――非退化基本可行解nondominated solution――非优超解noninferior set――非劣集noninferior solution――非劣解nonnegative constrains ――非负约束non-zero-sum game――非零和对策normal distribution――正态分布northwest corner method ――西北角法n-person game――多人对策nucleolus――核仁null graph――零图Oobjective function ――目标函数objective( indicator) function――指标函数one estimate approach――三时估计法operational index――运行指标operation――运算optimal basis ――最优基optimal criterion ――最优准则optimal solution ――最优解optimal strategy――最优策略optimal value function――最优值函数optimistic coefficient method――乐观系数法optimistic estimate――最乐观时间optimistic method――乐观法optimum binary tree――最优二元树optimum service rate――最优服务率optional plan――可供选择的方案order method――顺序解法ordered forest――有序森林ordered tree――有序树outdegree――出度outweigh――胜过Ppacking problem ――装箱问题parallel job――平行作业partition problem――分解问题partition――划分path――路path――通路pay-off function――支付函数payoff matrix――支付矩阵payoff――支付pendant edge――悬挂边pendant vertex――悬挂点pessimistic estimate――最悲观时间pessimistic method――悲观法pivot number ――主元plan branch――方案分支plane graph――平面图plant location problem――工厂选址问题player――局中人Poisson distribution――泊松分布Poisson process――泊松流policy――策略polynomial algorithm――多项式算法positive deviational variables――正偏差变量posterior――后验分析potential method ――位势法preceding activity ――紧前工序prediction posterior analysis――预验分析prefix code――前级码price coefficient vector ――价格系数向量primal problem――原问题principal of duality ――对偶原理principle of optimality――最优性原理prior analysis――先验分析prisoner’s dilemma――囚徒困境probability branch――概率分支production scheduling problem――生产计划program evaluation and review technique――计划评审技术(PERT) proof――证明proper noninferior solution――真非劣解pseudo-random number――伪随机数pure integer programming ――纯整数规划pure strategy――纯策略Qqueue discipline――排队规则queue length――排队长queuing theory――排队论Rrandom number――随机数random strategy――随机策略reachability matrix――可达矩阵reachability――可达性regular graph――正则图regular point――正则点regular solution――正则解regular tree――正则树relation――关系replenish――补充resource vector ――资源向量revised simplex method――修正单纯型法risk type decision――风险型决策rooted tree――根树root――树根Ssaddle point――鞍点saturated arc ――饱和弧scheduling (sequencing) problem――排序问题screening method――舍取法sensitivity analysis ――灵敏度分析server――服务台set of admissible decisions(policies) ――允许决策集合set of admissible states――允许状态集合set theory――集合论set――集合shadow price ――影子价格shortest path problem――最短路线问题shortest path――最短路径simple circuit――简单回路simple graph――简单图simple path――简单通路Simplex method of goal programming――目标规划单纯形法Simplex method ――单纯形法Simplex tableau――单纯形表single slack time ――单时差situation――局势situation――局势slack variable ――松弛变量sojourn time――逗留时间spanning graph――支撑子图spanning tree――支撑树spanning tree――生成树stable set――稳定集stage indicator――阶段指标stage variable――阶段变量stage――阶段standard form――标准型state fork――状态结点state of system――系统状态state transition equation――状态转移方程state transition――状态转移state variable――状态变量state――状态static game――静态对策station equilibrium state――统计平衡状态stationary input――平稳输入steady state――稳态stochastic decision process――随机性决策过程stochastic inventory method――随机贮存模型stochastic simulation――随机模拟strategic equivalence――策略等价strategic variable, decision variable ――决策变量strategy (policy) ――策略strategy set――策略集strong duality property ――强对偶性strong ε-core――强ε-核心strongly connected component――强连通分支strongly connected graph――强连通图structure variable ――结构变量subgraph――子图sub-policy――子策略subset――子集subtree――子树surplus variable ――剩余变量surrogate worth trade-off method――代替价值交换法symmetry property ――对称性system reliability problem――系统可靠性问题Tteam length――队长tear cycle method――破圈法technique coefficient vector ――技术系数矩阵test number of cell ――空格检验数the branch-and-bound technique ――分支定界法the fixed-charge problem ――固定费用问题three estimate approach一―时估计法total slack time――总时差traffic intensity――服务强度transportation problem ――运输问题traveling salesman problem――旅行售货员问题tree――树trivial graph――平凡图two person finite zero-sum game二人有限零和对策two-person game――二人对策two-phase simplex method ――两阶段单纯形法Uunbalanced transportation problem ――产销不平衡运输问题unbounded ――无界undirected graph――无向图uniform distribution――均匀分布unilaterally connected component――单向连通分支unilaterally connected graph――单向连通图union of sets――并集utility function――效用函数Vvertex――顶点voting game――投票对策Wwaiting system――等待制waiting time――等待时间weak duality property ――弱对偶性weak noninferior set――弱非劣集weak noninferior solution――弱非劣解weakly connected component――弱连通分支weakly connected graph――弱连通图weighed graph ――赋权图weighted graph――带权图weighting method――加权法win expectation――收益期望值Zzero flow――零流zero-sum game――零和对策zero-sum two person infinite game――二人无限零和对策。
国际自动化与计算杂志.英文版.
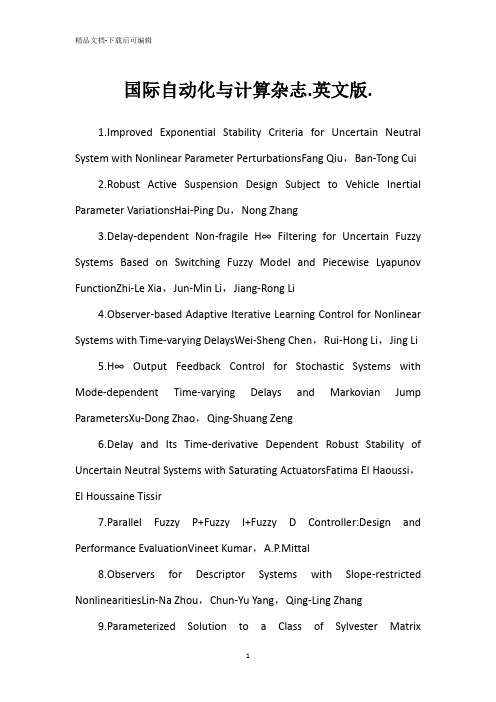
国际自动化与计算杂志.英文版.1.Improved Exponential Stability Criteria for Uncertain Neutral System with Nonlinear Parameter PerturbationsFang Qiu,Ban-Tong Cui2.Robust Active Suspension Design Subject to Vehicle Inertial Parameter VariationsHai-Ping Du,Nong Zhang3.Delay-dependent Non-fragile H∞ Filtering for Uncertain Fuzzy Systems Based on Switching Fuzzy Model and Piecewise Lyapunov FunctionZhi-Le Xia,Jun-Min Li,Jiang-Rong Li4.Observer-based Adaptive Iterative Learning Control for Nonlinear Systems with Time-varying DelaysWei-Sheng Chen,Rui-Hong Li,Jing Li5.H∞ Output Feedback Control for Stochastic Systems with Mode-dependent Time-varying Delays and Markovian Jump ParametersXu-Dong Zhao,Qing-Shuang Zeng6.Delay and Its Time-derivative Dependent Robust Stability of Uncertain Neutral Systems with Saturating ActuatorsFatima El Haoussi,El Houssaine Tissir7.Parallel Fuzzy P+Fuzzy I+Fuzzy D Controller:Design and Performance EvaluationVineet Kumar,A.P.Mittal8.Observers for Descriptor Systems with Slope-restricted NonlinearitiesLin-Na Zhou,Chun-Yu Yang,Qing-Ling Zhang9.Parameterized Solution to a Class of Sylvester MatrixEquationsYu-Peng Qiao,Hong-Sheng Qi,Dai-Zhan Cheng10.Indirect Adaptive Fuzzy and Impulsive Control of Nonlinear SystemsHai-Bo Jiang11.Robust Fuzzy Tracking Control for Nonlinear Networked Control Systems with Integral Quadratic ConstraintsZhi-Sheng Chen,Yong He,Min Wu12.A Power-and Coverage-aware Clustering Scheme for Wireless Sensor NetworksLiang Xue,Xin-Ping Guan,Zhi-Xin Liu,Qing-Chao Zheng13.Guaranteed Cost Active Fault-tolerant Control of Networked Control System with Packet Dropout and Transmission DelayXiao-Yuan Luo,Mei-Jie Shang,Cai-Lian Chen,Xin-Ping Guanparison of Two Novel MRAS Based Strategies for Identifying Parameters in Permanent Magnet Synchronous MotorsKan Liu,Qiao Zhang,Zi-Qiang Zhu,Jing Zhang,An-Wen Shen,Paul Stewart15.Modeling and Analysis of Scheduling for Distributed Real-time Embedded SystemsHai-Tao Zhang,Gui-Fang Wu16.Passive Steganalysis Based on Higher Order Image Statistics of Curvelet TransformS.Geetha,Siva S.Sivatha Sindhu,N.Kamaraj17.Movement Invariants-based Algorithm for Medical Image Tilt CorrectionMei-Sen Pan,Jing-Tian Tang,Xiao-Li Yang18.Target Tracking and Obstacle Avoidance for Multi-agent SystemsJing Yan,Xin-Ping Guan,Fu-Xiao Tan19.Automatic Generation of Optimally Rigid Formations Using Decentralized MethodsRui Ren,Yu-Yan Zhang,Xiao-Yuan Luo,Shao-Bao Li20.Semi-blind Adaptive Beamforming for High-throughput Quadrature Amplitude Modulation SystemsSheng Chen,Wang Yao,Lajos Hanzo21.Throughput Analysis of IEEE 802.11 Multirate WLANs with Collision Aware Rate Adaptation AlgorithmDhanasekaran Senthilkumar,A. Krishnan22.Innovative Product Design Based on Customer Requirement Weight Calculation ModelChen-Guang Guo,Yong-Xian Liu,Shou-Ming Hou,Wei Wang23.A Service Composition Approach Based on Sequence Mining for Migrating E-learning Legacy System to SOAZhuo Zhang,Dong-Dai Zhou,Hong-Ji Yang,Shao-Chun Zhong24.Modeling of Agile Intelligent Manufacturing-oriented Production Scheduling SystemZhong-Qi Sheng,Chang-Ping Tang,Ci-Xing Lv25.Estimation of Reliability and Cost Relationship for Architecture-based SoftwareHui Guan,Wei-Ru Chen,Ning Huang,Hong-Ji Yang1.A Computer-aided Design System for