computer networking[English]课后题答案
计算机网络英文版习题答案

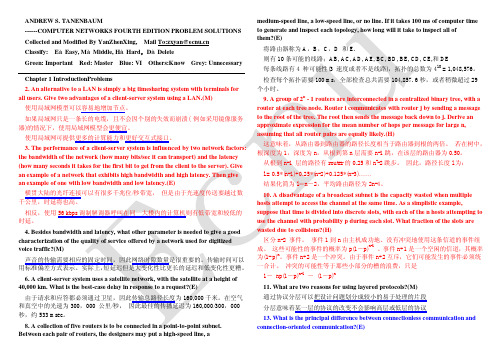
P63 #5 Consider sending a packet of F bits over a path of Q links. Each link transmits at R bps. The network is lightly loaded so that there are no queuing delays. Propagation delay is negligible.a.Suppose the network is a packet-switched virtual-circuit network. Denote the VC setup time by t s seconds. Suppose the sending layers add a total of h bits of header to the packet. How long does it take to send the file from source to destination?t s+[(F+h)/R]Qb.Suppose the network is a packet-switched datagram network and a connectionless service is used. Now suppose each packet has 2h bits of header. How long does it take to send the packet?[(F+2h)/R]Qc.Finally, suppose that the network is a circuit-switched network. Further suppose that the transmission rate of the circuit between source and destination is R bps. Assuming ts setup time and h bits of header appended to the packet, how long does it take to send the packet?t s+(F+h)/RP64 #6 This elementary problem begins to explore propagation delay and transmission delay, two central concepts in data networking. Consider two hosts, A and B, connected by a single link of rate R bps. Suppose that the two hosts are separated by m meters and suppose that the propagation speed along the link is s meters/sec. Host A sends a packet of size L bits to host B.[a] Express the propagation delay, d prop, in terms of m and s.[b] Determine the transmission time of the packet, d trans, in terms of L and R.[c] Ignoring processing and queueing delays, obtain an expression for the end-to-end delay.[d] Suppose Host A begins to transmit the packets at time t=0. At time t=d trans, where is the last bit of the packet?[e] Suppose d prop is greater than d trans. At time t=d trans, where is the first bit of the packet?[f] Suppose d prop is less than d trans. At time t=d trans, where is the first bit of the packet?[g] Suppose s=2.5 x 108, L=100 bits and R=28kbps. Find the distance m so that d prop = d trans.[a] d prop = m/s[b] d trans = L/R[c] end-to-end delay = d prop + d trans=m/s+L/R[d] The beginning position of the link.[e] On the channel between A and B.[f] On the host B.[g] m/s = L/R = > m = sL/R = > m = 892.86 kmP65 #10 Consider the queueing delay in a router buffer. Suppose that all packets are L bits, the transmission rate is R bps, and that N packets simultaneously arrive at the buffer every LN/R seconds. Find the average queueing delay of a packet (in terms of L, R and N). (Hint: The queueing delay for the first packet is zero; for the second packet L/R; for the third packet 2L/R. The Nth packet has already been transmitted when the second batch of packets arrives.)As the Nth packet has already been transmitted when the next batch of packets arrive, we only need to consider the delay for a single batch of packets.Average delay = Total delay / Number of packetsDelay for 1st packet = 0Delay for 2nd packet = L/RDelay for 3rd packet = 2L/R......Delay for Nth packet = (N-1)L/RTotal delay for N packets = (0 + 1 + 2 ... +(N-1) ) * (L/R)Using the formulas for sum of integer series, this can be written as: Total delay for N packets = (N-1) * (N/2) * (L/R)Therefore, average delay for N packets = ((N-1) * L) / 2RP170 #12 What is the difference between persistent HTTP with pipelining and persistent HTTP without pipelinning? Which of the two is used by HTTP/1.1?For the persistent connection without pipelining, the client issues a new request only when the previous has been received. In this case, the client experiences one RTT in order to request and receive each of the referenced objects.For the persistent connection with pipelining, the client issues a request as soon as it encounters a reference. It is possible for only RTT to be expended for all the referenced objects.P170 #14 Telnet into a Web server and send a multiline request message. Include in the request message theIf-modified-since: header line to force a response message with the 304 Not Modified status code.GET/somedir/exp.html HTTP/1.1Host: Connection: closeUser-agent: Mozilla/4.0If-Modified-Since: Thu, 30 May 2007 12:00:00 GMTAccept-language: frP172 #6 Suppose within your web browser you click on a link to obtain a web page. The IP address for the associated URL is not cached in your local host, so a DNS look-up is necessary to obtain the IP address. Suppose that n DNS servers are visited before your host receives the IP address from DNS; the successive visits incur an RTT (Round Trip Time) of RTT1, ... RTTn. Further suppose that the web page associated with the link contains exactly one object, consisting of a small amount of HTTP text. Let RTT0 denote the RTT between the local host and the remote server containing the object. Assuming zero transmission time of the object, how much time elapses from when the client clicks on the link until the client receives the object? (Hint: read pages 90 .. 93)Time to visit DNS servers and get IP address = RTT1 + RTT2 + ... + RTTnTime to establish TCP connection (SYN and SYNACK) = RTT0Time to send HTTP request and receive reply = RTT0Total time = 2 * RTT0 + (RTT1 + RTT2 + ... + RTTn)P171 #16 Suppose Alice with a Web-based e-mail account (such as Yahoo! Mail or Hotmail) sends a message to Bob, who accesses his mail from his mail server using POP3. Discuss how the message gets from Alice’s host to Bob’s host. Be sure to list the series of application-layer protocols that are used to move the message between the two hosts.The series of application-layer protocols: HTTP、SMTP、POP3Suppose that you send an e-mail message whose only data is a Microsoft Excel attachment. What might the header lines (including MIME lines) look like?From:***********To:***********Subject: helloMIME-Version: 1.0Content-Transfer-Encoding: base64Content-Type: Application/MS-ExcelP286 #5 Suppose host A sends two TCP segments back to back to host B over a TCP connection. The first segment has sequence number 90: the second has sequence number 110.a.How much data is in the first segment?a.20 bytesb.Suppose that the first segment is lost but the second segment arrives at B. In the acknowledgement that host B sends to host A, what will be the acknowledgement number?b.ACK90P291 #27 Consider the following plot of TCP window size as a function of time. (reproduced below for you) Assuming TCP Reno is the protocol experiencing the behavior shown above, answer the following questions. In all cases, you should provide a short discussion justifying your answer.a. Identify the intervals of time when TCP slow start is operating.b. Identify the intervals of time when TCP congestion avoidance is operating.c. After the 16th transmission round, is segment loss detected by a tripleduplicate ACK or by a timeout?d. After the 22nd transmission round, is segment loss detected by a triple duplicate ACK or by a timeout?e. What is the initial value of Threshold at the first transmission round?f. What is the value of Threshold at the 18th transmission round?g. What is the value of Threshold at the 24th transmission round?h. During what transmission round is the 70th segment sent?i. Assuming a packet loss is detected after the 26th round by the receipt of a triple duplicate ACK, what will be the values of the congestion-window size and of Threshold?Solution:a.1-6, 23-26b.6-16, 17-22c.a triple duplicate ACKd.timeoute.32f.21g.13h.7i.4, 4P293 #34 Consider sending an object of size O = 100 Kbytes from server to client. Let S = 536 bytes and RTT = 100 msec. suppose the transport protocol uses static windows with window size W. (See Section 3.7.2)a.For a transmission rate of 28 kbps, determine the minimum possible latency. Determine the minimum window size that achieves this latency.b.Repeat (a) for 100 kbps.tency=28.8s W=2tency=8.2s W=4P405 #8 Consider a datagram network using 8-bit host addresses. Suppose a router uses longest prefix matching and has t he following forwarding table:-----------------------------------------------------Prefix Match Interface-----------------------------------------------------00 001 110 211 3-----------------------------------------------------For each of the four interfaces, give the associated range of destination host addresses and the number of addresses in the range.6P407 #15 Consider sending a 3000-byte datagram into a link that has a MTU of 500 bytes. Suppose the original datagram is stamped with the identification number 422. How many fragments are generated? What are their characteristics?there are「2980/480」=7 fragments be generatedP408 #22 Consider the network shown in Problem 21 (reproduced below). Using Dijkstra’s algorithm, and showing your work using a table similar to Table 4.3, do the following:a. Compute the shortest path from s to all network nodesSteps D(t),P(t) D(u),P(u)D(v),P(v)D(w),P(w)D(x),P(x)D(y),P(y)D(z),P(z)0 1,s 4,s ∞∞∞∞∞1 3.t 10,t ∞∞5,t 3,t2 4,u 6,u ∞5,t 3,t3 4,u 6,u ∞5,t4 5,v 7,v 5,v5 6,w 5,v6 6,wPlease fill in the following tables using DV algorithm:For the node Z in the graph shown in the 22nd topic (P408), please fill in the following routing table in the router z about the initial distance-vector Destination node Next hop Current shortest distancevalue-DzS —∞T T 2U —∞V —∞W —∞X —∞Y Y 14Z Z 0following rout-ing table in the node z to update this routing tableDestination node Currentdistance-DyDestination node Current distance-DtS 5 S 1 T 4 T 0 U 2 U 2P493 #7 How big is the MAC address space?The IPv4 address space?The IPv6 address space?MAC address: 6 bytes, MAC address space 2^48IPV4 address: 4 bytes, IPV4 address space 2^32IPV6 address: 16 bytes, IPV6 address space 2^128P494 #4 Consider the 4-bit generator, G, shown in Figure 5.8, and suppose the D has the value 10101010. What is the value of R?G=1001, D=10101010, R=101。
计算机网络习题答案(二)英文
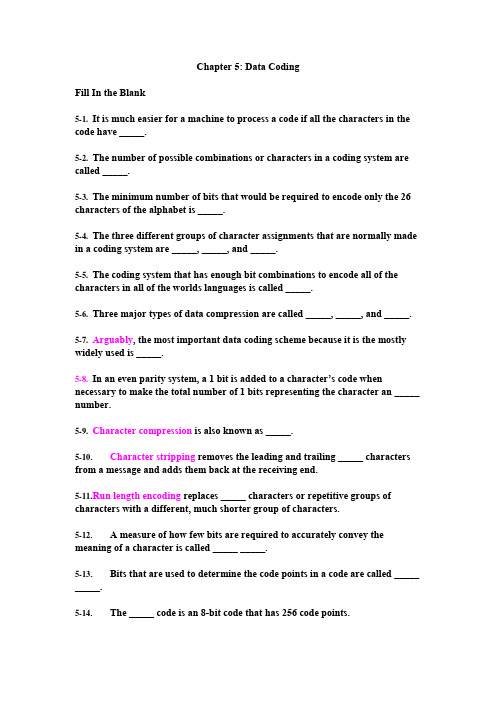
Chapter 5: Data CodingFill In the Blank5-1.It is much easier for a machine to process a code if all the characters in the code have _____.5-2.The number of possible combinations or characters in a coding system are called _____.5-3.The minimum number of bits that would be required to encode only the 26 characters of the alphabet is _____.5-4.The three different groups of character assignments that are normally made in a coding system are _____, _____, and _____.5-5.The coding system that has enough bit combinations to encode all of the characters in all of the worlds languages is called _____.5-6.Three major types of data compression are called _____, _____, and _____. 5-7.Arguably, the most important data coding scheme because it is the mostly widely used is _____.5-8.In an even parity system, a 1 bit is added to a character’s code when necessary to make the total number of 1 bits representing the character an _____ number.5-9.Character compression is also known as _____.5-10. Character stripping removes the leading and trailing _____ characters from a message and adds them back at the receiving end.5-11.R un length encoding replaces _____ characters or repetitive groups of characters with a different, much shorter group of characters.5-12. A measure of how few bits are required to accurately convey the meaning of a character is called _____ _____.5-13. Bits that are used to determine the code points in a code are called _____ _____.5-14. The _____ code is an 8-bit code that has 256 code points.True or False5-1.The term binary digit is abbreviated bit.5-2.Machines cannot send Morse code because the coded characters have different numbers of code elements.5-3.It is more difficult for a machine to process a code if all of the bits are of the same duration.5-4.When even parity is used, a 0 bit is added, if necessary, to make the total number of 0 bits in the character an even number.5-5.The escape character in a coding system is a different character than the one that is generated when you press the ESC key on the keyboard of a PC.5-6.ASCII is a 7-bit code.5-7.Unicode provides enough code points so that all characters in all languages of the world have a unique 16-bit code point.5-8.Code efficiency is a measure of how many extra bits are used beyond those required to convey the meaning of a character.5-9.Data compression is the process of reducing the number of bits used to represent a character, or reducing the number of characters before they are transmitted.5-10.C haracter stripping is the process of removing control characters from a message before it is transmitted.5-11.T he binary digits are 1 and 2.5-12.A code is a predetermined set of symbols that have variable meanings.5-13.M orse code is not considered a binary code, because its two elements are of different length.5-14.A binary code works well for machines communicating by electrical means because the 1 bits and 2 bits can be represented by a current flow that is either on or off.5-15.F or transmission efficiency, it is ideal to have a coding system that uses a minimum number of bits to represent each character.5-16.M ost coding systems include a technique called an escape character.5-17.T he necessity to support escape characters complicates the design of equipment that is to code and decode the data.5-18.T he ASCII code is the most widely used code in computers and communications networks today.5-19.U nicode is a 16-bit character code.Multiple Choice5-1. Characters that control the positioning of information on a workstation screen or paper are called _____.a. page control charactersb. format effector charactersc. device control charactersd. screen control characterse. a and b5-2. It is much easier for a machine to process a code if the code has the following attributes: _____.a. it is a true binary codeb. all of the characters have the same number of bitsc. all of the bits are perfectly formedd. all of the bits are the same duratione. a and cf. All of the above.5-3. The unique sequence of bits assigned to represent the various characters of a code are called _____.a. code pointsb. character assignmentsc. control charactersd. character algorithmse. None of the above.5-4.The purpose of escape characters is to _____.a. allow a program to abort a message prematurelyb. implement a priority system by allowing one message to be prematurelyended so another can be sent on the circuitc. act as an alternate escape control character when more than 8 bits areneededd. indicate that the characters that follow are to be interpreted as having analternate meaninge. indicate that a PDU has been received correctly5-5. The ASCII code is also known as the _____.a. International Telegraph Alphabet 5b. extended ASCII codec. 8-bit coded. PC codee. EBCDIC code5-6. The EBCDIC code _____.a. was developed by IBMb. is an 8-bit codec. has 256 code pointsd. is used on older IBM mainframe computerse. All of the above.f. None of the above.5-7. Unicode _____.a. is a 16-bit codeb. was developed by a group of companiesc. supports the characters of all languagesd. All of the above.e. None of the above.5-8. Code efficiency is calculated _____.a. by minimizing the number of bits transmitted for a given messageb. by dividing the information bits by the total number of bits in a characterc. by dividing the total number of bits by the information bits in a characterd. by measuring the error rate at the receiving end of a transmission5-9. Three major types of data compression are _____.a. character removal, run length encoding, and bit compressionb. bit stripping, double clocking, and character strippingc. character compression, Huffman coding, and character strippingd. character stripping, run length encoding, and character compressione. over clocking, transmission digitizing, and double ACKing5-10. A 10-bit code could represent how many characters?a. 100b. 210 -1c. 29d. 512e. 2105-11.The number of possible combinations or characters in a coding system is called the _____.a. character assignmentb. code pointsc. control characterd. code limite. binary code5-12.Many coding systems include an extra bit, called a _____ , for checking purposes.a. parity bitb. padding bitc. control bitd. binary digite. checking bit5-13.When an ESC character is sent as a part of the data, it means that _____.a. the transmission is being abortedb. this is the end of the transmissionc. the characters that follow are to be interpreted as having an alternate meaningd. the characters that follow are encryptede. the transmission should be ignored5-14. Graphic characters _____.a. can be displayed on a workstation screenb. are special characters only used by graphic artistsc. are only present in specialized code systemsd. can also be used as format effector characters5-15Code conversion _____.a. changes one character to another for security purposesb. changes the characters in one coding system to those of another coding systemc. can be readily performed by a computerd. All of the above.e. b and cChapter 6: Data Communication FundamentalsFILL IN THE BLANK6-1. The three attribute s of a sine wave are its _____ , _____ , and _____.6-2. The FM radio band in the United States extends from 88 MHz to 108 MHz. Its bandwidth is _____.6-3. A signal drop of 10 dB represents a drop in power of _____times.6-4. A radio signal with a frequency of 101 MHz falls within the _____radio band.6-5. Speech with frequencies above _____is attenuate d and not transmitted through the public telephone network.6-6. Changing a communication signal by alter ing its amplitude, frequency, or phase is called _____.6-7. The unit of signaling rate on a communication circuit is called _____.6-8. The unit of measure of a circuit's data carrying rate is called _____6-9. Sending a tribit on a circuit requires _____(how many) unique signal changes to be transmitted?6-10. A circuit that allows transmission in one direction only is called a _____ circuit.6-11. A circuit that allows transmission in either direction but not at the same time is called a _____circuit.6-12. A circuit that allows transmission in both directions simultaneously is called a _____circuit.6-13. A circuit that allows all of the bits in a character to be transmitted simultaneously is called a _____circuit.6-14. A circuit in which the bits of a character are transmitted one after the other on a single communication path is called a _____circuit.6-15. The mechanism by which character synchronization occurs in asynchronous transmission is called _____and _____bits.6-16. The means by which the receiver knows which bits to group together to form a character is called _____.6-17. When each block of data to be transmitted