CCNA最新题库
思科认证CCNA认证试题与答案中文版
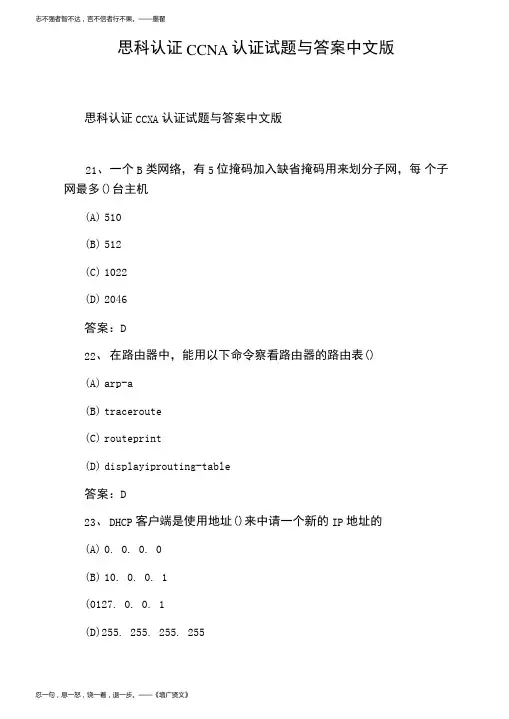
答案:D 注释:这个题目不是太严谨,应该加上子网掩码. A:224. 0. 0. 5 是多播地址 B: 127. 0.0. 0 保留作为测试使用 C:网络地址 26、 设置主接口由 up 转 down 后延迟 30 秒切换到备份接口,主 接口 由 down 转 up 后 60 秒钟切换回主接口的配置为()
忍一句,息一怒,饶一着,退一步。——《增广贤文》
人之为学,不日进则日退,独学无友,则孤陋而难成;久处一方,则习染而不自觉。——《顾炎武》
答案:D 注释:255. 255. 255. 255 是全网广播,DHCP 客户端发送全网广播来 查 找 DHCP 服务器. 24、 下而有关 NAT 叙述正确的是() (A) NAT 是英文“地址转换”的缩写,又称地址翻译 (B) XAT 用来实现私有地址与公用网络地址之间的转换 (C) 当内部网络的主机访问外部网络的时候,一定不需要 NAT (D) 地址转换的提出为解决 IP 地址紧张的问题提供了一个有效途 径 答案:ABD 25、 以下属于正确的主机的 IP 地址的是()
(A) arp-a (B) traceroute (C) routeprint (D) displayiprouting-table
答案:D 23、 D0. 0. 0 (B) 10. 0. 0. 1 (0127. 0. 0. 1 (D)255. 255. 255. 255
192. 168. 1. 1
答案:D 注释:PC 的'默认网关要指向路由器的以太网口的 IP 地址. 28、 ISDNB 信道速率是()
(A) 16kbps (B) 64kbps
最新CCNA认证考试真题
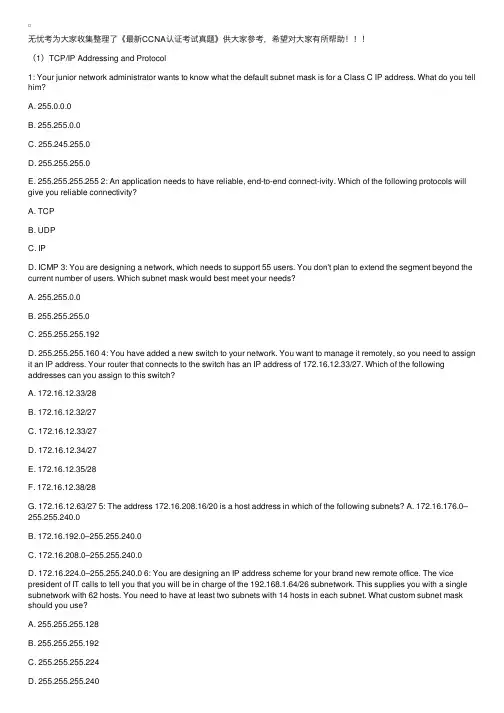
⽆忧考为⼤家收集整理了《最新CCNA认证考试真题》供⼤家参考,希望对⼤家有所帮助(1)TCP/IP Addressing and Protocol1: Your junior network administrator wants to know what the default subnet mask is for a Class C IP address. What do you tell him?A. 255.0.0.0B. 255.255.0.0C. 255.245.255.0D. 255.255.255.0E. 255.255.255.255 2: An application needs to have reliable, end-to-end connect-ivity. Which of the following protocols will give you reliable connectivity?A. TCPB. UDPC. IPD. ICMP 3: You are designing a network, which needs to support 55 users. You don't plan to extend the segment beyond the current number of users. Which subnet mask would best meet your needs?A. 255.255.0.0B. 255.255.255.0C. 255.255.255.192D. 255.255.255.160 4: You have added a new switch to your network. You want to manage it remotely, so you need to assign it an IP address. Your router that connects to the switch has an IP address of 172.16.12.33/27. Which of the following addresses can you assign to this switch?A. 172.16.12.33/28B. 172.16.12.32/27C. 172.16.12.33/27D. 172.16.12.34/27E. 172.16.12.35/28F. 172.16.12.38/28G. 172.16.12.63/27 5: The address 172.16.208.16/20 is a host address in which of the following subnets? A. 172.16.176.0–255.255.240.0B. 172.16.192.0–255.255.240.0C. 172.16.208.0–255.255.240.0D. 172.16.224.0–255.255.240.0 6: You are designing an IP address scheme for your brand new remote office. The vice president of IT calls to tell you that you will be in charge of the 192.168.1.64/26 subnetwork. This supplies you with a single subnetwork with 62 hosts. You need to have at least two subnets with 14 hosts in each subnet. What custom subnet mask should you use?A. 255.255.255.128B. 255.255.255.192C. 255.255.255.224D. 255.255.255.240E. 255.255.255.248 7: You have subnetted the 210.106.14.0 network with a /24 mask. Your boss at Acme, Inc. wants to know how many usable subnetworks and usable host addresses per subnet this would provide. What should you tell her?A. One network with 254 hostsB. Two networks with 128 hostsC. Four networks with 64 hostsD. Six networks with 30 hosts 8: Identify three valid host addresses in any subnet of the 201.168.27.0 network, assuming a fixed subnet mask of 255.255.255.240. (Choose three.)A. 201.168.27.33B. 201.168.27.112C. 201.168.27.119D. 201.168.27.126E. 201.168.27.175F. 201.168.27.208 9: What is the subnetwork address for a host with the IP address 201.100.5.68/28?A. 201.100.5.0B. 201.100.5.32C. 201.100.5.64D. 201.100.5.65E. 201.100.5.31F. 201.100.5.1 10: Which of the following protocols uses a three-way handshake mechanism to establish sessions?A. TCPB. IPC. UDPD. IPXE. Frame relay 11: Which of the following protocols is connection-oriented? A. TCPB. IPC. IPXD. Frame relay 12: You are using an application on your Windows 2000 client machines that provides error correction. You need a protocol to provide fast transport. Which protocol should your application use?A. TCPB. IPC. UDPD. SPXE. AppleTalk 13: When using TCP, after a session is open, the applications can adjust the number of segments they receive before sending an acknowledgment. This behavior is known as ______________.A. MTU adjustmentB. WindowingC. Flexible Send PathD. FCS 14: If the destination did not receive a segment, how will the TCP host know to resend the information?A. The ACK received will not include the segment number that was not received.B. The ACK received will include the segment number that was not received.C. The sending host will send a PACK to verify segment receipt.D. The destination host will send a YACK message back to the sending host. 15: You are planning on using a single network that supports 208 users. Which IP address class would you choose to be the most efficient?A. Class AB. Class BC. Class CD. Class DE. Class E 16: RFC 1918 defines the private IP address ranges. Which of the following IP addresses are considered part of these ranges? (Choose three.)A. 10.23.45.67B. 126.21.34.56C. 172.16.32.1D. 172.31.234.55E. 192.169.4.5 17: A new network is being designed for your company, Acme, Inc. If you use a Class C IP network, which subnet mask will provide one usable subnet per department while allowing enough usable host addresses for each department specified in the table?Department Number of Users Corporate 7 Customer Support 15 Financial 13 HR 7 Engineering 16 A. 255.255.255.0B. 255.255.255.192C. 255.255.255.224D. 255.255.255.240E. 255.255.255.248 18: Which of these protocols provides data transport, relying on the error correction capabilities of the application itself?A. UDPB. TCPC. SNMPD. ICMP 19: Which of the following are used by TCP to ensure reliable delivery of data? (Choose two.)A. MAC address resolutionB. Sequence numbersC. AcknowledgmentsD. PingE. Routing updates 20: You discover that you are able to adjust the window size of the TCP segment. You increase the window size to test the results. What will you observe happening on your network?A. Increased throughputB. Decreased throughputC. Increased latencyD. Decreased reliability21: Your organization is using the 192.168.1.0/24 address space. You need 28 subnets. What subnet mask would you use to create these subnets?A. 255.255.255.0B. 255.255.255.128C. 255.255.255.192D. 255.255.255.224E. 255.255.255.240F. 255.255.255.248 22: Which of the following protocols maps IP addresses to MAC addresses for connectivity to occur between two hosts?A. ARPB. RARPC. SLARPD. DHCP 23: Your junior network administrator cannot seem to ping a host in another network and asks you why it isn't working. Which of the following is not an answer that you would give him?A. The host's default gateway is down.B. The destination host is not powered on.C. The IP address of the router interface is incorrect.D. The IP address of the switch to which the destination host connects is incorrect.E. The host is in a different subnet. 24: Which of the following classes of IP addresses is utilized for multicasting?A. Class AB. Class BC. Class CD. Class D 25: You give your IT department a spreadsheet of IP addresses and their subnets. You receive a call from one of the junior techs asking what the /26 means next to the IP addresses. You tell her: A. It represents the number of hosts possible on that subnetwork.B. It represents the number of subnetworks that are being used.C. It represents the class of IP address being used.D. It represents the number of bits in the subnet mask that are 1. 26: You are given an IP network of 192.168.5.0 and told that you need to separate this network into subnetworks that can support a maximum of 16 hosts per subnet. This will help alleviate congestion on the network. What subnet mask can you use to create the subnets necessary to meet the given criteria?A. 255.0.0.0B. 255.255.0.0C. 255.255.255.0D. 255.255.255.224E. 255.255.255.240 27: Which of the following would a Class A network be assigned to?A. Government agencyB. Small-to-medium sized corporationD. An individual 28: A client has the IP address 192.168.5.98/27. Which of the following addresses are on the same subnet as this host? (Choose two.)A. 192.168.5.95B. 192.168.5.100C. 192.168.5.128D. 192.168.5.110 29: Which of the following IP addresses is not a public IP address that can be routed over the Internet?A. 2.3.4.5B. 11.12.13.14C. 165.23.224.2D. 172.31.45.34E. 203.33.45.22 30: You are given a Class B network. What is the default subnet mask assigned to the Class B network?A. 255.255.255.255B. 255.255.0.0C. 255.224.0.0D. 0.0.0.0 31: You are troubleshooting your router's interfaces. For some reason, the Ethernet interface will not accept the IP address of 192.168.5.95/27 that you've assigned. Which of the following explains the router's refusal to take the IP address?A. Class C addresses cannot be assigned to Ethernet interfaces.B. The /27 is an invalid mask.C. It is a broadcast address.D. It is a public IP address.E. It is a private IP address. 32: You are a network technician at Acme, Inc. You are required to divide the 172.12.0.0 network into subnets. Each subnet must have the capacity of 458 IP addresses. Also, according to the requirements, you must provide the maximum number of subnets. Which subnet mask should you use?A. 255.255.255.254B. 255.255.254.0C. 255.255.240.254D. 255.255.0.0 33: What is the subnetwork and broadcast IP address of 192.168.2.37 with the subnet mask of255.255.255.248?A. 192.168.2.24/192.168.2.31B. 192.168.2.32/192.168.2.39C. 192.168.2.40/192.168.2.47D. 192.168.2.48/192.168.2.55E. 192.168.2.56/192.168.2.63 34: One of your co-workers at Acme, Inc., needs to convert the binary number 11011010 into a decimal. What is the decimal equivalent?A. 218B. 219C. 220E. 222 35: One of your co-workers at Acme, Inc., needs to convert the binary number 01011010 into a decimal. What is the decimal equivalent?A. 75B. 83C. 90D. 97 36: One of your co-workers at Acme, Inc. , n e e d s t o c o n v e r t t h e b i n a r y n u m b e r 1 1 0 1 0 1 1 0 i n t o a d e ci m a l . W h a t i s t h e d e c i m a l e q u i v a l e n t ? / p > p b d s f i d = " 2 1 0 " > A . 1 9 8 / p > p b d s f i d = " 2 1 1 " > B . 2 14 / p > p b d s f i d = " 2 1 2 " > C . 25 2 / p > p b d s f i d = " 2 1 3 " > D . 2 5 5 3 7 : O n e o f y o u r c o - w o r k e r s a t A c m e , I n c . , n e e d s t o c o n v e r t t h e b i n a r y n u m b e r 1 0 1 1 0 1 1 0 i n t o a d e c i m a l . W h a t i s t h e d e c i m a l e q u i v a l e n t ? / p > p b d s f i d = " 2 1 4 " > A . 1 8 2 / p > p b d s f i d = " 2 1 5 " > B . 1 9 2 / p > p b d s f i d = " 2 16 " > C . 2 0 2 / p > p b d s f i d = " 2 17 " > D . 2 1 2 38 : Y o u a r e c o n f i g u r i n g a s u b n e t f o r t h e A c m e , I n c . , b r a n c h o f f i c e i n B e i j i n g . Y o u n e e d t o a s s i g n I P a d d r e s s e s t o h o s t s i n t h i s s u b n e t . Y o u h a v e b e e n g i v e n t h e s u b n e t m a s k o f 2 5 5 . 2 5 5 . 2 5 5 . 2 2 4 . W h i c h o f t h e s e I P a d d r e s s e s w o u l d b e v a l i d ? ( C h o o s e t h r e e . ) / p > p b d s f i d = " 2 1 8 " > A . 1 5 . 2 3 4 . 1 1 8 . 6 3 / p > p b d s f i d = " 2 19 " > B . 9 2 . 1 1 . 1 7 8 . 9 3 / p > p b d s f i d = " 2 2 0 " > C . 1 3 4 . 1 7 8 . 1 8 . 5 6 / p > p b d s f i d = " 2 2 1 " > D . 1 9 2 . 1 6 8 . 1 6 . 8 7 / p > p b d s f i d = " 2 2 2 " > E . 2 0 1 . 4 5 . 1 1 6 . 1 5 9 / p > p b d s f i d = " 2 2 3 " > F . 2 1 7 . 6 3 . 1 2 . 1 9 2 3 9: Y o u a r e a n e t w o r k t e c h n i c i a n a t A c m e , I n c . Y o u h a v e s u b n e t t e d t h e 2 0 8 . 9 8 . 1 1 2 . 0 n e t w o r k w i t h a / 2 8 m a s k . Y o u r b o s s a s k s y o u h o w m a n y u s a b l e s u b n e t w o r k s a n d u s a b l e h o s t a d d r e s s e s p e r s u b n e t t h i s w i l l p r o v id e . W h a t s h o u l d y o u t e l l h e r , a s s u m i n g y o u r r o u t e r i s u s i n g i p s u b n e t - z e r o ? / p > p b d s f i d = " 22 4 " > A . 6 2 n e t w o r k s a n d 2 h o s t s / p > p b d s f i d = " 2 2 5 " > B . 6 n e t w o r k s a n d3 0 h o s t s / p > p b d s f i d = " 2 2 6 " > C . 8 n e t w o r k s a n d 3 2 h o s t s / p > p b d s f i d = " 2 2 7 " > D . 1 6 n e t w o r k s a n d 1 6 h o s t s / p > p b d s f i d = " 2 2 8 " > E . 1 6 n e t w o r k s a n d 14 h o s t s 4 0 : W h a t i s a d i s a d v a n t a g e o f u s i n g a c o n n e c t i o n -o r i e n t e d p r o t o c o l s u c h a s T C P ? / p > p b d s f i d = " 2 2 9 " > A . P a c k e t a c k n o w l e d g m e n t m i g h t a d d o v e r h e a d . / p > p b d s f i d = " 2 3 0 " > B . P a c k e t s a r e n o t t a g g e d w i t h s e q u e n c e n u m b e r s . / p > p b d s f i d = " 2 3 1 " > C . L o s s o r d u p l i c a t i o n o f d a t a p a c k e t s i s m o r e l i k e l y t o o c c u r . / p > p b d s f i d = " 2 32 " > D . T h e a p p l i c a t i o n l a y e r m u s t a s s u m e r e s p o n s i b i l i t y f o r t h e c o r r e c t s e q u e n c i n g o f t h ed a t a p a c ke t s . 4 1 : Y o u a r e a n e t w o r k t e c h n i c i a n a t A c m e , I n c . Y o u h a v e s u b n e t t e d t h e 1 9 2 . 16 8 .7 2 . 0 n e t w o r k w i t h a / 3 0 m a s k f o r c o n n e c t i o n s b e t w e e n y o u r r o u t e r s . Y o u r b o s s a s k s y o uh o w m a n y u s a b l e s u b n e t w o r k s a n d u s a b l e h o s t a d d r e s s e s p e r s u b n e t t h i s w i l l p r o v i d e . W h a t s h o u l d y o u t e l l h e r , a s s u m i n g y o u r r o u t e r c a n n o t u s e i p s u b n e t - z e r o ? / p > p b d s f i d = " 2 3 3 " > A . 6 2 n e t w o r k s a n d 2 h o s t s / p > p b d s f i d = " 2 3 4 " > B . 6 n e t w o r k s a n d 3 0 h o s t s / p > p b d s f i d = " 23 5 " > C . 8 n e t w o r k s a n d 3 2 h o s t s / p > p b d s f i d = " 2 3 6 " > D . 1 6 n e t w o r k s a n d 1 6 h o s t s / p > p b d s f id = " 2 3 7 " > E . 1 4 ne t w o r k s a n d 1 4 h o s t s 4 2 : W h i c h of t h e f o l l o w i ng I P a d d r e s s e s a r e c o n s i d e re d " n e t w o r k " a d d r e s s e s w i t h a / 2 6 p r ef i x ? ( C h o o s e t w o . ) / p > p b d s f i d = " 2 3 8 " > A . 1 6 5 . 2 0 3 . 2 . 0 / p > p b d s f i d = " 2 3 9 " > B . 1 6 5 . 2 0 3 . 5 . 1 9 2 / p > p b d s f i d = " 2 4 0 " > C . 1 6 5 . 2 0 3 . 6 . 6 3 / p > p b d s f i d = " 2 4 1 " > D . 1 6 5 . 2 0 3 . 6 . 1 9 1 / p > p b d s f i d = " 2 4 2 " > E . 1 6 5 . 2 0 3 . 8 . 2 5 5 4 3 : I d e n t i f y t h r e e v a l i d h o s t s i n a n y s u b n e t o f 1 9 2 . 1 6 8 . 3 2 . 0 , a s s u m i ng th e s u b n e t m a s k u s e di s 2 5 5 . 2 5 5 . 2 5 5 . 2 4 0 . (C h o o s e t h r e e . ) / p > p b d s f i d = " 2 4 3 " > A . 1 9 2 . 1 6 8 . 3 2 . 3 3 / p > p b d s f i d = " 2 4 4 " > B . 1 9 2 . 1 6 8 . 3 2 .1 12 / p > p b d s f i d = " 2 4 5 " > C . 1 9 2 . 1 6 8 .3 2 . 