Framed-mould in Autoclave ProcessingTian-Guo Jin,Feng-Yang Bi2.Wear State Recognition of Drills Based on K-means Cluster and Radial Basis Function Neural NetworkXu Yang3.The Knee Joint Design and Control of Above-knee Intelligent Bionic Leg Based on Magneto-rheological DamperHua-Long Xie,Ze-Zhong Liang,Fei Li,Li-Xin Guo4.Modeling of Pneumatic Muscle with Shape Memory Alloy and Braided SleeveBin-Rui Wang,Ying-Lian Jin,Dong Wei5.Extended Object Model for Product Configuration DesignZhi-Wei Xu,Ze-Zhong Liang,Zhong-Qi Sheng6.Analysis of Sheet Metal Extrusion Process Using Finite Element MethodXin-Cun Zhuang,Hua Xiang,Zhen Zhao7.Implementation of Enterprises' Interoperation Based on OntologyXiao-Feng Di,Yu-Shun Fan8.Path Planning Approach in Unknown EnvironmentTing-Kai Wang,Quan Dang,Pei-Yuan Pan9.Sliding Mode Variable Structure Control for Visual Servoing SystemFei Li,Hua-Long Xie10.Correlation of Direct Piezoelectric Effect on EAPap under Ambient FactorsLi-Jie Zhao,Chang-Ping Tang,Peng Gong11.XML-based Data Processing in Network Supported Collaborative DesignQi Wang,Zhong-Wei Ren,Zhong-Feng Guo12.Production Management Modelling Based on MASLi He,Zheng-Hao Wang,Ke-Long Zhang13.Experimental Tests of Autonomous Ground Vehicles with PreviewCunjia Liu,Wen-Hua Chen,John Andrews14.Modelling and Remote Control of an ExcavatorYang Liu,Mohammad Shahidul Hasan,Hong-Nian Yu15.TOPSIS with Belief Structure for Group Belief Multiple Criteria Decision MakingJiang Jiang,Ying-Wu Chen,Da-Wei Tang,Yu-Wang Chen16.Video Analysis Based on Volumetric Event DetectionJing Wang,Zhi-Jie Xu17.Improving Decision Tree Performance by Exception HandlingAppavu Alias Balamurugan Subramanian,S.Pramala,B.Rajalakshmi,Ramasamy Rajaram18.Robustness Analysis of Discrete-time Indirect Model Reference Adaptive Control with Normalized Adaptive LawsQing-Zheng Gao,Xue-Jun Xie19.A Novel Lifecycle Model for Web-based Application Development in Small and Medium EnterprisesWei Huang,Ru Li,Carsten Maple,Hong-Ji Yang,David Foskett,Vince Cleaver20.Design of a Two-dimensional Recursive Filter Using the Bees AlgorithmD. T. Pham,Ebubekir Ko(c)21.Designing Genetic Regulatory Networks Using Fuzzy Petri Nets ApproachRaed I. Hamed,Syed I. Ahson,Rafat Parveen1.State of the Art and Emerging Trends in Operations and Maintenance of Offshore Oil and Gas Production Facilities: Some Experiences and ObservationsJayantha P.Liyanage2.Statistical Safety Analysis of Maintenance Management Process of Excavator UnitsLjubisa Papic,Milorad Pantelic,Joseph Aronov,Ajit Kumar Verma3.Improving Energy and Power Efficiency Using NComputing and Approaches for Predicting Reliability of Complex Computing SystemsHoang Pham,Hoang Pham Jr.4.Running Temperature and Mechanical Stability of Grease as Maintenance Parameters of Railway BearingsJan Lundberg,Aditya Parida,Peter S(o)derholm5.Subsea Maintenance Service Delivery: Mapping Factors Influencing Scheduled Service DurationEfosa Emmanuel Uyiomendo,Tore Markeset6.A Systemic Approach to Integrated E-maintenance of Large Engineering PlantsAjit Kumar Verma,A.Srividya,P.G.Ramesh7.Authentication and Access Control in RFID Based Logistics-customs Clearance Service PlatformHui-Fang Deng,Wen Deng,Han Li,Hong-Ji Yang8.Evolutionary Trajectory Planning for an Industrial RobotR.Saravanan,S.Ramabalan,C.Balamurugan,A.Subash9.Improved Exponential Stability Criteria for Recurrent Neural Networks with Time-varying Discrete and Distributed DelaysYuan-Yuan Wu,Tao Li,Yu-Qiang Wu10.An Improved Approach to Delay-dependent Robust Stabilization for Uncertain Singular Time-delay SystemsXin Sun,Qing-Ling Zhang,Chun-Yu Yang,Zhan Su,Yong-Yun Shao11.Robust Stability of Nonlinear Plants with a Non-symmetric Prandtl-Ishlinskii Hysteresis ModelChang-An Jiang,Ming-Cong Deng,Akira Inoue12.Stability Analysis of Discrete-time Systems with Additive Time-varying DelaysXian-Ming Tang,Jin-Shou Yu13.Delay-dependent Stability Analysis for Markovian Jump Systems with Interval Time-varying-delaysXu-Dong Zhao,Qing-Shuang Zeng14.H∞ Synchronization of Chaotic Systems via Delayed Feedback ControlLi Sheng,Hui-Zhong Yang15.Adaptive Fuzzy Observer Backstepping Control for a Class of Uncertain Nonlinear Systems with Unknown Time-delayShao-Cheng Tong,Ning Sheng16.Simulation-based Optimal Design of α-β-γ-δ FilterChun-Mu Wu,Paul P.Lin,Zhen-Yu Han,Shu-Rong Li17.Independent Cycle Time Assignment for Min-max SystemsWen-De Chen,Yue-Gang Tao,Hong-Nian Yu1.An Assessment Tool for Land Reuse with Artificial Intelligence MethodDieter D. Genske,Dongbin Huang,Ariane Ruff2.Interpolation of Images Using Discrete Wavelet Transform to Simulate Image Resizing as in Human VisionRohini S. Asamwar,Kishor M. Bhurchandi,Abhay S. Gandhi3.Watermarking of Digital Images in Frequency DomainSami E. I. Baba,Lala Z. Krikor,Thawar Arif,Zyad Shaaban4.An Effective Image Retrieval Mechanism Using Family-based Spatial Consistency Filtration with Object RegionJing Sun,Ying-Jie Xing5.Robust Object Tracking under Appearance Change ConditionsQi-Cong Wang,Yuan-Hao Gong,Chen-Hui Yang,Cui-Hua Li6.A Visual Attention Model for Robot Object TrackingJin-Kui Chu,Rong-Hua Li,Qing-Ying Li,Hong-Qing Wang7.SVM-based Identification and Un-calibrated Visual Servoing for Micro-manipulationXin-Han Huang,Xiang-Jin Zeng,Min Wang8.Action Control of Soccer Robots Based on Simulated Human IntelligenceTie-Jun Li,Gui-Qiang Chen,Gui-Fang Shao9.Emotional Gait Generation for a Humanoid RobotLun Xie,Zhi-Liang Wang,Wei Wang,Guo-Chen Yu10.Cultural Algorithm for Minimization of Binary Decision Diagram and Its Application in Crosstalk Fault DetectionZhong-Liang Pan,Ling Chen,Guang-Zhao Zhang11.A Novel Fuzzy Direct Torque Control System for Three-level Inverter-fed Induction MachineShu-Xi Liu,Ming-Yu Wang,Yu-Guang Chen,Shan Li12.Statistic Learning-based Defect Detection for Twill FabricsLi-Wei Han,De Xu13.Nonsaturation Throughput Enhancement of IEEE 802.11b Distributed Coordination Function for Heterogeneous Traffic under Noisy EnvironmentDhanasekaran Senthilkumar,A. Krishnan14.Structure and Dynamics of Artificial Regulatory Networks Evolved by Segmental Duplication and Divergence ModelXiang-Hong Lin,Tian-Wen Zhang15.Random Fuzzy Chance-constrained Programming Based on Adaptive Chaos Quantum Honey Bee Algorithm and Robustness AnalysisHan Xue,Xun Li,Hong-Xu Ma16.A Bit-level Text Compression Scheme Based on the ACW AlgorithmHussein A1-Bahadili,Shakir M. Hussain17.A Note on an Economic Lot-sizing Problem with Perishable Inventory and Economies of Scale Costs:Approximation Solutions and Worst Case AnalysisQing-Guo Bai,Yu-Zhong Zhang,Guang-Long Dong1.Virtual Reality: A State-of-the-Art SurveyNing-Ning Zhou,Yu-Long Deng2.Real-time Virtual Environment Signal Extraction and DenoisingUsing Programmable Graphics HardwareYang Su,Zhi-Jie Xu,Xiang-Qian Jiang3.Effective Virtual Reality Based Building Navigation Using Dynamic Loading and Path OptimizationQing-Jin Peng,Xiu-Mei Kang,Ting-Ting Zhao4.The Skin Deformation of a 3D Virtual HumanXiao-Jing Zhou,Zheng-Xu Zhao5.Technology for Simulating Crowd Evacuation BehaviorsWen-Hu Qin,Guo-Hui Su,Xiao-Na Li6.Research on Modelling Digital Paper-cut PreservationXiao-Fen Wang,Ying-Rui Liu,Wen-Sheng Zhang7.On Problems of Multicomponent System Maintenance ModellingTomasz Nowakowski,Sylwia Werbinka8.Soft Sensing Modelling Based on Optimal Selection of Secondary Variables and Its ApplicationQi Li,Cheng Shao9.Adaptive Fuzzy Dynamic Surface Control for Uncertain Nonlinear SystemsXiao-Yuan Luo,Zhi-Hao Zhu,Xin-Ping Guan10.Output Feedback for Stochastic Nonlinear Systems with Unmeasurable Inverse DynamicsXin Yu,Na Duan11.Kalman Filtering with Partial Markovian Packet LossesBao-Feng Wang,Ge Guo12.A Modified Projection Method for Linear