云南大学软件学院计算机网络原理期中试卷 王世普
云南大学《计算机网络信息安全》期中考试

云南大学《计算机网络信息安全》期中考试校级选修课云南大学2011-2012学年下学期《计算机网络信息安全与应用》考试试卷满分100分考试时间:开卷任课教师:贺思德学院软件学院专业网络工程学号11111111111111 姓名桐人题号1.1 1.2 1.3 2.1 2.2 3 总分得分一、在一台网络计算机上安装网络协议分析软件Wireshark,先清空IE浏览器的临时文件夹,捕获计算机访问互联网的以下数据。
将捕获数据文件保存,并分析内容。
二、发送一句短英文的电子邮件,捕获分析自己的电子邮件网络数据,回答以下问题:1、自己的网络计算机的MAC地址是98:4b:e1:c9:bb:b9本地网络出口网关的MAC地址是(参看教材20页例)7a-79-05-00-00-92、自己的网络计算机的IP地址是113.55.45.211自己注册的电子邮件服务器的IP地址是202.205.3.553、与邮件服务器建立TCP连接时本地主机的端口号是12783邮件服务器端的TCP端口号是804、在三次握手建立了TCP连接后,本机的HTTP进程用POST (178页表6.2)向邮件服务器登录邮箱时,从数据中是否可读出自己的用户名可以登录密码加密过无法读出5、当自己成功登录邮件服务器后,利用Wireshark的Analyze工具栏中的Follow TCP Stream工具,找出自己的主机发送给服务器的Cookies内容是u=23256500946、邮件服务器向本机返回的Cookie的内容是u=2325650094; Expires=Sat, 23-Jun-2012 17:00:17 GMT; Path=/7、从捕获数据中能否获取自己的电子邮件内容?简述电子邮件面临的安全问题,如何保护自己的用户名?如何保护自己的口令?如何保护邮件信息?如何防垃圾邮件?答:能够获取邮箱内容。
电子邮件所面临的安全问题有:邮件病毒,电子邮件炸弹,垃圾邮件,电子邮件信息窃取等。
云南大学 软件学院 计算机网络原理试卷

一、单项选择题(本大题共20小题,每小题1分,共20分)在每小题列出的四2.计算机网络中可以共享的资源包括()A、硬件、软件、数据、通信信道B、主机、外设、软件、通信信道C、硬件、程序、数据、通信信道D、主机、程序、数据、通信信道3.网络协议主要要素为()A、数据格式、编码、信号电平B、数据格式、控制信息、速度匹配C、语法、语义、同步D、编码、控制信息、同步4.采用专用线路通信时,可以省去的通信阶段是()A、建立通信线路B、建立数据传输链路C、传送通信控制信号和数据D、双方确认通信结束5.通信系统必须具备的三个基本要素是()A、终端、电缆、计算机B、信号发生器、通信线路、信号接收设备C、信源、通信媒体、信宿D、终端、通信设施、接收设备6.宽带传输通常使用的速率为()A0-10Mbit/sB1-2.5Mbit/sC5-10Mbit/s D、0-400Mbit/s7.计算机网络通信系统是()A、电信号传输系统B、文字通信系统C、信号通信系统D、数据通信系统8.网络接口卡的基本功能包括:数据转换、通信服务和()A、数据传输B、数据缓存C、数据服务D、数据共享9.完成通信线路的设置与拆除的通信设备是()A、线路控制器B、调制解调器C、通信控制器D、多路复用器10.在星型局域网结构中,连接文件服务器与工作站的设备是()A、调制解调器B、交换器C、路由器D、集线器11.在OSI七层结构模型中,处于数据链路层与运输层之间的是()A、物理层B、网络层C、会话层D、表示层12.完成路径选择功能是在OSI模型的()A、物理层B、数据链路层C、网络层D、运输层13.下列功能中,属于表示层提供的是()A、交互管理B透明传输C、死锁处理D、文本压缩14.在TCP/IP协议簇的层次中,解决计算机之间通信问题是在()A、网络接口层B、网际层C、传输层D、应用层15.对局域网来说,网络控制的核心是()A、工作站B网卡C、网络服务器D、网络互连设备16.在中继系统中,中继器处于()A、物理层B、数据链路层C、网络层D、高层17.各种网络在物理层互连时要求()A、数据传输率和链路协议都相同B、数据传输率相同,链路协议可不同C、数据传输率可不同,链路协议相同D、数据传输率和链路协议都可不同18.网络管理系统中,管理对象是指()A、网络系统中各种具体设备B、网络系统中各种具体软件C、网络系统中各类管理人员D、网络系统中具体可以操作的数据19.Intranet技术主要由一系列的组件和技术构成,Intranet的网络协议核心是()A、ISP/SPX B、P PP C、TCP/IP D、SLIP20.网络管理信息系统的分析设计以()A、功能模块设计为中心B、数据分析为中心C、系统拓扑结构设计为中心D、系统规模分析为中心计算机网络技术期末复习试卷一、填空题(0.5%×30)1.传送信号的一条通道叫____信道________。
2022年云南大学软件工程专业《计算机组成原理》科目期末试卷A(有答案)
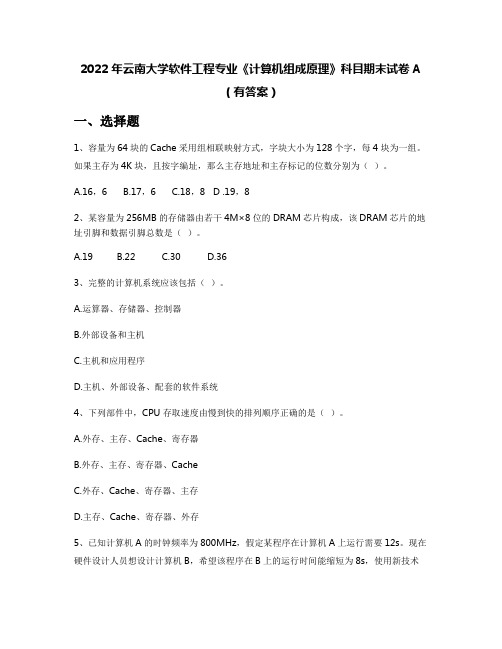
2022年云南大学软件工程专业《计算机组成原理》科目期末试卷A(有答案)一、选择题1、容量为64块的Cache采用组相联映射方式,字块大小为128个字,每4块为一组。
如果主存为4K块,且按字编址,那么主存地址和主存标记的位数分别为()。