1 1 9 / p > p b d s f i d = " 24 6 " > D . 1 9 2 . 1 6 8 . 3 2 . 1 2 6 / p > p bd s f i d = " 2 4 7 " > E . 1 9 2 . 1 6 8 . 3 2 . 1 7 5 / p > p b d s f i d = " 2 4 8 " > F . 1 9 2 . 1 6 8 . 3 2 . 2 0 8 4 4 : A C l a s s C ne t w o r k a d d r e s s h a s b e e n s u b n e t t e d w i t h a / 2 7 m a s k . W h i c h of t h e f o l l o w i ng a d d r e s s e s i s a b r oa d c a s t a d d r e s s f o r o n e o f t h e r e s u l t i n g s ub n e t s ? / p > p b d s f i d = " 2 4 9 " > A . 1 9 8 . 5 7 . 7 8 . 3 3 / p > pb d s f i d = " 2 5 0 " > B . 1 9 8 . 5 7 . 7 8 . 6 4 / p > p b d s f i d = " 2 5 1 " > C . 1 9 8 . 5 7 . 7 8 . 9 7 / p > p b d s f i d = " 2 5 2 " >D . 1 9 8 . 5 7 . 7 8 . 9 7 / p > p b d s f i d = " 2 5 3 " >E . 1 9 8 . 5 7 . 7 8 . 1 5 9 / p > p b d s f i d = " 2 5 4 " >F . 1 9 8 . 5 7 . 7 8 .2 5 4 4 5 : W h a t i s t h e s u b n e t w o r k a d d r e s s f o r a h o s t w i t h I P a d d r e s s 1 6 5 . 1 0 0 . 5 . 6 8 / 2 8 ? / p > p bd s f i d = " 2 5 5 " > A . 1 6 5 . 1 0 0 . 5 . 0 / p > p b d s f i d = " 2 5 6 " > B . 1 6 5 . 1 0 0 . 5 . 3 2 / p > p b d s f i d = " 2 5 7 " > C .1 6 5 . 1 0 0 . 5 . 6 4 / p > p b d s f i d = "2 5 8 " > D . 1 6 5 . 1 0 0 . 5 . 6 5 / p > p b d s f i d = " 2 5 9 " > E . 1 6 5 . 1 0 0 . 5 .3 1 / p > p b d s f i d = " 2 6 0 " > F . 1 6 5 . 1 0 0 . 5 . 14 6 : Y o u r b o s s w a n t s t o k n o w w h a t T C P s t a n d s f o r . W h a t d o y o u t e l l h i m ? / p > p b d s f i d = " 2 6 1 " > A . T r a n s m i s s i o n C h e c k P r o t o c o l / p > p b d s f i d = " 2 6 2 " > B . T r a n s p o r t C h e c k P r o t o c o l / p > p b d s f i d = " 2 6 3 " > C . T r a n s m i s s i o n C o n t r o l P r o t o c o l / p > p b d s f i d = " 2 6 4 " > D . T r a n s p o r t C o n t r o l P r o t o c o l 4 7 : Y o u r b o s s w a n t s t o k n o w w h a t U D P s t a n d s f o r . W h a t d o y o u t e l l h i m ? / p > p b d s f i d = " 2 65 " > A . U n r e l i a b l e D a t a P r o t o c o l / p > p b d s f i d = " 26 6 " > B . U n r e l i a b l e D a t a P r o g r a m / p > p b d s f i d = " 2 67 " > C . U s e r - D e f i n e d P r o t o c o l / p > p b d s f i d = "2 6 8 " > D . U s e r D a t a g r a m P r o t o c o l 4 8 : W h i c h o f t h e f o l l o w i n g s t a t e m e n t s a c c u r a t e l y d e s c r ib e s U D P ? / p > p b d s f i d = " 2 6 9 " > A . U D Pc o p i e s f i l e s b e t w e e n a c o m p u t e r a nd a s y s te m r u n n i n g r s h d , t h e r e m o t e s h e l l s e r v i c e ( d a e m o n ) . / p > p b d sf i d = " 2 7 0 " > B . U D P i s a m e m b e r o f t h e T C P / I P s u i t e o f p r o t o c o l s t h a tg o v e r n s th e e x c h a n g e o f e l e c t r o ni c m a i l b e t w e e n m e s s a g e t ra n s f e r a g e n t s . / p > pb d s f i d = " 2 7 1 " > C . U D P i s a m e m b e r o f t h e T C P / I P s u i t e o f p r o t oc o l s a nd i s u se d t o c o p yf i l e s b e t w e e n t w o c o m p u t e r s o n t h e I n t e r n e t . B o t h c o m p u t e r s m u s t s u p p o r t t h e i r r e s p e c t i v e r o l e s : o n e m u s t b e a c l i e n t , a n d t h e o t h e r a s e r v e r . / p > p b d s f i d = " 2 7 2 " > D . U D P i s a T C P c o m p l e m e n t t h a t o f f e r s a c o n n e c t i o n l e s s d a t ag r a m s e r v i c e g u a r a n t e e i n g n e i th e r d e li v e r y n o r c o r r e c t s e q u e n c i n g o f d e l i v e r e d p a c k e t s ( m u c h l i k e I P ) . 4 9 : W h i c h o f t h e f o l l o w i n g h o s t a d d r e s s e s a r e m e m b e r s o f n e t w o r k s t h a t c a n b e r o u t e d a c r o s s t h e p u b l i c I n t e r n e t ? ( C h o o s e t h r e e . ) / p > p b d s f i d = " 2 7 3 " > A . 1 0 . 2 0 . 1 2 . 6 4 / p > p b d s f i d = " 2 7 4 " > B . 1 7 2 . 1 6 . 32 . 1 2 9 / p > p b d s f i d = " 2 7 5 " > C . 1 7 2 . 6 4 .3 2 . 34 / p > p b d s f i d = " 2 7 6 " > D . 1 9 2 . 1 6 8 . 2 3 . 25 2 / p > p bd s f i d = " 2 7 7 " > E . 1 9 6 . 1 0 4 . 1 2 . 9 5 / p > p b d s f i d = " 2 7 8 " > F . 2 1 4 . 1 9 2 . 4 8 . 2 5 4 5 0 : Y o u a re c o n n e c t i n g y o u r S e r i a l 0 / 1 i n t e rf a c e t o t h e I n t e r n e t . W h i c h o f t h e f o l l o w i ng n e e d t o b e d o n e f o r th e c o n n e c ti o n t o w o r k ? ( C h o o s e t w o . ) / p > p b d s f i d = " 2 7 9 " > A . A s s i g n a p u b l i c I P a d d r e s s . / p > pb d s f i d = " 2 8 0 " > B . U s e t h e s h u t d o w nc o m m a nd . / p > p b d s f i d = " 2 8 1 " > C . U se t h e n o s h u t d o w nc o m m a nd . / p > p b d s f i d = " 2 8 2 " > D . M a ke s u r e t h e i n t e rf a c e i s r u n n i ng i n f u l l - d u p l e x . / p >。
思科 CCNA 学习试题 答案!!!
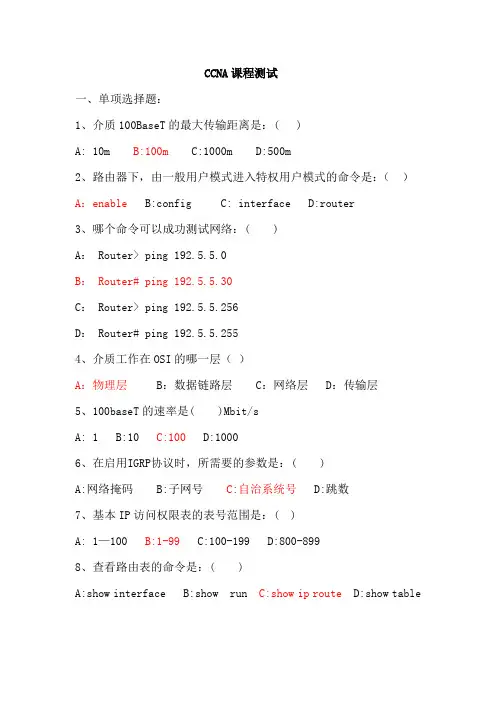
CCNA课程测试一、单项选择题:1、介质100BaseT的最大传输距离是:( )A: 10m B:100m C:1000m D:500m2、路由器下,由一般用户模式进入特权用户模式的命令是:()A:enable B:config C: interface D:router3、哪个命令可以成功测试网络:( )A: Router> ping 192.5.5.0B: Router# ping 192.5.5.30C: Router> ping 192.5.5.256D: Router# ping 192.5.5.2554、介质工作在OSI的哪一层()A:物理层 B:数据链路层 C:网络层 D:传输层5、100baseT的速率是( )Mbit/sA: 1 B:10 C:100 D:10006、在启用IGRP协议时,所需要的参数是:( )A:网络掩码 B:子网号C:自治系统号 D:跳数7、基本IP访问权限表的表号范围是:( )A: 1—100 B:1-99 C:100-199 D:800-8998、查看路由表的命令是:( )A:show interface B:show run C:show ip route D:show table9、工作在OSI第三层的设备是:( )A:网卡B:路由器 C: 交换机 D:集线器10、OSI第二层数据封装完成后的名称是:( )A:比特 B: 包C:帧 D:段11、为了禁止网络210.93.105.0 ftp到网络223.8.151.0,允许其他信息传输,则能实现该功能的选项是:( )A:access-list 1 deny 210.93.105.0.0.0.0.0.0B: access-list 100 deny tcp 210.93.105.0 0.0.0.255 223.8.151.00.0.0.255 eq ftpC:access-list 100 permit ip any anyD:access-list 100 deny tcp 210.93.105.0 0.0.0.255 223.8.151.0 0.0.0.255 eq ftpaccess-list 100 permit ip any any12、路由器下“特权用户模式”的标识符是:( )A: > B:! C:# D: (config-if)#13、把指定端口添加到VLAN的命令是:( )A: vlan B: vlan-membership C: vtp D:switchport14、交换机工作在OSI七层模型的哪一层( )A:物理层B:数据链路层C:网络层 D:传输层15、在OSI七层模型中,介质工作在哪一层( )A:传输层 B:会话层C:物理层 D:应用层16、交换机转发数据到目的地依靠( )A:路由表B:MAC地址表 C:访问权限表 D:静态列表17、为了使配置私有IP的设备能够访问互联网,应采用的技术是( )?A:NAT B:VLAN C:ACCESS-LIST D:DDR18、VLAN主干协议VTP的默认工作模式是( )A:服务器模式 B:客户端模式 C:透明模式 D:以上三者都不是19、路由器的配置文件startup-config存放在( )里A:RAM B:ROM C:FLASH D:NVRAM20、配置路由器特权用户“加密密码”的命令是:( )A:password B:enable password C:enable secretD:passwd21、某网络中,拟设计10子网,每个子网中放有14台设备,用IP 地址段为199.41.10.X ,请问符合此种规划的子网掩码是( ) A: 255.255.255.0 B:255.255.240.0C: 255.255.255.240 D:255.248.0.022、在路由表中到达同一网络的路由有:静态路由、RIP路由、IGRP 路由,OSPF路由,则路由器会选用哪条路由传输数据:( )A:静态路由 B: RIP路由 C:IGRP路由 D:OSPF路由23、扩展IP访问权限表的表号范围是:( )A: 1—100 B:1-99 C:100-199 D:800-89924、把访问权限表应用到路由器端口的命令是:( )A: permit access-list 101 out B: ip access-group 101 out C: apply access-list 101 out D: access-class 101 out 25、混合型协议既具有“距离矢量路由协议”的特性,又具有“链路状态路由协议”的特性,下列协议中属于混合型协议的是:( ) A: RIP B: OSPF C: EIGRP D: IGRP26、在路由器上,命令show access-list的功能是():A:显示访问控制列表内容 B:显示路由表内容C:显示端口配置信息 D:显示活动配置文件27、RIP路由协议认为“网络不可到达”的跳数是:( )A: 8 B:16 C:24 D:10028、查看E0端口配置信息的命令是:( )A:show access-list B:show ip routeC:show version D:show interface e029、配置路由器时,封装PPP协议的命令是:( )A:encap ppp B:ppp C: group ppp D: int ppp30、路由器上“水平分割”的功能是:( )A:分离端口B:阻止路由环路 C:简化配置 D:方便故障处理31、OSI七层模型中,“包”是哪一层数据封装的名称()A:物理层 B:数据链路层C:网络层 D:传输层32、OSI七层模型中,“段”是哪一层数据封装的名称()A:物理层 B:数据链路层 C:网络层 D:传输层33、备份路由器IOS的命令是:( )A: copy flash tftpB: copy running-config tftpC: copy IOS tftpD: copy startup-config tftp34、PPP工作在OSI的哪一层()A:物理层B:数据链路层 C:网络层 D:传输层35、FTP工作在OSI哪一层()A:会话层 B:表示层 C:传输层D:应用层36、TELNET工作在OSI哪一层()A:会话层 B:表示层 C:传输层D:应用层37、SMTP工作在OSI哪一层()A:会话层 B:表示层 C:传输层D:应用层38、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP地址所在子网的子网号为()A:192.168.50.32 B:192.168.80.64C:192.168.50.96 D:192.168.50.7139、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP地址所在子网的广播地址为()A:192.168.50.32 B:192.168.80.64C:192.168.50.96 D:192.168.50.7140、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP地址所在子网的子网有效IP为()A:192.168.50.33---192.168.50.39B:192.168.50.41---192.168.50.50C:192.168.50.65---192.168.50.70D:192.168.50.66---192.168.50.7541、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP和掩码结合,共划分了多少个子网(不包括全0子网和全1子网)()A: 8 B:30 C:6 D:1442、IP地址为:192.168.50.70,掩码为:255.255.255.248,则该IP和掩码结合划分子网时,每个子网的容量为()A:8 B:4 C:12 D:643、网络172.12.0.0需要划分子网,要求每个子网中有效IP数为458个,为了保证子网数最大,则掩码应为()A:255.255.255.0 B:255.255.254.0 C:255.255.0.0D:255.255.248.044、哪一个命令可以设置路由器特权用户的“明文密码”()A:enable password B:password C:enable secretD: secret45、RIP协议的管理距离是()A:100 B:110 C:120 D:15046、下列路由协议中,属于链路状态路由协议的是()A:RIP B:EIGRP C:IGRP D:OSPF47、默认情况下,RIP定期发送路由更新的时间是()A:15S B:30S C:60S D:90S48、如果网络中的路由器都是cisco路由器,则优先选择哪一个路由协议()A:RIP B:EIGRP C:IGRP D:OSPF49、下列对RIP的配置中,合法的命令是()A: router rip 100network 10.12.0.0B: router rip 100network 10.0.0.0C: router ripnetwork 10.12.0.0D: router rip 100network 10.0.0.050、为了查看路由器的E0端口上,是否挂接了访问权限表,应该使用的命令是()A:show access-list B:show interface e0C: show ip interface e0 D:show e051、关于帧中继的说法,正确的是()A:速率最大为1Mbit/s B: 不提供差错校验功能C:可以偷占带宽 D:数据传输质量高于DDN52、关于PPP和HDLC的说法中,错误的是()A:PPP是通用协议,HDLC是CISCO私有协议B:PPP有验证功能,HDLC无验证功能C:PPP效率低,HDLC效率高D:在配置ISDN时,广域网协议不能封装成PPP,但可以封装成HDLC 53、对交换机的描述,正确的是()A:单广播域,单冲突域的设备B:单广播域,多冲突域的设备C:多广播域,单冲突域的设备D:多广播域,多冲突域的设备54、对路由器的描述,正确的是()A:单广播域,单冲突域的设备B:单广播域,多冲突域的设备C:多广播域,单冲突域的设备D:多广播域,多冲突域的设备55、交换机上VLAN的功能描述中,正确的是()A:可以减少广播域的个数B:可以减少广播对网络性能的影响C: 可以减少冲突域的个数D: 可以减小冲突域的容量56、两个VLAN之间要想通信,应该使用的设备是()A:集线器 B:二层交换机C:路由器 D:PC机57、要把交换机的配置文件保存到tftp服务器,应使用的命令为()A:copy ios tftp B:copy running-config tftpC: copy flash tftp D:copy config tftp58、命令“ping 127.0.0.1”的功能是()A:测试网卡是否正常 B:测试网关是否正常C:测试TCP/IP协议是否正常 D:测试介质是否正常59、路由器上的命令“show version”的功能是()A:显示版本信息 B:显示端口配置信息 C:显示路由表D:显示路由协议信息60、路由器上激活端口的命令是()A:shutdown B:no shutdown C: up D:no up61、某台PC,能ping通路由器,但不能telnet到路由器,可能的原因是(D )A:PC的IP地址设置错误 B:路由器端口IP设置错误C:路由器端口处于关闭状态D:telnet密码未设置62、OSI七层模型中,网络层的数据封装名称为()A:比特 B:帧C:包 D:段63、OSI七层模型中,物理层的数据封装名称为()A:比特 B:帧 C:包 D:段64、OSI七层模型中,数据链路层的数据封装名称为()A:比特B:帧 C:包 D:段65、OSI七层模型中,传输层的数据封装名称为()A:比特 B:帧 C:包D:段66、帧中继环境下,为了区分虚电路,应该使用的地址是()A:IP地址 B:MAC地址 C:DLCI D:IPX地址67、路由器“路由模式”的提示符号是()A: # B: (config)# C:(config-if)# D:(config-router)# 68、EIGRP的管理距离()A:90 B:100 C:110 D:12069、RIP协议负载均衡的路径数量为()A:无限制 B:最多4条 C:最多5条D:最多6条70、下面有关交换机的描述中,正确的是()A:所有交换机都支持VLAN功能B:交换机端口数量最多为48口C:交换机独占带宽D:交换机端口的最大速率为100Mbit/s71、为了阻止交换机环路,交换机上所采用的技术为()A:水平分割 B:生成树协议 C:触发更新 D:地址学习72、帧中继环境中,CIR的含义是()A:提高线路速率B:保证线路速率 C:降低线路速率D:配置线路速率73、路由器上端口fa0/0,其最大传输速率是()Mbit/sA:128 B: 10 C:100 D: 100074、帧中继环境中,在物理端口上,建立子接口的命令是()A:create B:interface C:encapsulation D:ip address 75、路由器上,命令“show int s0”的显示结果为:Serial0 is up , line protocol is down出现该结果的可能原因是()A:端口处于关闭状态 B:物理端口被烧毁C:两端设备协议不一致 D:路由表中无路由76、如果把路由器的某个端口的IP配置为:192.168.10.64,掩码配置为:255.255.255.248,则该端口()A:能和其他设备正常通信B:会变成“administratively down”状态C:端口被烧毁D:出现错误提示,配置命令执行失败77、网关的功能()A:过滤数据包B:不同网段通信 C:校验数据帧D:把数据封装成“段”78、能够分配给设备的IP,应该是()A:网络有效IP B:网络号 C:网络广播地址 D:任意IP 79、路由器“全局模式”的提示符为()A: > B: # C: (config)# D: (config-router)#80、路由器当前的模式为“端口模式”,要退回到“特权模式”,应该使用的快捷键为()A:ctrl+b B: ctrl+z C:ctrl+c D:ctrl+p81、下列命令中,无法正确执行的是()A:Router(config)#show runB: Router#ping 127.0.0.1C: Router(config)#hostname ciscoD: Router#reload82、路由器上,设置端口速率的命令是()A:clock rate B:bandwidth C:set D:encap83、路由器上,清空路由表的命令是()A:clear ip B:delete ip route C:delete routeD: clear ip route *84、路由表中,某条路由的“路由代码为D”,则表明该路由为()A:直连路由 B:静态路由 C:IGRP路由 D:EIGRP路由85、两台路由器直连到一起,应该使用的线缆为()A:交叉线缆 B:直通线缆 C:反转线缆 D:任意线缆86、通过路由器的“配置端口console”对路由器进行配置,应该使用的线缆为()A:交叉线缆 B:直通线缆C:反转线缆 D:任意线缆87、下面对Cisco2621路由器和Cisco2501路由器描述中,错误的是()A:Cisco2621路由器的可扩展性优于Cisco2501路由器B:Cisco2621是模块化路由器C:Cisco2501上提供一个100Mbit/s的快速以太网端口D:Cisco2501是固定端口的路由器88、为了连接“帧中继”线路,网络中的路由器需要提供的端口类型为()A:FastEthernet B:Serial C:BRI D:Ethernet89、路由器“特权模式”的提示符是:()A:> B:# C:(config)# D: (config-if)#90、下列关于路由器和交换机的描述中,错误的是()A:路由器可以用来连接internetB:二层交换机可以用来实现“异地网络”互连C:路由器可以用来做路径选择D:交换机可以转发广播二、多项选择题:正确答案的个数在每题的题后括号中有说明91、在路由器上,可以使用的命令有:( ) [选3个]A:ping B:show interfaces C:show ip route D:ipconfig E:wincfg92、在配置帧中继子接口时,在物理接口上应该配置的内容是:( )[选3个]A:配置IP地址B:封装帧中继协议C:指定子接口类型D:设定子接口 E:配置密码93、请选出交换机处理帧的三种模式:( )[选3个]A:直通模式 B:存储转发模式 C:侦测模式 D:分段模式E:阻塞模式94、对于IP为199.41.27.0,子网掩码为255.255.255.240,则该IP地址和子网掩码相作用会得到一系列IP,从下列选项中选出属于“有效IP”的选项:( ) [选3个]A:199.141.27.33 B:199.141.27.112 C:199.141.27.119D:199.141.27.126 E:199.141.27.175 F:199.141.27.208 95、属于私有IP段的是( )[选3个]A:10.0.0.0-10.255.255.255B:172.16.0.0-172.31.255.255 C:202.110.100.0-202.110.100.255D:192.168.0.0-192.168.255.255E:126.0.0.0-126.255.255.25596、下列哪一设备工作时,要用到OSI的七个层(一层到七层)()[选3个]A:PC B:网管机 C:WEB服务器 D:交换机 E:路由器97、网络中经常使用DDN服务,请选出DDN的优点()[选3个] A:传输质量高 B:接入方式灵活 C:偷占带宽D:使用虚电路E:专用线路98、网络中经常使用“帧中继”服务,请选出帧中继的优点()[选3个]A:偷占带宽B:提供拥塞管理机制C:可以使用任意广域网协议D:灵活的接入方式99、默认情况下,IGRP衡量路径好坏时,考虑的因素为()[选2个]A:带宽 B:可靠性 C:最大传输单元D:延时100、交换机的三大功能为()[选3个]A:地址学习 B:转发过滤 C:消除回路 D:发送数据包。
Cisco CCNA 认证考试最新真题
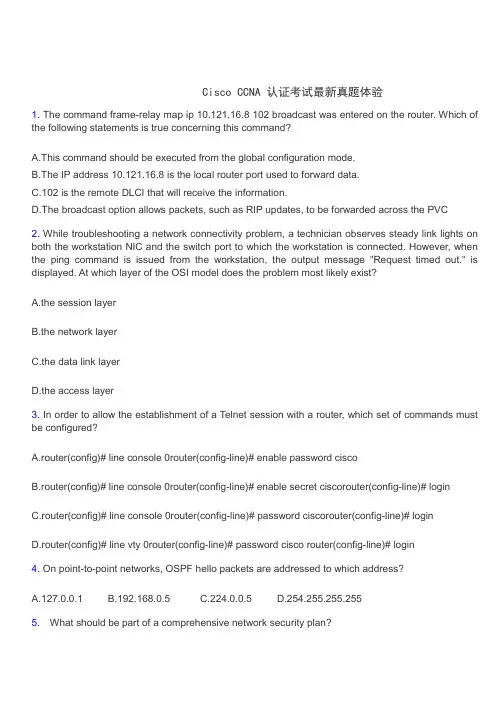
Cisco CCNA 认证考试最新真题体验1. The command frame-relay map ip 10.121.16.8 102 broadcast was entered on the router. Which of the following statements is true concerning this command?A.This command should be executed from the global configuration mode.B.The IP address 10.121.16.8 is the local router port used to forward data.C.102 is the remote DLCI that will receive the information.D.The broadcast option allows packets, such as RIP updates, to be forwarded across the PVC2. While troubleshooting a network connectivity problem, a technician observes steady link lights on both the workstation NIC and the switch port to which the workstation is connected. However, when the ping command is issued from the workstation, the output message "Request timed out." is displayed. At which layer of the OSI model does the problem most likely exist?A.the session layerB.the network layerC.the data link layerD.the access layer3. In order to allow the establishment of a Telnet session with a router, which set of commands must be configured?A.router(config)# line console 0router(config-line)# enable password ciscoB.router(config)# line console 0router(config-line)# enable secret ciscorouter(config-line)# loginC.router(config)# line console 0router(config-line)# password ciscorouter(config-line)# loginD.router(config)# line vty 0router(config-line)# password cisco router(config-line)# login4. On point-to-point networks, OSPF hello packets are addressed to which address?A.127.0.0.1B.192.168.0.5C.224.0.0.5D.254.255.255.2555. What should be part of a comprehensive network security plan?A.Allow users to develop their own approach to network security.B.Physically secure network equipment from potential access by unauthorized individualsC.Encourage users to use personal information in their passwords to minimize the likelihood of passwords being forgottenD.Delay deployment of software patches and updates until their effect on end-user equipment is well known and widely reported6. During startup, the router displays the following error message:boot: cannot open "flash:" What will the router do next?A.Because of damaged flash memory, the router will fail the POST.B.It will attempt to locate the IOS from a TFTP server. If this fails, it will initiate the setup dialogC.It will attempt to locate the IOS from a TFTP server. If this fails, it will load a limited IOS from ROM.D.It will attempt to locate the configuration file from a TFTP server. If this fails, it will initiate the setup dialog7. At which OSI layer is a logical path created between two host systems?A.sessionB.transportworkD.physical8. A routing protocol is required that supports:1) routing update authentication2) an addressing scheme that conserves IP addresses3) multiple vendors4) a network with over 50 routersWhich routing protocol fulfills these requirements?A.RIPv1B.RIPv2C.EIGRPD.OSPF9. When a new trunk is configured on a 2950 switch, which VLANs by default are allowed over the trunk link?A.no VLANsB.all VLANsC.only VLANs 1 - 6D.only the VLANs that are specified when creating the trunk10. Which protocol provides a method of sharing VLAN configuration information between switches?A.VTPB.STPC.ISLD.802.1QDBDCB CCDBA博主的更多文章>>CCNA第一学期《Final Examination》2009-02-27 08:58:47 标签:CCNA[推送到技术圈]1请参见图示。
