ccna6.0第一学期第2章答案
ccna第二章答案
1. Which statements correctly identify the role of intermediary devices in the network? (Choose three.)determine pathways for data 确定数据通路initiate data communicationsretime and retransmit data signals 重分发originate the flow of datamanage data flows 管理数据final termination point for data flow2. Select the statements that are correct concerning network protocols. (Choose three.)define the structure of layer specific PDU'sdictate how to accomplish layer functionsoutline the functions necessary for communications between layers limit the need for hardware compatibilityrequire layer dependent encapsulationseliminate standardization among vendors3. What are two functions of encapsulation? (Choose two.)tracks delay between end devicesenables consistent network paths for communicationallows modification of the original data before transmissionidentifies pieces of data as part of the same communicationensures that data pieces can be directed to the correct receiving end device4. What is a primary function of the trailer information added by the data link layer encapsulation?supports error detection 支持错误检测‘ensures ordered arrival of dataprovides delivery to correct destinationidentifies the devices on the local networkassists intermediary devices with processing and path selection5. Which statements correctly identify the role of intermediary devices in the network? (Choose three.)determine pathways for datainitiate data communicationsretime and retransmit data signalsoriginate the flow of datamanage data flowsfinal termination point for data flow6. What is a PDU?corruption of a frame during transmissiondata reassembled at the destinationretransmitted packets due to lost communicationa layer specific encapsulation 一个具体的封装层7. Which characteristic correctly refers to end devices in a network?manage data flowsoriginate data flow 原数据流retime and retransmit data signalsdetermine pathways for data8.Refer to the exhibit. "Cell A" at IP address 10.0.0.34 has established an IP session with "IP Phone 1" at IP address 172.16.1.103. Based upon the graphic, which device type best describes the function of wireless device "Cell A?"the destination devicean end devicean intermediate devicea media device9.Refer to the exhibit. Which three labels correctly identify the network types for the network segments that are shown?(Choose three.)Network A -- WANNetwork B -- WANNetwork C -- LANNetwork B -- MANNetwork C -- WANNetwork A -- LAN10. Which three statements best describe a Local Area Network (LAN)? (Choose three.)A LAN is usually in a single geographical area.The network is administered by a single organization.The connection between segments in the LAN is usually through a leased connection.The security and access control of the network are controlled by a service provider.A LAN provides network services and access to applications for users within a common organization.Each end of the network is generally connected to a Telecommunication Service Provider (TSP).11.Refer to the exhibit. Which networking term describes the data interleaving process represented in the graphic?pipingPDUstreamingmultiplexingencapsulation12. What is the primary purpose of Layer 4 port assignment?to identify devices on the local mediato identify the hops between source and destinationto identify to the intermediary devices the best path through the network to identify the source and destination end devices that are communicating to identify the processes or services that are communicating within the end devices13. What device is considered an intermediary device?1.file serve2.IP phone ptop 4.printer 5.switch14.Refer to the exhibit. Which term correctly identifies the device type that is included in the area B? sourceendtransferintermediary 中间设备15.Refer to the exhibit. What type of network is shown?WANMANLANWLAN16. Which layer encapsulates the segment into packets?physicaldata linknetwork 网络层封装的是数据包transport17. What can be identified by examining the network layer header?the destination device on the local mediathe destination host address 网络层头部封装目的主机的地址the bits that will be transferred over the mediathe source application or process creating the data18. What is the purpose of the TCP/IP Network Access layer?path determination and packet switchingdata presentationreliability, flow control, and error detectionnetwork media control 接入层控制网络媒体the division of segments into packets19. During the encapsulation process, what occurs at the data link layer? No address is added.The logical address is added.The physical address is added. 