A.16,6B.17,6C.18,8 D .19,82、某容量为256MB的存储器由若干4M×8位的DRAM芯片构成,该DRAM芯片的地址引脚和数据引脚总数是()。
A.19B.22C.30D.363、完整的计算机系统应该包括()。
A.运算器、存储器、控制器B.外部设备和主机C.主机和应用程序D.主机、外部设备、配套的软件系统4、下列部件中,CPU存取速度由慢到快的排列顺序正确的是()。
A.外存、主存、Cache、寄存器B.外存、主存、寄存器、CacheC.外存、Cache、寄存器、主存D.主存、Cache、寄存器、外存5、已知计算机A的时钟频率为800MHz,假定某程序在计算机A上运行需要12s。
现在硬件设计人员想设计计算机B,希望该程序在B上的运行时间能缩短为8s,使用新技术后可使B的时钟频率大幅度提高,但在B上运行该程序所需要的时钟周期数为在A上的1.5倍。
那么,机器B的时钟频率至少应为()能运到所希望的要求。
A.800MHzB.1.2 GHzC.1.5GHzD.1.8GHz6、一次总线事务中,主设备只需给出一个首地址,从设备就能从首地址开始的若干连续单元读出或写入多个数据。
这种总线事务方式称为()。
A.并行传输B.串行传输C.突发传输D.同步传输7、假设某存储器总线采用同步通信方式,时钟频率为50MHz,每个总线事务以突发方式传输8个字,以支持块长为8个字的Cache行读和Cache行写,每字4B.对于读操作,方式顺序是1个时钟周期接收地址,3个时钟周期等待存储器读数,8个时钟周期用于传输8个字。
请问若全部访问都为读操作,该存储器的数据传输速率为()。
云南大学--软件学院--计算机网络原理-期末试题复习总结

注意:这是04-05学期王老师出的试题。
1.Ethernet使用的MAC协议是(1)。
当发生冲突时,将进入二进制指数退避阶段,对于第3次冲突,等待重传的最长时间是512位时间的(2)倍。
(1)A.ALOHA B.CSMA/CD C.CSMA/CA D.CSMA/DD (2)A.1 B.3C.5 D.72.网络体系结构定义计算机网络的分层结构,TCP/IP模型和ISO/OSI参考模型是两个主要的网络模型,其中TCP/IP协议传送层之上的层是(3)层,而ISO/OSI 则是一个(4)层的模型。
(3)A.应用B.表述C.会话D.网络(4)A.4 B.5 C.6 D.73.传统的以太网传输介质是同轴电缆,其中使用粗同轴电缆的网络称为(5)网络,使用细同轴电缆的网络称为(6)网络。
10Base-T网络使用的传输介质是无屏蔽双绞线,简称为(7)。
(5)A.5BASE B.10BASE-10 C.10BASE-5D.10BASE-2 (6)A.5BASE B.10BASE-10 C.10BASE-5 D.10BASE-2(7)A.UPT B.UTP C.UPP D.UUP 4.有N个节点共享一条总传输速率为R的通信信道,若采用TDMA协议,则每个节点的平均传输速率是(8),而瞬时传输速率则为(9);如果采用FDMA 协议,则每个节点的平均传输为(10),而瞬时传输速率则为(11)。
(8)A.R B.R/N C.NR D.2R(9)A.R B.R/N C.NR D.2R(10)A.R B.R/N C.NR D.2R(11)A.R B.R/N C.NR D.2R5.可靠传输协议rdt3.0的发送和接收窗口都是1,对其进行改进后的GBN协议和SR协议都把发送窗口尺寸扩大为N(>1)。
但GBN协议的接收窗口为(12),而SR协议的接收窗口为(13)。
对SR协议,若使用k位的序号,则其发送窗口尺寸应(14)。
(12)A.1 B.N/4 C.N/2 D.N(13)A.1 B.N/4 C.N/2 D.N(14)A.不大于2k B.等于2k C.不大于2k-1D.等于2k-16.PPP协议可以用在(15)链路上,并使用(16)协议完成链路状态的管理,使用(17)协议完成网络层地址配置和压缩方式协商。
云南大学2011至2012学年下学期软件学院2010级《高级计算机网络原理》期中考试(闭卷)试卷(答案)
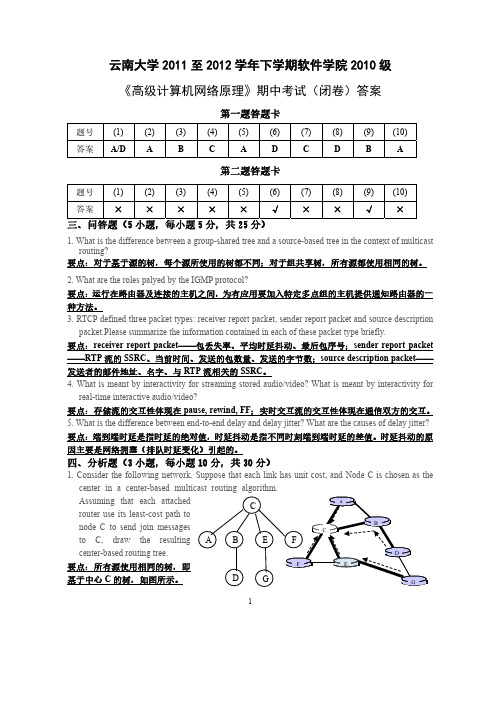
云南大学2011至2012学年下学期软件学院2010级《高级计算机网络原理》期中考试(闭卷)答案第一题答题卡题号(1) (2) (3) (4) (5) (6) (7) (8) (9) (10) 答案A/D A B C A D C D B A第二题答题卡题号(1) (2) (3) (4) (5) (6) (7) (8) (9) (10)答案×××××√××√×三、问答题(5小题,每小题5分,共25分)1. What is the difference between a group-shared tree and a source-based tree in the context of multicastrouting?要点:对于基于源的树,每个源所使用的树都不同;对于组共享树,所有源都使用相同的树。
2. What are the roles palyed by the IGMP protocol?要点:运行在路由器及连接的主机之间,为有应用要加入特定多点组的主机提供通知路由器的一种方法。