新10月CCNA题库word版1~100题
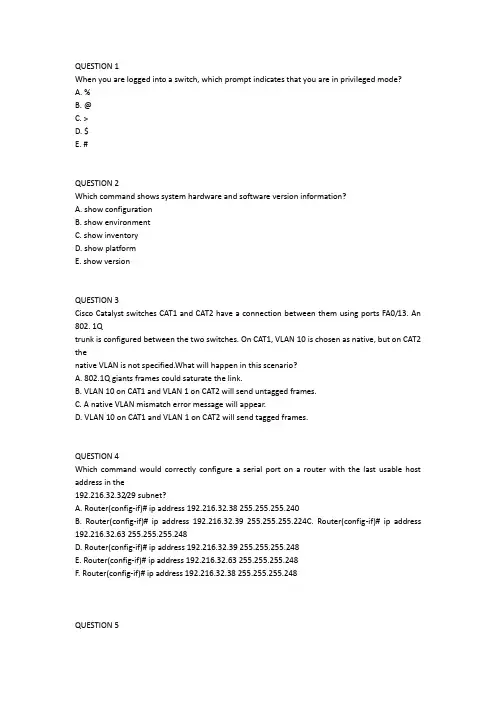
QUESTION 1When you are logged into a switch, which prompt indicates that you are in privileged mode?A. %B. @C. >D. $E. #QUESTION 2Which command shows system hardware and software version information?A. show configurationB. show environmentC. show inventoryD. show platformE. show versionQUESTION 3Cisco Catalyst switches CAT1 and CAT2 have a connection between them using ports FA0/13. An 802. 1Qtrunk is configured between the two switches. On CAT1, VLAN 10 is chosen as native, but on CAT2 thenative VLAN is not specified.What will happen in this scenario?A. 802.1Q giants frames could saturate the link.B. VLAN 10 on CAT1 and VLAN 1 on CAT2 will send untagged frames.C. A native VLAN mismatch error message will appear.D. VLAN 10 on CAT1 and VLAN 1 on CAT2 will send tagged frames.QUESTION 4Which command would correctly configure a serial port on a router with the last usable host address in the192.216.32.32/29 subnet?A. Router(config-if)# ip address 192.216.32.38 255.255.255.240B. Router(config-if)# ip address 192.216.32.39 255.255.255.224C. Router(config-if)# ip address 192.216.32.63 255.255.255.248D. Router(config-if)# ip address 192.216.32.39 255.255.255.248E. Router(config-if)# ip address 192.216.32.63 255.255.255.248F. Router(config-if)# ip address 192.216.32.38 255.255.255.248QUESTION 5The network default gateway applying to a host by DHCP is 192.168.5.33/28. Which option is the valid IPaddress of this host?A. 192.168.5.55B. 192.168.5.47C. 192.168.5.40D. 192.168.5.32E. 192.168.5.14QUESTION 6Which two addresses can be assigned to a host with a subnet mask of 255.255.254.0? (Choose two.)A. 113.10.4.0B. 186.54.3.0C. 175.33.3.255D. 26.35.2.255E. 17.35.36.0QUESTION 7The network administrator has asked you to check the status of the workstation's IP stack by pinging theloopback address. Which address would you ping to perform this task?A. 10.1.1.1B. 127.0.0.1C. 192.168.0.1D. 239.1.1.1QUESTION 8Workstation A has been assigned an IP address of 192.0.2.24/28. Workstation B has been assigned an IPaddress of 192.0.2.100/28. The two workstations are connected with a straight-through cable. Attempts toping between the hosts are unsuccessful. What two things can be done to allow communications betweenthe hosts? (Choose two.)A. Replace the straight-through cable with a crossover cable.B. Change the subnet mask of the hosts to /25.C. Change the subnet mask of the hosts to /26.D. Change the address of Workstation A to 192.0.2.15.E. Change the address of Workstation B to 192.0.2.111.QUESTION 9Your ISP has given you the address 223.5.14.6/29 to assign to your router's interface. They have alsogiven you the default gateway address of 223.5.14.7. After you have configured the address, the router isunable to ping any remote devices. What is preventing the router from pinging remote devices?A. The default gateway is not an address on this subnet.B. The default gateway is the broadcast address for this subnet.C. The IP address is the broadcast address for this subnet.D. The IP address is an invalid class D multicast address.QUESTION 10Which command is used to copy the configuration from RAM into NVRAM?A. copy running-config startup-configB. copy startup-config: running-config:C. copy running config startup configD. copy startup config running configE. write terminalQUESTION 11Which command is used to load a configuration from a TFTP server and merge the configuration intoRAM?A. copy running-config: TFTP:B. copy TFTP: running-configC. copy TFTP: startup-configD. copy startup-config: TFTP:QUESTION 12A system administrator types the command to change the hostname of a router. Where on the Cisco IFS isthat change stored?A. NVRAMB. RAMC. FLASHD. ROME. PCMCIAQUESTION 13Which command is used to configure a default route?A. ip route 172.16.1.0 255.255.255.0 0.0.0.0B. ip route 172.16.1.0 255.255.255.0 172.16.2.1C. ip route 0.0.0.0 255.255.255.0 172.16.2.1D. ip route 0.0.0.0 0.0.0.0 172.16.2.1QUESTION 14If IP routing is enabled, which two commands set the gateway of last resort to the default gateway?(Choose two.)A. ip default-gateway 0.0.0.0B. ip route 172.16.2.1 0.0.0.0 0.0.0.0C. ip default-network 0.0.0.0D. ip default-route 0.0.0.0 0.0.0.0 172.16.2.1E. ip route 0.0.0.0 0.0.0.0 172.16.2.1QUESTION 15Which command would you configure globally on a Cisco router that would allow you to view directlyconnected Cisco devices?A. enable cdpB. cdp enableC. cdp runD. run cdpQUESTION 16Which command is used to see the path taken by packets across an IP network?A. show ip routeB. show routeC. tracerouteD. trace ip routeQUESTION 17Which command is used to debug a ping command?A. debug icmpB. debug ip icmpC. debug tcpD. debug packetQUESTION 18Which command displays CPU utilization?A. show protocolsB. show processC. show systemD. show versionQUESTION 19When configuring a serial interface on a router, what is the default encapsulation?A. atm-dxiB. frame-relayC. hdlcD. lapbE. pppQUESTION 20What must be set correctly when configuring a serial interface so that higher-level protocols calculate thebest route?A. bandwidthB. delayC. loadD. reliabilityQUESTION 21A company implements video conferencing over IP on their Ethernet LAN. The users notice that thenetwork slows down, and the video either stutters or fails completely. What is the most likely reason forthis?A. minimum cell rate (MCR)B. quality of service (QoS)C. modulationD. packet switching exchange (PSE)E. reliable transport protocol (RTP)QUESTION 22Which layer in the OSI reference model is responsible for determining the availability of the receivingprogram and checking to see if enough resources exist for that communication?A. transportB. networkC. presentationD. sessionE. applicationQUESTION 23Data transfer is slow between the source and destination. The quality of service requested by the transportlayer in the OSI reference model is not being maintained. To fix this issue, at which layer should thetroubleshooting process begin?A. presentationB. sessionC. transportD. networkE. physicalQUESTION 24Which protocols are found in the network layer of the OSI reference model and are responsible for pathdetermination and traffic switching?A. LANB. routingC. WAND. networkQUESTION 25Which command reveals the last method used to powercycle a router?A. show reloadB. show bootC. show running-configD. show versionQUESTION 26Which three options are valid WAN connectivity methods? (Choose three.)A. PPPB. WAPC. HDLCD. MPLSE. L2TPv3CCNA考试报名1700元7F. ATMQUESTION 27Refer to the exhibit. Which WAN protocol is being used?A. ATMB. HDLCC. Frame RelayD. PPPQUESTION 28What is the difference between a CSU/DSU and a modem?A. A CSU/DSU converts analog signals from a router to a leased line; a modem converts analog signalsfrom a router to a leased line.B. A CSU/DSU converts analog signals from a router to a phone line; a modem converts digital signalsfrom a router to a leased line.C. A CSU/DSU converts digital signals from a router to a phone line; a modem converts analog signalsfrom a router to a phone line.D. A CSU/DSU converts digital signals from a router to a leased line; a modem converts digital signalsfrom a router to a phone line.QUESTION 29A network administrator must configure 200 switch ports to accept traffic from only the currently attachedCCNA考试报名1700元8host devices. What would be the most efficient way to configure MAC-level security on all these ports?A. Visually verify the MAC addresses and then telnet to the switches to enter the switchport-port securitymac-address command.B. Have end users e-mail their MAC addresses. Telnet to the switch to enter the switchport-port securitymac-address command.C. Use the switchport port-security MAC address sticky command on all the switch ports that have enddevices connected to them.D. Use show mac-address-table to determine the addresses that are associated with each port and thenenter the commands on each switch for MAC address port-security.QUESTION 30When troubleshooting a Frame Relay connection, what is the first step when performing a loopback test?A. Set the encapsulation of the interface to HDLC.B. Place the CSU/DSU in local-loop mode.C. Enable local-loop mode on the DCE Frame Relay router.D. Verify that the encapsulation is set to Frame Relay.What occurs on a Frame Relay network when the CIR is exceeded?A. All TCP traffic is marked discard eligible.B. All UDP traffic is marked discard eligible and a BECN is sent.C. All TCP traffic is marked discard eligible and a BECN is sent.D. All traffic exceeding the CIR is marked discard eligible.QUESTION 32What are two characteristics of Frame Relay point-to-point subinterfaces? (Choose two.)A. They create split-horizon issues.B. They require a unique subnet within a routing domain.C. They emulate leased lines.D. They are ideal for full-mesh topologies.E. They require the use of NBMA options when using OSPF.QUESTION 33Refer to the exhibit. Addresses within the range 10.10.10.0/24 are not being translated to the 1.128.0/16range. Which command shows if 10.10.10.0/24 are allowed inside addresses?A. debug ip natB. show access-listC. show ip nat translationD. show ip nat statisticsQUESTION 34A wireless client cannot connect to an 802.11b/g BSS with a b/g wireless card. The client sectionof theaccess point does not list any active WLAN clients. What is a possible reason for this?A. The incorrect channel is configured on the client.B. The client's IP address is on the wrong subnet.C. The client has an incorrect pre-shared key.D. The SSID is configured incorrectly on the client.QUESTION 35Which two features did WPAv1 add to address the inherent weaknesses found in WEP? (Choose two.)CCNA考试报名1700元10艾迪飞论坛艾迪飞论坛A. a stronger encryption algorithmB. key mixing using temporal keysC. shared key authenticationD. a shorter initialization vectorE. per frame sequence countersQUESTION 36Which two wireless encryption methods are based on the RC4 encryption algorithm? (Choose two.)A. WEPB. CCKMC. AESD. TKIPE. CCMPQUESTION 37What are two characteristics of RIPv2? (Choose two.)A. classful routing protocolB. variable-length subnet masksC. broadcast addressingD. manual route summarizationE. uses SPF algorithm to compute pathQUESTION 38Which two Ethernet fiber-optic modes support distances of greater than 550 meters?A. 1000BASE-CXCCNA考试报名1700元11艾迪飞论坛艾迪飞论坛艾迪飞论坛B. 100BASE-FXC. 1000BASE-LXD. 1000BASE-SXE. 1000BASE-ZXQUESTION 39What two things will a router do when running a distance vector routing protocol? (Choose two.)A. Send periodic updates regardless of topology changes.B. Send entire routing table to all routers in the routing domain.C. Use the shortest-path algorithm to the determine best path.D. Update the routing table based on updates from their neighbors.E. Maintain the topology of the entire network in its database.QUESTION 40Refer to the exhibit. According to the routing table, where will the router send a packet destined for10.1.5.65?A. 10.1.1.2B. 10.1.2.2C. 10.1.3.3D. 10.1.4.4QUESTION 41Which command shows if an access list is assigned to an interface?A. show ip interface [interface] access-listsB. show ip access-lists interface [interface]C. show ip interface [interface]D. show ip access-lists [interface]QUESTION 42Refer to the exhibit. Which rule does the DHCP server use when there is an IP address conflict?A. The address is removed from the pool until the conflict is resolved.B. The address remains in the pool until the conflict is resolved.C. Only the IP detected by Gratuitous ARP is removed from the pool.D. Only the IP detected by Ping is removed from the pool.E. The IP will be shown, even after the conflict is resolved.QUESTION 43Refer to the exhibit. You are connected to the router as user Mike. Which command allows you to seeoutput from the OSPF debug command?A. terminal monitorB. show debuggingC. show sessionsD. show ip ospf interfaceQUESTION 44Refer to the exhibit. If number 2 is selected from the setup script, what happens when the user runs setupfrom a privileged prompt?A. Setup is additive and any changes will be added to the config script.B. Setup effectively starts the configuration over as if the router was booted for the first time.C. Setup will not run if an enable secret password exists on the router.D. Setup will not run, because it is only viable when no configuration exists on the router.QUESTION 45Refer to the exhibit. Which (config-router) command will allow the network represented on the interface tobe advertised by RIP?A. redistribute ethernet0B. network ethernet0CCNA考试报名1700元14艾迪飞论坛艾迪飞论坛C. redistribute 10.12.0.0D. network 10.12.0.0QUESTION 46Refer to the exhibit. What information can be gathered from the output?A. One router is running RIPv1.B. RIP neighbor is 224.0.0.9.C. The network contains a loop.D. Network 10.10.1.0 is reachable.QUESTION 47Refer to the exhibit. What type of connection would be supported by the cable diagram shown?A. PC to routerB. PC to switchC. server to routerD. router to routerQUESTION 48Refer to the exhibit. What type of connection would be supported by the cable diagram shown?A. PC to routerB. PC to switchC. server to switchD. switch to routerQUESTION 49Which two statements describe the Cisco implementation of VLANs? (Choose two.)A. VLAN 1 is the