FeasibilityProblemsYi-Ju Wang,Hong-Yu Zhang13.A Neuro-genetic Based Short-term Forecasting Framework for Network Intrusion Prediction SystemSiva S. Sivatha Sindhu,S. Geetha,M. Marikannan,A. Kannan14.New Delay-dependent Global Asymptotic Stability Condition for Hopfield Neural Networks with Time-varying DelaysGuang-Deng Zong,Jia Liu hHTTp://15.Crosscumulants Based Approaches for the Structure Identification of Volterra ModelsHouda Mathlouthi,Kamel Abederrahim,Faouzi Msahli,Gerard Favier1.Coalition Formation in Weighted Simple-majority Games under Proportional Payoff Allocation RulesZhi-Gang Cao,Xiao-Guang Yang2.Stability Analysis for Recurrent Neural Networks with Time-varying DelayYuan-Yuan Wu,Yu-Qiang Wu3.A New Type of Solution Method for the Generalized Linear Complementarity Problem over a Polyhedral ConeHong-Chun Sun,Yan-Liang Dong4.An Improved Control Algorithm for High-order Nonlinear Systems with Unmodelled DynamicsNa Duan,Fu-Nian Hu,Xin Yu5.Controller Design of High Order Nonholonomic System with Nonlinear DriftsXiu-Yun Zheng,Yu-Qiang Wu6.Directional Filter for SAR Images Based on NonsubsampledContourlet Transform and Immune Clonal SelectionXiao-Hui Yang,Li-Cheng Jiao,Deng-Feng Li7.Text Extraction and Enhancement of Binary Images Using Cellular AutomataG. Sahoo,Tapas Kumar,B.L. Rains,C.M. Bhatia8.GH2 Control for Uncertain Discrete-time-delay Fuzzy Systems Based on a Switching Fuzzy Model and Piecewise Lyapunov FunctionZhi-Le Xia,Jun-Min Li9.A New Energy Optimal Control Scheme for a Separately Excited DC Motor Based Incremental Motion DriveMilan A.Sheta,Vivek Agarwal,Paluri S.V.Nataraj10.Nonlinear Backstepping Ship Course ControllerAnna Witkowska,Roman Smierzchalski11.A New Method of Embedded Fourth Order with Four Stages to Study Raster CNN SimulationR. Ponalagusamy,S. Senthilkumar12.A Minimum-energy Path-preserving Topology Control Algorithm for Wireless Sensor NetworksJin-Zhao Lin,Xian Zhou,Yun Li13.Synchronization and Exponential Estimates of Complex Networks with Mixed Time-varying Coupling DelaysYang Dai,YunZe Cai,Xiao-Ming Xu14.Step-coordination Algorithm of Traffic Control Based on Multi-agent SystemHai-Tao Zhang,Fang Yu,Wen Li15.A Research of the Employment Problem on Common Job-seekersand GraduatesBai-Da Qu。
自动验证技术获得图灵奖

Computer Education特别报道自动验证技术获得图灵奖刘瑞挺/文三人分享图灵奖正当我们忙于抗震救灾和准备奥运的时候,2008年6月21日晚,美国计算机协会(ACM)在旧金山召开了2007年度ACM颁奖盛典。
颁布了2007年度图灵奖、ACM Infosys基金会奖以及人工智能、软件系统、计算机理论与实践、计算科学与工程等领域的多个奖项。
2007年度ACM图灵奖由三位研究人员分享,分别是卡内基·梅隆大学的Edmund M. Clarke教授、德克萨斯大学奥斯汀分校的 E. Allen Emerson教授和法国Grenoble大学Verimag实验室的Joseph Sifakis教授,奖金是由英特尔公司和谷歌公司共同提供的25万美元,以表彰他们“在将模型检测发展为硬件和软件业中广泛采用的高效验证技术上的贡献”。
自动验证用途广今天,软件、硬件、网络的规模越来越大,例如一个芯片上就有上亿个晶体管电路,一个嵌入式系统虽小,也五脏俱全。
如果设计出了问题,一旦投产,损失就相当大。
如何在设计时就能证明系统正确,或者如何能及时发现设计中的错误呢?目前,一种成效卓著的自动验证技术(Automatic V erification Technology)已经在硬件和软件工业界得到了广泛的应用,特别是在半导体芯片的设计与生产中得到成功的应用。
正如英特尔研究中心副总裁钱安达(AndrewChien)在评价模型检测技术时所说:“英特尔和整个计算机工业都从他们的贡献中直接获益”。
谷歌的高级工程副总裁Alan Eustace也说:“谷歌像其他同时代的技术公司一样,很大一部分成功都来自于先驱们的研究贡献”。
这些祝贺与评价充满了真诚的感激之情。
模型检测是核心所谓模型检测技术(ModelChecking),本质上是用严密的数学方法来验证一个设计是否满足预先设定的需求,从而自动地发现设计中的错误。
按照定义,它是一种检查某一给定模型是否满足某一逻辑规则的方法。
两类布尔函数的OBDD阶
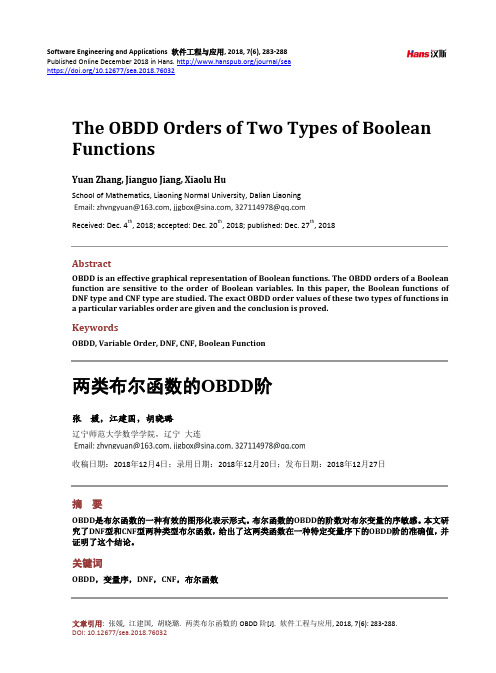
命题 1 给定 DNF 型布尔函数 f = 的 OBDD 阶为 nm + 2 。
∑∏ xij ( n, m ∈ N + ) ,在变量序 x11 x1m xn1 xnm 下
i =1 j =1
n
n
证明:采用数学归纳法。 基础步 取 m m ∈ N + 为定值,当 i = 1 时,布尔函数 = f x11 ⋅ x12 x1m 。则 f 在序 x11 x12 x1m 下
x1 x2 xn y1 y2 yn ,f 的 OBDD 阶是 2n +1 。
通过以上示例分析, 变量序对 OBDD 的影响是显著的, 一个好的变量序可以使布尔函数对应的 OBDD 更紧凑,从而减少空间的占用。而如果不幸选择了坏序,则 OBDD 的阶可能随变量数增多呈指数增长。 因此选择一个合适的变量序来构造布尔函数的 OBDD 显得尤为重要。
关键词
OBDD,变量序,DNF,CNF,布尔函数
文章引用: 张媛, 江建国, 胡晓璐. 两类布尔函数的 OBDD 阶[J]. 软件工程与应用, 2018, 7(6): 283-288. DOI: 10.12677/sea.2018.76032
张媛 等
Copyright © 2018 by authors and Hans Publishers Inc. This work is licensed under the Creative Commons Attribution International License (CC BY). /licenses/by/4.0/
The OBDD Orders of Two Types of Boolean Functions
02---故障树向二元决策图的转换算法
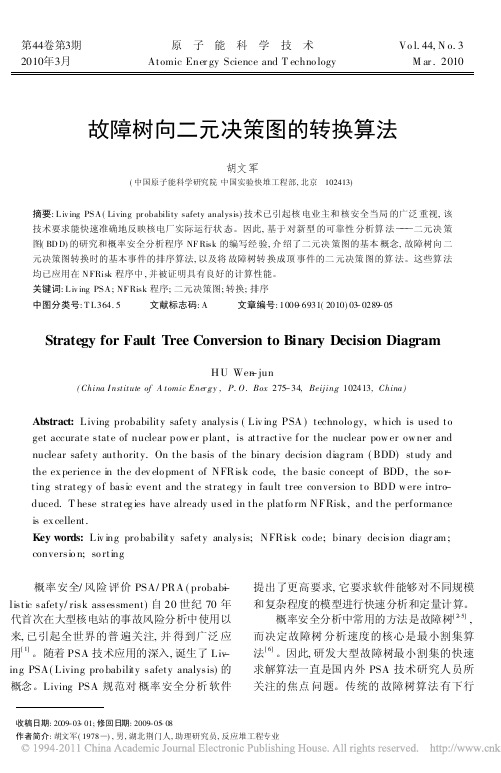
第44卷第3期原子能科学技术Vo l.44,N o.3 2010年3月Atomic Ener gy Science and T echno logy M ar.2010故障树向二元决策图的转换算法胡文军(中国原子能科学研究院中国实验快堆工程部,北京 102413)摘要:L iv ing PSA (Living pr obability safety analysis)技术已引起核电业主和核安全当局的广泛重视,该技术要求能快速准确地反映核电厂实际运行状态。
因此,基于对新型的可靠性分析算法 二元决策图(BD D)的研究和概率安全分析程序NF Risk 的编写经验,介绍了二元决策图的基本概念,故障树向二元决策图转换时的基本事件的排序算法,以及将故障树转换成顶事件的二元决策图的算法。
这些算法均已应用在N FRisk 程序中,并被证明具有良好的计算性能。
关键词:L iv ing PSA ;NF Risk 程序;二元决策图;转换;排序中图分类号:T L 364.5 文献标志码:A 文章编号:1000-6931(2010)03-0289-05Strategy for Fault Tree Conversion to Binary Decision DiagramH U Wen -jun收稿日期:2009-03-01;修回日期:2009-05-08作者简介:胡文军(1978 ),男,湖北荆门人,助理研究员,反应堆工程专业(China I nstitute of A tomic Ener gy ,P.O.Box 275-34,Beij ing 102413,China)Abstract:Living probability safety analysis (Liv ing PSA )technolo gy,w hich is used to get accurate state of nuclear pow er plant,is attractive for the nuclear pow er ow ner and nuclear safety authority.On the basis of the binary decision diag ram (BDD)study and the ex perience in the dev elo pment of NFRisk code,the basic concept of BDD,the so r -ting strateg y o f basic event and the strateg y in fault tree conversion to BDD w ere intro -duced.T hese strateg ies have already used in the platfo rm NFRisk,and the performance is ex cellent.Key words:Liv ing pro bability safety analysis;NFRisk co de;binary decision diagr am ;conversio n;so rting概率安全/风险评价PSA/PRA (probab-i listic safety/risk assessment)自20世纪70年代首次在大型核电站的事故风险分析中使用以来,已引起全世界的普遍关注,并得到广泛应用[1]。
逻辑综合中的大体概念

1. 逻辑综合(Logic Synthesis)EDA工具把数字电路的功能描述(或结构描述)转化为电路的结构描述。
实现上述转换的同时要满足用户给定的约束条件,即速度、功耗、成本等方面的要求。
2. 逻辑电路(Logic Circuit)逻辑电路又称数字电路,在没有特别说明的情况下指的是二值逻辑电路。
其电平在某个阈值之上时看作高电平,在该阈值之下时看作低电平。
通常把高电平看作逻辑值1;把低电平看作逻辑值0。
3. 约束(restriction)设计者给EDA工具提出的附加条件,对逻辑综合而言,约束条件一般包括速度、功耗、成本等方面的要求。
4. 真值表(Truth Table)布尔函数的表格描述形式,描述输入变量每一种组合情况下函数的取值。
输入变量组合以最小项形式表示,函数的取值为真或假(1 或0)。
5. 卡诺图(Karnaugh Map)布尔函数的图形描述形式,图中最小方格和最小项对应,两个相邻的最小方格所对应的最小项只有一个变量的取值不同。
卡诺图适合于用观察法化简布尔函数,但是当变量的个数大于4时,卡诺图的绘制和观察都变得很困难。
6. 单输出函数(Single-output Function)一个布尔函数的单独描述。
7. 多输出函数(Multiple-output Function)输入变量相同的多个布尔函数的统一描述。
8. 最小项(Minterm)设a1,a2,…a i,…a n是n个布尔变量,p为n个因子的乘积。
若是在p中每一变量都以原变量a i或反变量的形式作为因子出现一次且仅出现一次,则称p 为n个变量的一个最小项。
最小项在卡诺图中对应于最小的方格;在立方体表示中对应于极点。
9. 蕴涵项(Implicant)布尔函数f的"与-或"表达式中的每一乘积项都叫作f的蕴涵项。
例如:f=+中的乘积项和都是函数f的蕴涵项。
蕴涵项对应于立方体表示法中的立方体。
10.质蕴涵项(Prime Implicant,PI)设函数f有多个蕴涵项,若某个蕴涵项i所包含的最小项集合不是任何别的蕴涵项所包含的最小项集合的子集的话,则称i为函数f的质蕴涵项。
3_BDD
Introduction to BinaryDecision DiagramProf. Chien-Nan LiuTEL: 03-4227151 ext:4534Email: jimmy@.tw1Outlines•Representing Boolean Functions–Decision graph structure–Reduction to canonical form–Effect of variable ordering–Variants to reduce storage•Algorithms–General framework–Basic operations»Restriction (Cofactor)»If-Then-Else–Derived operations–Computing functional properties3Decision Structures−Vertex represents decision −Follow dashed line for value 0−Follow solid line for value 1−Function value determined by leaf valueX1X2X3f 00000010010001111000101111001111X1X2X2X3X3X3X30110Truth Table1Decision TreeBinary Decision Diagram (BDD)f = x 1x 2+x 3terminal node :•attribute–value(v) = 0–value(v) = 1nonterminal node :•index(v) = i •two children–low(v)–high(v)X1X2X2X3X3X3X31010111: 05BDDA BDD graph which has a vertex v as root corresponds to the function F v :(1) If v is a terminal node :a) if value(v) is 1, then F v = 1b) if value(v) is 0, then F v = 0(2) If F is a nonterminal node (with index(v) = i)F v (x 1, …, x n ) = x i ’F low(v)(x i+1, …, x n ) +x i F high(v)(x i+1, …, x n )Variable Ordering•Assign arbitrary total ordering to variablee.g. X1 < X2 < X3•Variable must appear in ascending order along all paths•Properties–No conflicting variable assignments along path –Simplifies manipulationX1X2X3X1X3X3X2X1X1X1OKNot OK7•Merge equivalent leavesX1X2X2X3X3X3X3010101X1X2X2X3X3X3X301aaaReduction Rule #2•Merge isomorphic