3. RTCP defined three packet types: receiver report packet, sender report packet and source descriptionpacket.Please summarize the information contained in each of these packet type briefly.要点:receiver report packet——包丢失率、平均时延抖动、最后包序号;sender report packet ——RTP流的SSRC、当前时间、发送的包数量、发送的字节数;source description packet——发送者的邮件地址、名字、与RTP流相关的SSRC。
云南大学软件学院计网参考题
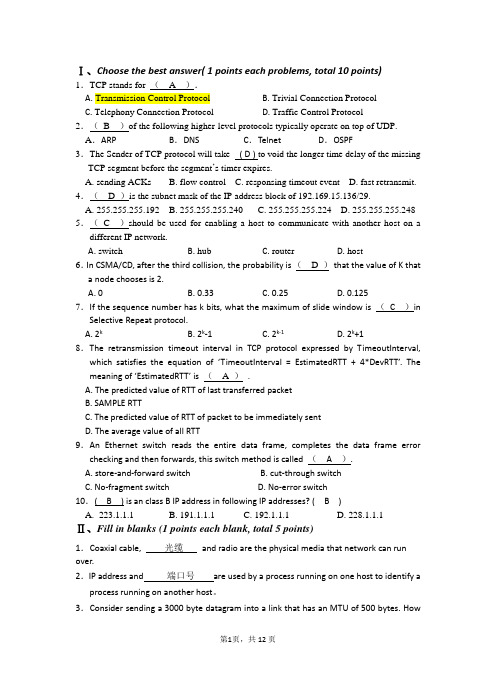
Ⅰ、Choose the best answer( 1 points each problems, total 10 points)1.A. B. Trivial Connection ProtocolC. Telephony Connection ProtocolD. Traffic Control Protocol2.(B )of the following higher-level protocols typically operate on top of UDP. A.ARP B.DNS C.Telnet D.OSPF3.The Sender of TCP protocol will take ( D ) to void the longer time delay of the missing TCP segment before the segment’s timer expires.A. sending ACKsB. flow controlC. responsing timeout eventD. fast retransmit. 4.( D )is the subnet mask of the IP address block of 192.169.15.136/29.A. 255.255.255.192B. 255.255.255.240C. 255.255.255.224D. 255.255.255.248 5.(C )should be used for enabling a host to communicate with another host on a different IP network.A. switchB. hubC. routerD. host6.In CSMA/CD, after the third collision, the probability is ( D )that the value of K thata node chooses is 2.A. 0B. 0.33C. 0.25D. 0.1257.If the sequence number has k bits, what the maximum of slide window is (C )in Selective Repeat protocol.A. 2kB. 2k-1C. 2k-1D. 2k+18.The retransmission timeout interval in TCP protocol expressed by TimeoutInterval, which satisfies the equation of ‘TimeoutInterval = EstimatedRTT + 4*DevRTT’. The meaning of ‘EstimatedRTT’ is ( A ).A. The predicted value of RTT of last transferred packetB. SAMPLE RTTC. The predicted value of RTT of packet to be immediately sentD. The average value of all RTT9.An Ethernet switch reads the entire data frame, completes the data frame error checking and then forwards, this switch method is called ( A ).A. store-and-forward switchB. cut-through switchC. No-fragment switchD. No-error switch10.( B ) is an class B IP address in following IP addresses? ( B )A. 223.1.1.1B. 191.1.1.1C. 192.1.1.1D. 228.1.1.1Ⅱ、Fill in blanks (1 points each blank, total 5 points)1.Coaxial cable, 光缆and radio are the physical media that network can run over.2.IP address and 端口号are used by a process running on one host to identify a process running on another host。
(4)--软件工程2005-2006学年期中考试试题及答案