default Ethernet VLAN.B. CDP advertisements are only sent on VLAN 1002.C. By default, the management VLAN is VLAN 1005.D. By default, the switch IP address is in VLAN 1005.E. VLAN 1002 through 1005 are automatically created and cannot be deleted.QUESTION 50Refer to the exhibit. What can be determined about the router from the console output?A. No configuration file was found in NVRAM.B. No configuration file was found in flash.C. No configuration file was found in the PCMCIA card.D. Configuration file is normal and will load in 15 seconds.QUESTION 52Refer to the exhibit. Which command would allow the translations to be created on the router?A. ip nat pool mynats 1.1.128.1 1.1.135.254 prefix-length 19B. ip nat outside mynats 1.1.128.1 1.1.135.254 prefix-length 19C. ip nat pool mynats 1.1.128.1 1.1.135.254 prefix-length 18D. ip nat outside mynats 1.1.128.1 1.1.135.254 prefix-length 18QUESTION 53Refer to the exhibit. An administrator pings the default gateway at 10.10.10.1 and sees the output asshown. At which OSI layer is the problem?A. data link layerB. application layerC. access layerD. session layerE. network layerQUESTION 54Refer to the exhibit. Which value will be configured for Default Gateway of the Local Area Connection?A. 10.0.0.0B. 10.0.0.254C. 192.223.129.0D. 192.223.129.254QUESTION 55Refer to the exhibit. The user at Workstation B reports that Server A cannot be reached. What is preventing Workstation B from reaching Server A?A. The IP address for Server A is a broadcast address.B. The IP address for Workstation B is a subnet address.C. The gateway for Workstation B is not on the same subnet.D. The gateway for Server A is not on the same subnet.QUESTION 56Refer to the exhibit. What does the (*) represent in the output?A. Packet is destined for a local interface to the router.B. Packet was translated, but no response was received from the distant device.C. Packet was not translated, because no additional ports are available.D. Packet was translated and fast switched to the destination.QUESTION 57Refer to the exhibit. What command sequence will enable PAT from the inside to outside network?A. (config) ip nat pool isp-net 1.2.4.2 netmask 255.255.255.0 overloadB. (config-if) ip nat outside overloadC. (config) ip nat inside source list 1 interface ethernet1 overloadD. (config-if) ip nat inside overloadQUESTION 58Refer to the exhibit. What will happen to HTTP traffic coming from the Internet that is destined for172.16.12.10 if the traffic is processed by this ACL?A. Traffic will be dropped per line 30 of the ACL.B. Traffic will be accepted per line 40 of the ACL.C. Traffic will be dropped, because of the implicit deny all at the end of the ACL.D. Traffic will be accepted, because the source address is not covered by the ACL.QUESTION 59Refer to the exhibit. Which statement describes the effect that the Router1 configuration has on devices inthe 172.16.16.0 subnet when they try to connect to SVR-A using Telnet or SSH?A. Devices will not be able to use Telnet or SSH.B. Devices will be able to use SSH, but not Telnet.C. Devices will be able to use Telnet, but not SSH.D. Devices will be able to use Telnet and SSH.QUESTION 60What are three advantages of VLANs? (Choose three.)A. VLANs establish broadcast domains in switched networks.B. VLANs utilize packet filtering to enhance network security.C. VLANs provide a method of conserving IP addresses in large networks.D. VLANs provide a low-latency internetworking alternative to routed networks.E. VLANs allow access to network services based on department, not physical location.F. VLANs can greatly simplify adding, moving, or changing hosts on the network.QUESTION 61An administrator would like to configure a switch over a virtual terminal connection from locations outsideof the local LAN. Which of the following are required in order for the switch to be configured from a remotelocation? (Choose two.)A. The switch must be configured with an IP address, subnet mask, and default gateway.B. The switch must be connected to a router over a VLAN trunk.C. The switch must be reachable through a port connected to its management VLAN.D. The switch console port must be connected to the Ethernet LAN.E. The switch management VLAN must be created and have a membership of at least one switchport.F. The switch must be fully configured as an SNMP agent.QUESTION 62Which of the following host addresses are members of networks that can be routed across the publicInternet? (Choose three.)A. 10.172.13.65B. 172.16.223.125C. 172.64.12.29D. 192.168.23.252E. 198.234.12.95F. 212.193.48.254QUESTION 63Given a subnet mask of 255.255.255.224, which of the following addresses can be assigned to networkhosts? (Choose three.)A. 15.234.118.63B. 92.11.178.93C. 134.178.18.56D. 192.168.16.87E. 201.45.116.159F. 217.63.12.192QUESTION 64Which of the following are benefits of VLANs? (Choose three.)A. They increase the size of collision domains.B. They allow logical grouping of users by function.C. They can enhance network security.D. They increase the size of broadcast domains while decreasing the number of collision domains.E. They increase the number of broadcast domains while decreasing the size of the broadcast domains.F. They simplify switch administration.Which router IOS commands can be used to troubleshoot LAN connectivity problems? (Choose three.)A. pingB. tracertC. ipconfigD. show ip routeE. winipcfgF. show interfacesQUESTION 67。
完整版CCNA测试题库及答案
完整版CCNA测试题库及答案描述载波侦听多路由访问/冲突检测(CSMA/CD)的工作原理。
CSMA/CD是一种帮助设备均衡共享带宽的协议,可避免两台设备同时在网络介质上传输数据。
虽然他不能消除冲突,但有助于极大的减少冲突,进而避免重传,从而提高所的设备的数据传输效率。
区分半双工和全双工通信。
并指出两种方法的需求。
与半双工以太网使用一对导线不同,全双工以太网使用两队导线,全双工使用不同的导线来消除冲突,从而允许同时发送和接收数据,而半双工可接收或发送数据,但不能同时接收和发送数据,且仍会出现冲突。
要使用全双工,电缆两端的设备都必须支持全双工,并配置成一全双模式运行。
描述MAC地址的组成部分以及各部分包含的信息。
MAC(硬件)地址时一种使用十六进制表示的地址,长48位(6B)。
其中前24位(3B)称为OUI(Organizationally Unique Idebtifier,组织唯一表示符),有IEEE分配给NIC制造商;余下的部分呢唯一地标识了NIC识别十进制数对应的二进制值和十六进制值。
用这三种格式之一表示的任何数字都可以转换为其他两种格式,能够执行这种转换对理解IP地址和子网划分至关重要。
识别以太网帧中与数据链路层相关的字段。
在以太网中,与数据链路层相关的字段包括前导码,帧其实位置分隔符,目标MAC地址,源MAC地址,长度或者类型以及帧校验序列。
识别以太网布线相关的IEEE标准。
这些标准描述了各种电缆类型的功能和物理特征,包括(但不限于)10Base2、10Base5和10BaseT。
区分以太网电缆类型及其用途。
以太网电缆分3种:直通电缆,用于将PC或路由器的以太网接口连接到集线器或交换机;交叉电缆。
用于将集线器连接到集线器,集线器连接到交换机,交换机连接到交换机以及PC连接到PC;反转电缆,用于PC和路由器或交换机之间建立控制台连接。
描述数据封装过程及其在分组创建中的作用。
数据封装指的是在OSI模型各层给数据添加信息的过程,也成为分组创建。
CCNA题库V104.2 补充新题 64Q(题库改版后新题目)
学网络技术去鸿鹄论坛命运的改变从技术开始鸿鹄团队致力于为每一位网络技术爱好者提供帮助有事您发帖,斑竹为您跑腿,给您答疑。
CCNA题库战报交流群:82327397欢迎备考CCNA的朋友加入,一起讨论交流,通过CCNA考试!CCNA最新题库/最新战报发布区:/forum-261-1.htmlCCNA考试代号:640-802考试时间:中文110分钟英文110+30=140分钟通过分数:825题库版本:V104.2Exam AQUESTION 1Which two commands correctly verify whether port security has been configured on port FastEthernet 0/12on a switch?(choose two)A.SW1#show swithport port-security interface FastEthernet 0/12B.SW1# show swithport port-secure interface FastEthernet 0/12C.SW1# show port-secure interface FastEthernet 0/12D.SW1#show running-configAnswer: CDQUESTION 2Which component of VPN technology ensures that data can be read only by its intended recipient?A.data integrity B.encryption C.key exchange D.authenticationAnswer: DQUESTION 3Refer to the exhibit.What is the effect of the configuration that is shown?A.It tells the router or switch to try establish an SSH connection first and if that fail to use telnet.B.Itconfigures a cisco network device to use the SSH protocol on incoming communications via the virtualterminal ports.C.It allows seven failed login attempts before the VTY lines are temporarily shutdown.D.It configures the virtual terminal lines with the password 030752180500.E.It configures SSH globally for all logins.Answer: BQUESTION 4Which IPV6 routing protocol uses multicast group FFO2::8 to send updates?A.RIPng B.OSPFv3C.IS-IS for IPv6D.staticAnswer: Cb b s .h h 010.co mWhich of the following are true regarding the debug output shown in the graphic?(choose two)A.This router was configured with the commands:RtrA(config)#router ripRtrA(config-router)#version 2RtrA(config-router)#network 172.16.0.0RtrA(config-router)#network 10.0.0.0B.This router was configured with the commands:RtrA(config)#router ripRtrA(config-router)#network 172.16.0.0RtrA(config-router)#network 10.0.0.0C.etwork 10.0.0.0 will be displayed in the routing table.work 192.168.168.0 will be displayed in the routing table.E.This router was configured with the commands:RtrA(config)#router ripRtrA(config-router)#network 192.168.1.0RtrA(config-router)#network 10.0.0.0RtrA(config-router)#network 192.168.168.0F.split-horizon was disabled on this router.Answer: BCQUESTION 6The network administrator is asked to configure 113 point-to-point links.Which IP addressing scheme best defines the address range and subnet mask that meet the requirement and waste the fewest subnet and host addresses?A.10.10.0.0/18 subnetted with mask 255.255.255.252B.10.10.0.0/25 subnetted with mask 255.255.255.252C.10.10.0.0/24 subnetted with mask 255.255.255.252D.10.10.0.0/23 subnetted with mask 255.255.255.252E.10.10.0.0/16 subnetted with mask 255.255.255.252Answer: Db b s .h h 010.co mVLAN 3 is not yet configured on your switch.What happens if you set the switchport access vlan 3commmand interface configuration mode?A.The command is accepted and the respective VLAN is added to vlan dat.B.The command is rejected.C.The command is accepted and you must configure the VLAN manually.D.The port turns amber.Answer: AQUESTION 8Which parameter can be tuned to affect the selection of a static route as a backup.when a dynamic protocol is also being used?A.link bandwidth B.hop count C.link costD.administrative distanceE.link delayAnswer: DQUESTION 9Refer to the exhibit. In the Frame Relay network, which ip address would be assigned to the interfaces with point-to-poin PVCs?A.DLCI 16:192.168.10.1/24DLCI 17:192.168.10.2/24DLCI 99:192.168.10.3/24DLCI 28:192.168.10.4/24b b s .h h 010.co mB.DLCI 16:192.168.10.1/24DLCI 17:192.168.11.1/24DLCI 99:192.168.10.2/24DLCI 28:192.168.11.2/24C.DLCI 16:192.168.10.1/24DLCI 17:192.168.11.1/24DLCI 99:192.168.12.1/24DLCI 28:192.168.13.1/24D.DLCI 16:192.168.10.1/24DLCI 17:192.168.10.1/24DLCI 99:192.168.10.2/24DLCI 28:192.168.10.3/24Answer: BQUESTION 10Why will a switch never learn a broadcast address?A.Broadcast frames are never sent to swiches.B.Broadcast addresses use an incorrect format for the switching table.C. A broadcast address will never be the source address of a frame.D.Broadcasts only use network layer addressing.E.A broadcast frame is never forwarded by a switch.Answer: CQUESTION 11Wich command can you use to manually assign a static IPV6 address to a muter interface?A.ipv6 address PREFIX_1::1/64B.ipv6 autoconfig 2001:db8:2222:7272::72/64C.ipv6 autoconfigD.ipv6 address 2001:db8:2222:7272::72/64Answer: DQUESTION 12The EIGRP configuration in the Glencoe router uses a single network statement.From the output shown in the graph would advertise these networks in EIGRP?b b s .h h 010.co mwork 172.26.168.0 area 478work 172.26.0.0work 172.26.168.128 0.0.0.127work 172.26.168.128 area 478Answer: BQUESTION 13Which IPsec security protocol should be used when confidentiality is required?A.AH B.MD5C.PSK D.ESPAnswer: DQUESTION 14What is the function of the command switchport trunk native vlan 999 on a…(此处文字不清楚).?A.It designates VLAN 999 for untagged traffic.B.It blocks VLAN 999 traffic from passing on the trunk.C.It creates a VLAN 999 interface.D.It designates VLAN 999 as the default for all unkown tagged traffic.Answer: DQUESTION 15Which command can be used from a PC to verfy the connectivity between host that connect thro…(字体不清)…?A.tracert address B.ping address C.arp addressD.traceroute addressAnswer: AQUESTION 16In which solution is a router ACL used?A.protecting a server frome unauthorized accesB.controlling path selection,based on the route metricC.reducing router CPU utilizationD.filterring packets that are passing through a routerAnswer: DQUESTION 17Which statement is true, as relates to classful or classless routing?b b s .h h 010.co mA.RIPV1 and OSPF are classless routing protocols.B.Classful routing protocols send the subnet mask in routing updates.C.Automatic summarization at classful boundaries can cause problems on disc……D.EIGRP and OSPF are classful routing protocols and summarize routes by def……Answer: CQUESTION 18A router has two FastEthernet interfaces and needs to connect to four vlans in the local network.How can you accomplish this task,using the fewest physical interfaces and without decreasing network performance?A.Add two more FastEthernet interfaces.B.Add a second router to handle the vlan traffic.e a hub to connect the four vlans with a FastEthernet interface on router.D.Implement a router-on-a-stick configuration.Answer: DQUESTION 19Refer to the exhibit.How many broadcast domains are configured on switch2?A.5B.20C.4D.1Answer: CQUESTION 20What is the effect of using the service password-encryption command?A.nly passwords configured after the command has been entered will be encrypted.B.Only the enable password will be encrypted.C.Only the enable secret password will be encryptedD.It will encrypt the secret password and remove the enable secret password from the configuration.E.It will encrypt all current and future passwords.Answer: Eb b s .h h 010.co mQUESTION 21Refer to the exhibit.A technician has installed SwithchB and needs to configure it for remote access from the management workstation connected SwitchA Which set of commands is required to accomplish this task?A.SwitchB(config)#interface FastEthernet 0/1SwitchB(config)#ip address 192.168.8.252 255.255.255.0SwitchB(config)#no shutdownB.SwitchB(config)#ip default-gateway 192.168.8.254SwitchB(config)#interface vlan 1SwitchB(config)#ip address 192.168.8.252 255.255.255.0SwitchB(config)#no shutdown C.SwitchB(config)#interface vlan 1SwitchB(config)#ip address 192.168.8.252 255.255.255.0SwitchB(config)#ip default-gateway 192.168.8.254 255.255.255.0SwitchB(config)#no shutdownD.SwitchB(config)#ip default-network 192.168.8.254SwitchB(config)#interface vlan 1SwitchB(config)#ip address 192.168.8.252 255.255.255.0SwitchB(config)#no shutdownAnswer: BQUESTION 22Refer to the exhibit.The speed of all serial links is E1 and the speed of the all Ethernet links is 100Mb/s.A static route will be established on the Manchester router to the direct traffic toward the internet over the most direct path available.What configuration on the Manchester router will establish a router toward the internet for traffic that originates from workstation on the Manchester LAN?b b s .h h 010.co mA.ip route 0.0.0.0 255.255.255.0 