is surrounded with synchronizing and other control characters the transmission is called _____.6-18. When each character to be transmitted is surrounded with start and stop bits, the transmission is called _____.6-19. The _____condition is the idle condition on a line. Conventionally it is the same as the signal for a 1 bit.6-20. The purpose of the _____in synchronous transmission is to maintain synchronization between the transmitting node and the receiving node.6-21. _____modulation is better suited for high-speed analog transmission because the receiver more easily detects changes in _____than changes in amplitude or frequency.6-22. _____equalizers assume that the circuit meets a n average set of loss, noise, and distortion parameter s, and shape the transmitted signal accordingly.6-23. _____equalizers examine the actual parameters of the circuit being used, and shape the signal to match its specific characteristics.6-24. Modems that use the V.34 standard use a sophisticated modulation technique called _____, and they assume that most of the actual transmission will occur on _____circuits.6-25. High-speed modems achieve a high throughput rate by using sophisticated modulation and __________techniques.6-26. A _____ensures that the signal entering a digital circuit has properly shaped, square pulses, and is precisely timed.6-27. The time it takes the modems on an HDX circuit to reverse their function –the time for the transmitting modem to switch to being the receiver, and the receiving modem to switch to being the transmitter—is called _____.6-28. The advantages of _____transmission over _____transmission include better data integrity; higher capacity circuits; easier integration of voice, data and other signals; better security and privacy; and lower cost.6-29. The type of digital modulation that takes 8,000 samples per second but uses only 4 bits per sample to code the difference between the values of two samples is called _____.6-30. An _____converts analog signals to a digital format.6-31. The difference between the actual value (height) of an analog signal and the nearest integer value, which is assigned when the signal is digitized, is called_____.6-32. When the number of data bits in a character is divided by the total number of bits required to transmit the character, the __________is being calculated. TRUE OR FALSE6-1. Signaling is the propagation of a signal on a medium.6-2. Playing the A key above middle C on a piano results in a digital signal that has 880 pulses per second.6-3. Sound waves, electrical waves, and electromagnetic waves have essentially different characteristics.6-4. A digital signal level is measured in decibels.6-5. The loss of signal strength between two points on a communication circuit is called attenuation.6-6. The amplitude and phase of a voice signal remain constant while its frequency changes.6-7. ADPCM is accomplished by shifting each channel to a different part of the frequency spectrum.6-8. The speed of a circuit is measured in baud.6-9. A 2,400 baud signal can carry data at a maximum rate of 7,200 bps.6-10. When 2 bits of information are coded into one signal change, they are called bi-bits.6-11. The most common digital signals are unipolar.6-12. When transmitting digital signals on an analog circuit, a modem is used.6-13. An analog signal that has been digitized can be closely restored to its original analog shape by a D/A converter.6-14. PCM is the ITU-T’s recommended method for digitizing voice at 32 Kbps. 6-15. In a modem, equalizer circuitry compensates for the variability of the actual transmission line used.6-16. Line turnaround time in a modem can be a significant part of the total transmission time.6-17. Modems can never handle full-duplex transmission.6-18. Phase modulation is the technique of chang ing a digital signal’s phase in order to modulate it.6-19. V.34-bis modems assume that most data transmission occurs on digital lines.6-20. The transmission speed between a pair of V.90 modems is symmetric.6-21. Cable modems for each CATV system are unique.6-22. Modem eliminator s are a low-cost alternative to modems on LAN circuits.6-23. There are very few practical uses for simplex transmission.6-24. Parallel mode transmission is widely used on WANs to achieve high throughput.6-25. Asynchronous transmission is widely used today.6-26. Start bits precede every data block in synchronous transmission.6-27. To jam a spread spectrum signal, one simply broadcasts a jamming signal on the spread spectrum signal’s carrier frequency.MULTIPLE CHOICE6-1. The reasons that digital transmission is superior to analog transmission are _____.a. better data integrityb. higher capacityc. easier integrationd. better security and privacye. lower costf. All of the above.g. only a, b, c, and d6-2. A modem is a form of a _____.a. A/D converterb. D/A converterc. codecd. DTEe. None of the above.f. a and b6-3. The three attributes of an analog signal discussed in the chapter are _____.a. frequency, decibels, and modulationb. phase, frequency, and amplitudec. amplitude, carrier, and sined. bit rate, speed, and error ratee. unipolarity, quantization, and equilibrium6-4. Parallel transmission occurs _____.a. during spread spectrum transmissionb. when a PC sends data to a printer using a serial cablec. on most WAN circuitsd. All of the above.e. None of the above.6-5. Differential Manchester coding _____.a. is often used on WANsb. is almost never usedc. is subservient to Manchester codingd. requires an analog circuit to work properlye. None of the above.6-6. The most widely used interface standard between PCs and modems is _____.a. point-to-pointb. USBc. RS-232-Dd. RS-232-Ce. X.256-7. The X.21 interface standard _____.a. is a replacement for RS-232-Cb. defines the interface to a digital circuitc. uses a PL-259 connectord. All of the above.e. None of the above.6-8. A network interface card _____.a. provides the interface from a PC to a networkb. provides the interface from one network to anotherc. provides the interface from a modem to a networkd. converts signals from analog to digitale. None of the above.6-9. When two modems send signals to each other for the process of establishing transmission parameters, it is called _____.a. synchronizingb. call setupc. call establishmentd. MOST (acronym for modem startup)e. handshaking6-10. Hertz is the unit of measure for _____.a. baudb. bit ratec. trellis code modulationd. cycles per seconde. data ratef. None of the above.6-11. The difference between the exact height of an analog signal and the nearest integer value when a digitizing sample is taken is called _____.a. digitizing discrepancyb. digitizing errorc. quantizing noised. digitizing discernmente. a and cf. b and c6-12. QAM uses a combination of _____and _____to generate quadbits.a. phase changes and relative amplitudesb. phase changes and dibitsc. phase changes and frequency changesd. amplitude changes and frequency changese. amplitude changes and dibitsChapter 7: Data Link Control ProtocolsFILL IN THE BLANK7-1. A set of rules that define the exact format of messages exchanged between computers or between computers and people is called a _____.7-2. Data link protocols are necessary so that all of the devices on the network are operating by the same set of rules and are able to _____with each other.7-3. The part of a protocol consisting of the rules that specify the way the receiving terminal signals the sending terminal if it has received data correctly, how and under what circumstances the line will be turned around, and whether the receiving terminal can accept more data is called _____.7-4. The part of the protocol consisting of rules specifying what happens when an error is detected, what to do if communications suddenly and unexplainably cease, and the way communications are reestablished after they are broken is called _____.7-5. The part of a protocol consisting of rules for ending the communications under normal and abnormal circumstances is called _____.7-6. The ability of data terminal equipment (DTE) to be able to transmit and receive any bit pattern as data is called _____.7-7. Predetermined communication parameters are those that are set _____by switches or specified as parameters in software.7-8. When a central or control station asks each station on the circuit or network if it has traffic to send, it is using a line control technique called _____.7-9. When any station that has traffic looks to see if the circuit is free, and if it is, begins sending its traffic the line control technique is called _____.7-10. In a polling system, one way that priority can be given to a terminal is by listing its address in the polling list _____.7-11. The _____of a message contains and conveys information about the message, such as the destination node’s address, a sequence number, and perhaps a date and time.7-12. BISYNC is defined to only support the 6-bit transcode (SBT), EBCDIC, and _____.7-13. Character synchronization is accomplished in BISYNC by sending _____ characters at the beginning and periodically in the middle of each transmission.7-14. Compared to BISYNC, DDCMP and other byte-count protocols implement transparency in a much more _____manner.7-15. The HDLC ___ field is used to mark the beginning and ending of frames.7-16. The technique that ensures a flag’s uniqueness by not allowing any other sequence of six consecutive 1 bits in the data stream is called _____.7-17. A protocol that is primarily used by PC workstations to send IP overdial-up lines, typically when dial ing in to an ISP for connection to the Internet, is called _____.7-18. The _____protocol was developed by IBM and then generalize d to become HDLC.7-19. SDLC is a _____of HDLC.7-20. SDLC is a subset of _____.7-21. A _____changes one protocol to another, when, for example, a message is sent between two networks that use different protocols.7-22. A sophisticated check character at the end of each block of data is called a _____.7-23. A technique used to ensure that a fast transmitting node does not send data faster than a receiving node can receive and process it is called _____.7-24. The flow control technique that allows multiple frames to be in transit on the line at one time is called _____.TRUE OR FALSE7-1. Data link protocols are concerned with the transmission of data through an entire network.7-2. All protocols use the same bit patterns as control characters.7-3. Data transparency allows a protocol to be able to transmit and receive any bit patterns as data.7-4. A protocol is implemented by transmitting certain bit patterns or characters on the communication circuit.7-5. The code used for the data is independent of the protocol being used.7-6. Because of collision s, contention systems are rarely used for line access.7-7. Poll ing systems require several stations on the circuit to act as master stations.7-8. Hub polling is the most common implementation of a polling system.7-9. Polling systems are dependent on the data code being used.7-10. Token passing systems require one station on the circuit to take responsibility to ensure that there are always multiple tokens circulating on the circuit.7-11. Data messages normally consist of three parts: the header, text, and trailer. 7-12. The ACK character normally acknowledges the receipt of a block of data. 7-13. Stop-and-wait flow control is inherently efficient because of its simplicity. 7-14. Stop-and-wait flow control allows multiple blocks of data to be in transit on the line at one time.7-15. PPP has largely replaced the SLIP protocol because it has better error detection.7-16. KERMIT is error checked but is a very slow protocol.7-17. A bit-oriented protocol uses multiple control characters to mark the start and end of parts of a message.7-18. HDLC is a bit-oriented protocol.7-19. SLDC is a byte-count-oriented protocol.7-20. The best known bit-oriented protocol is BISYNC.7-21. SDLC was an outgrowth of the original work on HDLC.7-22. SDLC operates in one of three modes; however, one mode is rarely used. 7-23. The basic operational unit for HDLC is a PDU.7-24. HDLC uses a FRA character to mark the beginnings and ends of frames. 7-25. BISYNC supports only selected data codes.7-26. BISYNC supports transparency.7-27. DDCMP has largely been replaced by HDLC.7-28. Go-back-n is an implementation of sliding window flow control.7-29. The LAP protocols are variant s of HDLC.7-30. PPP is a widely used synchronous protocol for dialing into the Internet through an ISP.MULTIPLE CHOICE7-1. In HDLC, when a 0 bit is inserted after all strings of five consecutive 1 bits, the term applied is _____.a. zeroingb. bit stuffingc. synchronizingd. oneinge. string breaking7-2. When two stations on a circuit transmit at the same time, a(n)_____occurs.a. altercationb. divisionc. pollingd. bit stuffinge. collision7-3. In order to know what stations to poll and in what sequence, the master station uses a _____.a. message headerb. polling listc. start of header characterd. polling PDAe. cyclic redundancy check7-4. When a receiver must acknowledge every block of data before the next block is sent, the _____type of flow control is being used.a. stop-and-waitb. stop-and-checkc. stop-and-flopd. sliding framee. sliding window7-5. The name of the flow control protocol in which the sending station, on receipt of a NAK, resends the damaged or out of sequence frame and all frames after it is _____.a. selective rejectb. TCPc. selective repeatd. send all before ne. HDLC7-6. HDLC is an example of _____.a. sliding window flow controlb. a serial line interface protocolc. an asynchronous protocold. All of the above.e. None of the above.7-7. When an HDLC node receives a flag character, it knows that _____.a. an error has occurredb. it should signal the sender to stop sending trafficc. a frame is beginning or endingd. it should switch to transparent modee. None of the above.7-8. HDLC’s information frames _____.a. are used to send an NAK when a frame is received incorrectlyb. are used to establish the way the protocol will proceedc. are used to send information from one node to a router for flow controld. contain the data field that holds the information being transmittede. are not used in ABM mode7-9. The part of a message that contains the destination address is called the_____.a. headerb. address PDUc. textd. trailere. flag7-10. Software or hardware that changes one protocol to another is called a_____ .a. CODECb. protocol converterc. modemd. routere. encryptor7-11. Contention systems work best _____.a. on circuits that have only more than two DTEsb. when the speed of the circuit is relatively fastc. on circuits that have heavy message trafficd. All of the above.e. None of the above.7-12. Desirable attributes for a data link protocol to have are _____.a. transparencyb. efficiencyc. bit linearityd. a, b, and ce. a and b7-13. Techniques to ensure that a fast transmitting node does not send data faster than the receiving node can receive and process it are called _____ .a. token passingb. flow controlc. parity checkingd. cyclic redundancy checkinge. error control7-14. The LAPD protocol is used _____.a. between an X.25 DTE and a packet switching networkb. on an ISDN D channelc. on frame relay networksd. on value added networkse. as a substitute for TCP/IP7-15. Go-back-n and selective repeat are two common implementations of _____.a. bit oriented protocolsb. byte protocolsc. byte-count oriented protocolsd. sliding window flow controle. transmission control protocolsChapter 8: Transmission MediaFILL IN THE BLANK8-1. A type of media that provides some type of physical path, such as wire, cable, or optical fiber, along which the signal moves from end to end is called _______ or guided media.8-2. Air is an example of _______ media.8-3. Twisted pair wire is an example of _______ media.8-4. The best media to use in homes and offices where costs must be kept low and bandwidth requirements are moderate is ____.8-5. The most appropriate media to use when there is a need for very high bandwidth and high security is _____.8-6. The most appropriate media to use when there is a need for high bandwidth and to broadcast to a wide area is ____.8-7. Wire containing at least three twists per foot and that is about the same as normal telephone cable installed in most office buildings is called _____.8-8. _____ cable normally contains four pairs of wires and is the type that is most commonly being installed in new homes and businesses, particularly when it is known that a computer network will be used.8-9. The shielding in shielded twisted pair wire provides a degree of _____ _____ in electrically noisy environments.8-10. _____ is advantageous when tap s in the cable need to be made—it is easier to tap than optical fiber.8-11. The characteristic of _____ include: high bandwidth, difficult to tap and splice; not subject to electrical interference, cable is very small diameter and lightweight.8-12. A _____ is required to operate a microwave transmitter.8-13. _____ _____ is the delay that occurs because light and radio signals only travel at 186,000 miles per second.8-14. Satellites in _____ orbits circle the earth at 22,300 miles.8-15. Satellites in _____ orbits are approximately 6,000 miles high.8-16. _____ works by modulating a laser light beam instead of broadcasting a radio wave.8-17. _____ is a fiber that has a glass core approximately 9 microns in diameter. 8-18. Data are placed on an optical fiber with a light source, either an LED or a _____.8-19. When UTP is used in a data application it is normally terminate d with a _____ jack.8-20. A type of satellite commonly used to send television programming into homes is called a _____.TRUE OR FALSE8-1. Optical fiber is an example of an unguided medium.8-2. Guided media are also known as wireless media.8-3. Wireless media are the most common media used today.8-4. Optical fiber emits an electro-optical field when carrying communications signals.8-5. CAT 3 cable is most frequently used for telephone transmission in older buildings.8-6. CAT 5 cable is commonly being installed in new homes and businesses.8-7. An advantage of UTP wire is its relatively low cost.8-8. Coaxial cable can be tapped easily.8-9. Optical fiber can be tapped easily.。
计算机网络(第四版)课后习题(英文)+习题答案(中英文)
damaged is p, what is the mean number of transmissions required to send a frame? Assume that acknowledgements are never lost.(M) 假设某帧传到第 k 次才传输成功, 起初 k-1 次传输皆尝试失败, 概率为 pk-1 , 第 k 次传输成功,概率为(1-p) ,则发送一帧成功的平均传输次数为:
1. a.