云南大学2005至2006学年上学期软件学院《软件工程》期中考试(闭卷)试卷满分:100分 考试时间:120分钟 任课教师:李彤专业:____学号:____姓名:_____1. Explain the following terms (15 Points, 3 Points for Each):(1) User interface(2) Software evolution(3) Software requirements(4) System model(5) Verification2. Answer the following questions briefly (20 Points, 5 Points for Each):(1) Advantages of incremental development?(2) What is the component-based development?(3) What is the multiple inheritance?(4) What is the architectural design?3. Multiple Choices (10 Points, 1 Point for Each):(1)A generalized description of a collection of similar objects is aa. classb. instancec. subclassd. super class(2)Which of the following should be considered as candidateobjects in a problem space?a. eventsb. peoplec. datad. all of the above(3)Which of the following should not be included in the CASEtoolset architecture?a. design editorb. code generatorc. wage systemd. design translator(4)Where was the ETHICOMP Working Conference 2007 held in2-3 April 2007?a. Peking Universityb. Yunnan Universityc. Beijing University of Aeronautics and Astronauticsd. Harbin Institute of Technology(5)What types of requirements are elicited during softwarerequirements analysis?a. functional and non-functionalb. algorithmic and data structurec. architectural and structurald. usability and reliability(6)The data flow diagrama. depicts relationships between data objectsb. depicts functions that transform the data flowc. specified major logical decisions as they occurd. indicates system reactions to external events(7)Which of the following is not an area of concern in the designmodel?a. architectureb. datac. interfacesd. project scope(8)V&V meansa. verification and validationb. visa and visualc. version and validationd. vista and visit(9)The types of requirements includea. over all requirements and specific requirementsb. Chinese requirements and foreign requirementsc. student requirements and teacher requirementsd. user requirements and system requirements(10)Extreme programming is an approacha. to sleeping not more than 2 hours a dayb. to development based on the development and delivery ofvery small increments of functionalityc. to doing everything extremelyd. to developing software with managers4. True or False (10 Points, 1 Point for Each):(1)In evolutionary development, specification, development andvalidation are