172.16.100.2B.ip route 0.0.0.0 255.255.255.252 128.107.1.1C.ip route 0.0.0.0 0.0.0.0 128.107.1.1D.ip route 0.0.0.0 0.0.0.0 172.16.100.1E.ip route 0.0.0.0 255.255.255.255 172.16.100.2F.ip route 0.0.0.0 0.0.0.0 172.16.100.2Answer: FQUESTION 23What Frame Relay mechanism is used to build the map illustrated in the accompanying graphic?A.inverse multiplexingB.LMI mapingC.Inverse ARPD.ARPE.Proxy ARPAnswer: CQUESTION 24Refer to the exhibit.A network engineer is troubleshooting an internet connectivity problem on the computer.What is causing the problem?b b s .h h 010.co mA.wrong DNS serverB.wrong default gatewayC.incorrect IP addressD.incorrect subnet maskAnswer: CQUESTION 25How many broadcast domains are shown in the graphic assuming only the default vlan is configured on the switches?b b s .h h 010.co mA.oneB.sixC.twelveD.twoAnswer: AQUESTION 26How dose a DHCP server dynamically assign IP address to host?A.Addresses are allocated after a negotiation between the server and the host to determine the length ofthe agreement.B.Addresses are assigned for a fixed period of time.At the end of period,a newquest for an address mustbe made ,and another address is then assigned.C.Addresses are leased to host.A host will usually keep the same address by periodically contacting theDHCP sever to renew the lease.D.Addresses are permanently assigned so that the host uses the same address at all times.Answer: CQUESTION 27Which type of EIGRP route entry describes a feasible successor?A. a primary route,stored in the routing table B. a backup route,stored in the routing table C. a backup route,stored in the topology table D.a primary route,stored in the topology tableAnswer: CQUESTION 28What is the purpose of the inverse ARP?A.to map a known DLCI to an IP addressB.to map a known IP address to a MAC addressC.to map known SPID to a MACaddressD.to map a known DLCI to a MAC addressE.to map a known IP address to a SPID.F.to map a known MAC address to an IP addressAnswer: AQUESTION 29What is the default maximum number of equal-cost paths that can be placed into the routing of a cisco OSPF router?A.16B.2C.unlimitedD.4Answer: Db b s .h h 010.co mQUESTION 30Which IPV6 routing protocol uses multicast group FF02::9 to send updates?A.RIPng B.OSPFv3C.staticD.IS-IS for IPv6Answer: AQUESTION 31What are two benefits of using NAT?(choose two)A.NAT protects network security because private networks are not advertised.B.NAT accelerates the routing process because no modifications are made on the packets.C.Dynamic NAT facilitates connections from the outside of the network.D.NAT facilitates end-to-end communication when IPsec is enable.E.NAT eliminates the need to re-address all host that require extemal access.F.NAT conserves addresses through host MAC-level multiplexing.Answer: AEQUESTION 32Which three statements about RSTP are true?(choose three)A.RSTP significantly reduces topology reconverging time after a link failure.B.RSTP expends the STP port roles by adding the alternate and backup roles.C.RSTP port atates are blocking,discarding,learing,or forwarding.D.RSTP also uses the STP proprsal-agreement sequence.E.RSTP use the same timer-baseed process as STP on point-to-point links.F.RSTP provides a faster transition to the forwarding state on point-to-point links than STP does.Answer: ABFQUESTION 33Refer to the exhibit.The serial0/0 interface of the Tampa router connects the Oriando router.Which two statements are true about the connection between these two routers?(choose two)b b s .h h 010.co mA.The only device with which the Tampa router will negotiate a data link is the Orlando router.B.The link is addressed on the *zero*subnet 10.0.0.0 network.C.The link uses a three-way handshake for authentication.D.The link uses a two-way handshake for authentication.E.Data exchanges between the Oriando and Tampa routers are encrypted.Answer: BCQUESTION 34A switch is configured as a vtp sever with a domain name of CCNA.Which cisco ios privileged modecommand,followed by a reload of the swith,will reset the VTP management domain name of the switch to a NULL value?A.#vtp domain unset B.#delete vlan.dat C.#no vtp domain D.#vtp domain nullAnswer: BQUESTION 35If an Ethernet port on a router was assigned an IP address of 172.1.1.1/20,what is the maximum number of hosts allowed on this subnet?A.4094B.1024C.8190D.2046b b s .h h 010.co mE.4096Answer: AQUESTION 36Which two statements about static NAT translations are true?(choose two)A.They are always present in the NAT table.B.They allow connection to be initiated from the outside.C.They can be configured with access lists, to allow two or more connections to be initiated from theoutside.D.They require no inside or outside interface markings because addresses are statically defined.Answer: ABQUESTION 37Which of these represents an IPv6 link-local address?A.FE08::280e:611:a:f14f:3d69B.FE81::280f:512b:e14f:3d69C.FE80::380e:611a:e14f:3d69D.FEFE:0345:5f1b::e14d:3d69Answer: CQUESTION 38What are three features of the IPV6 protocol?(choose three)plicated header B.plug-and-play C.no broadcasts D.checksums E.optional IPsec F.autoconfigurationAnswer: BCFQUESTION 39Assuming default setting,how can you erase the VTP database of VLANs on a CISCO IOS switch running in VTP server mode?A.Enable VTP pruningB.From privileged mode ,erase the startup configuration file,then reload.C.From privileged mode ,erase the vlan date file, then reload.D.Cycle the switch power.Answer: CQUESTION 40Refer to the exhibit.which address and mask combination a summary of the routes learned by EIGRP?b b s .h h 010.co mA.192.168.25.0 255.255.255.240B.192.168.25.16 255.255.255.252C.192.168.25.0 255.255.255.252D.192.168.25.28 255.255.255.240E.192.168.25.16 255.255.255.240F.192.168.25.28 255.255.255.240Answer: EQUESTION 41Refer to the exhibit A frame on vlan 1on switch s1 is sent to switch s2 when the frame is received on vlan 2,what causes this behavior?A.trunk mode mismatchesb b s .h h 010.co mB.vlans that do not correspond to a unique IP subnetC.native vlan mismatchesD.allowing only vlan 2 on the destination.Answer: CQUESTION 42Refer to the exhibit.The network administrator normally establishes a telnet session with the switch from host A.However,host A is unavailable.The administrator ′s attempt to the switch from host B fails,but pings to the other two hosts are successful.what is the issue?A.Host B and the switch need to be in the same subnet.B.The switch needs and appropriate default gateway assigned.C.The switch interface connected to the router is down.D.Host B need to be assigned an IP address in vlan 1.Answer: BQUESTION 43What value is primarily used to determine which port becomes the root port on each nonroot switch in a spanning-tree topology?A.lowest port MAC addressB.port priority number and MAC address.C.VTP revision numberD.highest port priority number.E.path costAnswer: EQUESTION 44Refer to the exhibit.Router 1 was just successfully rebooted.identify the current OSPF router ID for Router 1.b b s .h h 010.co mA.208.149.23.194B.220.173.149.10C.208.149.23.162D.190.172.32.10Answer: AQUESTION 45Why do large OSPF networks use a hierarchical design?(choose three)A.to confine network instability to single areas of the network.B.to reduce the complexity of router configuration C.to speed up convergenceD.to lower costs by replacing routers with distribution layer switchesE.to decrease latency by increasing bandwidthF.to reduce routing overheadAnswer: ACFQUESTION 46A network administrator receives an error message while tring to configure the Ethernet interface of a router with IP address 10.24.24.24/29.which statement explains the reason for this issue?A.The address is a broadcast address B.The Ehernet interface is faultyC.VLSM-capable routing protocols must be enable first on the router.D.This address is a network address.Answer: DQUESTION 47Which two are advantages of static routing when compared to dynamic routing?(choose two)A.Security increases because only the network administrator may change the routing tables.B.Configuration complexity decreases as network size increases.C.Routing updates are automatically sent to neighbors.D.Route summarization iscompued automatically by the router.E.Routing traffic load is reduced when used in stub network linksF.An efficient algorithm is used to build routing tables,using automatic updates.G.Routing tables adapt automatically to topology changes.b b s .h h 010.co mAnswer: AEQUESTION 48A company has a small network,consisting of a single switch and a single router.The switch has been configured with two vlans,and route-on-a-stick is being configured on the router for inter-vlan routing.A trunk is configured to connect the switch to the router.What is the minimum number of router subinterfaces that are required for all the vlans to communicate?A.one B.three C.two D.zeroAnswer: CQUESTION 49Which command can be a router to verify the layer 3 path to a host?A.traceroute address B.tracert address C.ssh address D.telnet addressAnswer: AQUESTION 50Which dose the frame-relay interface-dlc i command configure?A.remote DLCI on the main interface B.local DLCI on the main interface C.local DLCI on the subinterface D.remote DLCI on the subinterfaceAnswer: CQUESTION 51What is the OSPF default frequency,in seconds,at which a cisco router sends hello packets on a multi-access network?A.10B.40C.30D.20Answer: AQUESTION 52Refer to the exhibt.Host A has tested connectivity to a remote network.What is the default gateway for host A?b b s .h h 010.co mA.172.16.182.1B.192.168.1.1C.10.16.176.1D.192.168.1.6Answer: AQUESTION 53Which commands is necessary to permit SSH or Telnet access to a cisco switch that is otherwise configured for these vty line protocols?A.transport type allB.transport output allC.transport preferred allD.transport input allAnswer: DQUESTION 54Which command shows your active Telnet connections?A.show sessionB.show cdp neighborsC.show usersD.show queueAnswer: AQUESTION 55Which two states are the port states when RSTP has converged?(choose two)A.blocking B.learning C.disabled D.forwarding E.listeningAnswer: ADb b s .h h 010.co mQUESTION 56There are no boot system commands in a router configuration in NVRAM.What is the fallback sequence that router will use to find an ios during reload?A.Flash,TFTP server,ROM B.Flash,NVRAM,ROMC.ROM,NVRAM,TFTP serverD.NVRAM,TFTP server,ROME.TFTP server,Flash,NVRAMAnswer: A QUESTION 57Refer to the graphic.A host is connected to switch port Fa0/3 with a crossover cable.The host and switch have…as shown.However,the port indicator on switch port Fa0/3 is not on,and the host can notcommunicate with…to vlan 2 on the same switch.Based on the information given.what is the problem?A.The switch has been assigned an incorrect subnet mask.B.Switch port FA0/3 is not configured as a trunk port C.Switch port FA0/3 has been blocked by STPD.The switch and the hosts must be in the same subnetE.The cable is the wrong typeAnswer: E QUESTION 58Refer to the exhibit.Which user-mode password has just been set?A.Telnet B.Auxiliary C.SSH D.Consoleb b s .h h 010.co mAnswer: AQUESTION 59DNS servers provide what service?A.they run a spell check on host names to ensure accurate routingB.they map individual hosts to their specific IP addressC.they convert domain names into IP addressD.Given an IP address,they determine the name of the host that is…Answer: CQUESTION 60Which command enables RSTP on a switch?A.spanning-tree mode rapid-pvstB.spanning-tree uplinkfastC.spanning-tree backbonefastD.spanning-tree mode mst Answer: A QUESTION 61Which two are features of IPv6?(choose two)A.multicast B.broadcast C.allcastD.podcastE.anycast Answer: AE QUESTION 62Which statement about access lists that are applied to an interface is true?A.you can apply multiple access lists with the same protocol or in different…B.you can config one access list,per direction,per layer 3 protocolC.you can place as many access lists as you want on any interfaceD.you can apply ony one access list on any interfaceAnswer: DQUESTION 63Which item represents the standard IP ACL?A.access-list 50 deny 192.168.1.1 0.0.0.255B.access-list 110 permit ip any anyC.access-list 2500 deny tcp any host 192.168.1.1 eq 22D.access-list 101 deny tcp any host 192.168.1.1bbs.hh1.c o mAnswer: AQUESTION 64What is one benefit of PVST+?A.PVST+reduces the CPU cycles for all the switches in the networkB.PVST+automatically selects the root bridge location,to provide optimiz…C.PVST+allow the root switch location to be optimized per vlan.D.PVST+supports Layer 3 load balancing without loops.Answer: Cmoc.1hh.sbb。
最新CCNA题库 V102上卷(含答案无水印)
学网络技术去鸿鹄网网络技术从零开始梦想之路鸿鹄开启鸿鹄论坛:鸿鹄团队致力于为每一位网络技术爱好者提供帮助有事您发帖,斑竹为您跑腿,给您答疑。