Which of the OSI layers handles each of the following: (a) Dividing the transmitted bit stream into frames.
b. (b) Determining which route through the subnet to use.(E) 把传输的比特流划分为帧——数据链路层 决定使用哪条路径通过子网——网络层. 19. If the unit exchanged at the data link level is called a frame and the unit exchanged at the network level is called a packet, do frames encapsulate packets or do packets encapsulate frames? Explain your answer.(E) 帧封装包。 当一个包到达数据链路层时,整个数据包,包括包头、数据及全部内 容,都用作帧的数据区。或者说,将整个包放进一个信封(帧)里面,( 如果能装入的 话)。 21. List two ways in which the OSI reference model and the TCP/IP reference model are the same. Now list two ways in which they differ.(M) 相似点:都是独立的协议栈的概念;层的功能也大体相似。 不同点:OSI 更好的区分了服务、接口和协议的概念,因此比 TCP/IP 具有更好的 隐藏性,能够比较容易的进行替换;OSI 是先有的模型的概念,然后再进行协议的 实现, 而 TCP/IP 是先有协议, 然后建立描述该协议的模型; 层次数量有差别; TCP/IP 没有会话层和表示层,OSI 不支持网络互连。OSI 在网络层支持无连接和面向连接 的通信, 而在传输层仅有面向连接的通信, 而 TCP/IP 在网络层仅有一种通信模式 (无 连接),但在传输层支持两种模式。 22. What is the main difference between TCP and UDP?(E) TCP 是面向连接的,而 UDP 是一种数据报服务。
计网课后习题答案(英文)
Review Questions第一章1.Which characteristics of a multiterminal system make it different from a computer network?A processing power of multiterminal systems remained fully centralized, whilecomputer networks have a distributed processing power.一个多端系统处理能力仍然完全集中,而计算机网络具有分布式处理能力。
2.When were the first important results achieved in the field of joining computers using long-haul links?In the late 60s在60年代后期3.What is ARPANET?A.A network of supercomputers belonging to military organizations and research institutes in the United StatesB.An international scientific research networkC.The technology of creating WANsA is correct4.When did the first network operating systems appear?In the late 60s60年代后期5.In what order did the events listed here take place?A.The invention of WebB.The development of standard LAN technologiesC.The start of voice transmission in digital form through telephone networksThe invention of World Wide Web互联网的诞生6.Which of the events stimulated LAN development?Appearance of large-scale integrated circuits (LSI devices) resulted in invention of microcomputers which in its turn stimulated a research activity in the area of local computer networks (LANs). The adoption of personal computers was a powerful incentive for the development of LANs.大规模集成电路(LSI器件出现)导致这反过来刺激了研究活动在本地计算机网络(LAN)的微型计算机的发明。
computer network课后答案(1)
Chapter 1 Review Questions1. There is no difference. Throughout this text, the words “host” and “end system” are used interchangeably. End systems include PCs, workstations, W eb servers, mail servers, Internet-connected PDAs, W ebTVs, etc.3. A networking program usually has two programs, each running on a different host, communicating with each other. The program that initiates the communication is the client. Typically, the client program requests and receives services from the server program.22. application-layer message: data which an application wants to send and passed onto the transport layer; transport-layer segment: generated by the transport layer and encapsulates application-layer message with transport layer header; network-layer datagram: encapsulates transport-layer segment with a network-layer header; linklayer frame: encapsulates network-layer datagram with a link-layer header.23. Routers process layers 1 through 3. (This is a little bit of a white lie, as modern routers sometimes act as firewalls or caching components, and process layer four as well.) Link layer switches process layers 1 through 2. Hosts process all five layers.Chapter 1 ProblemsProblem 6.a) d m s prop = / seconds.b) d L R trans = / seconds.c) d (m/ s L / R) end to end = + ? ? seconds.d) The bit is just leaving Host A.e) The first bit is in the link and has not reached Host B.f) The first bit has reached Host B.g) W ant(2.5 10 ) 89328 10100 83 ≠ =≠= S =Rm L km.Problem 10.It takes LN / R seconds to transmit the N packets. Thus, the buffer is empty when a batch of N packets arrive.The first of the N packets has no queueing delay. The 2nd packet has a queueing delayof L / R seconds. The n th packet has a delay of (n ?1)L / R seconds. The average delay is2( 1)21 ( 1) / 1 1 1 ( 1)1 0?=?┣ ? = ┣ = ?= =NRN N LR Nn LR Nn L R LNNnNn.Problem 11.a) The transmission delay is L / R . The total delay isIL RRLR IIL?+ =? 1/(1 )b) Let x = L / R .Total delay =axx1?Problem 14.a) 40,000 bitsb) 40,000 bitsc) the bandwidth-delay product of a link is the maximum number of bits that can be inthe linkd) 1 bit is 250 meters long, which is longer than a football fielde) s/RProblem 18.a) 150 msecb) 1,500,000 bitsc) 600,000,000 bitsChapter 2 Review Questions1. The W eb: HTTP; file transfer: FTP; remote login: Telnet; Network News: NNTP; email: SMTP.5. No. As stated in the text, all communication sessions have a client side and a server side. In a P2P file-sharing application, the peer that is receiving a file is typically the client and the peer that is sending the file is typically the server.6. The IP address of the destination host and the port number of the destination socket.10. The applications associated with those protocols require that all application data be received in the correct order and without gaps. TCP provides this service whereas UDP does not.22. With the UDP server, there is no welcoming socket, and all data from different clients enters the server through this one socket. With the TCP server, there is a welcoming socket, and each time a client initiates a connection to the server, a new socket is created. Thus, to support n simultaneous connections, the server would need n+1 sockets. Chapter 2 ProblemsProblem 1.a) Fb) Tc) Fd) FProblem 4.Application layer protocols: DNS and HTTPTransport layer protocols: UDP for DNS; TCP for HTTPProblem 9.a) The time to transmit an object of size L over a link or rate R is L/R. The average time is the average size of the object divided by R:┐= (900,000 bits)/(1,500,000 bits/sec) = .6 secThe traffic intensity on the link is (1.5 requests/sec)(.6 msec/request) = .9. Thus, theaverage access delay is (.6 sec)/(1 - .9) = 6 seconds. The total average response time is therefore 6 sec + 2 sec = 8 sec.b) The traffic intensity on the access link is reduced by 40% since the 40% of the requests are satisfied within the institutional network. Thus the average access delayis (.6 sec)/[1 쭯(.6)(.9)] = 1.2 seconds. The response time is approximately zero if the request is satisfied by the cache (which happens with probability .4); the average response time is 1.2 sec + 2 sec = 3.2 sec for cache misses (which happens 60% of the time). So the average response time is (.4)(0 sec) + (.6)(3.2 sec) = 1.92 seconds. Thus the average response time is reduced from 8 sec to 1.92 sec. Chapter 3 Review Questions1. Source port number y and destination port number x.2. An application developer may not want its application to use TCP’s congestion contro l, which can throttle the application’s sending rate at times of congestion. Often, designers of IP telephony and IPvideoconference applications choose to run their applications over UDP because they want to avoid TCP’s congestion control.Also, some applications do not need the reliable data transfer provided by TCP.4. a) false b) false c) true d) false e) true f) false g) false5. a) 20 bytes b) ack number = 90Chapter 3 ProblemsProblem 1.source port numbersdestination port numbersa) A ∪ S 467 23b) B ∪ S 513 23c) S ∪ A 23 467d) S ∪ B 23 513e) Y es.f) No.Problem 3.1 1 0 0 0 1 0 10 1 1 1 0 0 0 00 1 0 1 0 1 0 1+0 0 0 1 0 0 0 10 1 0 0 1 1 0 01 1 0 0 0 1 0 1+One's complement = 1 1 1 0 1 1 1 0.To detect errors, the receiver adds the four words (the three original words and the checksum). If the sum contains a zero, the receiver knows there has been an error. All one-bit errors will be detected, but two-bit errors can be undetected (e.g., if the last digit of the first word is converted to a 0 and the last digit of the second word is converted to a 1).Problem 19.a) True. Suppose the sender has a window size of 3 and sends packets 1, 2, 3 at t0 . At t1 (t1 > t0) the receiver ACKS 1, 2, 3. At t2 (t2 > t1) the sender times out and resends 1, 2, 3. At t3 the receiver receives the duplicates and re-acknowledges 1, 2, 3. At t4 the sender receives theACKs that the receiver sent at t1 and advances its nwindow to 4, 5, 6. At t5 the sender receives the ACKs 1, 2, 3 the receiver sent at t2 . These ACKs are outside its window.b) True. By essentially the same scenario as in (a).c) True.d) True. Note that with a window size of 1, SR, GBN, and the alternating bit protocol are functionally equivalent. The window size of1 precludes the possibility of out-of-order packets (within the window).A cumulative ACK is just an ordinary ACK in this situation, since it can only refer to the single packet within the window.Chapter 4 Review Questions3. Forwarding is about moving a packet from a router’s input link to the appropriate output link. Routing is about determining the end-to-routes between sources and destinations.8. switching via memory; switching via a bus; switching via an interconnection network12. Y es. They have one address for each interface.16. 50% overhead34. FalseChapter 4 ProblemsProblem 7.a)Prefix Match Link Interface11100000 011100001 00000000 111100001 2otherwise 3b) Prefix match for first address is 4th entry: link interface 3Prefix match for second address is 2nd entry: link interface 1Prefix match for first address is 3rd entry: link interface 2Problem 8.Destination Address Range Link Interface00000000through 00011111101000000through 10111111110000000through 21011111111000000through 311111111number of addresses in each range = 26 = 64Problem 13.Any IP address in range 101.101.101.65 to 101.101.101.127Four equal size subnets: 101.101.101.64/28, 101.101.101.80/28, 101.101.101.96/28,101.101.101.112/28Problem 16.MP3 file size = 4 million bytes. Assume the data is carried in TCP segments, with each TCP segment also having 20 bytes of header. Then each datagram can carry 1500- 40=1460 bytes of the MP3 file Number of fragments required = 274014604 106= ?????? ≠= . All but the last fragment will be1,500 bytes; the last fragment will be 1060+40 = 1100 bytes. The offsets will be multiples of 185 (as in example in Section 4.4.1). Chapter 5 Review Questions1. Although each link guarantees that an IP datagram sent over the link will be received at the other end of the link without errors, it is not guaranteed that IP datagrams will arrive at the ultimate destination in the proper order. With IP, datagrams in the same TCP connection can take different routes in the network, and therefore arrive out of order. TCP is still needed to provide the receiving end of the application the byte stream in the correct order. Also, IP can lose packets due to routingloops or equipment failures. 7. 248 MAC addresses; 232 IPv4 addresses; 2128 IPv6 addresses.Chapter 5 ProblemsProblem 4.If we divide 1001 into 10101010000 we get 10010111, with a remainder of R = 001.Problem 11.At t = 0 A transmits. At t = 576 , A would finish transmitting. In the worst case, Bbegins transmitting at time t = 224 . At time t = 224 + 225 = 449 B 's first bit arrives at A . Because 449 < 576 , A aborts before completing the transmission of the packet, as it is supposed to do. Thus A cannot finish transmitting before it detects that B transmitted. This implies that if A does not detect the presence of a host, then no other host begins transmitting while A is transmitting.。
计算机网络英文题库(附答案)chapter1

Chapter 1 Computer Networks and the Internet networks use VC. numbers to forward packets toward their1.The ( ) is a worldwide computer network, that is, a network that destination.interconnects millions of computing devices throughout the world. D datagram networks use VC. numbers and virtual-circuit networks ppt3 use destination addresses to forward packets toward their destination.A public Internet 9.In the following options, which one is not a guided media? ( )B Intranet A twisted-pair wireC switch net B fiber opticsD television net C coaxial cable2.Which kind of media is not a guided media? ( ) D satelliteA twisted-pair copper wire 10.Processing delay does not include the time to ( ).B a coaxial cable A examine the packet’s headerC fiber optics B wait to transmit the packet onto the linkD digital satellite channel C determine where to direct the packetD check bit-error in the packet3.Which kind of media is a guided media? ( )11.In the following four descriptions, which one is correct? ( )A geostationary satelliteB low-altitude satelliteC fiber opticsD wireless LAN A The traffic intensity must be greater than 1.B The fraction of lost packets increases as the traffic intensity decreases.C If the traffic intensity is close to zero, the average queuing delay 4.The units of data exchanged by a link-layer protocol are called ( ).will be close to zero. A FramesD If the traffic intensity is close to one, the average queuing delay B Segmentswill be close to one. C Datagrams12.The Internet’s network layer is responsible for moving network-layer D bit streamspackets known as ( ) from one host to another. 5.Which of the following option belongs to the circuit-switched networks?A frame ( )B datagram A FDMC segment B TDMD message C VC networks13.The protocols of various layers are called ( ). D both A and BA the protocol stack 6.( )makes sure that neither side of a connection overwhelms the otherB TCP/IPside by sending too many packets too fast.C ISPA Reliable data transferD network protocolB Flow control14.There are two classes of packet-switched networks: ( ) networks andC Congestion controlvirtual-circuit networks.D Handshaking procedureA datagram7.