sequential.a. Trueb. False(2)Distributed system model shows how data and processing isdistributed across a range of components.a. Trueb. False(3)Spiral development process is represented as a spiral rather thanas a sequence of activities with backtracking.a. Trueb. False(4)Architectural design is not a creative process so the processdiffers depending on the type of system being developed.a. Trueb. False(5)Functional requirements define system properties andconstraints e.g.reliability,response time and storage requirements. Constraints are I/O device capability, system representations, etc.a. Trueb. False(6)Adding more people to a project that is already behind scheduleis a good way to catch up.a. Trueb. False(7)For increasing the performance, the designers should use finerather than large-grain components.a. Trueb. False(8)Architectural designs should decide how the architectures willbe evaluated?a. Trueb. False(9)Milestones are the end-point of a process activity.a. Trueb. False(10)Exhaustive testing can show a program is free from defects.However, exhaustive testing is impossible.a. Trueb. False5. Read the following charts carefully, and then explain what they mean. (13 Points)6. Read the following chart carefully, and then explain what it means. (12 Points)(a)(b)(c)7. (20 Points)Analyse and design a simple management information system of a library. The system allows the users to manage items (including books, magazines, films and programs). Draw out the following models briefly:(1) user case (5 Points),(2) class hierarchy (8 Points) and(3) sequence diagram (7 Points).云南大学2009至2010学年上学期软件学院软件工程/网络工程/信息安全专业2007级本科《软件工程》期末考试(闭卷)试卷B 卷参考答案满分:100分 考试时间:120分钟 任课教师:李彤1. Explain the following terms (15 Points, 3 Points for Each):(1) User interfaceThe interface between users and the software systems.(2) Software evolutionThe software change in the software life cycle.(3) Software requirementsThe requirements are the descriptions of the software services and constraints that are generated during the requirements engineering process. It may range from a high-level abstract statement of a service or of a system constraint to a detailed mathematical functional specification.(4) System modelA system model is a specification which helps the analyst to understand the functionality of the system and is used to communicate with customers.