数据链路层添加一个物理地址The process port number is added.20.Refer to the exhibit. Which set of devices contains only end devices? A, C, DB, E, G, HC, D, G, H, I, JD, E, F, H, I, JE, F, H, I, J21. What is the proper order of the layers of the OSI model from the highest layer to the lowest layer?4physical, network, application, data link, presentation, session, transportapplication, physical, session, transport, network, data link, presentationapplication, presentation, physical, session, data link, transport, networkapplication, presentation, session, transport, network, data link, physicalpresentation, data link, session, transport, network, physical, application22. Which two layers of the OSI model have the same functions as the TCP/IP model Network Access Layer? (Choose two.)34NetworkTransportPhysicalData Link TCP/IP 工作在第一层和第二层Session。
ccna第二章练习答案.docx
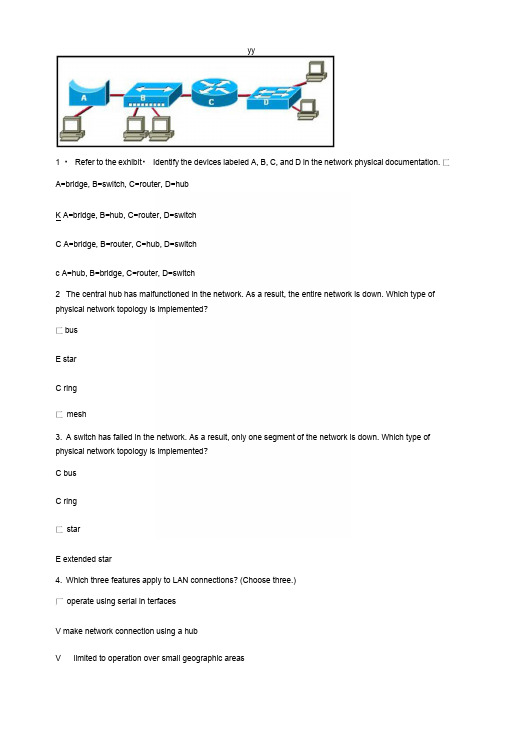
yy1 ・ Refer to the exhibit・ Identify the devices labeled A, B, C, and D in the network physical documentation. 匚A=bridge, B=switch, C=router, D=hubK A=bridge, B=hub, C=router, D=switchC A=bridge, B=router, C=hub, D=switchc A=hub, B=bridge, C=router, D=switch2 The central hub has malfunctioned in the network. As a result, the entire network is down. Which type of physical network topology is implemented?匚busE starC ring匚mesh3. A switch has failed in the network. As a result, only one segment of the network is down. Which type of physical network topology is implemented?C busC ring匚starE extended star4. Which three features apply to LAN connections? (Choose three.)厂operate using serial in terfacesV make network connection using a hubV limited to operation over small geographic areas厂 provide part-time connectivity to remote servicesV typically operate under local administrative control厂provide lower bandwidth services compared to WANs5. What is one advantage of defining network communication by the seven layers of the OSI model? 【:It in creases the ban dwidth of a n etwork.E It makes networking easier to learn and understand・It eliminates many protocol restrictions.匚It increases the throughput of a network.c It reduces the need for testing network connectivity.6. What makes it easier for different networking vendors to design software and hardware that willin teroperate?E OSI modelc proprietary desig ns匚IP addressing schemec standard logical topologies匚standard physical topologies7. Which term describes the process of adding headers to data as it moves down OSI layers?匚division匚encoding匚separation匚segmentationE encapsulation8. What is the term used to describe the transport layer protocol data unit?匚bits c packetsE segments匚framesc data streams9. Which of the following are layers of the TCP/IP model? (Choose three.)▽ Applicati onr PhysicalV Internet0 Network Access厂Prese ntation10. Which of the following are data link layer encapsulation details? (Choose two.)0 A header and trailer are added・厂Data is con verted into packets ・V Packets are packaged into frames・厂Frames are divided into segments.厂Packets are changed into bits for Internet travel.11. Which layer of the OSI model provides network services to processes in electronic mail and file transfer programs?匚data link匚transport匚n etworkE application12. Which two features apply to WAN connections? (Choose two.)V operate using serial interfacesP make network connection using a hub厂limited to operation over small geographic areasI- typically operate under local administrative control▽provide lower bandwidth services compared to LANs13. Which of the following are ways that bandwidth is commonly measured? (Choose three.)