nodesX1X2X2X3X3X3X31X1X2X2X3X301X X YZXYZ9•Eliminate Redundant TestsX1X2X2X3X301X1X2X301X YYExample ROBDD•Canonical representation of Boolean function for given variable ordering–Two functions equivalent iff graphs isomorphic»can be tested in linear time–Desirable property : The simplest form is canonicalX1X2X2X3X3X3X30111X1X2X301Initial GraphReduced Graph11Reduce•Visit OBDD bottom up and label each vertex with an identifier •Redundancy–if id( low(v ) ) = id( high(v ) ), then vertex v is redundant ⇒set id(v ) = id( low(v ) )–if id( low(v ) ) = id( low(u ) ) and id( high(v ) ) = id( high(u ) ), then set id(v ) = id(u )• A different identifier is given to each vertex at level i •Terminated when root is reached•An ROBDD is identified by a subset of vertices with different identifiersReducea bbcc101index=1index=2index=3123450101id =1id =1id =2id =1id =2id =3id =3id =4id =3id =51241id =1id =2id =3id =4id =5: 0(a)(b)(c)Construct ROBDD Directly•Using a hash table called unique table–Contain a key for each vertex of an OBDD–Key : (variable, right children, left children)–Constructed bottom up–Each key uniquely identify the specific function–Look up the table can determine if another vertex in thetable implements the same function13The Unique Table•Represent an ROBDD• A strong canonical form•Check equivalence of two Boolean functions by comparing the corresponding identifiers•Can represent multiple-output functions15Multi-Rooted ROBDDabc1id =1id =2id =3id =4id =5f = (a+b) cvariable order (a, b, c)Unique tableIdentifier Variable Right child Left child5 a 3 4 4 b 3 1 3 c 2 1KeyMulti-Rooted ROBDDa bc1id =1id =2id =3id =4id =5did =6f = (a+b) cg = b c df is constructed first and is associated with id =5g : id =6Unique tableIdentifier Variable Right child Left child6 d 4 1 5 a 3 4 4 b 3 1 3 c 2 1Key17The Unique Table•Unique table : hash table mapping (Xi, G, H) into a node in the DAG–before adding a node to the DAG, check to see if it already exists –avoids creating two nodes with the same function–strong canonical form : pointer equality determines function equalityHash Table Mapping (X1, T1, 1 ) --> U1(X1, T2, T1) --> U2(X2, T3, 1 ) --> T1(X2, 0 , T3) --> T2(X3, 0 , 1 ) --> T3X1X2X3U 2X211X11U 1T 1T 2T 3truefalseNon-Shared ROBDDU1 = X1’+ X2’+ X3’U2 = X1’X2’+ X1’X3’X1X2X3U 11110X1X2X3U 2X21119Multi-Rooted (Shared) ROBDD• A DAG node F is represented by a tuple (Xi, G, H)–Xi is called the top variable of F–node (Xi, G, H) represents the function ite(Xi, G, H) = XiG + Xi’H•DAG contains both external and internal functionsX1X2X3U 2X211X11U 1T 1T 2T 3U 1= X 1’+X 2’+X 3’=(X 1, T 1, 1)U 2= X 1’X 2’+X 1’X 3’=(X 1, T 2, T 1)T 1= X 2’+X 3’=(X 2, T 3, 1)T 2= X 2’X 3’=(X 2, 0, T 3)T 3= X 3’=(X 3, 0, 1)0 = (X ∞, 0, 0)1 = (X ∞, 1, 1)External functions User functionsInternal functionsSeparated vs. Shared•Separated–51 nodes for 4-bit adder–12481 nodes for 64-bit adder –Quadratic growth•Shared–31 nodes for 4-bit adder –571 nodes for 64-bit adder –Linear growth21Maintaining Shared ROBDD•Storage Model–Single, multiple-rooted DAG–Function represented by pointer to node in DAG –Maintain Unique (hash) table to keep canonical•Storage Management–User cannot know when storage for node can be freed –Must implement automatic garbage collection•Algorithmic Efficiency–Functions equivalent iff pointer equal»if (p1 == p2) ...–Can test in constant timeOrdering Effects•The size of ROBDD depends on the ordering of variablesex : x 1x 2+ x 3x 4x 1< x 2< x 3< x 4X1X3X21X423Ordering Effects (cont’d)x 1< x 3< x 2< x 4X1X3X31X2X4X2Sample Function Classes•General Experience–Many tasks have reasonable ROBDD representations –Algorithms remain practical for up to 100,000 vertex ROBDD–Heuristic ordering methods generally satisfactoryFunction Class Best WorstOrdering Sensitivity ALU (Add/Sub)Linear Exponential High Symmetric LinearQuadratic None MultipicationExponentialExponentialLow25Symbolic Manipulation•Strategy–Represent data as set of ROBDDs»with identical variable orderings–Express solution method as sequence of symbolic operations –Implement each operation by ROBDD manipulation •Algorithmic Properties–Arguments are ROBDDs with identical variable orderings –Result is ROBDD with same ordering –“Closure Property”•Two Basic Operations–Restriction –If-Then-ElseRestriction Operation•Concept–Effect of setting function argument Xi to constant K(0,1)–Also called Cofactor operation•Implementation–Depth-first traversal–Complexity near-linear in argument graph sizeFF[X i = K]KX i -1X i +1X 1X n….….27Restriction AlgorithmRestrict (F, x, k)Bypass any nodes for variable xChoose Hi child for k = 1Choose Lo child for k = 0Reduce resulte.g. Restrict variable b to 1a bb1c c a bb 01c c a1c c 01cFind nodesBypassReduceFFFFSpecial cases of Restriction•Case 1 : Restrict on root node variablex•Case 2 : Restrict on variable less than root node–e.g. x < yRestrict ( , x, 1 )xRestrict ( , x, 0 )yRestrict ( , x, 1 )y29If-Then-Else Operation•Concept–Basic technique for building ROBDD from network or formula•Argument I (if), T (then), E (else)–Functions over variables X –Represented as ROBDDs •Result–ROBDD representing composite function –IT +I’E •Implementation–combination of depth-first traversal and dynamic programming–Worst case complexity : product of argument graph sizesIf-Then-Else Algorithm•Recursive FormulationITE (I, T, E) = x ITE(I[x=1], T[x=1], E[x=1]) +x’ITE(I[x=0], T[x=0], E[x=0])•General Algorithm–Select top root variable x of I, T and E –Compute restrictions»Guaranteed to be one of special cases –Apply recursively to get results Lo and Hi –Still remain canonical form•Termination Conditions–I = 1 ==> Return T –I = 0 ==> Return E –T = 1, E = 0 ==> Return I31An ITE Example•Given f = ab + bc + ac, g = c under the order a < b < c ITE (f, g, 0)= ITE[ a , ITE( f (a=1), g (a=1), 0), ITE( f (a=0), g (a=0), 0)]= ITE[ a , ITE( b+bc+c, c, 0), ITE( bc, c, 0)]= ITE{ a , ITE[ b , ITE(1, c, 0), ITE(c, c, 0)],ITE[ b , ITE(c, c, 0), ITE(0, c, 0)]}= ITE[ a , ITE(b, c, c), ITE(b, c, 0)]= ITE[ a , c, ITE(b, c, 0)]ab 01c sel1T1E1=sel2T2sel1sel2T1T2E1E2b=1b=0Algorithmic Issues & Derived Operations•Efficiency–Maintain computed table and unique table to increaseefficiency–Worst case complexity product of graph sizes for I, T, E•Derived operations–Express as combination of If-Then-Else and Restrict –Preserve closure property»Result is a ROBDD with the same variable ordering33Detailed ITE AlgorithmITE(f, g, h) {if (terminal case)return (r = trivial result) ;else { /* exploit previous information */if (computed table has entry {(f, g, h), r} )return (r from computed table) ;else {x = top variable of f, g, h ;t = ITE(f x , g x , h x ) ;e = ITE(f x’, g x’, h x’) ;if (t == e) /* children with isomorphic OBDDs */return (t) ;r = find_or_add_unique_table(x, t, e) ; /* add r to unique table if not present */Update computed table with {(f, g, h), r} ;return (r) ;}}}Derived Algebraic Operations•Other common operations can be expressed in terms of If-Then-ElseMUXG F 0XMUXF 1X110F GXF GXAND (F, G)If-Then-Else (F, G, 0)If-Then-Else (F, 1, G)OR (F, G)35ITE OperatorsOperatorEquivalent ite form00f ‧g ite ( f, g, 0 )f ‧g ’ite ( f, g ’, 0 )f ff ’‧g ite ( f, 0, g )g gf ⊕g ite ( f, g ’, g )f + g ite ( f, 1, g )( f + g )’ite ( f, 0, g ’ )( f ⊕ g )’ite ( f, g, g ’ )g ’ite ( g, 0, 1 )f + g ’ite ( f, 1, g ’ )f ’ite ( f, 0, 1 )f ’ + g ite ( f, g, 1 )( f ‧g )’ite ( f, g ’, 1 )11Generating ROBDD from Network•Task : Represent output functions of gate network as ROBDDsa b c bac b cbb a A B C T 1T 2Out A new_var(“a”)B new_var(“b”)C new_var(“c”)T 1AND(A, B)T 2AND(B, C)Out OR(T 1, T 2)abcT1T2OutEvaluationNetwork37Functional Composition•Create new function by composing functions F and G •Useful for composing hierarchical modulesFF[X i = G]X i -1X i +1X 1X n….