(5) VerificationAre we building the product right?i.e.the software should conform to its specification.2. Answer the following questions briefly (20 Points, 5 Points for Each):(1) Advantages of incremental development?1. Accelerated delivery of customer services. Each increment delivers the highest priority functionality to the customer.2. User engagement with the system. Users have to be involved in the development which means the system is more likely to meet their requirements and the users are more committed to the system. (2) What is the component-based development?Component-based software engineering (CBSE) is an approach to software development that relies on software reuse. It emerged from the failure of object-oriented development to support effective reuse. Single object classes are too detailed and specific. Components are more abstract than object classes and can be considered to be stand-alone service providers.(3) What is the multiple inheritance?Rather than inheriting the attributes and services from a single parent class, a system which supports multiple inheritance allows object classes to inherit from several super-classes.(4) What is the architectural design?The design process for identifying the sub-systems making up a system and the framework for sub-system control and communication is architectural design.3. Multiple Choices (10 Points, 1 Point for Each):(1) a, (2) d, (3) c, (4) b, (5) a, (6) b, (7) d, (8) a, (9) d, (10) b.4. True or False (10 Points, 1 Point for Each):(1) b, (2) a, (3) a, (4) b, (5) b, (6) b, (7) b, (8) a, (9) a, (10) a.5. (13 Points)It describes the software reengineering process activities:•Source code translation–Convert code to a new language.•Reverse engineering–Analyse the program to understand it;•Program structure improvement–Restructure automatically for understandability;•Program modularisation–Reorganise the program structure;•Data reengineering–Clean-up and restructure system data.6. (12 Points)It describes the Types of composition.(1) Sequential composition where the composed components are executed ininterfaces of each component. composition where onecomponent calls on another.This provides interfaceof one component is composed with the required interface of another. (3) Additive composition where the interfaces of two components are put together to create a new component.7. (20 Points)(1) User case (5 Points)Ar ticle p rintingArticle s ea rchUs er a d m inis tra tio nLib raryUs erLib raryS taff(2) Class hierarchy (8 Points)(3) Sequence diagram (7 Points)。