厂GHzps▽kbpsV Mbps厂Nbps厂MHzpsV Gbps14. Refer to the following list. Choose the correct order of data encapsulation when a device sends information. segments bits packetsdata frames匚1 -3-5-4-2C 2- 1-3-5-4C 2-4-3-5-1匚4-3-1-2-5E 4-1 -3-5-2C 3-5-1-2-415. Which of the following are factors that determine throughput? (Choose two.)厂types of passwords used on servers厂type of Layer 3 protocol usedV n etwork topologywidth of the network cable0 number of users on the network16. Refer to the exhibit・ Which column shows the correct sequenee of OSI model layers?E D17. Which layer of the OSI model provides connectivity and path selection between two end systems where routing occurs?c physical layer匚data link layerE network layer匚transport layer18. Which best describes the function of the physical layer?E Defines the electrical and functional specifications for the link between end systems・匚Provides reliable transit of data across a physical link.匚Provides connectivity and path selection between two end systems・匚Concerned with physical addressing, network topology and media access.。
ccna第二学期练习答案
ERouting Chapter 1 - CCNA Exploration: 路由协议和概念 (版本1口令可用于限制对 Cisco IOS 所有或部分内容的访问。
请选择可以用口令保护的模式和接口。
(选择三项。
)VTY 接口控制台接口特权执行模式2路由器从相连的以太网接口收到消息后,会更改哪项报头地址,再将消息从另一个接口发送出去第 2 层源地址和目的地址3请参见图示。
网络管理员已经为路由器连接到直连网络的接口配置了如图所示的 IP 地址。
从路由器 ping 相连网络上的主机口之间相互 ping 都会遭到失败。
此问题最可能的原因是什么必须使用no shutdown命令启用接口。
4请参见图示。
主机 A ping 主机 B。
当 R4 收到对以太网接口的 ping 时,哪两块报头信息包括在内(选择两项。
)目的 IP 地址:目的 MAC 地址:5网络管理员刚把新配置输入 Router1。
要将配置更改保存到 NVRAM,应该执行哪一条命令Router1# copy running-config startup-config6您需要配置图中所示的串行连接,必须在 Sydney 路由器上发出以下哪条配置命令才能与 Melbourne 站点建立连接(选择三Sydney(config-if)# ip addressSydney no shutdownSydney(config-if)# clock rate 560007请参见图示。
从路由器的运行配置输出可得出什么结论显示的命令决定了路由器的当前运行情况。
8请参见图示。
在主机 2 连接到 LAN 上的交换机后,主机 2 无法与主机 1 通信。
导致此问题的原因是什么主机 1 和主机 2 位于不同的网络中。
9输入以下命令的作用是什么R1(config)# line vty 0 4R1(config-line)# password check123R1(config-line)# login设置通过 Telnet 连接该路由器时使用的口令10以下哪一项正确描述了路由器启动时的顺序加载 bootstrap、加载 IOS、应用配置11加载配置文件时的默认顺序是怎样的NVRAM、TFTP、CONSOLE12请参见图示。
CCNA 640 802 第六版 笔记

目录Chapter 1 Internetworking(网际互联) (2)Exam Essentials (2)Chapter 2 Introduction to TCP/IP (4)Exam Essentials (4)Chapter 3 Subnetting,VLSM, Troubleshooting TCP/IP (8)Exam Essentials (8)Chapter 4 Cisco’s Internetworking Operating System (IOS) and Security Device Manager (SDM) (10)Exam Essentials (10)Chapter 5 Managing a Cisco Internetwork (12)Exam Essentials (12)Chapter 6 IP Routing (21)Exam Essentials (21)Chapter 7 Enhanced IGRP (EIGRP) and Open Shortest Path First (OSPF) (26)Exam Essentials (26)Chapter 8 Layer 2 Switching and Spanning Tree Protocol (STP) (32)Exam Essentials (32)Chapter 9 V irtual LANs_虚拟局域网(VLANs) (37)Exam Essentials (37)Chapter 10 Security (42)Exam Essentials (42)Chapter 11 Network Address Translation (NA T) (46)Exam Essentials (46)Chapter 12 Cisco’s Wireless Technologies (48)Exam Essentials (48)Chapter 13 Internet Protocol V ersion 6(IPv6) (51)Exam Essentials (51)Chapter 14 Wide Area Networks (54)Exam Essentials (54)Chapter 1 Internetworking(网际互联)Exam Essentials①Remember the possible causes of LAN traffic congestion.②Understand the difference between a collision domain and a broadcast domain.③Understand the difference between a hub, a bridge, a switch, and a router.④Remember the difference between connection-oriented and connectionlessnetwork services.⑤Remember the OSI layers.⑥Remember the types of Ethernet cabling and when you would use them.⑦Understand how to connect a console cable from a PC to a router and start HyperTerminal.⑧Remember the three layers in the Cisco three-layer model.把一个大的网络划分为一些小的网络就称为网络分段,这些工作由路由器,交换机和网桥来完成。
CCNA学习指南第2章复习题中英文翻译版

CCNA学习指南第2章复习题中英文翻译版1. What are the decimal and hexadecimal equivalents of the binary number 10011101?(Choose two.)1. 二进制数10011101等效的十进制和十六进制数分别是多少?(选择两项。