….GX nX 1…FX i -1X i +1X 1X n……FX i -1X i +1X 1X n……1MUX1GX nX 1…Variable Qualification•Eliminate dependency on some argument through qualificationF∃Xi FX i -1X i +1X 1X n….….∃FX i -1X i +1X 1X n ……FX i -1X i +1X 1X n……139Variants & Optimizations•Concept–Refinements to ROBDD representation –Do not change fundamental properties•Objective–Reduce memory requirement –Improve algorithmic efficiency–Make commonly performed operations faster•Common Optimizations–Share nodes among multiple functions –Negated arcsNegation Arcs•Concept–Dot on arc represents complement operator»Invert function value–Can appear internal or external arc01b a a+ba+b 01b aa+b41Effect of Negation Arcs•StorageSavings–At most 2X reduction in numbers of nodes•Algorithmic Improvement–Can complement function in constant time•Problem–Negation arc allow multiple representations of a function–Modify algorithms with restricted conversions for use of negative arcs1b a a + b 01baabDensity Computation•Definition–p(F) : fraction of variable assignments for which F = 1•Applications–Testability measures –Probability computations•Recursive Formulation–p(F) = [ p( F[x=1] ) + p( F[x=0] ) ] / 2•Computation–Compute bottom-up, starting at leaves –At each node, average density of childrend2d1d1a1a1d0d01a1a0a07/321/43/161/41/81/41/41/41/21/2Let E be a set and A ⊆EThe characteristic function of A is the function X A: E -> { 0, 1 }X A(x) = 1 if x ∈AX A(x) = 0 if x ∉AEx :E = { 1, 2, 3, 4 }A = { 1, 2 }X A(1) = 1X A(3) = 043Characteristic FunctionGiven a Boolean functionf : B n-> B mthe mapping relation denoted as F ⊆B n×B m isdefined asF(x, y) = { (x, y) ∈B n×B m| y = f(x) }The characteristic function of a function f is definedfor (x, y) s.t. X f(x, y) = 1 iff(x, y) ∈F45Ex : y = f(x1, x2) = x1 + x2x1 x2 y 0 0 00 1 11 0 11 1 1Fy(x1, x2, y) =x1 x2 y F 0 0 0 10 0 1 00 1 0 00 1 1 11 0 0 01 0 1 11 1 0 01 1 1 1Summary•ROBDD–Reduced graph representation of Boolean Function –Canonical for given variable ordering –Size sensitive to variable ordering•Algorithmic Principles–Operations maintain closure property»Result ROBDD with same ordering as arguments »Can perform further operations on results –Limited set of basic operations to implement»Restrict, If-Then-Else»Other operations defined in terms of basic operations。
计算机系统形式化验证中的模型检测方法综述
计算机系统形式化验证中的模型检测方法综述形式化方法是用数学和规律的方法来描述和验证系统设计是否满意需求。
它将系统属性和系统行为定义在抽象层次上,以形式化的标准语言去描述系统。
形式化的描述语言有多种,如一阶规律,Z 语言,时序规律等。
采纳形式化方法可以有效提高系统的平安性、全都性和正确性,关心分析冗杂系统并且及早觉察错误。
形式化验证是保证系统正确性的重要方法,主要包括以数学、规律推理为根底的演绎验证(deductive verification)和以穷举状态为根底的模型检测(model checking)。
演绎验证是基于人工数学来证明系统模型的正确性。
它利用规律公式来描述系统,通过定理或证明规章来证明系统的某些性质。
演绎验证既可以处理有限状态系统,又可以解决无限状态问题。
但是演绎验证的过程一般为定理证明器帮助,人工参加,无法做到完全自动化,推导过程冗杂,工作量大,效率低,不能适用于大型的冗杂系统,因此适用范围较窄。
常见的演绎验证工具有HOL,ACL2,PVS和TLV等。
模型检测主要应用于验证并发的状态转换系统,通过遍历系统的状态空间,对有限状态系统进展全自动验证,快速高效地验证出系统是否满意其设计期望。
下面将主要介绍模型检测方法的进展历史和讨论现状,以及当前面临的挑战和将来进展方向等问题。
2 模型检测及相关技术模型检测方法最初由Clarke,Emerson等人于1981年提出,因其自动化高效等特点,在过去的几十年里被广泛用于实时系统、概率系统和量子等多个领域。
模型检测根本要素有系统模型和系统需满意的属性,其中属性被描述成时态规律公式Φ。
检测系统模型是否满意时态规律公式Φ,假设满意那么返回“是”,不满意那么返回“否”及其错误路径或反例。
时态规律主要有线性时态规律LTL(Linear TemporalLogic)和计算树规律CTL(Computation Tree Logic)。
2.1 线性时态规律对一个系统进展检测,重要的是对系统状态正确性要求的形式化,其中一个根本维度是时间,同时需要知道检验结果与时间维度的关系。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
Resolution and Binary Decision Diagramscannot simulate each other polynomiallyJan Friso Groote1,2Hans Zantema1,3JanFriso.Groote@cwi.nl hansz@cs.uu.nl1:CWI,P.O.Box94.079,1090GB Amsterdam,The Netherlands2:Department of Mathematics and Computing Science,Eindhoven University of TechnologyP.O.Box513,5600MB Eindhoven,The Netherlands3:Department of Computer Science,Utrecht University,P.O.Box80.089,3508TB Utrecht,The NetherlandsAbstractThere are many different ways of proving formulas in proposition logic.Many of these caneasily be characterized as forms of resolution(e.g.[12]and[9]).Others use so-called binarydecision diagrams(BDDs)[2,10].Experimental evidence suggests that BDDs and resolutionbased techniques are fundamentally different,in the sense that their performance can differ verymuch on benchmarks[14].In this paper we confirm thesefindings by mathematical proof.Weprovide examples that are easy for BDDs and exponentially hard for any form of resolution,andvice versa,examples that are easy for resolution and exponentially hard for BDDs.1IntroductionWe consider formulas in proposition logic:formulas consisting of proposition letters from some set P,constants t(true)and f(false)and connectives∨,∧,¬,→and↔.There are different ways of proving the correctness of these formulas,i.e.,proving that a given formula is a tautology.In the automatic reasoning community resolution is a popular proof technique, underlying the vast majority of all proof search techniques in this area,including for instance the well known branch-and-bound based technique named after Davis-Putnam-Loveland[5] or the remarkably effective methods by St˚almarck[12]and the GRASP prover[9].In the VLSI and the process analysis communities binary decision diagrams(BDDs)are popular[2,10].BDDs have caused a considerable increase of the scale of systems that can be verified,far beyond anything a resolution based method has achieved.On the other hand there are many examples where resolution based techniques out-perform BDDs with a major factor,for instance in proving safety of railway interlockings([7]).Out-performance in both directions has been described in[14].However,benchmark studies only provide an impression,saying very little about the real relation of resolution and BDDs.The results may be influenced by badly chosen variable orderings in BDDs or non optimal proof search strategies in resolution.Actually,givensuch benchmarks it can not be excluded that there exist a resolution based technique that always out-performs BDDs,provided a proper proof search strategy would be chosen.So,a mathematical comparison between the techniques is called for.This is not straightforward, as resolution and BDDs look very different.BDDs work on arbitrary formulas,whereas resolution is strictly linked to formulas in conjunctive normal form.And the resolution rule and the BDD construction algorithms appear of a totally dissimilar nature.Moreover,classical(polynomial)complexity bounds cannot be used,as the problem we are dealing with is(co-)NP-complete.Fortunately,polynomial simulations provide an elegant way of dealing with this(see e.g.[16]).We say that proof system A polynomially simulates proof system B if for every formulaφthe size of the proof ofφin system A is smaller than a polynomial applied to the size of the proof ofφin system B.Of course,if the polynomial is more than linear,proofs in system A may still be substantial longer than proofs in system B, but at least the proofs in A are never exponentially longer.It is self evident that for practical applications it is important that the order of the polynomial is low.If it can be shown that for some formulas in B the proofs are exponentially longer than those in A we consider A as a strictly better proof system than B.It has for instance been shown that‘extended resolution’is strictly better than resolution[8],being strictly better than Davis-Putnam resolution[6]; for an extended overview of comparisons of systems based on resolution,Frege systems and Gentzen systems we refer to[16].We explicitly construct a sequence of biconditional formulas that are easy for BDDs,but exponentially hard for resolution.The proof that they are indeed hard for resolution is based on results from[15,1].The reverse is easier,namely showing that there is a class of formulas easy for any‘reasonable’form of resolution and exponentially hard for BDDs.Here the formulas are related to the pigeon hole formulas,for which we prove that the BDD approach is exponentially hard,which is of interest in itself.It was proven before in[8]that for the same formulas resolution is exponentially hard for every strategy.We start with preliminaries on OBDDs in Section2.In Section3we prove that OBDD proofs are exponential for pigeon hole formulas and related formulas.In Section4we prove that OBDD proofs are polynomial for biconditional formulas.In Section5we present our results on resolution.In Section6we present the our main results in comparing resolution and OBDDs.Finally,in Section7we describe some points of further research. Acknowledgment.Special thanks go to Oliver Kullmann and Alasdair Urquhart for their help with lower bounds for resolution.2Binary Decision DiagramsThe kind of Binary Decision Diagrams that we use presupposes a total ordering<on P,and therefore are also called Ordered Binary Decision Diagrams(OBDDs).First we present some basic definitions and properties as they are found in e.g.