( ) means that the switch must receive the entire packet before it canB circuit-switchedbegin to transmit the first bit of the packet onto the outbound link.C television A Store-and-forward transmissionB FDMD telephoneC End-to-end connection 15.Access networks can be loosely classified into three categories:D TDM residential access, company access and ( ) access.8.Datagram networks and virtual-circuit networks differ in that ( ).A cabledA datagram networks are circuit-switched networks, andB wirelessvirtual-circuit networks are packet-switched networks.B datagram networks are packet-switched networks, andC campusD city areavirtual-circuit networks are circuit-switched networks.Question 16~17 C datagram networks use destination addresses and virtual-circuit1D distributed applicationsSuppose, a is the average rate at which packets arrive at the queue, R is24.The Internet provides two services to its distributed applications: a the transmission rate, and all packets consist of L bits, then the trafficintensity is ( 16 ), and it should no greater than ( 17 ). connectionless unreliable service and () service.A flow control16. A LR/aB connection-oriented reliableB La/RC congestion controlC Ra/LD TCP25.It defines the format and the order of messages exchanged between twoD LR/aor more communicating entities, as well as the actions taken on the 17.A 2B 1 transmission and/or receipt of a message or other event. The sentence describes ( ).C 0A InternetD -1B protocol 18.In the Internet, the equivalent concept to end systems is ( ).C intranet A hostsD network B servers26.In the following options, which does not define in protocol? ( )C clientsA the format of messages exchanged between two or more D routerscommunicating entities 19.In the Internet, end systems are connected together by ( ).B the order of messages exchanged between two or more A copper wirecommunicating entities B coaxial cableC the actions taken on the transmission of a message or other eventC communication linksD the transmission signals are digital signals or analog signals 模拟D fiber optics信号20.End systems access to the Internet through its ( ).27.In the following options, which is defined in protocol? ( ) A modemsA the actions taken on the transmission and/or receipt of a message orB protocolsother eventC ISPB the objects exchanged between communicating entities D socketsC the content in the exchanged messages21.End systems, packet switches, and other pieces of the Internet, run ( )D the location of the hosts that control the sending and receiving of information within the28.In the following options, which does not belong to the network edge?Internet.( )A programsA end systemsB processesB routersC applicationsC clientsD protocolsD servers22.There are many private networks, such as many corporate and29.In the following options, which belongs to the network core? ( ) government networks, whose hosts cannot exchange messages withA end systemshosts outside of the private network. These private networks are oftenB routersreferred to as ( ).C clientsA internetsD serversB LAN30.In the following options, which is not the bundled with the Internet ’s C intranetsconnection-oriented service? ( ) D WANA reliable data transfer23.The internet allows ( ) running on its end systems to exchange dataB guarantee of the transmission timewith each other.C flow control***A clients applicationsD congestion-controlB server applications31.An application can rely on the connection to deliver all of its data C P2P applicationswithout error and in the proper order. The sentence describes ( ).2***A flow control C data switchingB congestion-control D message switchingC reliable data transfer 40.In ( ) networks, the resources needed along a path to provide forD connection-oriented service communication between the end system are reserved for the duration 持续of the communication session. 32.It makes sure that neither side of a connection overwhelms 淹没压倒the other side by sending too many packets too fast. The sentence A packet-switcheddescribes ( ). B data-switchedA flow control C circuit-switchedB congestion-control D message-switchedC connection-oriented service 41.In ( ) networks, the resources are not reserved; a session’s messagesD reliable data transfer use the resources on demand, and as a consequence, may have to wait 33.It helps prevent the Internet from entering a state of gridlock. When a for access to communication link.packet switch becomes congested, its buffers can overflow and packet A packet-switchedloss can occur. The sentence describes ( ). B data-switchedA flow control C circuit-switchedB congestion-control D message-switchedC connection-oriented service 42.In a circuit-switched network, if each link has n circuits, for each linkD reliable data transfer used by the end-to-end connection, the connection gets ( ) of the 34.The Internet’s connection-oriented service has a name, it is ( ). link ’s bandwidth for the duration of the connection.A TCP A a fraction 1/nB UDP B allC TCP/IP C 1/2D IP D n times35.In the following options, which service does not be provided to an 43.For ( ), the transmission rate of a circuit is equal to the frame rate application by TCP?( ) multiplied by the number of bits in a slot.A reliable transport A CDMAB flow control B packet-switched networkC video conferencing C TDMD congestion control D FDM36.The Internet’s connectionless service is called ( ). 44.( ) means that the switch must receive the entire packet before it canA TCP begin to transmit the first bit of the packet onto the outbound link.B UDP A Queuing delayC TCP/IP B Store-and-forward transmissionD IP C Packet loss37.In the following options, which does not use TCP?( ) D PropagationA SMTP 45.The network that forwards packets according to host destinationB internet telephone addresses is called ( ) network.C FTP A circuit-switchedD HTTP B packet-switched38.In the following options, which does not use UDP?( ) C virtual-circuitA Internet phone D datagramB video conferencing 46.The network that forwards packets according to virtual-circuit numbersC streaming multimedia is called ( ) network.D telnet A circuit-switched39.There are two fundamental approaches to building a network core, ( ) B packet-switchedand packet switching. C virtual-circuitA electrical current switching D datagramB circuit switching3。
计算机网络英文题库(附答案)chapter1
计算机网络英文题库(附答案)chapter1精心整理Chapter1ComputerNetworksandtheInternet1.The()isaworldwidecomputernetwork,thatis,anetworktha tinterconnectsmillionsofcomputingdevicesthroughoutt heworld.ppt3A publicInternetB IntranetC switchnetD televisionnet 2.Whichkindofmediaisnotaguidedmedia?()A twisted-paircopperwireB acoaxialcableC fiberopticsD digitalsatellitechannel 3.Whichkindofmediaisaguidedmedia?()A geostationarysatelliteB low-altitudesatelliteC fiberopticsD wirelessLAN4.ed().A FramesB SegmentsC DatagramsD bitstreams5.ABCD6.()makessurethatneithersideofaconnectionoverwhelmsth eothersidebysendingtoomanypacketstoofast.A ReliabledatatransferB FlowcontrolC CongestioncontrolD Handshakingprocedure7.()meansthattheswitchmustreceivetheentirepacketbefor eitcanbegintotransmitthefirstbitofthepacketontotheo utboundlink.A Store-and-forwardtransmissionB FDMC End-to-endconnectionD TDM8.Datagramnetworksandvirtual-circuitnetworksdifferint hat().Adatagramnetworksarecircuit-switchednetworks,a ndvirtual-circuitnetworksarepacket-switchednetworks.Bdatagramnetworksarepacket-switchednetworks,an dvirtual-circuitnetworksarecircuit-switchednetworks.D satellite 10.Processingdelaydoesnotincludethetimeto().A examinethepacket’sheaderB waittotransmitthepacketontothelinkC determinewheretodirectthepacketD checkbit-errorinthepacket 11.Inthefollowingfourdescriptions,whichoneiscorrect?() A Thetrafficintensitymustbegreaterthan1.B Thefractionoflostpacketsincreasesasthetraffic intensitydecreases.CIfthetrafficintensityisclosetozero,theaverage queuingdelaywillbeclosetozero.DIfthetrafficintensityisclosetoone,theaverageq ueuingdelaywillbeclosetoone.12.TheInternet’snetwo rklayerisresponsibleformovingne twork-layerpacketsknownas()fromonehosttoanother.A frameB datagramC segmentD message 13.Theprotocolsofvariouslayersarecalled().A theprotocolstackB TCP/IPC ISPD networkprotocol 14.Therearetwoclassesofpacket-switchednetworks:()netw orksandvirtual-circuitnetworks.A datagramB circuit-switchedC televisionD telephone 15.Accessnetworkscanbelooselyclassifiedintothreecateg ories:residentialaccess,companyaccessand()access.A cabledB wirelessC campusD cityareaQuestion16~17Suppose,a istheaveragerateatwhichpacketsarriveatthe queue,Rhan(17).16. A LR/aB LaC RaD LR17.A 2B 1C 0D -118.IntheInternet,theequivalentconcepttoendsystemsis().A hostsB serversC clientsD routers19.IntheInternet,endsystemsareconnectedtogetherby().A copperwireB coaxialcableC communicationlinksD fiberoptics20.EndsystemsaccesstotheInternetthroughits().A modemsB protocolsC ISPD sockets21.Endsystems,packetswitches,andotherpiecesoftheInter net,run()thatcontrolthesendingandreceivingofinformationwithintheInternet.A programsB processesC applicationsD protocols22.Therearemanyprivatenetworks,suchasmanycorporatean dgovernmentnetworks,whosehostscannotexchangemessage 24.TheInternetprovidestwoservicestoitsdistributedapplications:aconnectionlessunreliableserviceand()service.A flowcontrolB connection-orientedreliableC congestioncontrolD TCP25.Itdefinestheformatandtheorderofmessagesexchangedb etweentwoormorecommunicatingentities,aswellastheactionstakenonthetransmissionand/orreceiptofamessageorotherevent.Thesentencedescribes().A InternetB protocolC intranetD network26.Inthefollowingoptions,whichdoesnotdefineinprotocol ()AtheformatofmessagesexchangedbetweentwoormorecommunicatingentitiesBtheorderofmessagesexchangedbetweentwoormorecommunicatingentitiesC theactionstakenonthetransmissionofamessageoro thereventD thetransmissionsignalsaredigitalsignalsoranal ogsignals27.Inthefollowingoptions,whichisdefinedinprotocol?() Atheactionstakenonthetransmissionand/orreceipt ofamessageorothereventB theobjectsexchangedbetweencommunicatingentitiesC thecontentintheexchangedmessagesD thelocationofthehosts 28.Inthefollowingoptions,whichdoesnotbelongtothenetwo rkedge?()A endsystemsB routersC clientsD servers29.Inthefollowingoptions,whichbelongstothenetworkcore ()A endsystemsB routersC clientsD servers30.nternet’A reliabledatatransferBCD31.A flowcontrolB congestion-controlC reliabledatatransferD connection-orientedservice 32.Itmakessurethatneithersideofaconnectionoverwhelmst heothersidebysendingtoomanypacketstoofast.Thesente ncedescribes().A flowcontrolB congestion-controlC connection-orientedserviceD reliabledatatransfer33.IthelpspreventtheInternetfromenteringastateofgridlock.Whenapacketswitchbecomescongested,itsbufferscanoverflowandpacketlosscanoccur.Thesentencedescribes().A flowcontrolB congestion-controlC connection-orientedserviceD reliabledatatransfer34.TheInternet’sconnection-orientedservicehasaname,i tis().A TCPB UDPC TCP/IPD IPA SMTPB internettelephoneC FTPD HTTP38.Inthefollowingoptions,whichdoesnotuseUDP?()A InternetphoneB videoconferencingC streamingmultimediaD telnet39.Therearetwofundamentalapproachestobuildinganetwor kcore,()andpacketswitching.A electricalcurrentswitchingB circuitswitchingC dataswitchingD messageswitching40.In()networks,theresourcesneededalongapathtoprovide forcommunicationbetweentheendsystemarereservedfort hedurationofthecommunicationsession.A packet-switchedB data-switchedC circuit-switchedD message-switched41.In()networks,theresourcesarenotreserved;asession’smessagesusetheresourcesondemand,andasaconsequence ,mayhavetowaitforaccesstocommunicationlink.A packet-switchedB data-switchedC circuit-switchedD message-switched42.Inacircuit-switchednetwork,ifeachlinkhas n circuits, foreachlinkusedbytheend-to-endconnection,theconnec tiongets()ofthelink’sbandwidthfor thedurationofthe connection.A afraction1/nB allC 1/2D ntimes43.For(),thetransmissionrateofacircuitisequaltothefra meratemultipliedbythenumberofbitsinaslot.A CDMAB packet-switchednetworkC TDMD FDM44.()meansthattheswitchmustreceivetheentirepacketbefo eoutboundlink.A QueuingdelayBC PacketlossD Propagation45.ABCD 46.Thenetworkthatforwardspacketsaccordingtovirtual-ci rcuitnumbersiscalled()network.A circuit-switchedB packet-switchedC virtual-circuitD datagram47.Inthefollowingentries,whichisnotakindofaccessnetwo rk?()A residentialaccessB companyaccessC wirelessaccessD localaccess 48.Supposethereisexactlyonepacketswitchbetweenasendin ghostandareceivinghost.Thetransmissionratesbetween thesendinghostandtheswitchandbetweentheswitchandth ereceivinghostare R1and R2,respectively.Assumingthattheswitchusesstore-and-forwardpacketswitching,whatisthetotalend-to-enddelaytosendapacketoflength L?(Ignorequeuingdelay,propagationdelay,andprocessingdelay.)()A L/R1+L/R2B L/R1C L/R2D noneoftheabove51.Considersendingapacketof3000bitsoverapathof5links.Eachlinktransmitsat1000bps.Queuingdelays,propagationde layandprocessingdelayarenegligible.(6points)(1).Supposethenetworkisapacket-switchedvirtualcircuitnetwork.VCsetuptimeis0.1seconds.Supposethesendinglayersaddatotalo f500bitsofheadertoeachpacket.Howlongdoesittaketosendthefilefro msourcetodestination?(2).Supposethenetworkisapacket-switcheddatagramnetworkandaconnectionlessserviceisused.Nowsupposeeachpackethas200bi tsofheader.Howlongdoesittaketosendthefile?(3).Supposethatthenetworkisacircuit-switchednetwork.Furthersupposethatthetransmissionrateofthecircuitbetweensourceandde stinationis200bps.Assuming0.02ssetuptimeand200bitsofheaderappe ndedtothepacket,howlongdoesittaketosendthepacket?Solution:?(1).?t=5*(3000+500)/1000+0.1=17.6s?(2).?t=5*(3000+200)/1000=16s?? (3).?t=(3000+200)/200+0.02=16.02s?? /:。
计算机网络英文答案