2008年云南大学软件学院计算机网络期中考试试题
2008年云南大学软件学院计算机网络期中考试试题姓名:学号:成绩:任课教师:刘春花一、单项选择题(每题2分,共50分)1.一座大楼内的一个计算机网络系统,属于A、PANB、LANC、MAND、WAN2.在下列传输介质中,哪种介质的典型传输率最高?A、双绞线B、同轴电缆C、光纤D、无线介质3.完成路径选择功能是在OSI模型的A、物理层B、数据链路层C、网络层D、运输层4.域名与下面哪个一一对应A、物理地址B、IP地址C、网络D、以上均错5.在中继系统中,中继器处于A、物理层B、数据链路层C、网络层D、高层6、下列有关计算机网络叙述错误的是______。
A:利用Internet网可以使用远程的超级计算中心的计算机资源B:计算机网络是在通信协议控制下实现的计算机互联C:建立计算机网络的最主要目的是实现资源共享D:以接入的计算机多少可以将网络划分为广域网、城域网和局域网7、如果某局域网的拓扑结构是______,则局域网中任何一个节点出现故障都会会影响整个网络的工作。
A:总线型结构 B:树型结构 C:环型结构 D:星型结构8、TCP/IP协议是Internet中计算机之间通信所必须共同遵循的一种______。
A:信息资源 B:通信规定 C:软件 D:硬件9、为了以拨号的方式接入因特网,必须使用的设备是______。
A:Modem B:网卡 C:电话机 D:声卡10、下面______命令用于测试网络是否连通。
A:telnet B:ipconfig C:ping D:tracert11、在Internet中,用于文件传输的协议是______。
A:HTTP B:SMTP C:FTP D:POP12、系统可靠性最高的网络拓扑结构是______。
A:总线型 B:网状型 C:星型 D:树型13、分布范围小,投资少,配置简单是______的特点。
A:局域网 B:城域网 C:广域网 D:互联网14、下列选项中,属于计算机网络作用的是______。
云南大学--软件学院--机网习题大全
选择14、计算机网络拓扑是通过网中结点与通信线路之间的几何关系表示网络中各实体间的____B_____。
A、联机关系B、结构关系C、主次关系D、层次关系15、双绞线由两根相互绝缘的、绞合成均匀的螺纹状的导线组成,下列关于双绞线的叙述,不正确的是_A____。
A、它的传输速率达10Mbit/s~100Mbit/s,甚至更高,传输距离可达几十公里甚至更远B、它既可以传输模拟信号,也可以传输数字信号C、与同轴电缆相比,双绞线易受外部电磁波的干扰,线路本身也产生噪声,误码率较高D、通常只用作局域网通信介质16、ATM网络采用固定长度的信元传送数据,信元长度为_B__A、1024B B、53B C、128B D、64B17、127.0.0.1属于哪一类特殊地址(B )。
A、广播地址B、回环地址C、本地链路地址D、网络地址18、HTTP的会话有四个过程,请选出不是的一个。
(D )A、建立连接B、发出请求信息C、发出响应信息D、传输数据19、在ISO/OSI参考模型中,网络层的主要功能是_BA、提供可靠的端—端服务,透明地传送报文B、路由选择、拥塞控制与网络互连C、在通信实体之间传送以帧为单位的数据D、数据格式变换、数据加密与解密、数据压缩与恢复20、下列哪个任务不是网络操作系统的基本任务?_A___A、明确本地资源与网络资源之间的差异B、为用户提供基本的网络服务功能C、管理网络系统的共享资源D、提供网络系统的安全服务21、以下选项不属于以太网的“543”原则是指?__D__A、5个网段B、4个中继器C、3个网段可挂接设备D、5个网段可挂接22、既可应用于局域网又可应用于广域网的以太网技术是DA、以太网B、快速以太网C、千兆以太网D、万兆以太网23、交换机端口可以分为半双工与全双工两类。
对于100Mbps的全双工端口,端口带宽为_B__。
A、100MpbsB、200MbpsC、400MpbsD、800Mpbs24、要把学校里行政楼和实验楼的局域网互连,可以通过(A )实现A交换机BMODEM C中继器D网卡25、以下哪一类IP地址标识的主机数量最多?(D )A、D类B、C类C、B类D、A类26、子网掩码中“1”代表(B )。
云南大学 软件学院 计网实验8
云南大学软件学院实验报告课程:计算机网络原理实验任课教师:姓名:学号:专业:成绩:实验八、Link States Algorithm的实现1.实验目的:通过编程模拟实现LSA.2.实验环境:软件开发平台,可以使用任何编程语言。
3.实验要求(1)求网络中任何两个结点之间的最短路径(网络中至少有4个节点)。
(2)得到任何一个节点上的转发表。
4.实验内容、拓扑结构通过链路状态算法计算A点到其它各点的cost,最终输出A的路由表。