CCNA CCNP最新题库/最新战报发布区:/thread.php?fid-166.html 鸿鹄客服QQ:712023090请加QQ群:96564501103107466鸿鹄题库新纪元CCNA V102上卷(共上下两卷,加lab集)1What can a network administrator utilize by using PPP Layer2encapsulation?(Choose three.)A.VLAN supportpressionC.AuthenticationD.Sliding windowsE.Multilink supportF.Quality of serviceAnswer:B,C,E2Which two statements best describe the wireless security standard that is defined by WPA? (Choose two.)A.It specifies use of a static encryption key that must be changed frequently to enhance security.B.It requires use of an open authentication method.C.It specifies the use of dynamic encryption keys that change each time a client establishes a connection.D.It requires that all access points and wireless devices use the same encryption key.E.It includes authentication by PSK.Answer:C,E3While troubleshooting a connectivity problem,a network administrator notices that a port status LED on a Cisco Catalyst series switch is alternating green and amber.Which condition could this indicate?A.The port is experiencing errors.B.The port is administratively disabled.C.The port is blocked by spanning tree.D.The port has an active link with normal traffic activity.Answer:A4Refer to the exhibit.The network shown in the exhibit is running the RIPv2routing protocol.The network has converged, and the routers in this network are functioning properly.The FastEthernet0/0interface on R1goes down.In which two ways will the routers in this networkrespond to this change?(Choose two.)A.All routers will reference their topology database to determine if any backup routes to the192.168.1.0network are known.B.Routers R2and R3mark the route as inaccessible and will not accept any further routing updates from R1until their hold-down timers expire.C.Because of the split-horizon rule,router R2will be prevented from sending erroneous information to R1about connectivity to the192.168.1.0network.D.When router R2learns from R1that the link to the192.168.1.0network has been lost,R2will respond by sending a route back to R1with an infinite metric to the192.168.1.0network.E.R1will send LSAs to R2and R3informing them of this change,and then all routers will send periodic updates at an increased rate until the network again converges.Answer:C,D5Which three statements are correct about RIP version2?(Choose three.)A.It has the same maximum hop count as version1.B.It uses broadcasts for its routing updates.C.It is a classless routing protocol.D.It has a lower default administrative distance than RIP version1.E.It supports authentication.F.It does not send the subnet mask in updates.Answer:A,C,E6What should be part of a comprehensive network security plan?A.Allow users to develop their own approach to network security.B.Physically secure network equipment from potential access by unauthorized individuals.C.Encourage users to use personal information in their passwords to minimize the likelihood of passwords being forgotten.D.Delay deployment of software patches and updates until their effect on end-user equipment is well known and widely reported.E.Minimize network overhead by deactivating automatic antivirus client updates.Answer:B7How should a router that is being used in a Frame Relay network be configured to avoid split horizonissues from preventing routing updates?A.Configure a separate sub-interface for each PVC with a unique DLCI and subnet assigned to thesub-interface.B.Configure each Frame Relay circuit as a point-to-point line to support multicast and broadcast traffic.C.Configure many sub-interfaces on the same subnet.D.Configure a single sub-interface to establish multiple PVC connections to multiple remote router interfaces.Answer:A8Refer to the exhibit.Which statement describes DLCI17?A.DLCI17xn R2and R3.B.DLCI17describes a PVC on R2.It cannot be used on R3or R1.C.DLCI17is the Layer2address used by R2to describe a PVC to R3.D.DLCI17describes the dial-up circuit from R2and R3to the service provider. Answer:C9Which routing protocol by default uses bandwidth and delay as metrics?A.RIPB.BGPC.OSPFD.EIGRPAnswer:D10Refer to the exhibit.Switch-1needs to send data to a host with a MAC address of00b0.d056.efa4.What will Switch-1do with this data?A.Switch-1will drop the data because it does not have an entry for that MAC address.B.Switch-1will flood the data out all of its ports except the port from which the data originated.C.Switch-1will send an ARP request out all its ports except the port from which the data originated.D.Switch-1will forward the data to its default gateway.Answer:B11Refer to the exhibit.Why would the network administrator configure RA in this manner?A.To give students access to the InternetB.To prevent students from accessing the command prompt of RAC.To prevent administrators from accessing the console of RAD.To give administrators access to the InternetE.To prevent students from accessing the InternetF.To prevent students from accessing the Admin networkAnswer:B12While troubleshooting a network connectivity problem,a technician observes steady link lights on boththe workstation NIC and the switch port to which the workstation is connected.However,when the ping command is issued from the workstation,the output message"Request timed out."is displayed.At which layer of the OSI model does the problem most likely exist?A.The session layerB.The protocol layerC.The data link layerD.The access layerE.The network layerF.The application layerAnswer:E13A network administrator has configured two switches,named London and Madrid,to use VTP. However,the switches are not sharing VTP messages.Given the command output shown in the graphicWhy are these switches not sharing VTP messages?A.The VTP version is not correctly configured.B.The VTP operating mode is not correctly configured.C.The VTP domain name is not correctly configured.D.VTP pruning mode is disabled.E.VTP V2mode is disabled.F.VTP traps generation is disabled.Answer:C14On point-to-point networks,OSPF hello packets are addressed to which address?A.127.0.0.1B.172.16.0.1C.192.168.0.5D.223.0.0.1E.224.0.0.5F.254.255.255.255Answer:E15Refer to the exhibit.The switches on a campus network have been interconnected as shown.All of the switches are running Spanning Tree Protocol with its default settings.Unusual traffic patterns are observed and it is discovered that Switch9is the root bridge.Which change will ensure that Switch1will be selected as the root bridge instead of Switch9?A.Lower the bridge priority on Switch1.B.Raise the bridge priority on Switch1.C.Lower the bridge priority on Switch9.D.Raise the bridge priority on Switch9.E.Disable spanning tree on Switch9.F.Physically replace Switch9with Switch1in the topology.Answer:A16You just entered the following command:Company(config)#line console0A.Configure the terminal type.B.Enter protocol parameters for a serial line.C.Create a password on the console terminal line.D.Establish a terminal type4connection to a remote host.Answer:C17The part of Company network is shown below:According to the diagram,which of the following is true about the internetwork?pany2is the root bridge.B.Spanning Tree is not runn ing.C.No collisions can occur in traffic between CompanyB and CompanyC.panyD and Company Server1are in the same network.E.If Fa0/0is down on Company-R,PassGuideA cannot access Company Server1Answer:E18Which three of the following are reasons for assigning ports to VLANs on a switch?(Choose three.)A.to permit more devices to connect to the networkB.to iscC.to logically group hosts on the basis of functionD.to increase network securityAnswer:B,C,D19The Company network is shown below:Based on the information shown above,when the Company network administrator attempts to ping Host Company-PC2from Host Company-PC1and shown.What is a possible problem?A.The link between Company1and Company2is down.B.Interface Fa0/0on Company2is shutdown.C.The link between Company2and Company3is down.D.The default gateway on Company-PC1is incorrect.Answer:C20What is the objective of a default route?A.Offering routing to override the configured dynamic routing protocolB.Offering routing to a local web serverC.Offering routing from an ISP to a stub networkD.Offering routing to a destination that is not specified in the routing table and which is outside the local networkAnswer:D21Which three benefits are of VLANs?(Choose three.)A.To increase the size of collision domains.B.To allow logical grouping of users by function.C.To enhance network security.D.To increase the number of broadcast domains while decreasing the size of the broadcast domains. Answer:B,C,D22A default Frame Relay WAN is classified as what type of physical network?A.Point-to-pointB.Broadcast multi-accessC.Nonbroadcast multi-accessD.Nonbroadcast multipointE.Broadcast point-to-multipointAnswer:C23Refer to the exhibit.How many broadcast domains exist in the exhibited topology?A.OneB.TwoC.ThreeD.FourE.FiveF.SixAnswer:C24The command frame-relay map ip10.121.16.8102broadcast was entered on the router.Which of thefollowing statements is true concerning this command?A.This command should be executed from the global configuration mode.B.The IP address10.121.16.8is the local router port used to forward data.C.102is the remote DLCI that will receive the information.D.This command is required for all Frame Relay configurations.E.The broadcast option allows packets,such as RIP updates,to be forwarded across the PVC. Answer:E25Which type of attack is characterized by a flood of packets that are requesting a TCP connection to a server?A.Denial of serviceB.Brute forceC.ReconnaissanceD.Trojan horseAnswer:A26Which of the following are associated with the application layer of the OSI model?(Choose two.)A.PingB.TelnetC.FTPD.TCPE.IPAnswer:B,C27What are two recommended ways of protecting network device configuration files from outside network security threats?(Choose two.)A.Allow unrestricted access to the console or VTY ports.e a firewall to restrict access from the outside to the network devices.C.Always use Telnet to access the device command line because its data is automatically encrypted.e SSH or another encrypted and authenticated transport to access device configurations.E.Prevent the loss of passwords by disabling password encryption.Answer:B,D28Refer to the exhibit.Switch1has just been restarted and has passed the POST routine.Host A sends its initial frame to Host C.What is the first thing the switch will do as regards populating the switching table?A.Switch1will add192.168.23.4to the switching table.B.Switch1will add192.168.23.12to the switching table.C.Switch1will add000A.8A47.E612to the switching table.D.Switch1will add000B.DB95.2EE9to the switching table.Answer:C29Exhibit:The user of Host1wants to ping the DSL modem/router at192.168.1.254.Based on the Host1 ARP table that is shown in the exhibit,what will Host1do?A.Send a unicast ARP packet to the DSL modem/routerB.Send unicast ICMP packets to the DSL modem/routerC.Send Layer3broadcast packets to which the DSL modem/router respondsD.Send a Layer2broadcast that is received by Host2,the switch,and the DSL modem/router Answer:B30Which spread spectrum technology does the802.11b standard define for operation?A.IRB.DSSSC.FHSSD.DSSS and FHSSE.IR,FHSS,and DSSSAnswer:B31Refer to the exhibit.Assume that all router interfaces are operational and correctly configured.In addition,assume that OSPF has been correctly configured on router R2.How will the default route configured on R1affect the operation of R2?A.Any packet destined for a network that is not directly connected to router R1will be dropped.B.Any packet destined for a network that is not directly connected to router R2will be dropped immediately.C.Any packet destined for a network that is not directly connected to router R2will be dropped immediately because of the lack of a gateway on R1.D.The networks directly connected to router R2will not be able to communicate with the172.16.100.0, 172.16.100.128,and172.16.100.64subnetworks.E.Any packet destined for a network that is not referenced in the routing table of router R2will be directed to R1.R1will then send that packet back to R2and a routing loop will occur.Answer:E32A network interface port has collision detection and carrier sensing enabled on a shared twisted pair network.From this statement,what is known about the network interface port?A.This is a10Mb/s switch port.B.This is a100Mb/s switch port.C.This is an Ethernet port operating at half duplex.D.This is an Ethernet port operating at full duplex.E.This is a port on a network interface card in a PC.Answer:C33Refer to the topology and router configuration shown in the graphic.A host on the LAN is accessing an FTP server across the Internet.Which of the following addresses could appear as a source address for the packets forwarded by the router to the destination server?A.10.10.0.1B.10.10.0.2C.199.99.9.33D.199.99.9.57E.200.2.2.17F.200.2.2.18Answer:D34What is the purpose of the Cisco VLAN Trunking Protocol?A.To allow traffic to be carried from multiple VLANs over a single link between switchesB.To allow native VLAN information to be carried over a trunk linkC.To allow for managing the additions,deletions,and changes of VLANs between switchesD.To provide a mechanism to manually assign VLAN membership to switch portsE.To provide a mechanism to dynamically assign VLAN membership to switch portsAnswer:C35Which two statements describe the Cisco implementation of VLANs?(Choose two.)A.VLAN1is the default Ethernet VLAN.B.CDP advertisements are only sent on VLAN1002.C.By default,the switch IP address is in VLAN1005.D.VLANs1002through1005are automatically created and cannot be deleted.Answer:A,D36Refer to the exhibit.What two results would occur if the hub were to be replaced with a switch that is configured with one Ethernet VLAN?(Choose two.)A.The number of collision domains would remain the same.B.The number of collision domains would decrease.C.The number of collision domains would increase.D.The number of broadcast domains would remain the same.E.The number of broadcast domains would decrease.F.The number of broadcast domains would increase.Answer:C,D37Three access points have been installed and configured to cover a small office.What term defines thewireless topology?A.BSSB.IBSSC.ESSD.SSIDAnswer:C38A TCP/IP transfer is diagrammed in the exhibit.A window size of three has been negotiated for this transfer.Which message will be returned from the receiver to the sender as part of this TCP/IP transfer?A.Send ACK1-3B.Send ACK3C.Send ACK4D.Send ACK4-6E.Send ACK6F.Send ACK7Answer:C39Which two statements are true based the output of the show frame-relay lmi command issued on the Branch router?(Choose two.)A.LMI messages are being sent on DLCI0.B.LMI messages are being sent on DLCI1023.C.Interface Serial0/0is not configured to encapsulate Frame Relay.D.The Frame Relay switch is not responding to LMI requests from the router.E.The LMI exchange between the router and Frame Relay switch is functioning properly.F.The router is providing a clock signal on Serial0/0on the circuit to the Frame Relay switch. Answer:A,D40.Refer to the graphic.A static route to the10.5.6.0/24network is to be configured on the HFD router. Which commands will accomplish this?(Choose two.)A.HFD(config)#ip route10.5.6.00.0.0.255fa0/0B.HFD(config)#ip route10.5.6.00.0.0.25510.5.4.6C.HFD(config)#ip route10.5.6.0255.255.255.0fa0/0D.HFD(config)#ip route10.5.6.0255.255.255.010.5.4.6E.HFD(config)#ip route10.5.4.60.0.0.25510.5.6.0F.HFD(config)#ip route10.5.4.6255.255.255.010.5.6.0Answer:CD41.What should be done prior to backing up an IOS image to a TFTP server?(Choose three.)A.Make sure that the server can be reached across the network.B.Check that authentication for TFTP access to the server is set.C.Assure that the network server has adequate space for the IOS image.D.Verify file naming and path requirements.E.Make sure that the server can store binary files.F.Adjust the TCP window size to speed up the transfer.Answer:ACD42.What are the possible trunking modes for a switch port?(Choose three.)A.transparentB.autoC.onD.desirableE.clientF.forwardingAnswer:BCD43.The network172.25.0.0has been divided into eight equal subnets.Which of the following IP addresses can be assigned to hosts in the third subnet if the ip subnet-zero command is configured on the router?