Chapter 5 ProblemsProblem 1The rightmost column and bottom row are for parity bits.1 0 1 0 01 0 1 0 01 0 1 0 01 0 1 1 10 0 0 1 1Problem 2Suppose we begin with the initial two-dimensional parity matrix:0 0 0 01 1 1 10 1 0 11 0 1 0With a bit error in row 2, column 3, the parity of row 2 and column 3 is now wrong in the matrix below:0 0 0 01 1 0 10 1 0 11 0 1 0Now suppose there is a bit error in row 2, column 2 and column 3. The parity of row 2 is now correct! The parity of columns 2 and 3 is wrong, but we can't detect in which rows the error occurred!0 0 0 01 0 0 10 1 0 11 0 1 0The above example shows that a double bit error can be detected (if not corrected). Problem 3To compute the Internet checksum, we add up the values at 16-bit quantities: 00000000 0000000100000010 0000001100000100 0000010100000110 0000011100001000 00001001-------------------------00010100 00011001The one's complement of the sum is 11101011 11100110.Problem 4a) To compute the Internet checksum, we add up the values at 16-bit quantities: 00000001 0000001000000011 0000010000000101 0000011000000111 0000100000001001 00001010-------------------------00011001 00011110The one's complement of the sum is 11100110 11100001.b) To compute the Internet checksum, we add up the values at 16-bit quantities: 01000001 0100001001000011 0100010001000101 0100011001000111 0100100001001001 01001010-------------------------01011000 01011111The one's complement of the sum is 10100111 10100000c) To compute the Internet checksum, we add up the values at 16-bit quantities: 01100001 0110001001100011 0110010001100101 0110011001100111 0110011101101000 01101001-------------------------11111001 11111101The one's complement of the sum is 00000110 00000010.Problem 5If we divide 1001 into 10101010000 we get 10111101, with a remainder of R = 101.Problem 6a) If we divide 1001 into 10010001000 we get 10000001, with a remainder of R =001.b) If we divide 1001 into we get 10100011000 we get 10110101, with a remainderof R = 101.c) If we divide 1001 into 010********* we get 010111101, with a remainder of R =101.Problem 7 a)1)1()(--=N p Np p E21)1)(1()1()('------=N N p N Np p N p E ))1()1(()1(2----=-N p p p N NNp p E 1*0)('=⇒=b)NN NN N Np E NN N 11)11()11()11(1*)(11--=-=-=--1)11(lim =-∞→NN eNNN 1)11(lim =-∞→Thusep E N 1*)(lim =∞→Problem 8)1(2)1()(--=N p Np p E)3(2)2(2)1)(1(2)1()('------=N N p N Np p N p E))1(2)1(()1()3(2----=-N p p p N N121*0)('-=⇒=N p p E)1(2)1211(12*)(----=N N N N p Eee p E N 21121*)(lim =⋅=∞→Problem 9a) (1 – p(a))3 p(A) where,p(A) = probability that A succeeds in a slotp(A) = p(A transmits and B does not and C does not)= p(A transmits) p(B does not transmit) p(C does not transmit) = p(1 – p) (1 – p) = p(1 – p)2Hence, p(A succeeds for first time in slot 4) = (1 – p(a))3 p(A) = (1 – p(1 – p)2)3 p(1 – p)2b) p(A succeeds in slot 2) = p(1-p)2 p(B succeeds in slot 2) = p(1-p)2p(C succeeds in slot 2) = p(1-p)2p(either A or B or C succeeds in slot 2) = 3 p(1-p)2 (because these events are mutually exclusive)c) p(some node succeeds in a slot) = 3 p(1-p)2 p(no node succeeds in a slot) = 1 - 3 p(1-p)2Hence, p(first success occurs in slot 4) = p(no node succeeds in first 3 slots) p(some node succeeds in 4th slot) = (1 - 3 p(1-p)2)3 3 p(1-p)2d) efficiency = p(success in a slot) = 3 p(1-p)2Problem 10Problem 11The length of a polling round is)/(poll d R Q N +.The number of bits transmitted in a polling round is NQ . The maximum throughput therefore isQR d R d R Q N NQ poll poll +=+1)/(Problem 12a), b), c) See figure below.d)1. Forwarding table in A determines that the datagram should be routed to interface111.111.111.002.2. The adapter in A creates and Ethernet packet with Ethernet destination address22-22-22-22-22-22.3. The first router receives the packet and extracts the datagram. The forwardingtable in this router indicates that the datagram is to be routed to 122.222.222.003. 4. The first router then sends the Ethernet packet with the destination address of 55-55-55-55-55-55 and source address of 33-33-33-33-33-33 via its interface with IP address of 122.222.222.002.5. The process continues until the packet has reached Host F .e)ARP in A must now determine the LAN address of 111.111.111.002. Host A sends out an ARP query packet within a broadcast Ethernet frame. The first router receives the query packet and sends to Host A an ARP response packet. This ARP response packet is carried by an Ethernet frame with Ethernet destination address 00-00-00-00-00-00.Problem 13a) b) c) See figure below:d)1. Forwarding table in A determines that the datagram should be routed to interface111.111.111.002.2. The adapter in A creates and Ethernet packet with Ethernet destination address22-22-22-22-22-22.3. The router receives the packet and extracts the datagram. The forwarding table inthis router indicates that the datagram is to be routed via interface 122.222.222.002.4. The router then replaces the destination MAC address in the datagram it receivedfrom host A, with the MAC address of F (77-77-77-77-77-77) and sends the datagram over the interface 122.222.222.002.5. The switch (that is connected to the interface 122.222.222.002 of the router)forwards the datagram to its interface where F is connected. The datagram then reaches F.e) ARP in A must now determine the MAC address of 111.111.111.002. Host A sends out an ARP query packet within a broadcast Ethernet frame. The router receives the query packet and sends to Host A an ARP response packet. This ARP response packet is carried by an Ethernet frame with Ethernet destination address 00-00-00-00-00-00.Problem 14Wait for 51,200 bit times. For 10 Mbps, this wait is12.51010102.5163=⨯⨯bpsbits msecFor 100 Mbps, the wait is 512 μsec.Problem 15At 0=t A transmits. At 576=t , A would finish transmitting. In the worst case, B begins transmitting at time 224=t . At time 449225224=+=t B 's first bit arrives at A . Because 576449<, A aborts before completing the transmission of the packet, as it is supposed to do.Thus A cannot finish transmitting before it detects that B transmitted. This implies that if A does not detect the presence of a host, then no other host begins transmitting while A is transmitting.Problem 16Because A 's retransmission reaches B before B 's scheduled retransmission time, B refrains from transmitting while A retransmits. Thus A and B do not collide. Thus the factor 512 appearing in the exponential backoff algorithm is sufficiently large.Problem 17We want 5.)51/(1=+a or, equivalently, trans prop t t a /2.==. )108.1/(8⨯=d t prop m/sec and 576(=trans t bits 810/()bits/sec μ76.5)=sec. Solving for d we obtain 265=d meters. For the 100 Mbps Ethernet standard, the maximum distance between two hosts is 200 m.For transmitting station A to detect whether any other station transmitted during A 's interval, trans t must be greater than 26522⋅=prop t m 8108.1/⨯m/sec μ94.2=sec. Because76.594.2<, A will detect B 's signal before the end of its transmission.a)Let Y be a random variable denoting the number of slots until a success:1)1()(--==m m Y P ββ, where β is the probability of a success.This is a geometric distribution, which has mean β/1. The number of consecutive wasted slots is 1-=Y X thatββ-=-==11][][Y E X E x1)1(--=N p Np β11)1()1(1-----=N N p Np p Np xefficiency 11)1()1(1-----+=+=N N p Np p Np k kxk kb)Maximizing efficiency is equivalent to minimizing x , which is equivalent to maximizingβ. We know from the text that β is maximized at Np 1=.c)efficiency 11)11()11(1-----+=N N N N k k∞→N limefficiency 1/1/11-+=-+=e k k ee k kd) Clearly, 1-+e k k approaches 1 as ∞→k .a)bpsbits m m 681010204sec/102900⨯⋅+⋅sec5.12sec)108105.4(66μ=⨯+⨯=--b)∙ At time 0=t , both A and B transmit.∙ At time sec 5.12μ=t , A detects a collision.∙ At time sec25μ=t last bit of B 's aborted transmission arrives at A .∙At time sec 5.37μ=tfirst bit of A 's retransmission arrives at B .∙ At time sec 5.137********sec 5.376μμ=⨯+=bpsbits t A 's packet is completelydelivered at B .c) sec 5.512sec 1005sec 5.12μμμ=⋅+Problem 20i) from A to left router: Source MAC address: 00-00-00-00-00-00 Destination MAC address: 22-22-22-22-22-22 Source IP: 111.111.111.001 Destination IP: 133.333.333.003ii) from the left router to the right router: Source MAC address: 33-33-33-33-33-33 Destination MAC address: 55-55-55-55-55-55 Source IP: 111.111.111.001 Destination IP: 133.333.333.003iii) from the right router to F: Source MAC address: 88-88-88-88-88-88Destination MAC address: 99-99-99-99-99-99Source IP: 111.111.111.001Destination IP: 133.333.333.003Problem 21i) from A to switch: Source MAC address: 00-00-00-00-00-00Destination MAC address: 55-55-55-55-55-55Source IP: 111.111.111.001Destination IP: 133.333.333.003ii) from switch to right router: Source MAC address: 00-00-00-00-00-00Destination MAC address: 55-55-55-55-55-55Source IP: 111.111.111.001Destination IP: 133.333.333.003iii) from right router to F: Source MAC address: 88-88-88-88-88-88Destination MAC address: 99-99-99-99-99-99Source IP: 111.111.111.001Destination IP: 133.333.333.003Problem 22If all the 14 nodes send out data at the maximum possible rate of 100 Mbps, a total aggregate throughput of 14*100 = 1400 Mbps is possible.Problem 23Each departmental hub is a single collision domain that can have a maximum throughput of 100 Mbps. The links connecting the web server and the mail server has a maximum throughput of 100 Mbps. Hence, if the three collision domains and the web server and mail server send out data at their maximum possible rates of 100 Mbps each, a maximum total aggregate throughput of 500 Mbps can be achieved among the 14 end systems.Problem 24All of the 14 end systems will lie in the same collision domain. In this case, the maximum total aggregate throughput of 100 Mbps is possible among the 14 end sytems.Problem 25Problem 26The time required to fill 8⋅L bits is.sec 8sec 106483m L L =⨯⋅b) For ,500,1=L the packetization delay is.sec 5.187sec 81500m m =For ,48=L the packetization delay is.sec 6sec 848m m =c)Store-and-forward delay R L 408+⋅=For 500,1=L , the delay issec 77sec 15512sec 1015540815006μ≈≈⨯+⋅mFor ,48=L store-and-forward delay sec 1μ<.d) Store-and-forward delay is small for both cases for typical ATM link speeds. However, packetization delay for 1500=L is too large for real-time voice applications.Problem 27Problem 28Chapter 6 Review Questions1.In infrastructure mode of operation, each wireless host is connected to the largernetwork via a base station (access point). If not operating in infrastructure mode, a network operates in ad-hoc mode. In ad-hoc mode, wireless hosts have noinfrastructure with which to connect. In the absence of such infrastructure, thehosts themselves must provide for services such as routing, address assignment,DNS-like name translation, and more.2.a) Single hop, infrastructure-basedb) Single hop, infrastructure-lessc) Multi-hop, infrastructure-basedd) Multi-hop, infrastructure-less3.Path loss is due to the attenuation of the electromagnetic signal when it travelsthrough matter. Multipath propagation results in blurring of the received signal at the receiver and occurs when portions of the electromagnetic wave reflect offobjects and ground, taking paths of different lengths between a sender andreceiver. Interference from other sources occurs when the other source is alsotransmitting in the same frequency range as the wireless network.4.a) Increasing the transmission powerb) Reducing the transmission rate5.APs transmit beacon frames. An AP‟s beacon frames will be transmitted over oneof the 11 channels. The beacon frames permit nearby wireless stations to discover and identify the AP.6.False7.APs transmit beacon frames. An AP‟s beacon frames will be transmitted over oneof the 11 channels. The beacon frames permit nearby wireless stations to discover and identify the AP.8.False9.Each wireless station can set an RTS threshold such that the RTS/CTS sequenceis used only when the data frame to be transmitted is longer than the threshold.This ensures that RTS/CTS mechanism is used only for large frames.10.No, there would n‟t be any advantage. Suppose there are two stations that want totransmit at the same time, and they both use RTS/CTS. If the RTS frame is as long as a DATA frames, the channel would be wasted for as long as it would have been wasted for two colliding DATA frames. Thus, the RTS/CTS exchange is only useful when the RTS/CTS frames are significantly smaller than the DATA frames.11.Initially the switch has an entry in its forwarding table which associates thewireless station with the earlier AP. When the wireless station associates with the new AP, the new AP creates a frame with the wireless station‟s MAC address and broadcasts the frame. The frame is received by the switch. This forces the switch to update its forwarding table, so that frames destined to the wireless station are sent via the new AP.12.Any ordinary Bluetooth node can be a master node whereas access points in802.11 networks are special devices (normal wireless devices like laptops cannot be used as access points).13.False14.“Opportunistic Scheduling” refers to matching the physical layer protocol tochannel conditions between the sender and the receiver, and choosing the receivers to which packets will be sent based on channel condition. This allows the base station to make best use of the wireless medium.15.UMTS to GSM and CDMA-2000 to IS-95.16.No. A node can remain connected to the same access point throughout itsconnection to the Internet (hence, not be mobile). A mobile node is the one that changes its point of attachment into the network over time. Since the user is always accessing the Internet through the same access point, she is not mobile. 