)A. 159B. 157C. 185D. 0x9DE. 0xD9F. 0x1592. Which of the following allows a router to respond to an ARP request that is intended for a remote host?2. 下列哪一项允许路由器对远端主机的ARP请求做出响应?A. Gateway DP网关DPB. Reverse ARP (RARP)反向ARPC. Proxy ARP代理ARPD. Inverse ARP逆向ARPE. Address Resolution Protocol (ARP)地址解析协议3. You want to implement a mechanism that automates the IP configuration, including IP address, subnet mask, default gateway, and DNS information. Which protocol will you use to accomplish this?3. 你想实现自动IP配置,包括IP地址,子网掩码,默认网关和DNS信息。
你应该使用什么协议来完成这?A. SMTP简单邮件传输协议B. SNMP简单网络管理协议C. DHCP动态主机控制协议D. ARP地址解析协议4. What protocol is used to find the hardware address of a local device?4. 什么协议用来找本地设备的硬件地址?A. RARPB. ARPC. IPD. ICMPE. BootP5. Which of the following are layers in the TCP/IP model? (Choose three.)5. 下列哪些层属于TCP/IP模型?(选择三项。
思科第一学期第二章章节测验答案
1.下列哪些陈述正确指出了中间设备在网络中的作用?(选择三项)•确定数据传输路径•发起数据通信•重新定时和重新传输数据信号•发送数据流•管理数据流•数据流最后的终止点2.请选择关于网络协议的正确陈述。
(选择三项。
)•定义特定层PDU 的结构•规定实现协议层功能的方式•概述层与层之间通信所需的功能•限制了对硬件兼容性的需要•需要取决于协议层的封装过程•杜绝厂商之间的标准化3.封装的两个功能是什么?(选择两项)•跟踪终端设备之间的延迟•为通信提供统一的网络路径•在传输前可以修改原始数据•标识属于同一通信的数据片段•确保数据片段可以转发到正确的接收端设备4.数据链路层封装添加的报尾信息有何主要功能?•支持差错校验•确保数据按照顺序到达•确保送达正确目的•标识本地网络中的设备•帮助中间设备进行处理和路径选择5.OSI 模型哪两层的功能与TCP/IP 模型的网络接入层相同?(选择两项)•网络层•传输层•物理层•数据链路层•会话层6.什么是PDU?•传输期间的帧损坏•在目的设备上重组的数据•因通信丢失而重新传输的数据包•特定层的封装7.以下哪种特征正确代表了网络中的终端设备?•管理数据流•发送数据流•重新定时和重新传输数据信号•确定数据传输路8.请参见图示。
IP 地址为10.0.0.34 的“手机A”已经与IP 地址为172.16.1.103 的“IP电话1”建立了IP 会话。
请根据图示回答,下列哪个设备类型是对无线设备“手机A”功能的最准确描述?•目的设备•终端设备•中间设备•介质设备9.请参见图示。
下列哪三个标签正确标识了图示网段的网络类型?(选择三项)•网络 A -- WAN•网络 B -- WAN•网络 C -- LAN•网络 B -- MAN•网络 C -- WAN•网络 A -- LAN10.下列哪三项陈述是对局域网(LAN) 最准确的描述?(选择三项)•LAN 通常位于一个地域内。
•此类网络由由一个组织管理。
(完整版)ccna1章节与期末答案

第一章:正确答案:2.4.5•解析:由于不需要使用网络设备和专用服务器,对等网络易于创建,复杂性更低,且成本更少。
而且对等网络也没有集中管理。
这种网络安全性更低,不可扩展,而且那些同时充当客户端和服务器的设备可能性能更差正确答案:1解析:正确答案: 3.5解析:选择网络介质的条件包括:所选介质可以成功传送信号的距离、要安装所选介质的环境、必须传输的数据量和速度以及介质和安装的成本。
正确答案:3和4解析:终端设备上的应用程序可以生成数据,更改数据内容并且负责启动封装过程。
正确答案:1和4解析:终端设备会发出通过网络传输的数据。
中间设备会在链路发生故障时通过备用路径传输数据,并且会过滤数据传输以增强安全性。
网络介质提供网络消息的传输通道。
正确答案:4解析:外联网是公司外部的人或企业合作伙伴访问数据的网络区域。
内部网只描述通常仅供内部人员访问的网络区域。
当设备连接到有线网络时,有线LAN 会受BYOD(自带设备)影响。
使用大学无线LAN 的设备多为平板电脑和智能手机。
大学生主要使用无线WAN 来访问他们的手机运营商网络。
.正确答案:2解析:由于通过Internet 可以联系在线供应商,所以家庭用户通过Internet 进行网上购物。
内联网基本上是仅供内部使用的局域网。
外联网是外部合作伙伴访问组织内部特定资源的网络。
家庭用户并不一定使用LAN 来访问Internet。
例如,PC 可以通过调制解调器直接连接到ISP。
正确答案:1解析:内部网这个术语用于表示一个组织的私有局域网和广域网连接。
内部网的设计旨在仅允许该组织的成员、员工或其他获得授权的人员进行访问。
正确答案:2和4解析:电缆和DSL 均能实现高带宽、始终联网,并提供到主机计算机或LAN 的以太网连接。
10正确答案:2和3解析:移动电话连接需要使用移动电话网络。
卫星连接通常用于家庭或企业外部不便使用物理布线的位置。
11正确答案:2解析:当对网络资源的请求超出了可用容量时,网络就会变得拥堵。
CCNA第一学期Finalexam考试英文版答案

CCNA第一学期Finalexam考试英文版答案(R&S.)C 1A medium-sized business is researching available options for connecting to the Internet.Thecompany is looking for a high speed option with dedicated, symmetric access.Whichconnection type should the company choose?DSLdialupsatelliteleased linecable modem2What is the purpose of having a converged network?to provide high speed connectivity to all end devicesto make sure that all types of data packets will be treated equallyto achieve fault tolerance and high availability of data network infrastructure devicesto reduce the cost of deploying and maintaining thecommunication infrastructure3What characteristic of a network enables it to quickly grow to support new users andapplications without impacting the performance of the service being delivered to existing users?reliabilityscalabilityquality of serviceaccessibility4Which connection provides a secure CLI session with encryption to a Cisco switch?a console connectionan AUX connectiona Telnet connectionan SSH connection5A network technician is attempting to configure an interface by entering the followingcommand:SanJose(config)#ip address192.168.2.1255.255.255.0.The command isrejected by the device.What is the reason for this? The command is being entered from the wrong mode of operation.The command syntax is wrong.The subnet mask information is incorrect.The interface is shutdown and must be enabled before the switch will accept the IP address.6After several configuration changes are made to a router, the copy running-configurationstartup-configuration command is issued.Where will the changes be stored?flashROMNVRAMRAMthe configuration registera TFTP server7Refer to the exhibit.From global configuration mode,an administrator is attempting to create a message-of-the-day banner by using thecommand banner motd V Authorized access only!Violators will be prosecuted!V When users log in using Telnet,the banner does not appear correctly.What is the problem? The banner message is too long.The delimiting character appears in the banner message.The symbol“!”signals the end of a banner message.Message-of-the-day banners will only appear when a user logs in through the console port.8What are three characteristics of an SVI?