(Choose three.)A.172.25.78.243B.172.25.98.16C.172.25.72.0D.172.25.94.255E.172.25.96.17F.172.25.100.16Answer:ACD44.Refer to the graphic.Host1cannot receive packets from Host2.Assuming that RIP v1is the routing protocol in use,what is wrong with the IP configuration information shown?(Choose two.)A.The fa0/1interface of router R2has been assigned a broadcast address.B.The fa0/1network on router R2overlaps with the LAN attached to R1.C.Host2has been assigned the incorrect subnet mask.D.Host1has been configured with the255.255.248.0subnet mask.E.Host2on router R2is on a different subnet than its gateway.Answer:BC45.What are three valid reasons to assign ports to VLANs on a switch?(Choose three.)A.to make VTP easier to implementB.to isolate broadcast trafficC.to increase the size of the collision domainD.to allow more devices to connect to the networkE.to logically group hosts according to functionF.to increase network securityAnswer:BEF46.Refer to the topology shown in the exhibit.Which ports will be STP designated ports if all the links areoperating at the same bandwidth?(Choose three.)A.Switch A-Fa0/0B.Switch A-Fa0/1C.Switch B-Fa0/0D.Switch B-Fa0/1E.Switch C-Fa0/0F.Switch C-Fa0/1Answer:BCD47.Which statements describe two of the benefits of VLAN Trunking Protocol?(Choosetwo.)A.VTP allows routing between VLANs.B.VTP allows a single switch port to carry information to more than one VLAN.C.VTP allows physically redundant links while preventing switching loops.D.VTP simplifies switch administration by allowing switches to automatically share VLAN configuration information.E.VTP helps to limit configuration errors by keeping VLAN naming consistent across the VTP domain.F.VTP enhances security by preventing unauthorized hosts from connecting to the VTP domain. Answer:DE48What are two results of entering the Switch(config)#vtp mode client command on a Catalyst switch?(Choose two.)A.The switch will ignore VTP summary advertisements.B.The switch will forward VTP summary advertisements.C.The switch will process VTP summary advertisementsD.The switch will originate VTP summary advertisements.E.The switch will create,modify and delete VLANs for the entire VTP domain.Answer:BC49.A network administrator issues the ping192.168.2.5command and successfully tests connectivity to a host that has been newly connected to the network.Which protocols were used during the test? (Choose two.)A.ARPB.CDPC.DHCPD.DNSE.ICMPAnswer:AE50.Refer to the exhibit.Host A is to send data to Host B.How will Router1handle the data frame received from Host A?(Choose three.)A.Router1will strip off the source MAC address and replace it with the MAC address on the forwardingFastEthernet interface.B.Router1will strip off the source IP address and replace it with the IP address on the forwarding FastEthernetinterface.C.Router1will strip off the destination MAC address and replace it with the MAC address of Host B.D.Router1will strip off the destination IP address and replace it with the IP address of Host B.E.Router1will forward the data frame out interface FastEthernet0/1.F.Router1will forward the data frame out interface FastEthernet0/2.Answer:ACF51.Refer to the exhibit.What will Router1do when it receives the data frame shown?(Choose three.)A.Router1will strip off the source MAC address and replace it with the MAC address0000.0c36.6965.B.Router1will strip off the source IP address and replace it with the IP address192.168.40.1.C.Router1will strip off the destination MAC address and replace it with the MAC address0000.0c07.4320.D.Router1will strip off the destination IP address and replace it with the IP address of192.168.40.1.E.Router1will forward the data packet out interface FastEthernet0/1.F.Router1will forward the data packet out interface FastEthernet0/2.Answer:ACF52.Refer to the exhibit.Host A pings Host B.What source MAC address and source IP address are contained in the frame as the frame leaves R2destined for host B?A.abcd.abcd.a001B.abcd.abcd.b002C.abcd.abcd.c003D.10.2.0.15E.10.0.64.1F.10.0.128.15Answer:BD53.Refer to the exhibit.A network associate has configured OSPF with the command:City(config-router)#network192.168.12.640.0.0.63area0After completing the configuration,the associate discovers that not all the interfaces are participating in OSPF.Which three of the interfaces shown in the exhibit will participate in OSPF according to this configuration statement?(Choose three.)A.FastEthernet0/0B.FastEthernet0/1C.Serial0/0D.Serial0/1.102E.Serial0/1.103F.Serial0/1.104Answer:BCD54.A Catalyst2950needs to be reconfigured.What steps will ensure that the old configuration is erased?(Choose three.)A.Erase flash.B.Restart the switch.C.Delete the VLAN database.D.Erase the runnin configuration.E.Erase the startup configuration.F.Modify the configurationregister.Answer:BCE55.Refer to the exhibit.The FMJ manufacturing company is concerned about unauthorized access to the Payroll Server.The Accounting1,CEO,Mgr1,and Mgr2workstations should be the only computers with access to the Payroll Server.What two technologies should be implemented to help prevent unauthorized access to the server?(Choose two.)A.access listsB.encrypted router passwordsC.STPD.VLANsE.VTPF.wireless LANsAnswer:AD56.Refer to the exhibit.What commands must be configured on the2950switch and the router to allow communication between host1and host2?(Choose two.)A.Router(config)#interface fastethernet0/0Router(config-if)#ip address192.168.1.1255.255.255.0Router(config-if)#no shut downB.Router(config)#interface fastethernet0/0Router(config-if)#no shut downRouter(config)#interface fastethernet0/0.1Router(config-subif)#encapsulation dot1q10Router(config-subif)#ip address192.168.10.1255.255.255.0Router(config)#interface fastethernet0/0.2Router(config-subif)#encapsulation dot1q20Router(config-subif)#ip address192.168.20.1255.255.255.0C.Router(config)#router eigrp100Router(config-router)#network192.168.10.0Router(config-router)#network192.168.20.0D.Switch1(config)#vlan databaseSwitch1(config-vlan)#vtp domain XYZSwitch1(config-vlan)#vtp serverE.Switch1(config)#interface fastethernet0/1Switch1(config-if)#switchport mode trunkF.Switch1(config)#interface vlan1Switch1(config-if)#ip default-gateway192.168.1.1Answer:BE57.Which three Layer2encapsulation types would be used on a WAN rather than a LAN?(Choose three.)A.HDLCB.EthernetC.Token RingD.PPPE.FDDIF.Frame RelayAnswer:ADF58.Refer to the exhibit.The two connected ports on the switch are not turning orange or green.What would be the most effective steps to troubleshoot this physical layer problem?(Choose three.)A.Ensure that the Ethernet encapsulations match on the interconnected router and switch ports.B.Ensure that cables A and B are straight-through cables.C.Ensure cable A plugged into a trunk port.D.Ensure the switch has power.E.Reboot all of the devices.F.Reseat all cables.Answer:BDF59.What can be determined from the line of show ip route output shown in the exhibit?(Choose two.)A.The next routing update can be expected in35seconds.B.The IP address10.10.10.6is configured on S0/1.C.The IP address10.10.10.8is configured on S0/1.D.This route is using the default administrative distance.E.The10.10.10.8network is two hops away from this router.Answer:DE60.Refer to the exhibit.All of the routers in the network are configured with the ip subnet-zero command.Which network addresses should be used for Link A and Network A?(Choose two.)work A-172.16.3.48/26work A-172.16.3.128/25work A-172.16.3.192/26D.Link A-172.16.3.0/30E.Link A-172.16.3.40/30F.Link A-172.16.3.112/30Answer:BD61.Which two subnetworks would be included in the summarized address of172.31.80.0/20? (Choose two.)A.172.31.17.4/30B.172.31.51.16/30C.172.31.64.0/18D.172.31.80.0/22E.172.31.92.0/22F.172.31.192.0/18Answer:DE62.The network administrator has discovered that the power supply has failed on a switch in the company LAN and that the switch has stopped functioning.It has been replaced with a Cisco Catalyst 2950series switch.What must be done to ensure that this new switch becomes the root bridge on the network?A.Lower the bridge prioritynumber.B.Change the MAC address of the switch.C.Increase the VTP revision number for the domain.D.Lower the root path cost on the switch ports.E.Assign the switch an IP address with the lowestvalue.Answer:A63.Refer to the exhibit.Assume that all of the router interfaces are operational and configured correctly.How will router R2be affected by the configuration of R1that is shown in the exhibit?A.Router R2will not form a neighbor relationship with R1.B.Router R2will obtain a full routing table,including a default route,from R1.C.R2will obtain OSPF updates from R1,but will not obtain a default route from R1.D.R2will not have a route for the directly connected serial network,but all other directly connected networks will be present,as well as the two Ethernet networks connected to R1.Answer:D64.Which three IP addresses can be assigned to hosts if the subnet mask is/27and subnet zero is usable? (Choose three.)A.10.15.32.17B.17.15.66.128C.66.55.128.1D.135.1.64.34E.129.33.192.192F.192.168.5.63Answer:ACD65.Refer to the exhibit.A packet with a source IP address of192.168.2.4and a destination IP address of 10.1.1.4arrives at the HokesB router.What action does the router take?A.forwards the received packet out the Serial0/0interfaceB.forwards a packet containing an EIGRP advertisement out the Serial0/1interfaceC.forwards a packet containing an ICMP message out the FastEthernet0/0interfaceD.forwards a packet containing an ARP request out the FastEthernet0/1interfaceAnswer:C66.Refer to the exhibit.From RouterA,a network administrator is able to ping the serial interface of RouterB but unable to ping any of the subnets attached to RouterB.Based on the partial outputs in the exhibit,what could be the problem?。
网络工程师CCNA证书考试题库
网络工程师CCNA证书考试题库网络工程师是当今社会上一种备受青睐的职业,具备CCNA证书是成为一名合格网络工程师的基本要求之一。
CCNA(Cisco Certified Network Associate)是思科公司提供的一种权威的网络证书,考试内容涵盖了网络基础知识、路由器和交换机配置、网络安全等方面的内容。
下面将为大家整理一份网络工程师CCNA证书考试题库,供大家参考和复习。
一、网络基础知识1. OSI参考模型中,哪一层负责确定数据如何在网络中传输?A. 应用层B. 传输层C. 网络层D. 数据链路层2. IP地址的子网掩码用来做什么?A. 区分网络地址和主机地址B. 确定网络的物理拓扑C. 控制网络访问权限D. 提高网络安全性3. TCP协议是一种什么类型的协议?A. 面向连接型B. 面向无连接型C. 面向消息型D. 面向数据流型4. 下面哪种传输介质是最适合用于在大楼内部连接不同楼层的网络设备?A. 双绞线B. 同轴电缆C. 光纤D. 无线电波二、路由器和交换机配置1. 在路由器上配置静态路由需要设置哪些参数?A. 出接口B. 下一跳地址C. 网关地址D. 子网掩码2. 交换机的VLAN技术主要用来实现什么功能?A. 提高网络传输速度B. 划分不同的广播域C. 增加网络安全性D. 实现无线网络连接3. 在路由器上配置NAT技术的目的是什么?A. 增加网络带宽B. 实现内网主机与外网通信C. 提高网络可靠性D. 实现跨平台数据传输4. 交换机端口默认是属于哪个VLAN?A. VLAN1B. VLAN10C. VLAN100D. VLAN1000三、网络安全1. 以下哪种加密算法用于保护传输过程中的数据机密性?A. DESB. MD5C. RSAD. SHA2. 防火墙的作用是什么?A. 限制网络带宽的使用B. 监控网络流量C. 阻止非法入侵D. 加快网络数据传输速度3. 在网络安全方面,ACL(访问控制列表)主要用来控制什么?A. 网络拓扑B. 主机访问权限C. 广播域D. 数据传输速度4. DDos攻击是指什么?A. 拒绝服务攻击B. 数据泄露攻击C. 蠕虫攻击D. 恶意代码攻击通过以上网络工程师CCNA证书考试题库的复习,相信大家可以更加全面地了解CCNA考试的内容要求,提升自己的备考水平。
ccna考试题库最新版
ccna考试题库最新版CCNA(Cisco Certified Network Associate)认证是全球范围内最受欢迎的网络工程师认证之一,具备CCNA认证可以证明一个人在建立、规划、运行、安装和配置中等规模的局域网和广域网方面的专业知识。
为了帮助广大考生顺利通过CCNA考试,不断更新的CCNA考试题库至关重要。
以下是最新版本的CCNA考试题库,希望对考生们有所帮助。
第一部分:网络基础知识1. 什么是OSI七层模型?简要介绍每一层的功能。
2. TCP和UDP之间有哪些区别?请分别举例说明。
3. 什么是IP地址?IP地址的类型有哪些?请列举并简要介绍各自的特点。
4. 什么是子网掩码?为什么在网络中使用子网掩码?5. 简述常见的网络设备有哪些,以及各自的功能与作用。
第二部分:路由和交换技术1. 路由器和交换机之间有何区别?请进行比较并指出各自的优势和劣势。
2. 什么是VLAN?VLAN的作用及在网络中的应用场景是什么?3. OSPF和EIGRP是两种常见的路由协议,请比较它们的特点并举例说明。
4. 请解释静态路由和动态路由的概念以及在网络中的应用。
5. 交换机在网络中扮演什么角色?交换机的MAC地址表是如何工作的?第三部分:网络安全和管理1. 网络安全的重要性是什么?请列举几种常见的网络安全威胁并介绍应对策略。
2. 什么是ACL(访问控制列表)?ACL的作用是什么?请给出一个ACL的配置示例。
3. VPN是什么?VPN的工作原理及在企业网络中的应用。
4. SNMP是网络管理中常用的协议,它的作用是什么?请解释SNMP中的几个重要概念。
5. 如何保护无线网络的安全?请列举几种方法。
第四部分:WAN技术1. 什么是WAN?WAN的主要特点是什么?2. PPP协议和HDLC协议分别是什么?请比较它们的异同。
3. 什么是Frame Relay?Frame Relay的工作原理及在WAN中的应用。
4. 请解释T1和E1的概念,以及它们在传输速率和应用方面的差异。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
270. EIGRPAfter adding RTR_2 router, no routing updates are being exchanged between RTR_1 and the new location. All other inter connectivity and internet access for the existing locations of the company are working properly.The task is to identify the fault(s) and correct the router configuration to provide full connectivity between the routers.Access to the router CLI can be gained by clicking on the appropriate host.All passwords on all routers are cisco .IP addresses are listed in the chart below.Answer:RTR_A#show run!!interface FastEthernet0/0ip address 192.168.60.97 255.255.255.240!interface FastEthernet0/1ip address 192.168.60.113 255.255.255.240!interface Serial0/0ip address 192.168.36.14 255.255.255.252clockrate 64000!router eigrp 212network 192.168.36.0network 192.168.60.0no auto-summary!RTR_A#show ip route192.168.36.0/30 is subnetted, 1 subnetsC 192.168.36.12 is directly connected, Serial 0/0192.168.60.0/24 is variably subnetted, 5 subnets, 2 masksC 192.168.60.96/28 is directly connected, FastEthernet0/0C 192.168.60.112/28 is directly connected, FastEthernet0/1D 192.168.60.128/28 [ 90/21026560 ] via 192.168.36.13, 00:00:57, Serial 0/0 D 192.168.60.144/28 [ 90/21026560 ] via 192.168.36.13, 00:00:57, Serial 0/0D 192.168.60.24/30 [ 90/21026560 ] via 192.168.36.13, 00:00:57, Serial 0/0 D* 198.0.18.0 [ 90/21026560 ] via 192.168.36.13, 00:00:57, Serial 0/0******************************************************************************** RTR_2#show run!!interface FastEthernet0/0ip address 192.168.77.34 255.255.255.252!interface FastEthernet0/1ip address 192.168.60.65 255.255.255.240!interface FastEthernet1/0ip address 192.168.60.81 255.255.255.240!!router eigrp 22network 192.168.77.0network 192.168.60.0no auto-summary!RTR_2#show ip route192.168.60.0/28 is variably subnetted, 2 subnetsC 192.168.60.80 is directly connected, FastEthernet1/0C 192.168.60.64 is directly connected, FastEthernet0/1192.168.77.0/30 is subnetted, 1 subnetsC 192.168.77.32 is directly connected, FastEthernet0/0**********************************************************RTR_B#show run!interface FastEthernet0/0ip address 192.168.60.129 255.255.255.240!interface FastEthernet0/1ip address 192.168.60.145 255.255.255.240!interface Serial0/1ip address 192.168.60.26 255.255.255.252!router eigrp 212network 192.168.60.0!RTR_B#show ip route192.168.60.0/24 is variably subnetted, 5 subnets, 2 masksC 192.168.60.24/30 is directly connected, Serial0/1C 192.168.60.128/28 is directly connected, FastEthernet0/0C 192.168.60.144/28 is directly connected, FastEthernet0/1D 192.168.60.96/28 [ 90/21026560 ] via 192.168.60.25, 00:00:57, Serial 0/1 D 192.168.60.112/28 [ 90/21026560 ] via 192.168.60.25, 00:00:57, Serial 0/1 192.168.36.0/30 is subnetted, 1 subnetsD 192.168.36.12 [ 90/21026560 ] via 192.168.60.25, 00:00:57, Serial 0/1D* 