17.A permanent address for a mobile node is its IP address when it is at its homenetwork. A care-of-address is the one its gets when it is visiting a foreign network.The COA is assigned by the foreign agent (which can be the edge router in the foreign network or the mobile node itself).18.False19.The home network in GSM maintains a database called the home location register(HLR), which contains the permanent cell phone number and subscriber profile information about each of its subscribers. The HLR also contains information about the current locations of these subscribers. The visited network maintains a database known as the visitor location register (VLR) that contains an entry for each mobile user that is currently in the portion of the network served by the VLR.VLR entries thus come and go as mobile users enter and leave the network.The edge router in home network in mobile IP is similar to the HLR in GSM and the edge router in foreign network is similar to the VLR in GSM.20. Anchor MSC is the MSC visited by the mobile when a call first begins; anchorMSC thus remains unchanged during the call. Throughout the call‟s duration and regardless of the number of inter-MSC transfers performed by the mobile, the call is routed from the home MSC to the anchor MSC, and then from the anchor MSC to the visited MSC where the mobile is currently located.21. a) Local recoveryb) TCP sender awareness of wireless linksc) Split-connection approachesChapter 6 ProblemsProblem 1.Output corresponding to bit d 1 = [-1,1,-1,1,-1,1,-1,1]Output corresponding to bit d 0 = [1,-1,1,-1,1,-1,1,-1]Problem 2.Sender 2 output = [1,-1,1,1,1,-1,1,1]; [ 1,-1,1,1,1,-1,1,1]Problem 3.181111)1()1(111111)1()1(1112=⨯+⨯+-⨯-+⨯+⨯+⨯+-⨯-+⨯=d 181111)1()1(111111)1()1(1122=⨯+⨯+-⨯-+⨯+⨯+⨯+-⨯-+⨯=dProblem 4Sender 1: (1, 1, 1, -1, 1, -1, -1, -1)Sender 2: (1, -1, 1, 1, 1, 1, 1, 1)Problem 5a) The two APs will typically have different SSIDs and MAC addresses. A wirelessstation arriving to the café will associate with one of the SSIDs (that is, one of the APs). After association, there is a virtual link between the new station and the AP. Label the APs AP1 and AP2. Suppose the new station associates with AP1. When the new station sends a frame, it will be addressed to AP1. Although AP2 will also receive the frame, it will not process the frame because the frame is not addressed to it. Thus, the two ISPs can work in parallel over the same channel. However, the two ISPs will be sharing the same wireless bandwidth. If wireless stations in different ISPs transmit at the same time, there will be a collision. For 802.11b, the maximum aggregate transmission rate for the two ISPs is 11 Mbps.b)Now if two wireless stations in different ISPs (and hence different channels)transmit at the same time, there will not be a collision. Thus, the maximum aggregate transmission rate for the two ISPs is 22 Mbps for 802.11b.Problem 6Suppose that wireless station H1 has 1000 long frames to transmit. (H1 may be an AP that is forwarding an MP3 to some other wireless station.) Suppose initially H1 is the only station that wants to transmit, but that while half-way through transmitting its first frame, H2 wants to transmit a frame. For simplicity, also suppose every sta tion can hear every other station‟s signal (that is, no hidden terminals). Before transmitting, H2 will sense that the channel is busy, and therefore choose a random backoff value.Now suppose that after sending its first frame, H1 returns to step 1; that is, it waits a short period of times (DIFS) and then starts to transmit the second frame. H1‟s second frame will then be transmitted while H2 is stuck in backoff, waiting for an idle channel. Thus, H1 should get to transmit all of its 1000 frames before H2 has a chance to access the channel. On the other hand, if H1 goes to step 2 after transmitting a frame, then it too chooses a random backoff value, thereby giving a fair chance to H2. Thus, fairness was the rationale behind this design choice.Problem 7A frame without data is 32 bytes long. Assuming a transmission rate of 11 Mbps, thetime to transmit a control frame (such as an RTS frame, a CTS frame, or an ACK frame) is (256 bits)/(11 Mbps) = 23 usec. The time required to transmit the data frame is (8256 bits)/(11 Mbps) = 751DIFS + RTS + SIFS + CTS + SIFS + FRAME + SIFS + ACK= DIFS + 3SIFS + (3*23 + 751) usec = DIFS + 3SIFS + 820 usecProblem 8a) 1 message/ 2 slotsb) 2 messages/slotc) 1 message/slotd)i) 1 message/slotii) 2 messages/slotiii) 2 messages/slote)i) 1 message/4 slotsii) slot 1: Message A→ B, message D→ Cslot 2: Ack B→ Aslot 3: Ack C→ D= 2 messages/ 3 slotsiii)slot 1: Message C→ Dslot 2: Ack D→C, message A→ BRepeatslot 3: Ack B→ A= 2 messages/3 slotsProblem 10a)10 Mbps if it only transmits to node A. This solution is not fair since only A isgetting served. By “fair” it means that each of the four nodes should be allotted equal number of slots.b)For the fairness requirement such that each node receives an equal amount of dataduring each downstream sub-frame, let n1, n2, n3, and n4 respectively represent the number of slots that A, B, C and D get.Now,data transmitted to A in 1 slot = 10t Mbits(assuming the duration of each slot to be t)Hence,Total amount of data transmitted to A (in n1 slots) = 10t n1Similarly total amounts of data transmitted to B, C, and D equal to 5t n2, 2.5t n3, and t n4 respectively.Now, to fulfill the given fairness requirement, we have the following condition:10t n1 = 5t n2 = 2.5t n3 = t n4Hence,n2 = 2 n1n3 = 4 n1n4 = 10 n1Now, the total number of slots is N. Hence,n1+ n2+ n3+ n4 = Ni.e. n1+ 2 n1 + 4 n1 + 10 n1 = Ni.e. n1 = N/17Hence,n2 = 2N/17n3 = 4N/17n4 = 10N/17The average transmission rate is given by:(10t n1+5t n2+ 2.5t n3+t n4)/tN= (10N/17 + 5 * 2N/17 + 2.5 * 4N/17 + 1 * 10N/17)/N= 40/17 = 2.35 Mbpsc)Let node A receives twice as much data as nodes B, C, and D during the sub-frame.Hence,10tn1 = 2 * 5tn2 = 2 * 2.5tn3 = 2 * tn4i.e. n2 = n1n3 = 2n1n4 = 5n1Again,n1 + n2 + n3 + n4 = Ni.e. n 1+ n1 + 2n1 + 5n1 = Ni.e. n1 = N/9Now, average transmission rate is given by:(10t n1+5t n2+ 2.5t n3+t n4)/tN= 25/9 = 2.78 MbpsSimilarly, considering nodes B, C, or D receive twice as much data as any othernodes, different values for the average transmission rate can be calculated. Problem 11a)No. All the routers might not be able to route the datagram immediately. This isbecause the Distance Vector algorithm (as well as the inter-AS routing protocols like BGP) is decentralized and takes some time to terminate. So, during the time when the algorithm is still running as a result of advertisements from the new foreign network, some of the routers may not be able to route datagrams destined to the mobile node.b)Yes. This might happen when one of the nodes has just left a foreign network andjoined a new foreign network. In this situation, the routing entries from the oldforeign network might not have been completely withdrawn when the entries from the new network are being propagated.c)The time it takes for a router to learn a path to the mobile node depends on thenumber of hops between the router and the edge router of the foreign network for the node.Problem 12If the correspondent is mobile, then any datagrams destined to the correspondent would have to pass through the correspondent’s home agent. The foreign agent in the network being visited would also need to be involved, since it is this foreign agent that notifies the correspondent‟s home agent of the location of the correspond ent. Datagrams received by the correspondent‟s home agent would need to be encapsulated/tunneled between the correspondent‟s home agent and foreign agent, (as in the case of the encapsulated diagram at the top of Figure 6.23.Problem 13Because datagrams must be first forward to the home agent, and from there to the mobile, the delays will generally be longer than via direct routing. Note that it is possible, however, that the direct delay from the correspondent to the mobile (i.e., if the datagram is not routed through the home agent) could actually be smaller than the sum of the delayfrom the correspondent to the home agent and from there to the mobile. It would depend on the delays on these various path segments. Note that indirect routing also adds a home agent processing (e.g., encapsulation) delay.Problem 14First, we note that chaining was discussed at the end of section 6.5. In the case of chaining using indirect routing through a home agent, the following events would happen: ∙The mobile node arrives at A, A notifies the home agent that the mobile is now visiting A and that datagrams to the mobile should now be forwarded to thespecified care-of-address (COA) in A.∙The mobile node moves to B. The foreign agent at B must notify the foreign agent at A that the mobile is no longer resident in A but in fact is resident in Band has the specified COA in B. From then on, the foreign agent in A willforward datagrams it receives that are addressed to the mobile‟s COA in A to themobile‟s COA in B.∙The mobile node moves to C. The foreign agent at C must notify the foreign agent at B that the mobile is no longer resident in B but in fact is resident in C and has the specified COA in C. From then on, the foreign agent in B will forwarddatagrams it receives (from the foreign agent in A) that are addressed to themobile‟s COA in B to the mobile‟s COA in C.Note that when the mobile goes offline (i.e., has no address) or returns to its home network, the datagram-forwarding state maintained by the foreign agents in A, B and C must be removed. This teardown must also be done through signaling messages. Note that the home agent is not aware of the mobile‟s mobility beyond A, and that the correspondent is not at all aware of the mobile‟s mobility.In the case that chaining is not used, the following events would happen: ∙ The mobile node arrives at A, A notifies the home agent that the mobile is now visiting A and that datagrams to the mobile should now be forwarded to thespecified care-of-address (COA) in A.∙The mobile node moves to B. The foreign agent at B must notify the foreign agent at A and the home agent that the mobile is no longer resident in A but infact is resident in B and has the specified COA in B. The foreign agent in A canremove its state about the mobile, since it is no longer in A. From then on, thehome agent will forward datagrams it receives that are addressed to the mobile‟sCOA in B.∙The mobile node moves to C. The foreign agent at C must notify the foreign agent at B and the home agent that the mobile is no longer resident in B but in fact is resident in C and has the specified COA in C. The foreign agent in B canremove its state about the mobile, since it is no longer in B. From then on, thehome agent will forward datagrams it receives that are addressed to the mobile‟sCOA in C.When the mobile goes offline or returns to its home network, the datagram-forwarding state maintained by the foreign agent in C must be removed. This teardown must also bedone through signaling messages. Note that the home agent is always aware of the mobile‟s current foreign network. However, the correspondent is still blissfully unaware of the mobile‟s mobility.Problem 15Two mobiles could certainly have the same care-of-address in the same visited network. Indeed, if the care-of-address is the address of the foreign agent, then this address would be the same. Once the foreign agent decapsulates the tunneled datagram and determines the address of the mobile, then separate addresses would need to be used to send the datagrams separately to their different destinations (mobiles) within the visited network.Problem 16If the MSRN is provided to the HLR, then the value of the MSRN must be updated in the HLR whenever the MSRN changes (e.g., when there is a handoff that requires the MSRN to change). The advantage of having the MSRN in the HLR is that the value can be provided quickly, without querying the VLR. By providing the address of the VLR Rather than the MSRN), there is no need to be refreshing the MSRN in the HLR.Chapter 7 Review Questions1.Streaming stored audio/video: pause/resume, re-positioning, fast-forward; real-timeinteractive audio and video: people communicating and responding in real time.2.Camp 1: No fundamental changes in TCP/IP protocols; add bandwidth where needed;also use caching, content distribution networks, and multicast overlay networks.Camp 2: Provide a network service that allows applications to reserve bandwidth in the network. Camp 3, differentiated service: introduce simple classifying and policing schemes at the edge of the network, and give different datagrams different levels of service according to their class in the router queues.3.Uncompressed audio stored on CD has a bit rate of 1411.2 Kbps. mp3 files aretypically encoded in 128 Kbps or less, thereby giving them a compression ratio of almost 11. Image compression ratios are in the range of 10 to 100.4.Figure 6.1: simple, doesn‟t require meta file or streaming server; Figure 6.2: allowsmedia player t o interact directly with the web server, doesn‟t require a streaming server; Figure 6.3: media player interacts directly with a streaming server, which has been designed for the specific streaming application.5.End-to-end delay is the time it takes a packet to travel across the network from sourceto destination. Delay jitter is the fluctuation of end-to-end delay from packet to the next packet.6. A packet that arrives after its scheduled play out time can not be played out.Therefore, from the perspective of the application, the packet has been lost.7.First scheme: send a redundant encoded chunk after every n chunks; the redundantchunk is obtained by exclusive OR-ing the n original chunks. Second scheme: send a lower-resolution low-bit rate scheme along with the original stream. Interleaving does not increase the bandwidth requirements of a stream.8.The role of the DNS is to forward HTTP requests to DNS server managed by theCDN, which in turn redirects the request to an appropriate CDN server. The DNS does not have to be modified to support a CDN. A CDN should provide DNS with the host name and IP address of its authoritative name server (See Section 2.5.3).9.a)Models of traffic demand between network end pointsb)Well-defined performance requirementsc)Models to predict end-end performance for a given workload model, andtechniques to find a minimal high cost bandwidth allocation that will result in all user requirements being met.。
计算机网络英文版——提供给学生部分习题答案