(Choose three.) It is designed as a security protocol to protect switch ports.It is not associated with any physical interface on a switch.It is a special interface that allows connectivity by different types of media.It is required to allow connectivity by any device at any location.It provides a means to remotely manage a switch.It is associated with VLAN1by default.9A technician configures a switch with these commands: SwitchA(config)#interface vlan1SwitchA(config-if)#ip address192.168.1.1255.255.255.0 SwitchA(config-if)#no shutdownWhat is the technician configuring?Telnet accessSVIpassword encryptionphysical switchport access10In computer communication,what is the purpose of message encoding?to convert information to the appropriate form for transmissionto interpret informationto break large messages into smaller framesto negotiate correct timing for successful communication11What protocol is responsible for controlling the size of segments and the rate at whichsegments are exchanged between a web client and a web server?TCPIPHTTPEthernet12What are two benefits of using a layered network model? (Choose two.)It assists in protocol design.It speeds up packet delivery.It prevents designers from creating their own model.It prevents technology in one layer from affecting other layers.It ensures a device at one layer can function at the next higher layer.13What is the process of dividing a data stream into smaller pieces before transmission?segmentationencapsulationencodingflow control14When IPv4addressing is manually configured on a web server,which property of the IPv4configuration identifies the network and host portion for an IPv4address?DNS server addresssubnet maskdefault gatewayDHCP server address15A network administrator is troubleshootingconnectivity issues on a ing a tester,the administrator notices that the signals generated by the server NIC are distorted and not usable.In which layer of the OSI model is the error categorized?presentation layernetwork layerphysical layerdata link layer16A network engineer is measuring the transfer of bits across the company backbone for amission critical database application.The engineer notices that the network throughputappears lower than the bandwidth expected.Which three factors could influence thedifferences in throughput?(Choose three.)the amount of traffic that is currently crossing the networkthe sophistication of the encapsulation method applied to the datathe type of traffic that is crossing the networkthe latency that is created by the number of network devices that the data is crossingthe bandwidth of the WAN connection to the Internetthe reliability of the gigabit Ethernet infrastructure of the backbone17Which type of UTP cable is used to connect a PC to a switch port?consolerollovercrossoverstraight-through18What is a characteristic of the LLC sublayer?It provides the logical addressing required that identifies the device.It provides delimitation of data according to the physical signaling requirements of the medium.It places information in the frame allowing multiple Layer 3protocols to use the same network interface and media.It defines software processes that provide services to the physical layer.19What are the three primary functions provided by Layer 2data encapsulation?