[2,10].An OBDD is a Directed Acyclic Graph(DAG)where each node is labeled by a proposition letter from P,except for nodes that are labeled by0and1.From every node labeled by a proposition letter,there are two outgoing edges,labeled‘left’and‘right’,to nodes labeled by0or1,or a proposition letter strictly higher in the ordering>.The nodes labeled by0and1do not have outgoing edges.An OBDD compactly represents which valuations are valid,and which are not.Given a valuationσand an OBDD B,theσwalk of B is determined by starting at the root of theDAG,and iteratively following the left edge ifσvalidates the label of the current node,and otherwise taking the right edge.If0is reached by aσ-walk then B makesσinvalid,and if1 is reached then B makesσvalid.We say that an OBDD represents a formula if the formula and the OBDD validate exactly the same valuations.An OBDD is called reduced if the following two requirements are satisfied.1.For no node its left and right edge go to the same node.It is straightforward to seethat a node with such a property can be removed.We call this the eliminate operation.2.There are no two nodes with the same label of which the left edges go to the same node,and the right edges go to the same node.If this is the case these nodes can be taken together,which we call the merge operation.Applying the merge and the eliminate operator to obtain a reduced OBDD can be done in linear time.Reduced OBDDs have the following very nice property.Lemma2.1.For afixed order<on P,every propositional formulaφis uniquely represented by a reduced OBDD B(φ,<),andφand psi are equivalent if and only if B(φ,<)=B(ψ,<). As a consequence,a propositional formulaφis a contradiction if and only if B(φ,<)=0, and it is a tautology if and only if B(φ,<)=1.Hence by computing B(φ,<)for any suitable order<we can establish whetherφis a contradiction,orφis a tautology,orφis satisfiable. If the order<isfixed we shortly write B(φ)instead of B(φ,<).We write#(B(φ))for the number of internal nodes in B(φ).The main ingredient for the computation of B(φ)is the apply-operation:given the reduced OBBDs B(φ)and B(ψ)for formulasφandψand a binary connective⋄∈{∨,∧,→,↔}as parameters,the apply-operation computes B(φ⋄ψ).For the usual implementation of apply as described in[2,10]both time and space complexity are O(#(B(φ))∗#(B(ψ))).If B(φ)is known then B(¬φ)is computed in linear time simply by replacing every0by1and vice versa; this computation is considered as a particular case of an apply-operation.Now for everyφits reduced OBDD B(φ)can be computed by recursively calling the apply-operation.As the basis of this recursion we need the reduced OBDDs for the single proposition letters.These are simple:the reduced OBDD for p consists of a node labeled by p,having a left outgoing edge to0and a right outgoing edge to1.By maintaining a hash-table for all sub-formulas it can be avoided that for multiple occurrences of sub-formulas the reduced OBDD is computed more than once.By the OBDD proof of a formulaφwe mean the recursive computation of B(φ)using the apply-operation as described above.Ifφconsists of n boolean connectives then this proof consists of exactly n calls of the apply-operation.However,by the expansion of sizes of the arguments of apply this computation can be of exponential complexity,even if it ends in B(φ)=0.As the satisfiability problem is NP-complete,this is expected to be unavoidable for every way to compute B(φ).We give an explicit construction of formulas for which we prove that the OBDD proofs are of exponential size,independently of the order<on P.In[3] it was proved that representing the middle bits of a binary multiplier requires an exponential OBDD;this function is easily represented by a small circuit,but not by a small formula,and hence does not serve for our goal of having a small formula with an exponential OBDD proof.3Pigeon hole formulasIn this section we prove lower bounds for OBDD proofs for pigeon hole formulas and related formulas.Definition 3.1.Let m,n be positive integers and let p ij be distinct variables for i =1,...,m and j =1,...,n .LetC m,n =m i =1(n j =1p ij ),R m,n =n j =1(m i =1p ij ),R m,n = j =1,...,n,1≤i<k ≤m (¬p ij ∨¬p kj ),CR m,n =C m,n ∧R m,n PF m,n =C m,n ∧R m,n .In order to understand these formulas put the variables in a matrix according to the indexes.The formula C m,n states that in every of the m columns at least one variable is true,the formula R m,n states that in every of the n rows at least one variable is true,and the formula R m,n states that in every of the n rows at most one variable is true.Hence if C m,n holds then at least m of the variables p ij are true and if R m,n holds then at most n of the variables p ij are true.Hence if m >n then PF m,n is a contradiction.Since this reasoning describes the well-known pigeon hole principle,the formulas PF m,n are called pigeon hole formulas.Note that PF m,n is in conjunctive normal form.In [8]it has been proved that for every resolution proof for PF n +1,n the length is at least exponential in n .Here we prove a similar exponential lower bound for OBDD proofs,which is of interest in itself since pigeon hole formulas are widely considered as benchmark formulas.For the main result of the paper however we get better results by using similar lower bounds for CR m,n instead since the size of CR n,n is quadratic in n while pigeon hole formulas have cubic sizes.The contradictory formula in the main result is p ∧(¬p ∧CR n,n ).Our proof of these lower bounds has been inspired by the proof from [14]that every OBDD for CR n,n has a size that is exponential in √n ,which we improve to a size that is exponential in n .First we need two lemmas.Lemma 3.2.Let φbe a formula over variables in any finite set P .Let <be a total order on P .Let k <#P .Write I B ={0,1}.Let f φ:I B #P →I B the function representing φ,in such a way that the smallest k elements of P with respect to <correspond to the first k arguments of f φ.Let A ⊆{1,...,k }.Let z ∈I B k .Assume that for every distinct x , x ′∈I B k satisfying x i =x ′i =z i for all i ∈A there existsy ∈I B #P−k such that f φ( x , y )=f φ( x ′, y ).Then #B (φ,<)≥2#A .Proof.There are 2#A different ways to choose x ∈I B k satisfying x i =z i for all i ∈A .Now from the assumption it is clear that by fixing the first k arguments of f φ,at least 2#A different functions in the remaining #P −k arguments are obtained.All of these functions correspond to different nodes in the reduced OBDD B (φ,<),proving the lemma.2Lemma 3.3.Let m,n ≥1.Consider a matrix of n rows and m columns.Let the matrix entries be colored equally white and black,i.e.,the difference between the number of whiteentries and the number of black entries is at most one.Then at