计算机⽹络英⽂版——提供给学⽣部分习题答案Solution of Selected Exercises from the End of Chapter ExercisesChapter 1 - Introduction And Overview1.4 To what aspects of networking does data communications refer?Answer:Data communications refers to the study of low-level mechanisms and technologies used to send information acrossa physical communication medium, such as a wire, radio wave, or light beam.1.5 What is packet-switching, and why is packet switching relevant to the Internet?Answer: Packet switching divides data into small blocks, called packets, and includes an identification of the intended recipient in each packet. Packet switching changed networking in a fundamental way, and provided the basis for the modern Internet. Packet switching allows multiple senders to transmit data over a shared network.1.8 What is a communication protocol? Conceptually, what two aspects of communication does a protocol specify? Answer: A communication protocol refer to a specification for network communication.Major aspects of a protocol are syntax (format) and semantics (meaning) of the protocol.1.9 What is a protocol suite, and what is the advantage of a suite?Answer:protocols are designed in complete, cooperative sets called suites or families, instead of creating each protocol in isolation. Each protocol in a suite handles one aspect of communication; together, the protocols in a suite cover all aspects of communication. The entire suite is designed to allow the protocols to work together efficiently. 1.11 List the layers in the TCP/IP model, and give a brief explanation of each.(See Textbook)1.14 Give a brief explain of the layers in the ISO Open System Interconnection model.(See Textbook)Chapter 3 - Internet Applications And Network Programming3.1 What are the two basic communication paradigms used in the Internet?Answer: There are various approaches, but according to textbook, we can specify them as Stream Paradigm and Message Paradigm.3.2 Give six characteristics of Internet stream communication.(See Textbook)3.3 Give six characteristics of Internet message communication.(See Textbook)3.4 If a sender uses the stream paradigm and always sends 1024 bytes at a time, what size blocks can the Internet deliverto a receiver?Answer: stream paradigm does not provide any guarantees for block sizes, so all depends on individual transfer.3.6 What are the three surprising aspects of the Internet’s message delivery semantics?Answer:The Internet’s message delivery has the followi ng undesirable characteristics:* Messages can be lost* Messages can be duplicated* Messages can be delivered out-of-order3.8 When two applications communicate over the Internet, which one is the server?Answer: T he application that waits for some other applications to contact is called server, and the application that contact other one is called client.3.14 What two identifiers are used to specify a particular server?Answer: A particular server is identified by the following identifiers:* An identifier for the computer on which a server runs (IP Address)* An identifier for a particular service on the computer (Port Number)Chapter 4 - Traditional Internet Applications4.1 What details does an application protocol specify?(See Textbook)4.3 What are the two key aspects of application protocols, and what does each include?(See Textbook)4.6 What are the four parts of a URL, and what punctuation is used to separate the parts?Answer: The URL into four components: a protocol, a computer name, a document name, and parameters. The computer name and protocol port are used to form a connection to the server on which the page resides. And the document name and parameters are used to request a specific page.4.7 What are the four HTTP request types, and when is each used?(See Textbook)4.12 When a user requests an FTP directory listing, how many TCP connections are formed? Explain.Answer: FTP uses two types of connections to perform its functionality, namely* A control connection is reserved for commands. Each time the server needs to download or upload a file, the server opens a new connection.* A data connection is used to transfer files.4.16 List the three types of protocols used with email, and describe each.(See Textbook)4.17 What are the characteristics of SMTP?(See Textbook)4.20 What are the two main email access protocols?Answer: Two major email access protocols are:* Post Office Protocol (POP)* Internet Mail Access Protocol (IMAP)Chapter 6- Information Sources and Signals6.4 State and describe the four fundamental characteristics of a sine wave.(See Textbook)6.9 What is the analog bandwidth of a signal?Answer: Analog bandwidth of signal can be defined as to be the difference between the highest and lowest frequencies of the constituent parts (i.e., the highest and lowest frequencies obtained by Fourier analysis)6.11 Suppose an engineer increases the number of possible signal levels from two to four. How many more bits can be sent in the same amount of time? Explain.Answer: The number of levels that can be represented by n bits is given by 2n . So if number of levels changes from 2→4, it means number of bits goes from 1→2612. What is the definition of baud?Answer: Baud is defined as the number of times that a signal can change per second.6.14 What is the bandwidth of a digital signal? Explain.Answer: According to the definition of analog bandwidth, a digital signal has infinite bandwidth because Fourier analysis of a digital signal produces an infinite set of sine waves with frequencies that grow to infinity.6.18 What is the chief advantage of a Differential Manchester Encoding?Answer: The most important property of differential encoding is that the encoding works correctly even if the two wires carrying the signal are accidentally reversed.6.20 If the maximum frequency audible to a human ear is 20,000 Hz, at what rate must the analog signal from a microphone be sampled when converting it to digital?Answer: The sampling rate = 2 × f max, so the signal should be sampled at 2x20,000 = 40,000 HzChapter 7 - Transmission Media7.2 What are the three energy types used when classifying physical media according to energy used?Answer: Three types of energy used when classifying physical media are electrical, electromechanical (radio), and light7.4 What three types of wiring are used to reduce interference form noise?(See Textbook)7.10 List the three forms of optical fiber, and give the general properties of each.(See Textbook)7.21 What is the relationship between bandwidth, signal levels, and data rate?Answer: If a transmission system uses K possible signal levels and has an anal og bandwidth B, Nyquist’s Theorem states that the maximum data rate in bits per second, D, is: D = 2 B log2K7.22 If two signal levels are used, what is the data rate that can be sent over a coaxial cable that has an analog bandwidthof 6.2 MHz?Answer: Using the D= 2 B log2 K relationship, D = 2*6.2*log22 = 2*6.2*1 = 12.4 Mbps7.24 If a system has an input power level of 9000, and an output power level of 3000, what is the difference when expressed in dB?Answer: Decibel is expressed as 10log10(P out/P in) → 10log10(3,000/9,000) = to be determined by reader7.23 If a system has an average power level of 100, an average noise level of 33.33, and a bandwidth of 100 MHz, whatis the effective limit on channel capacity?Answer: Shannon theorem specify the maximum data rate that could be achieved over a transmission system that experiences noise: C = Blog2 (1 + S/N) = 100,000,000 * log2 (1 + 100/33.33) = 100,000,000 * log24 = 200,000,000 = 200 Mbps7.25 If a telephone system can be created with a signal-to-noise ratio of 40 dB and an analog bandwidth of 3000 Hz, how many bits per second could be transmitted?Answer: First we should convert 40 dB to a real number, namely if 40 = 10 log10S/N→S/N = 10,000 , Using the Shannon’s capacity expression C = B log2(1 + S/N) → C = 3,000 log2 (1+ 10,000) = to be determined by readerCh 8 - Reliability And Channel Coding8.1 List and explain the three main sources of transmission errors.(See Textbook)8.3 In a burst error, how is burst length measured?Answer: For a burst error, the burst size, or length, is defined as the number of bits from the start of the corruption to the end of the corruption.8.4 What is a codeword?Answer: We can define the set of all possible messages to be a set of datawords, and define the set of all possible encoded versions to be a set of codewords. So each possible code sequence is considered to be a codeword.8.8 Compute the Hamming distance for the following pairs: (0000, 0001), (0101, 0001), (1111, 1001), and ( 0001, 1110). (See Textbook)8.11 Generate a RAC parity matrix for a (20, 12) coding of the dataword 100011011111.(See Textbook)8.15 Express the two values in the previous exercise as polynomials.Answer:X10+ X7 + X5 + X3 + XX4+ X2+ 1Ch 9 - Transmission Modes9.1 Describe the difference between serial and parallel transmission.Answer: Transmission modes can be divided into two fundamental categories:* Serial: one bit is sent at a time* Parallel: multiple bits are sent at the same time9.2 What are the advantages of parallel transmission? What is the chief disadvantage?Answer: A parallel mode of transmission has two chief advantages:* High speed: Because it can send N bits at the same time, a parallel interface can operate N times faster than an equivalent serial interface.* Match to underlying hardware: Internally, computer and communication hardware uses parallel circuitry.Thus, a parallel interface matches the internal hardware well.The main disadvantage of parallel transmission is number of cables required, for long distance communication, this is an important consideration.9.4 What is the chief characteristic of asynchronous transmission?Answer:Asynchronous transmission can occur at any time, with an arbitrary delay between the transmission of two data items, it allows the physical medium to be idle for an arbitrary time between two transmissions.Chapter 11 - Multiplexing And Demultiplexing11.2 What are the four basic types of multiplexing?(See Textbook)11.4 What is a guard band?Answer: For proper communication without interference, we should choose a set of carrier frequencies with a gap between them known as a guard band. The guard band reduces or eliminates the possible interference between neighboring carrier signals.11.8 Explain how a range of frequencies can be used to increase data rate.Answer:To increase the overall data rate, a sender divides the frequency range of the channel into K carriers, and sends 1 /K of the data over each carrier.11.12 Suppose N users compete using a statistical TDM system, and suppose the underlying physical transport can sendK bits per second. What is the minimum and maximum data rate that an individual user can experience?Answer: If we neglect the overhead generated by statistical TDM, a system will have two possibilities: * Minimum: If all channels have equal data then the rate will be K/N bps* Maximum: If only one channel active and the others are passive, then rate will be K bpsChapter 13 - Local Area Networks: Packets, Frames, And Topologies13.1 What is circuit switching, and what are its chief characteristics?Answer: The term circuit switching refers to a communication mechanism that establishes a path between a sender and receiver with guaranteed isolation from paths used by other pairs of senders and receivers. The circuit switching has the following main characteristics:* Point-to-point communication* Separate steps for circuit creation, use, and termination* Performance equivalent to an isolated physical path13.3 In a packet switching system, how does a sender transfer a large file?Answer: The packet switching system requires a sender to divide each message into blocks of data that are known as packets . The size of a packet varies; each packet switching technology defines a maximum packet size. So, a large file will be divided into smaller pieces and sent.13.5 What are the characteristics of LANs, MANs, and W ANs?Answer: There are lots of details that can be said and discussed for categorization of network types based on geography, few points are highlighted below:* Local Area Network (LAN): Least expensive; spans a single room or a single building* Metropolitan Area Network (MAN) Medium expense; spans a major city or a metroplex* Wide Area Network (WAN) Most expensive; spans sites in multiple cities13.6 Name the two sublayers of Layer 2 protocols defined by IEEE, and give the purpose of each.Answer: The Layer 2 protocols defined by IEEE defines two sub-layers as mentioned below:* Logical Link Control (LLC) Addressing and demultiplexing* Media Access Control (MAC) Access to shared media13.8 What are the four basic LAN topologies?Answer: The four basic LAN topologies are star, ring, mesh and bus.13.10 In a mesh network, how many connections are required among 20 computers?Answer: The expression to calculate number of connections in a mesh network is given by n (n-1)/2. So for 20 computers then number of connections required will be = 20 (20 – 1)/2 =19013.15 Give a definition of the term frame .Answer: In a packet-switched network, each frame corresponds to a packet processed at data link layer.Chapter 14 - The IEEE MAC Sub-Layer14.1 Explain the three basic approaches used to arbitrate access to a shared medium.(See Textbook)14.3 List the three main types of channelization and the characteristics of each.(See Textbook)14.6 What is a token, and how are tokens used to control network access?Answer: A special control message is called a token. In a token passing system, when no station has any packets to send, the token circulates among all stations continuously. When a station captures the token, it sends its data, and when transmission completed, it releases the token.14.8 Expand the acronym CSMA/CD, and explain each part.Answer: The acronym CSMA/CD stands for Carrier Sense Multi-Access with Collision Detection, which means the following: * Carrier Sense: Instead of allowing a station to transmit whenever a packet becomes ready, Ethernet requires each station to monitor the cable to detect whether another transmission is already in progress.* Multiple Access: The system allows multiple users/hosts to make use of a common/shared media* Collision Detection. A collision can occur if two stations wait for a transmission to stop, find the cable idle, and both start transmitting.14.10 Why does CSMA/CD use a random delay? (Hint: think of many identical computers on a network.)Answer: Randomization is used to avoid having multiple stations transmit simultaneously as soon as the cable is idle.That is, the standard specifies a maximum delay, d, and requires each station to choose a random delay less than d after a collision occurs. In most cases, when two stations each choose a random value, the station that chooses the smallest delay willChapter 15 - Wired LAN Technology (Ethernet And 802.3)15.1 How large is the maximum Ethernet frame, including the CRC?Answer: According to Fig. 15.1 a conventional Ethernet frame has the following fields:* Header: 14 bytes (fixed)* Payload: 46-1500 bytes (there is a minimum frame size because of collision detection)* CRC: 4 bytes (fixed)Accordingly an Ethernet frame will be maximum 1518 bytes and minimum 64 bytes15.3 In an 802.3 Ethernet frame, what is the maximum payload size?Answer: The 802.3 Ethernet makes use of 8-bytes of the original/conventional Ethernet for Logical Link Control / Sub-Network Attachment Point (LLC / SNAP) header instead of extending/increasing the header. This is for sake of backward compatibility. So the maximum pay load is reduced from 1500 bytes to 1492 bytes.15.6 How did a computer attach to a Thicknet Ethernet?Answer: Hardware used with Thicknet was divided into two major parts:* Transceiver: A network interface card (NIC) handled the digital aspects of communication, and a separate electronic device called a transceiver connected to the Ethernet cable and handled carrier detection, conversion of bits into appropriate voltages for transmission, and conversion of incoming signals to bits.