198.0.18.0 [ 90/21026560 ] via 192.168.60.25, 00:00:57, Serial 0/1**************************************************************************RTR_1#show run!!interface FastEthernet0/0ip address 192.168.77.33 255.255.255.252 !interface Serial1/0ip address 198.0.18.6 255.255.255.0!!interface Serial0/0ip address 192.168.36.13 255.255.255.252 clockrate 64000!interface Serial0/1ip address 192.168.60.25 255.255.255.252 clockrate 64000!!router eigrp 212network 192.168.36.0network 192.168.60.0network 192.168.85.0network 198.0.18.0no auto-summary!ip classlessip default-network 198.0.18.0ip route 0.0.0.0 0.0.0.0 198.0.18.5ip http serverRTR_1#show ip route192.168.36.0/30 is subnetted, 1 subnetsC 192.168.36.12 is directly connected, Serial 0/0192.168.60.0/24 is variably subnetted, 5 subnets, 2 masksC 192.168.60.24/30 is directly connected, Serial0/1D 192.168.60.128/28 [ 90/21026560 ] via 192.168.60.26, 00:00:57, Serial 0/1D 192.168.60.144/28 [ 90/21026560 ] via 192.168.60.26, 00:00:57, Serial 0/1D 192.168.60.96/28 [ 90/21026560 ] via 192.168.36.14, 00:00:57, Serial 0/0192.168.77.0/30 is subnetted, 1 subnetsC 192.168.77.32 is directly connected, FastEthernet0/0C 192.0.18.0/24 is directly connected, Serial 1/0*S 0.0.0.0 via 198.0.18.5271. Please study the diagram carefully, and then drag and drop the network user application to the appropriate description of its primary use(Not all options are used.)Answer:272. In order to enhance the security of TestInside enterprise network, TestInside network administrators use ACL(Access Control lists). What are two reasons that the TestInside network administrator would use access lists?Answer:The purposes for setting ACLs on a router are controlling vty access into a router and filtering traffic as it passes through a router.Access Control List(ACL) can be used to affect traffic transmitted from one port to another. It acquired its name due to having filtering capability when traffic flows in and out of interface and it also can be used for other purposes, such as:A: Place restrictions on accessing router Telnet (VTY) .B: Filter routing information.C: Distinguish precedence of WAN traffic by queuing technology .D: Trigger calls through the Dial-on-demand routing (DDR).E: Change administrative distance of routing273. LABYou work as a network technician at . Study the exhibit carefully. You are required to perform configurations to enable internet access. The TestInside ISP has given you six public IP addresses in the 198.18.32.65 198.18.32.70/29 range. has 62 clients that needs to have simultaneous internet access. These local hosts use private IP addresses in the 192.168.6.65 - 192.168.6.126/26 range.You need to configure Router TestInside1 using the TestInsideA console. You have already made basic router configuration.You have also configured the appropriate NAT interfaces; NAT inside and NAT outside respectively. Now you are required to finish the configuration of TestInside1.Answer:TestInside1: TestInside1#Config tTestInside1(Config)#interface fa0/0TestInside1(Config-if)#ip nat insideTestInside1(Config)#interface S0/0TestInside1(Config-if)#ip nat outsideTestInside1(Config-if)#exitTestInside1(Config)#access-list 1 permit 192.168.6.65 0.0.0.63TestInside1(Config)#access-list 1 deny anyTestInside1(Config)#ip nat pool nat_test 198.18.32.65 198.18.32.70 prefix-length 29TestInside1(Config)#ip nat inside source list 1 pool nat_test overloadThis question tests the knowledge of NAT. The IP addresses in this question are changeable.274. Drag and drop question. Drag the items to the proper locations.Answer:275. LAB:Please input command here:Answer:Router>enableRouter#config terminalRouter(config)#hostname TIS-RCTIS-RC(config)#enable secret TestInside 1TIS-RC(config)#line console 0TIS-RC(config-line)#password TestInside2TIS-RC(config-line)#exitTIS-RC(config)#line vty 0 4TIS-RC(config-line)#password TestInside3TIS-RC(config-line)#loginTIS-RC(config-line)#exitTIS-RC(config)#interface fa0/0TIS-RC(config-if)#ip address 209.165.202.158 255.255.255.224 TIS-RC(config-if)#no shutdownTIS-RC(config-if)#exitTIS-RC(config)#interface s0/0/0TIS-RC(config-if)#ip address 192.0.2.30 255.255.255.240TIS-RC(config-if)#no shutdownTIS-RC(config-if)#exitTIS-RC(config)#router ripTIS-RC(config-router)#version 2TIS-RC(config-router)#network 209.165.202.128 TIS-RC(config-router)#network 192.0.2.16TIS-RC(config-router)#endTIS-RC#copy run start276. DropAnswer:Physical layer: Bit,physical device, cable ,NICData link layer: MAC,NIC,FrameNetwork layer: Packet, IP, routingTransport Layer: segments, windowing,UDP,segment 277. Drag DropAnswer:NAT addresses can be divided into two categories: inside network and outside network which are defined based on the NAT functions. The device that has NAT functions connects the inside and the outside network like a bridge, the NIC connected to the inside network is called "inside" , the NIC connected to theoutside network is called "outside", that is to say, the inside addresses are used by the inside network devices, while the outside addresses are used by the outside network devices.Addresses can also be divided into local and global addresses. Local address refers to the address that can be seen and used by the inside network devices; while global address refers to the address that can be seen and used by the outside network devices.These four addresses are :Inside local address is the IP address used by the inside network devices, which is often a private address. Inside global address is a public address provided by ISP. It is often used when the inside network devices communicate with the outside network devices.Outside local address is the address used by the outside network device as it appears to the inside network device. It is not necessarily a public network address.Outside global address is the real address used by the outside network devices.IP packets sent from the inside network devices regard "inside local address" as the source address and "outside local address" as the destination address. When the packets reach the "inside" interface of the NAT equipment, the addresses will be translated into "inside global address" and "outside global address" , the packets will be out from the "outside" interface .In the same way, IP packets sent from the outside network devices regard "outside global address" as the source address and "inside global address" as the destination address. When the packets reach the "outside" interface of the NAT equipment, the addresses will be translated into "outside local address" and "inside local address", the packets will be out from the "inside" interface.278. Drag DropAnswer:Ip --- protocol Address --- 192.168.125.34 Mask --- 0.0.0.0 279. DropAnswer:280. DropThe Missouri branch office router is connected through its s0 interface to the Alabama Headquarters router s1 interface.The Alabama router has two LANs. Missouri user obtain internet access through the Headquarters router. The network interfaces in the topology are addressed as follows:Missouri: e0-192.168.35.33/28;Alabama: e0-192.168.35.49/28e1-192.168.35.65/28s1-192.168.35.34/28The accounting server has the address of 192.168.35.66/28.Match the access list conditions on the left with the goals on the right.(Not all options on the left are used.)Answer:281. Refer to the exhibit.TIS-PCA is sending packets to the FTP server.Consider the packets as they leave TIS-RA interface Fa0/0 forwards TIS-RB.Drag the correct frame and packet address to their place in the table.Answer:Source MAC : 0000.0c93.9999 Source IP : 172.16.21.7 Destination MAC : 0000.0c89.3333 Destination IP ; 172.16.34.250282. What kind of information can you deduce from an IOS image file name?Answer:Step 1 ---- Check URLStep 2 ---- Check IP addressStep 3 ---- Check NICStep 4 ---- Check cable283. Drag the description on the left to the routing protocol on the right.(Not all options are used.)Answer:EIGRP is a private CISCO protocol, combining the advantages of the Link State Routing Protocol and the Distance Vector Routing Protocol, the default administrative distance is 90. EIGRP adopts Diffusing Update Algorithm (DUAL) to achieve fast convergence , supports Variable Length Subnet Mask (VLSM) and uses multicast and unicast instead of broadcast to communicate between routers. OSPF(Open Shortest Path First) is an Interior Gateway Protocol, which can be used for route decision in a single autonomous system. Compared to RIP, OSPF is a Link State Routing Protocol. By default, OSPF calculates the cost based on the bandwidth configured on interface , the higher the bandwidth, the lower the cost.284. As a CCNA candidate, you are required to have a firm understanding of the OSI model. At which layers of the OSI model do Wide Area Networks operate in? Please drag the items to the proper locations.Answer:A WAN is a data communications network that covers a relatively broad geographic area and that often uses transmission facilities provided by common carriers, such as telephone companies. WAN technologies generally function at the lower two layers of the OSI reference model: the physical layer and the data link layer as shown below.Note: Occasionally WAN's would also be considered to operate at layer 3, but since this question asked for only 2 chopices layers 1 and 2 are better choices.285. Drop Please study the exhibit shown below carefully, and complete a basic switch configuration.Answer:enable: allows access to high-level testing commands, such as debug.configure terminal: allows access to configuration commands that affect the system as a whole hostname: sets the system name.Interface vlan 1: activates the interface configuration mode for VLAN 1No shutdown: enables the switch management interfaceIP address: sets the switch management IP addressIP default-gateway: allows the switch to be managed from remote networks286. As the TestInside network administrator, you are required to configure the network security policy, And the policy requires that only one host be permitted to attach dynamically to each switch interface. If thatpolicy is violated, the interface should shut down. Which two commands must the network administrator configure on the 2950 Catalyst switch SWTestInside1 to meet this policy? Please choose appropriate commands and drag the items to the proper locations.Answer:Basically speaking, the function of Port Security is to remember the MAC address of the NIC connected to the switch port and allows this MAC address to use this port.If other NICs attempt to cross this port to connect to the switch, Port Security function will disable this port. switchport port-security maximum {max # of MAC addresses allowed}: This parameter will allow each port to bind more MAC addresses, not only one.switchport port-security violation {shutdown | restrict | protect}: This command tells the switch that how to deal with the situation when the number of MAC addresses accessed exceeds the desired maximum number.This port is disabled by default.287. Drag DropAnswer:288. As a CCNA candidate, you need to use a telnet session often. What are two characteristics of Telnet? Please choose two appropriate statements and drag the items to the proper locations.Answer:Telnet, by default, does not encrypt any data sent over the connection (including passwords), and so it is often practical to eavesdrop on the communications and use the password later for malicious purposes; anybody who has access to a router, switch, hub or gateway located on the network between the two hostswhere Telnet is being used can intercept the packets passing by and obtain login and password information (and whatever else is typed) with any of several common utilities. If a remote device wants to access the destination device through Telnet, the destination device must be configured to support Telnet connections.289. Refer to the exhibit.TIS-PCA is sending packets to the FTP server.Consider the packets as they leave TIS-RA interface Fa0/0 forwards TIS-RB.Drag the correct frame and packet address to their place in the table.Answer:Source MAC : 0000.0c93.9999Source IP : 172.16.21.7Destination MAC : 0000.0c89.3333Destination IP ; 172.16.34.250More often than not , in the process of the source host communicating with the destination host, the source host will consider that the IP address of the destination host and its own IP address are in the same networksegment, so it will send broadcast ARP request. In this subject, in the process of TIS-PCA sending data packets to FTP Server, TIS-PCA will first send broadcast ARP request to FTP Server, TIS-PCA itself will also receive this broadcast ARP request and find that the IP address of the destination host is in another subnet, so it will send request using the MAC address of interface Fa0/0 of its own.290. Drag and drop question. Drag the items to the proper locations.Answer:1. The high level testing commands such as debug that allow access should be conducted under enable mode2. Access to configuration commands under configure terminal3. The command to set the system name is hostname4. Configure vlan, interface vlan 1 may be used to configure details in vlan5. Input no shutdown under interface configure mode to activate interface6. Use command ip address to configure IP address, and sets the switch management7. Use command ip default-gateway to configure default gateway291. As a CCNA candidate, you need to know EIGRP very well. Which tables of EIGRP route information are held in RAM and maintained through the use of hello and update packets? Please choose twoappropriate tables and drag the items to the proper locations.Answer:Only the neighbor table and the topology table of EIGRP route information are held in RAM and maintained through the use of hello and update packets.292. Refer to the exhibit. Complete this network diagram by dragging the correct device name ofdescription name or description to the correct location. Not all the names or descriptions will be used.Answer:293. You work as a network technician for TestInside and are responsible for this network. You are required to configure the office network, In particular the host TestInsideC with the IP address 192.168.125.34/27, needs to be configured so that it cannot access hosts outside its own subnet.According to this, you decide to use the following command:[Access list 100 deny protocol address mask any]You are required to fill in the [protocol], [address], and [mask] in this command using the choices below:Answer:。