least (m −1)√22columns or at least (n −1)√22rows contain both a black and a white entry.Proof.If all rows contain both a black and a white entry we are done,so we may assume that at least one row consists of entries of the same color.By symmetry we may assume all entries of this row are white.If also a row exists with only black entries,then all columns contain both a black and a white entry and we are done.Since there is a full white row,we conclude that no full black column exists.Let r be the number of full white rows and c be the number of full white columns.The number of entries in these full white rows and columns together is mr +cn −cr ,and the total number of white entries is at most mn +12,hencemn +12≥mr +cn −cr =mn −(m −c )(n −r ).Assume the lemma does not hold.Then m −c <(m −1)√22and n −r <(n −1)√22,andmn +12≥mn −(m −c )(n −r )>mn −(m −1)√22∗(n −1)√22=mn −(m −1)(n −1)2from which we conclude m +n <2,contradiction.2Theorem 3.4.For m ≥n ≥1and for every total order <on P ={p ij |i =1,...,m,j =1,...,n }both time and space complexity of the OBDD proofs of both CR m,n and PF m,n is Ω(1.63n ).Proof.The last step in the OBDD proof of CR m,n is the application of apply on B (C m,n ,<)and B (R m,n ,<);the last step in the OBDD proof of PF m,n is the application of apply on B (C m,n ,<)and B (R m,n ,<).We prove that at either the OBDD B (C m,n ,<)has size at least 2(m −1)√22or both the OBDDs B (R m,n ,<)and B (R m,n ,<)have size at least 2(n −1)√22.Since m ≥n and 2√22>1.63,then the theorem immediately follows.Let P <⊂P consist of the ⌊nm 2⌋smallest elements of P with respect to <,and let P >=P \P <.hence elements of P >are greater than elements of P <.We say that row j ={p ij |i =1,...,m }is mixed if i,i ′exist such that p ij ∈P <and p i ′j ∈P >;we say that column i ={p ij |j =1,...,n }is mixed if j,j ′exist such that p ij ∈P <and p ij ′∈P >.From Lemma 3.3we conclude that either at least (n −1)√22rows are mixed or at least (m −1)√22columns are mixed.For both cases we will apply Lemma 3.2for k =⌊nm 2⌋.We number the elements of P from 1to mn such that the numbers 1,...,k correspond to the elements of P <.Assume that at least (m −1)√22columns are mixed.For every mixed column fix one element of P <in that column;collect the numbers of these elements in the set A .For i =1,...,k define z i =1for i corresponding to matrix elements in non-mixed columns and z i =0for i corresponding to matrix elements in mixed columns.Choose x , x ′∈I B k satisfying x = x ′and x i =x ′i =z i for all i ∈A .Then there exists i ∈A such that x i =x ′i .Now let y =(y k +1,...,y mn )be the vector defined by y j =0if j ∈P >corresponds to a matrix element in the same column as i ,and y j =1otherwise.Interpret the concatenation of x and y as an assignment to {0,1}on the matrix entries.Non-mixed columns contain only the value 1,and every mixed columns contains at least one value 1,except for one column which consists purely of zeros if and only if x i =0.Hence f C m,n ( x , y )=x i ,and similarlyf Cm,n( x′, y)=x′i.Since x i=x′i we obtain f C m,n( x, y)=f C m,n( x′, y).Now by Lemma3.2weconclude that#B(C m,n,<)≥2#A≥2(m−1)√22.For the remaining case assume that at least(n−1)√22rows are mixed.The required boundfor#B(R m,n,<)follows exactly as above by symmetry.It remains to prove the bound for #B(R m,n,<).For every mixed rowfix one element of P<in that row;collect all these elements in the set A.Define z i=0for all i=1,...,k.Choose x, x′∈I B k satisfying x= x′and x i=x′i=z i=0for all i∈A.Then there exists i∈A such that x i=x′i.Now definey=(y k+1,...,y mn)by choosing y j=0for all but one j,and y j=1for one single j for which i and j correspond to matrix elements in the same row.This is possible because i corresponds to an entry in a mixed row.Since in every other row at most one value is set to 1all corresponding clauses in R m,n are true.The only clause in R m,n that is possibly falseis the one corresponding to i and j.We obtain f Rm,n ( x, y)=¬x i and f Rm,n( x′, y)=¬x′i.Since x i=x′i we have f m,n( x, y)=f m,n( x′, y).Now by Lemma3.2we conclude that #B(R m,n,<)≥2#A≥2(n−1)√22.2 Note that we proved that either C m,n or both R m,n and R m,n must have OBDDs of exponential size.However,for each of these formulas seperately a properly chosen order may lead to small OBDDs.Indeed,ifp ij<p i′j′⇐⇒(i<i′)∨(i=i′∧j<j′)then#B(C m,n,<)=mn and ifp ij<p i′j′⇐⇒(j<j′)∨(j=j′∧i<i′)then#B(R m,n,<)=mn and#B(R m,n,<)=2(m−1)n,all being linear in the number of variables.4Biconditional formulasAn interesting class of formulas are biconditional formulas consisting of proposition letters, biconditionals(↔)and negations(¬).Biconditionals have very nice properties:they are associative,φ↔(ψ↔χ)≡(φ↔ψ)↔χ,commutative,φ↔ψ≡ψ↔φ,idempotent,φ↔φ≡t and negation distributes over the biconditionalφ↔¬ψ≡¬(φ↔ψ).Using these properties it is easy to show that there exists for every biconditional formulaφa biconditional normal formψin which there is at most one negation,and each proposition letter occurs at most once,such thatφ≡ψ.For a string S=p1,p2,p3,...,p n of proposition letters,where letters are allowed to occur more than once,we write[S]=p1↔(p2↔(p3···(p n−1↔p n))···).It is not difficult to see that[S]is a tautology if and only if all letters occur an even number of times in S.The BDD technique turns out to be very effective for biconditional formulas.We show that for any biconditional formulaφits OBDD proof has a polynomial complexity.For anybiconditional formula φ,we write |φ|for the size of φ,α(φ)for the number of variables occurring in φand αodd (φ)for the number of variables that occur an odd number of times in φ.It is useful to speak about the OBDD of n formulas,φ1,...,φn .This OBDD is a single DAG with up to n root nodes.The notion reduced carries over to these OBDDs.In particular,if φi and φj are equivalent,then the i th and j th root node are the same.Again the size of a DAG is defined to be the number of its internal nodes.We have the following lemma,showing that each reduced OBDD for a biconditional formula is small.Lemma 4.1.Let φbe a biconditional formula.Any reduced OBDD for φand ¬φhas size 2αodd (φ).Proof.First fix an arbitrary ordering <on the proposition letters.Note that there is a biconditional normal form ψthat is equivalent to φ.As by Lemma 2.1the reduced OBDD of φand ψare the same,we can as well construct the OBDD of ψ.Moreover,αodd (φ)=αodd (ψ).We prove this theorem by induction on αodd (ψ).•αodd (ψ)=0.As ψis a biconditional normal form,it does not contain any proposition letter,and hence is either equivalent to true or false.So,the reduced OBDD of φand ¬φdoes not contain internal nodes at all,and has size 0.•α(ψ)odd =n +1.Consider the first letter in the ordering <that occurs in ψand let it be p .The OBDDs for ψand ¬ψlook like:•p B ψ ©d d d •t t t B ψ[1/p ]•t t t B ψ[0/p ]•pB ¬ψ ©d d d •t t t B ¬ψ[1/p ]•t t t B ¬ψ[0/p ]Here ψ[v/p ]is the formula ψwhere v has been substituted for p .Clearly,as p occurs an odd time in ψ,ψ[0/p ]≡¬ψ[1/p ]and ψ[1/p ]≡¬ψ[0/p ].So,the reduced OBDD of ψ[0/p ],¬ψ[1/p ],ψ[1/p ]and ¬ψ[0/p ]is the same as the OBDD of ψ[0/p ]and ¬ψ[0/p ].Using the induction hypothesis,the size of this OBDD must be 2n .The reduced OBDD for ψand ¬ψadds two new nodes.So,the size of the reduced OBDD of ψand ¬ψis 2n +2.This equals 2αodd (ψ)+2,finishing the proof.2Theorem 4.2.Let <be an ordering on the proposition letters.•The complexity of the corresponding OBDD proof for any biconditional formula φis O (|φ|3).