* AUI: A physical cable known as an Attachment Unit Interface (AUI) connected a transceiver to a NIC in a computer. A transceiver was usually remote from a computer.15.7 How were computers attached to a Thinnet Ethernet?Answer: Thinnet Ethernet (formally named 10Base2) uses a thinner coaxial cable that was more flexible than Thicknet. The wiring scheme differed dramatically from Thicknet. Instead of using AUI connections between a computer and a transceiver, Thinnet integrates a transceiver directly on the NIC, and runs a coaxial cable from one computer to another.15.8 What is an Ethernet hub, and what wiring is used with a hub?Answer: An electronic device that serves as the central interconnection is known as a hub. Hubs were available in a variety of sizes, with the cost proportional to size. The hubs are becoming old-fashioned, and being replaced with switches.15.3 What category of twisted pair wiring is needed for a 10 Mbps network? 100 Mbps? 1000 Mbps?Answer: The three major categories of Ethernet and their wiring is listed below:* 10 Mbps: 10BaseT (Ethernet) Category 5* 100 Mbps: 100BaseT (Ethernet Fast) Category 5E* 1 Gbps: 1000BaseT (Gigabit Ethernet) Category 6Chapter 20 - Internetworking: Concepts, Architecture, and Protocols20.2 Will the Internet be replaced by a single networking technology? Why or why not?Answer: Incompatibilities make it impossible to form a large network merely by interconnecting the wires among networks. The beauty of the Internet is interconnection of wide range of technologies from various manufacturers.Diversity of the products and solutions is a richness instead of limitation as long as they all adopt the same set of protocols.20.3 What are the two reasons an organization does not use a single router to connect all its networks?Answer:An organization seldom uses a single router to connect all of its networks. There are two major reasons: * Because the router must forward each packet, the processor in a given router is insufficient to handle the traffic passing among an arbitrary number of networks.* Redundancy improves internet reliability. To avoid a single point of failure, protocol software continuously monitors internet connections and instructs routers to send traffic along alternative paths when a network or router fails.20.6 In the 5-layer reference model used with the TCP/IP Internet protocols, what is the purpose of each of the five layers?(See 1.11)Chapter 21- IP: Internet Addressing21.3 In the original classful address scheme, was it possible to determine the class of an address from the address itself? Explain.Answer:Yes, since in the classful addressing scheme initial bit(s) gives indication about the class being used.21.7 If an ISP assigned you a /28 address block, how many computers could you assign an address?Answer: When an organization is assigned /28 CIDR address, it means 28 bits out of 32 bits are fixed, so 32-28 = 4 bits available for user space. So number of users 24-2 = 4, since the all 0s and all 1s address are having special use and can’t be assigned to a user.21.8 If an ISP offers a / 17 address block for N dollars per month and a / 16 address block for 1.5 N dollars per month,which has the cheapest cost per computer?Answer: Number of addresses in /17 block 232-17 = 215Price per address: N /215 = N / 215Number of addresses in /16 block 232-16 = 216Price per address: 1.5N /216 = 0.75N/215 So /16 address block will be cheaper in comparison with the price given for /17 block.21.10 Suppose you are an ISP with a / 24 address block. Explain whether you accommodate a request from a customer who needs addresses for 255 computers. (Hint: consider the special addresses.)Answer: For a/24 address block, number of available addresses will be 232-24 = 28 = 256. However, a suffix with all 0s address is reserved for network ID and a suffix with all 1s address is reserved for broadcast address, so number of addresses that can be assigned to computers/hosts will be 256 -2 = 254.21.11 Suppose you are an ISP that owns a / 22 address block. Show the CIDR allocation you would use to allocateaddress blocks to four customers who need addresses for 60 computers each.Answer: The /22 address block can be assigned as follows:ddd.ddd.ddd.00/26ddd.ddd.ddd.01/26ddd.ddd.ddd.10/26ddd.ddd.ddd.11/26Chapter 22- Datagram Forwarding22.1 What are the two basic communication paradigms that designers consider when designing an internet?Answer:* Connection-oriented service * Connectionless service22.2 How does the Internet design accommodate heterogeneous networks that each have their own packet format?Answer: To overcome heterogeneity, the Internet Protocol defines a packet format that is independent of the underlying hardware. The result is a universal, virtual packet that can be transferred across the underlying hardware intact. The Internet packet format is not tied directly to any hardware. The underlying hardware does not understand or recognize an Internet packet.22.5 What is the maximum length of an IP datagram?In the current version of the Internet Protocol (IP version 4), a datagram can contain at most 64 K (65535) octets, including the header.22.7 If a datagram contains one 8-bit data value and no header options, what values will be found in header fields H.LEN and TOTAL LENGTH?Answer: H. LEN indicated header in 32-quantities, since no options, then this value will be 5. The TOTAL LENGTH indicated the number of bytes in a datagram including the header. This means 5x4 bytes + 1 (8-bits) = 21 bytesChapter 23 - Support Protocols And Technologies23.1 When a router uses a forwarding table to look up a next-hop address, the result is an IP address. What must happenbefore the datagram can be sent?Answer: Each router along the path uses the destination IP address in the datagram to select a next-hop address, encapsulates the datagram in a hardware frame, and transmits the frame across one network. A crucial step of the forwarding process requires a translation: forwarding uses IP addresses, and a frame transmitted across a physical network must contain the MAC address of the next hop.23.2 What term is used to describe the mapping between a protocol address and a hardware address?Answer: Translation from a computer’s IP address to an equivalent hardware address is known as address resolution, and an IP address is said to be resolved to the correct MAC address. The TCP/IP protocol being used for this is called Address Resolution Protocol (ARP). Address resolution is local to a network.23.5 How many octets does an ARP message occupy when used with IP and Ethernet addresses?Answer: According to Fig 23.3 an ARP message has 7-lines of each being 32-bit (4 bytes or octets), therefore,number of octets in an ARP can be determined as 7x4 = 28 octets23.10 What types of addresses are used in layers below ARP?Answer:ARP forms a conceptual boundary in the protocol stack; layers above ARP use IP addresses, and layers below ARP use MAC addresses.23.17 What is the chief difference between BOOTP and DHCP?Answer:The main difference is that the BOOTP protocol required manual administration. So before a computer could use BOOTP to obtain an address, a network administrator had to configure a BOOTP server to know the computer’s I P address. Chapter 24 - The Future IP (IPv6)24.3 List the major features of IPv6, and give a short description of each.(See Textbook)24.4 How large is the smallest IPv6 datagram header?Answer: IPv6 datagram header consists of a base header + zero or more extension header. Since, smallest header is being asked, we assume zero extension header and consider IPv6 will have only base header. If we look at IPv6 header format in Fig. 24.3, it shows that 10x4 bytes = 40 bytes.Chapter 26 - TCP: Reliable Transport Service26.2 List the features of TCP.(See Textbook)26.6 When using a sliding window of size N, how many packets can be sent without requiring a single ACK to be received?Answer: If the size of the window is N, then it means a sender can transmit up to N packets without waiting for an ACK, as long as other controls are in place.26.9 What is the chief cause of packet delay and loss in the Internet?Answer: The main cause of packet delay and loss in the Internet is congestion.Chapter 28 - Network Performance (QoS and DiffServ)28.1 List and describe the three primary measures of network performance.(See Textbook)28.2 Give five types of delay along with an explanation of each.(See Textbook)Chapter 30 - Network Security30.1 List the major security problems on the Internet, and give a short description of each.(See Textbook)30.2 Name the technique used in security attacks.(See Textbook)30.8 List and describe the eight basic security techniques.(See Textbook)。
计算机网络课后答案(全部)
计算机网络习题解答教材计算机网络谢希仁编著第一章概述习题1-01 计算机网络的发展可划分为几个阶段?每个阶段各有何特点?答: 计算机网络的发展过程大致经历了四个阶段。
第一阶段:(20世纪60年代)以单个计算机为中心的面向终端的计算机网络系统。
这种网络系统是以批处理信息为主要目的。
它的缺点是:如果计算机的负荷较重,会导致系统响应时间过长;单机系统的可靠性一般较低,一旦计算机发生故障,将导致整个网络系统的瘫痪。
第二阶段:(20世纪70年代)以分组交换网为中心的多主机互连的计算机网络系统。
为了克服第一代计算机网络的缺点,提高网络的可靠性和可用性,人们开始研究如何将多台计算机相互连接的方法。
人们首先借鉴了电信部门的电路交换的思想。
所谓“交换”,从通信资源的分配角度来看,就是由交换设备动态地分配传输线路资源或信道带宽所采用的一种技术。
电话交换机采用的交换技术是电路交换(或线路交换),它的主要特点是:①在通话的全部时间内用户独占分配的传输线路或信道带宽,即采用的是静态分配策略;②通信双方建立的通路中任何一点出现了故障,就会中断通话,必须重新拨号建立连接,方可继续,这对十分紧急而重要的通信是不利的。
显然,这种交换技术适应模拟信号的数据传输。
然而在计算机网络中还可以传输数字信号。
数字信号通信与模拟信号通信的本质区别在于数字信号的离散性和可存储性。
这些特性使得它在数据传输过程中不仅可以间断分时发送,而且可以进行再加工、再处理。
③计算机数据的产生往往是“突发式”的,比如当用户用键盘输入数据和编辑文件时,或计算机正在进行处理而未得出结果时,通信线路资源实际上是空闲的,从而造成通信线路资源的极大浪费。
据统计,在计算机间的数据通信中,用来传送数据的时间往往不到10%甚至1%。
另外,由于各异的计算机和终端的传输数据的速率各不相同,采用电路交换就很难相互通信。
为此,必须寻找出一种新的适应计算机通信的交换技术。
1964年,巴兰(Baran)在美国兰德(Rand)公司“论分布式通信”的研究报告中提出了存储转发(store and forward)的概念。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
1 复习题1. 没有不同。
主机和端系统可以互换。
端系统包括PC,工作站,WEB 服务器,邮件服务器,网络连接的PDA,网络电视等等。
2. 假设爱丽丝是国家A 的大使,想邀请国家B 的大使鲍勃吃晚餐。
爱丽丝没有简单的打个电话说“现在我没一起吃晚餐吧”。
而是她先打电话给鲍勃建议吃饭的日期与时间。
鲍勃可能会回复说那天不行,另外一天可以。
爱丽丝与鲍勃不停的互发讯息直到他们确定一致的日期与时间。
鲍勃会在约定时间(提前或迟到不超过15 分钟)出现再大使馆。
外交协议也允许爱丽丝或者鲍勃以合理的理由礼貌的退出约会。
3. 联网(通过网络互联)的程序通常包括2 个,每一个运行在不同的主机上,互相通信。
发起通信的程序是客户机程序。
一般是客户机请求和接收来自服务器程序的服务。
4. 互联网向其应用提供面向连接服务(TCP)和无连接服务(UDP)2 种服务。
每一个互联网应用采取其中的一种。
面相连接服务的原理特征是:①在都没有发送应用数据之前2 个端系统先进行“握手”。
②提供可靠的数据传送。
也就是说,连接的一方将所有应用数据有序且无差错的传送到连接的另一方。
③提供流控制。
也就是,确保连接的任何一方都不会过快的发送过量的分组而淹没另一方。
④提供拥塞控制。
即管理应用发送进网络的数据总量,帮助防止互联网进入迟滞状态。
无连接服务的原理特征:①没有握手②没有可靠数据传送的保证③没有流控制或者拥塞控制5. 流控制和拥塞控制的两个面向不同的对象的不同的控制机理。
流控制保证连接的任何一方不会因为过快的发送过多分组而淹没另一方。
拥塞控制是管理应用发送进网络的数据总量,帮助防止互联网核心(即网络路由器的缓冲区里面)发生拥塞。
6. 互联网面向连接服务通过使用确认,重传提供可靠的数据传送。
当连接的一方没有收到它发送的分组的确认(从连接的另一方)时,它会重发这个分组。
7. 电路交换可以为呼叫的持续时间保证提供一定量的端到端的带宽。
今天的大多数分组交换网(包括互联网)不能保证任何端到端带宽。
当发生拥塞等网络问题时,TDM 中的数据丢失可能只会是一部分,而FDM 中就可能是大部分或全部。
8. 在一个分组交换网中,在链路上流动的来自不同来源的分组不会跟随任何固定的,预定义的模式。
在TDM 电路交换中,每个主机从循环的TDM 帧中获得相同的时隙。
9. t0 时刻,发送主机开始传输。
在t1=L/R1 时刻,发送主机完成发送并且整个分组被交换机接收(无传输时延)。
因为交换机在t1 时刻接收到了整个分组,它可以在t1 时刻开始向接收主机发送分组。
在t2=t1+L/R2 时刻,交换机完成传输且接收主机收到了整个分组(同样,无传输时延)。
所以,端到端实验是L/R1+L/R2。
10. 在一个虚电路网络中,每个网络核心中的分组交换机都对经过它传输的虚电路的连接状态信息进行维护。
有的连接状态信息是维护在一个虚电路数字传输表格中。
11. 面向连接的VC 电路的特点包括:a.建立和拆除VC 电路是需要一个信令协议;b.需要在分组交换中维持连接状态。
有点方面,一些研究者和工程人员争论到:使用VC 电路可以更容易提供QoS 业务,如:保证最小传输率的业务,以及保证端到端的最大分组延时的业务。
12. a.电话线拨号上网:住宅接入;b.电话线DSL 上网:住宅接入或小型办公;c.混合光纤同轴电缆:住宅接入;d.100M交换机以太网接入:公司;e.无线局域网:移动接入;f.蜂窝移动电话(如W AP):移动。
13. 一个第一层ISP 与所有其它的第一层ISP 相连;而一个第二层ISP 只与部分第一层ISP 相连。
而且,一个第二层ISP 是一个或多个第一层ISP 的客户。
14. POP 是ISP 网络中一个或多个路由器构成的一个组,其它ISP 中的路由器也可以能连接到这个POP。
NAP 是一个很多ISP(第一层,第二层,以及其它下层ISP)可以互联的局部网络。
15. HFC 的带宽是用户间共享的。
在下行信道,所有的分组从头到尾由同一个源发出,因此在下行信道不会发生冲突。
16. 以太网的传输速率有:10Mbps,100Mbps,1Gbps 和10Gbps。
对于一个给定的传输速率,如果用户单独在线路上传输数据,则可以一直保持这个速率;但是如果有多个用户同时传输,则每个都不能达到所给定的速率(带宽共享)。
17. 以太网通常以双绞线或者细的同轴电缆为物理媒体,也可以运行在光纤链路和粗同轴电缆上。
18. 拨号调制解调器:最高56Kbps,带宽专用;ISDN:最高128Kbps,带宽专用;ADSL:下行信道5-8Mbps,上行信道最高1Mbps,带宽专用;HFC:下行信道10-30Mbps,上行信道一般只有几Mbps,带宽共享。
19. 时延由处理时延、传输时延、传播时延和排队时延组成。
所有这些时延除了排队时延都是固定的。
20. 5 种任务为:错误控制,流量控制,分段与重组,复用,以及连接建立。
是的,这些任务可以由两层(或更多层)来执行,比如:经常在多于一个层次上执行错误控制。
21. 英特网协议栈的5 个层次从上倒下分别为:应用层,传输层,网络层,链路层,和物理层。
每一层的主要任务见1.7.1 节。
应用层是网络应用程序及其应用层协议存留的地方;运输层提供了一个在应用程序的客户机和服务器之间传输应用层报文的服务;网络层负责将称为数据报的网络层分组从一台主机移动到另一台主机;链路层:通过一系列分组交换机(Internet 中的路由器)在源和目的地之间发送分组;物理层:将该帧中的一个一个比特从一个节点移动到下一个节点。
22. 应用层报文:应用程序要发出的在传输层上传递的数据;传输层报文段:将应用层报文加上传输层包头,由传输层管理和封装的信息;网络层数据报:将传输层报文段加上网络层包头之后封装;链路层帧:将网络层数据报加上链路层包头之后封装。
23. 路由器处理第一层到第三层(这是一个善意的谎话?本人理解为“这样说不确切”因为现代路由器常常还要扮演防火墙或者高速缓存器的角色,一次也处理第四层);链路交换机处理第一层和第二层;主机处理所有的5 层。
习题1. 本题不止一个答案,很多协议都能解决这个问题,下面是一个简单的例子:2. a.电路交换网更适合所描述的应用,因为这个应用要求在可预测的平滑带宽上进行长期的会话。
由于传输速率是已知,且波动不大,因此可以给各应用会话话路预留带宽而不会有太多的浪费。
另外,我们不需要太过担心由长时间典型会话应用积累起来的,建立和拆除电路时耗费的开销时间。
b.由于所给的带宽足够大,因此该网络中不需要拥塞控制机制。
最坏的情况下(几乎可能拥塞),所有的应用分别从一条或多条特定的网络链路传输。
而由于每条链路的带宽足够处理所有的应用数据,因此不会发生拥塞现象(只会有非常小的队列)。
3. a.因为这4 对相邻交换机,每对之间可以建立n 条连接,;因此最多可以建立4n 条连接。
b.可以通过右上角的交换机建立n 条连接,并且可以通过左下角交换机建立n 条连接,因此最多可以建立2n 条连接。
4. 由于收费站间隔100km,车速100km/h,收费站以每12m 通过一辆汽车的速度提供服务。
a)10 辆车,第一个收费站要花费120s,即2 分钟来处理。
每一辆车要达到第二个收费站都会有60 分钟的传输延时,因此每辆车要花费62 分钟才能达到第二个收费站,从第二个收费站到第三个收费站重复这一过程。
因此,(端到端)总延时为124 分钟。
b)每两个收费站之间的延时为7×12 秒+60 分=61 分24 秒,(端到端)总延时=3624×2=7,248s,即112 分48秒。
5. a)传输一个分组到一个链路层的时间是(L+h)/R。
Q段链路的总时间为:Q(L+h)/R。
所以发送文件所需要总的时间为:t s+(L+h)/Q。
b)Q(L+2h)/Rc)由于链路上没有存储转发延时,因此,总延时为:t s+(L+h)/R。
6. a)传播时延d prop=m/s秒b)传输时延d trans=L/R秒c)端到端时延d end-to-end=(m/s+L/R)秒d)该分组的最后一个bit 刚刚离开主机A。
e)第一个比特在链路中,还没有到达B。
f)第一个比特已经到达 B 。
g)m=LS/R=100×2.5e8/28e3=893km7. 考虑分组中的第一个 bit 。
在这个 bit 被传输以前,先要收集这个分组中的其它 bit ,这个需要:48×8/64e3 =6e-3s =6ms分组的传输延时:48×8/1e6=384e-6 s=0.384ms传播时延:2ms到该 bit 被解码的时延为:6+0.384+2=8.384ms (英文答案中的那个“.”表示乘)8. a)由于每个用户需要十分之一的带宽,因此可以支持 10 个用户。
b)p=0.1c)d)我们用中心极限定理来求这个概率的近似解。
令X j 表示J 个用户同时传输的概率,如P (X j =1)=p,则:所以所求概率约为:0.0019.10. 传输这 N 个分组需要 LN/R 秒。
当一批 N 个分组到达时,缓存器内是空的。
第一个分组没有排队时延,第二个分组的排队时延为 L/R 秒......第 N 个分组的排队时延为:(N-1)L/R 秒,所以 平均排队时延为:11. a)传输时延为 L/R ,总时延为b)令 x=L/R ,则总时延与 x 的函数为:总时延=x/(1-ax )。
12. a)一共有Q 个节点(源主机喝N-1 个路由器)用表示第q 个节点的处理时延。
用R q 表示第q 个节点处的传输速 率,令 。
用表示通过第q 条链路的传播时延。
则:b)用表示节点q 处的平均排队延时,则:13. 实验题?不会考吧。
14. a)“带宽时延”积=(1e7/2.5e8)*1e6=40,000bit b)40000bit c)一条链路的带宽时延积就是这条链路上具有的比特数的最大值。
d)1e7/4e4=250m,比一个足球场的长度还长。
e)s/R15. 2.5e8/1e6=25bps16. a)(1e7/2.5e8)*1e9=40,000,000bitb)400,000bit(包长度)c)1e7/4e5=25m17. a)传播时延=1e7/2.5e8=40ms;传输时延=4e5×250/2.5e8= 400ms因此总延时为:440msb)传播时延=2×40=80ms(发送及返回确认);传输时延=4e4×250/2.5e8=40ms,传送10 个分组,总时延=10×(80+40)=1200ms=1.2s18. a)地球同步卫星距离地面3600km,因此该链路的传播时延=3600e3/2.4e8=150msb)150e-3×10e6=1,500,000c)60×10e6=6e8bit19. 我们假设旅客和行李对应到达协议栈顶部的数据单元,当旅客检票的时候,他的行李也被检查了,行李和机票被加上标记。