(Choosethree.)error correction through a collision detection methodsession control using port numbersdata link layer addressingplacement and removal of frames from the mediadetection of errors through CRC calculationsdelimiting groups of bits into framesconversion of bits into data signals20What will a host on an Ethernet network do if it receives a frame with a destination MACaddress that does not match its own MAC address?It will discard the frame.It will forward the frame to the next host.It will remove the frame from the media.It will strip off the data-link frame to check the destination IP address.21What are two actions performed by a Cisco switch? (Choose two.)building a routing table that is based on the first IP address in the frame headerusing the source MAC addresses of frames to build and maintain a MAC address tableforwarding frames with unknown destination IP addresses to the default gatewayutilizing the MAC address table to forward frames via the destination MAC addressexamining the destination MAC address to add new entries to the MAC address table22What are two examples of the cut-through switching method?(Choose two.)store-and-forward switchingfast-forward switchingCRC switchingfragment-free switchingQOS switching23Refer to the exhibit.If host A sends an IP packet to host B,what will the destination address be in the frame when it leaves host A?DD:DD:DD:DD:DD:DD172.168.10.99CC:CC:CC:CC:CC:CC172.168.10.65BB:BB:BB:BB:BB:BBAA:AA:AA:AA:AA:AA24What are two services provided by the OSI network layer?(Choose two.)performing error detectionrouting packets toward the destinationencapsulating PDUs from the transport layerplacement of frames on the mediacollision detection25What information is added during encapsulation at OSI Layer3?source and destination MACsource and destination application protocolsource and destination port numbersource and destination IP address26What are two functions of NVRAM?(Choose two.)to store the routing tableto retain contents when power is removedto store the startup configuration fileto contain the running configuration fileto store the ARP table27Refer to the exhibit.The network administrator for a small advertising company has chosen to use the192.168.5.96/27 network for internal LAN addressing.As shown in the exhibit,a static IP address is assigned to the company web server.However,the web server cannot access the Internet.The administrator verifies that local workstations with IP addresses that are assigned by a DHCP server can access the Internet,and the web server is able to ping local workstations.Which component is incorrectly configured?subnet maskDNS addresshost IP addressdefault gateway address28Why does a Layer3device perform the ANDing process on a destination IP address andsubnet mask?to identify the broadcast address of the destination networkto identify the host address of the destination hostto identify faulty framesto identify the network address of the destination network29What are the three ranges of IP addresses that are reserved for internal private use?(Choosethree.)10.0.0.0/864.100.0.0/14127.16.0.0/12172.16.0.0/12192.31.7.0/24192.168.0.0/1630Which three addresses are valid public addresses? (Choose three.)198.133.219.17192.168.1.24510.15.250.5128.107.12.117192.15.301.24064.104.78.22731What type of IPv6address is FE80::1?loopbacklink-localmulticastglobal unicast32Refer to the exhibit.On the basis of the output,which two statements about network connectivity are correct? (Choose two.)There is connectivity between this device and the device at192.168.100.1.The connectivity between these two hosts allows for videoconferencing calls.There are4hops between this device and the device at 192.168.100.1.The average transmission time between the two hosts is2 milliseconds.This host does not have a default gateway configured.33Which subnet would include the address192.168.1.96as a usable host address?192.168.1.64/26192.168.1.32/27192.168.1.32/28192.168.1.64/2934How many hosts are addressable on a network that has a mask of255.255.255.248?268141625435Which statement is true about variable-length subnet masking?Each subnet is the same size.The size of each subnet may be different,depending on requirements.Subnets may only be subnetted one additional time.Bits are returned,rather than borrowed,to create additional subnets.36Refer to the exhibit.Consider the IP address of 192.168.10.0/24that has been assigned to a high school building.The largest network in this building has100 devices.If192.168.10.0is the network number for the largest network,what would be the network number for thenext largest network,which has40devices?192.168.10.0192.168.10.128192.168.10.192192.168.10.224192.168.10.24037In what two situations would UDP be the preferred transport protocol over TCP?