•The complexity of the corresponding OBDD proof for [S ]or ¬[S ]for any string S of proposition letters is O (|S |2).Proof.The OBDD proof forφconsists of O(|φ|)applications of apply applied on reduced OBDDs of sub-formulas ofφ.By Lemma4.1each of these reduced OBDDs has size O(|φ|).Since the complexity of apply(↔,B,B′)is O(#B∗#B′)and the complexity of apply(¬,B) is O(#B)for every apply operation the complexity is O(|φ|2),yielding O(|φ|3)for the fullOBDD proof forφ.For the OBDD proof for[S]or¬[S]only applications of apply(↔,B,B′)occur with #B=1,giving the complexity O(#B′),yielding O(|S|2)for the full OBDD proof.25ResolutionResolution is a very common technique to prove formulas.Contrary to the BDD technique, it is applied to formulas in conjunctive normal form(CNF),i.e.formulas of the formi∈I j∈J il ijwhere I and J i arefinite index sets and l ij is a literal,i.e.a formula of the form p or¬p for a proposition letter p.Each sub-formula j∈J i l ij is called a clause.As∧and∨are associative, commutative and idempotent it is allowed and convenient to view clauses as sets of literals and CNFs as sets of clauses.The resolution rule can be formulated by:{p,l1,...,l n}{¬p,l′1,...,l′n′}{l1,...,l n,l′1,...,l′n′}where p is a proposition letter and l i,l′j are literals.A proof of a set of clauses F is a sequence of clauses where the last clause is empty and each clause in the sequence is either taken from F,or matches the conclusion of the resolution rule,where both premises occur earlier in the sequence.In case one of the clauses involved is a single literal l,by this resolution rule all occurrences of the negation of l in all other clauses may be removed.Moreover,all other clauses containing l then may be ignored.Eliminating all occurrences of l and its negation in this way is called unit resolution.We call a resolution proof search system reasonable if it starts with doing unit resolution as long as there is a clause consisting of a single literal.All practical resolution proof search systems are reasonable.In order to apply resolution on arbitrary formulas,these formulas mustfirst be translated to CNF.This can be done in linear time maintaining satisfiability using the Tseitin transfor-mation[13].A disadvantage of this transformation is the introduction of new variables,but it is well-known that a transformation to CNF without the introduction of new variables is necessarily exponential.For instance,it is not difficult to prove that for(···((p1↔p2)↔p3)······↔p n)every clause in a CNF contains either p i or¬p i for every i.Since one such clause of n literals causes only one zero in the truth table of the formula,the full CNF contains2n−1 of these clauses to obtain all2n−1zeros in its truth table.Hence without the introduction of new variables every CNF of this formula is of exponential size.More general for every biconditional formulaφwithout the introduction of new variables every CNF consists of at least2αodd(φ)−1clauses each consisting of at leastαodd(φ)literals.The Tseitin transformation works as follows.Given a formulaφ.Every sub-formulaψof φnot being a proposition letter is assigned a new letter pψ.Now the Tseitin transformation ofφconsists of•the single literal pφ;•the conjunctive normal form of pψ↔(pψ1⋄pψ2)for every subtermψofφof the shape ψ=ψ1⋄ψ2for a binary operator⋄;•the conjunctive normal form of pψ↔¬pψ1for every subtermψofφof the shape ψ=¬ψ1.It is easy to see that this set of clauses is satisfiable if and only ifφis satisfiable.Moreover, every clause consists of at most three literals,and the number of clauses is linear in the size of the original formulaφ.It is not difficult to see that after applying the Tseitin transformation to a CNF,by a number of resolution steps linear in the size of the CNF,the original CNF can be re-obtained. By a resolution proof for an arbitrary formula we mean a resolution proof after the Tseitin transformation has been applied.We now give a construction of strings S n in which all letters occur exactly twice by which ¬[S n]is a contradiction,and for which we prove that every resolution proof of¬[S n]is very long.Although the construction is somewhat involved,we think that simpler constructions do not suffice.In[16]for instance it was proved that¬[p1,p2,...,p n,p1,p2,...,p n]admits a resolution proof that is quadratic in n.For a string S and a label i we write lab(S,i)for the string obtained from S by replacing every symbol p by a fresh symbol p i.For a string S of length n∗2n we write ins(n,S)for the string obtained from S by inserting the symbol i after the(i∗n)-th symbol for i=1,2,...,n. We defineS1=1,1,andS n+1=ins(n,lab(S n,0)),ins(n,lab(S n,1)),for n>0.For instance,we haveS1=1,1 ,S2=10,1,10,2 ,11,1 ,11,2 ,S3=100,10,1,101,21,2,111,11,3.,111,21,4,101,11,1,100,20,2,110,10,3,110,20,4Clearly S n is a string of length n∗2n over n∗2n−1symbols each occurring exactly twice.The string S n can be considered to consist of2n consecutive groups of n symbols,called n-groups. In the examples S1,S2and S3above the n-groups are under-braced.Write g n,k to be the k-th n-group in S n,for n>1and1≤k≤2n.Lemma5.1.Let A⊆{1,2,...,2n}for any n>0.Then there are at least min(#A,2n−#A) pairs(k,k′)such that k,k′∈{1,2,...,2n},k∈A,k′∈A and g n,k and g n,k′have a common symbol.Proof.We apply induction on n;for n=1the lemma clearly holds.Let m0=#{k∈A|k≤2n−1}and m1=#{k∈A|k>2n−1}.Say that(k,k′)is a matching pair if k∈A, k′∈A and g n,k and g n,k′have a common symbol.If k,k′≤2n−1then by construction g n,k and g n,k′have a common symbol if g n−1,k and g n−1,k′have a common symbol.If k,k′>2n−1 then by construction g n,k and g n,k′have a common symbol if g n−1,k−2n−1and g n−1,k′−2n−1 have a common symbol.Hence by induction hypothesis there are at least min(m0,2n−1−m0) matching pairs(k,k′)with k,k′≤2n−1and at least min(m1,2n−1−m1)matching pairs(k,k′) with k,k′>2n−1.Since by construction g n,k and g n,k+2n−1have a common symbol for every k=1,2,...,2n−1,there are at least|m0−m1|matching pairs(k,k′)with|k−k′|=2n−1. Hence the total number of matching pairs is at least|m0−m1|+min(m0,2n−1−m0)+min(m1,2n−1−m1).A simple case analysis shows that this is at least min(m0+m1,2n−m0−m1)=min(#A,2n−#A).2 Essentially this lemma states the well-known fact that for any set A of vertices of an n-dimensional cube there are at least min(#A,2n−#A)edges for which one end is in A and the other is not.It is applied in the next lemma stating a lower bound on connections between separate elements of S n rather than connections between n-groups.Lemma5.2.Let n>0and let B⊆{1,2,...,n∗2n}.Let X⊆{1,2,...,n∗2n}2consist of the pairs(i,j)for which i∈B and j∈B and for which either|i−j|=1or the i-th element of S n is equal to the j-th element of S n.Then#X≥min(#B,n∗2n−#B)2n.Proof.Assume that#B≤n∗2n−1,otherwise replace B by its complement.Let A be the set of numbers k∈{1,...,2n}for which all elements of the corresponding n-group g n,k correspond to elements of B,i.e.,{(k−1)∗n+1,...,k∗n}⊆B.Let m1=#A.Let m2 be the number of n-groups for which none of the elements correspond to elements of B,i.e., m2=#{k∈{1,...,2n}|{(k−1)∗n+1,...,k∗n}∩B=∅}.Let m3be the number of remaining n-groups,i.e.,n-groups containing elements corresponding to both elements of B and outside B.Clearly n∗m1≤#B≤n∗(m1+m3).Each of the m3remaining groups gives rise to a pair(i,j)∈X for which|i−j|=1.Hence#X≥m3.Now assume that m1>m3.Since n∗m1≤#B≤n∗2n−1we have m1=#A≤2n−1. By Lemma5.1we obtain at least m1pairs(k,k′)such that k∈A,k′∈A and g n,k and g n,k′have a common symbol.For at least m1−m3of the corresponding n-groups g n,k′none of the elements correspond to elements of B.Since g n,k and g n,k′have a common symbol for every corresponding pair(k,k′)this gives rise to at least m1−m3pairs(i,j)∈X for which the i-th element of S n is equal to the j-th element of S n.Hence in case m1>m3we conclude #X≥m3+(m1−m3)=m1.We conclude#X≥max(m3,m1)≥m1+m32≥#B2n.2Theorem5.3.Every resolution proof of¬[S n]contains2Ω(2n/n)resolution steps.。