(Choosetwo.)when applications need to guarantee that a packet arrives intact,in sequence,and unduplicatedwhen a faster delivery mechanism is neededwhen delivery overhead is not an issuewhen applications do not need to guarantee delivery of the datawhen destination port numbers are dynamic38What important information is added to the TCP/IPtransport layer header to ensurecommunication and connectivity with a remote network device?timing and synchronizationdestination and source port numbersdestination and source physical addressesdestination and source logical network addresses39What is the TCP mechanism used in congestion avoidance? three-way handshakesocket pairtwo-way handshakesliding window40Which three statements characterize UDP?(Choose three.)UDP provides basic connectionless transport layer functions.UDP provides connection-oriented,fast transport of data at Layer 3.UDP relies on application layer protocols for error detection.UDP is a low overhead protocol that does not provide sequencing or flow control mechanisms.UDP relies on IP for error detection and recovery.UDP provides sophisticated flow control mechanisms.41Which two tasks are functions of the presentation layer? (Choose two.)compressionaddressingencryptionsession controlauthentication42Which two protocols operate at the highest layer of the TCP/IP protocol stack?(Choose two.)DNSEthernetIPPOPTCPUDP43Which two roles can a computer assume in a peer-to-peer network where a file is beingshared between two computers?(Choose two.)clientmasterserverslavetransient44What is the function of the HTTP GET message?to request an HTML page from a web serverto send error information from a web server to a web clientto upload content to a web server from a web clientto retrieve client email from an email server using TCP port11045A wireless host needs to request an IP address.What protocol would be used to process therequest?FTPHTTPDHCPICMPSNMP46When planning for network growth,where in the network should packet captures take place toassess network traffic?on as many different network segments as possibleonly at the edge of the networkbetween hosts and the default gatewayonly on the busiest network segment47When applied to a router,which command would help mitigate brute-force password attacksagainst the router?exec-timeout30service password-encryptionbanner motd$Max failed logins=5$login block-for60attempts5within6048Refer to the exhibit.An administrator is testing connectivity to a remote device with the IP address10.1.1.1.What does the output of this command indicate?Connectivity to the remote device was successful.A router along the path did not have a route to the destination.A ping packet is being blocked by a security device along the path.The connection timed out while waiting for a reply fromthe remote device.。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
1 操作系统内核的作用是什么?
它会提供允许用户请求特定任务的用户界面。
内核将硬件驱动程序与计算机底层的电子元件链接。
它是一种可实现思科设备的初始配置的应用程序。
内核会调配硬件资源以满足软件要求。
Option 4
2 网络管理员与交换机建立远程 CLI 连接对其实施管理时,需要确保用户 ID、密码和会话内容的保密性。
应当选择哪种访问方法?
Telnet
控制台
AUX
SSH
Option 4
3 当在安全环境下执行初始配置时,下列哪个程序可用来访问 Cisco 2960 交换机?
使用 Telnet 通过网络远程访问交换机。
使用控制台端口从 PC 的串行接口或 USB 接口本地访问交换机。
使用安全外壳协议通过网络远程访问交换机。
使用 AUX 端口从 PC 的串行接口或 USB 接口本地访问交换机。
Option 2
4 哪个命令或组合键让用户返回命令层级中的上一级?
end
exit
Ctrl-Z
Ctrl-C
Option 2
5 某台具有有效操作系统的路由器包含在 NVRAM 中存储的配置文件。
配置文件中包含一个使能加密密码,但没有控制台密码。
当该路由器启动时,将显示哪种模式?
全局配置模式
设置模式
特权 EXEC 模式
用户 EXEC 模式
Option 4
6 Cisco IOS CLI 的上下文相关帮助功能为用户提供了哪两项功能?(请选择两项。
)
当提交了错误命令时显示错误消息
显示当前模式中的所有可用命令列表
允许用户使用 Tab 键完成缩写命令的其余部分
确定已输入命令的可用选项、关键字或参数
选择用于完成任务的最佳命令
Option 2 and Option 4 are correct.
7 show startup-config命令将显示哪些信息?
复制到 RAM 中的 IOS 映像
ROM 中的引导程序
RAM 中当前运行的配置文件的内容
NVRAM 中保存的配置文件的内容
Option 4
8 为什么必须配置设备的主机名?
设置了主机名之后,思科路由器或交换机才会开始运行
主机名必须在其他所有参数之前配置
用于在远程访问过程(SSH 或 Telnet)中识别设备
用于通过控制台端口对设备进行本地访问
Option 3
9 下列哪两个主机名遵循了 Cisco IOS 设备的命名约定指南?(选择两项。
)
Branch2!
RM-3-Switch-2A4
Floor(15)
HO Floor 17
SwBranch799
Option 2 and Option 5 are correct.
10 service password-encryption 命令如何增强思科路由器和交换机上的密码安全?
它在密码通过网络发送时对其进行加密。
它将对存储在路由器或交换机配置文件中的密码进行加密。
它要求用户键入加密密码以获得对路由器或交换机的控制台访问。
它要求在通过 Telnet 远程连接路由器或交换机时使用加密密码。
Option 2
11 请参见图示。
网络管理员正在交换机 SW1 上配置 MOTD。
此命令的用途是什么?
当用户访问交换机时显示一条消息
用于配置交换机 SW1,以便只有管理员组中的用户可通过 Telnet 访问 SW1
迫使管理员组的用户输入密码以进行身份验证
用于配置交换机 SW1,以便在用户输入 enable 命令时显示此消息
Option 1
12 在尝试解决网络故障时,技术人员多次更改当前的路由器配置文件。
这些更改未能解决问题,也未保存。
技术人员可以采取什么措施来放弃更改并处理NVRAM 中的文件?
发出reload命令,但不保存运行配置。
删除文件并重新启动设备。
关闭并重新打开终端仿真软件。
发出copy startup-config running-config命令。
Option 1
13 下列有关在 Cisco IOS 设备上运行配置文件的陈述,哪一项是正确的?
修改配置文件会立即对设备的操作造成影响。
配置文件存储在 NVRAM 中。
可使用erase running-config命令删除配置文件。
路由器重新启动时会自动保存配置文件。
Option 1
14 下列哪两项是思科设备上 RAM 的特征?(选择两项。
)
RAM 提供非易失性存储。
设备上活跃运行的配置存储在 RAM 中。
重新启动时 RAM 中的内容会丢失。
RAM 是思科交换机的组件,但不是思科路由器的组件。
RAM 可以存储多个版本的 IOS 和配置文件。
Option 2 and Option 3 are correct.
15 哪个接口允许远程管理第 2 层交换机?
AUX 接口
控制台端口接口
交换机虚拟接口
第一个以太网端口接口
Option 3
16 以下哪个接口是思科交换机上的默认 SVI?
FastEthernet 0/1
GigabitEthernet 0/1
VLAN 1
VLAN 99
Option 3
19 技术人员正在向 LAN 中添加新 PC。
在取出组件并完成所有连接后,技术人员启动了 PC。
操作系统加载后,技术人员打开了一个浏览器,检验 PC 是否能连接 Internet。
为什么 PC 无需任何其他配置就能连接到网络?
PC 无需任何其他信息即可在网络上运行。
PC 出厂时预配置了 IP 编址信息。
PC 预配置为使用 DHCP。
PC 使用了 DNS 来自动接收来自服务器的 IP 编址信息。
PC 虚拟接口与任何网络兼容。
Option 3
20 当用户对 PC 发出ping命令时,用户可以尝试确定什么?
在线路无流量的情况下,PC 上的 TCP/IP 协议栈是否运行正常
是否连接目的设备
流量到达目的地所用的路径
目的地处的设备类型
Option 2
21 请参见图示。
网络技术人员正在测试新网络中的连通性。
根据图中所示测试结果,技术人员连通了哪些设备?哪些设备没有连通?(选择两项。
)
connectivity: switch 2
connectivity: PC-D
connectivity: PC-B
no connectivity: switch 1
no connectivity: switch 2
no connectivity: PC-C
Option 1 and Option 6 are correct.
22 请参见图示。
根据show ip interface brief 命令的可见输出可得出哪三项结论?(选择三项。
)
已经配置了两个物理接口。
可以远程管理交换机。
一台设备与一个物理接口相连。
交换机上已经配置了密码。
两台设备与交换机相连。
已经配置默认 SVI。
Option 2, Option 3, and Option 6 are correct.。