# include<stdio.h># include<stdlib.h># define maxlen 10# define large 999 //(该处设置路径最大值,表示不存在该路线)typedef struct{int vexnum;char vexs[maxlen];int arcs[maxlen][maxlen];}graph;void init_graph(graph *g)//初始化图{int i = 0,j = 0;g -> vexnum = 5; //根据题目此处将图的节点数初始化为5个for(i = 0; i < 5; i++) //经过两层循环将条路径初始化为无穷大for(j = 0; j < 5; j++)g -> arcs[i][j] = 999;g -> arcs[0][1] = 7; g -> arcs[1][0] = 7; //将相邻两个节点的路径初始化为其权值g -> arcs[0][4] = 1; g -> arcs[4][0] = 1;g -> arcs[1][2] = 1; g -> arcs[2][1] = 1;g -> arcs[2][3] = 2; g -> arcs[3][2] = 2;g -> arcs[1][4] = 8; g -> arcs[4][1] = 8;g -> arcs[3][4] = 2; g -> arcs[4][3] = 2;g -> vexs[0] = 'A'; //将节点值初始化g -> vexs[1] = 'B';g -> vexs[2] = 'C';g -> vexs[3] = 'D';g -> vexs[4] = 'E';}void shortpath_dijkstra(graph g)//寻找最短路径{int cost[maxlen][maxlen]; //cost[i][j]: 节点i到节点j的成本int dist[maxlen]; //dist[i]: 源节点到i节点的距离或者是成本int path[maxlen]; //已经经过了的节点int s[maxlen]; //如果 s[i] = 1,那么i节点已经纳入最短路径集合int i,j,v0,min,u;char e;printf("Input the source point(AorBorCorDorE):");//用户输入源节点scanf("%c",&e);switch(e){case'A':v0=0;break;case'B':v0=1;break;case'C':v0=2;break;case'D':v0=3;break;case'E':v0=4;break;}for(i = 0; i < g.vexnum; i++){for(j = 0; j < g.vexnum; j++)cost[i][j] = g.arcs[i][j];}for(i = 0; i < g.vexnum; i++){dist[i] = cost[v0][i]; //初始化源节点到各个节点的成本,如果与源节点相邻则成本为权值,否则为无穷大if(dist[i] < large && dist[i] > 0)path[i] = v0;s[i] = 0;}s[v0] = 1;for(i = 0; i < g.vexnum; i++){min = large;u = v0;for(j = 0; j < g.vexnum; j++)if(s[j] == 0 && dist[j] < min){min = dist[j];u = j;}s[u] = 1;for(j = 0; j < g.vexnum; j++)if(s[j] == 0 && dist[u] + cost[u][j] < dist[j]){dist[j] = dist[u] + cost[u][j];path[j] = u;}}printf("Output%c\n\n",e);for(i = 0; i < g.vexnum; i++)if(s[i] == 1){u = i;while(u != v0){printf(" %c <- ",g.vexs[u]);u = path[u];}printf(" %c ",g.vexs[u]);printf(" :%d \n",dist[i]);}else printf(" %c <- %c: no path \n",g.vexs[i],g.vexs[v0]);}int main(){graph g;init_graph(&g);shortpath_dijkstra(g);system("pause");return 0;}从A点开始,寻找到其余各点的最短路径截图如下:4.实验分析,回答下列问题(1)给出LSA算法的主要思想。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
云南大学2015至2016学年上学期软件学院2014级《计算机网络原理》期中考试试卷(闭卷)答案满分:100分考试时间:100分钟任课教师:王世普第一题答题卡:第二题答题卡:1.(1)is the protocol suite for the current Internet..(1)A. NCP B. TCP/IP C.UNIX D.ACM2.A GIF image is sent as email ,What is the content-type (2) .(2)A.multipart/mixed B.multipart/imageC.image/JPEG D.image/gif3.A user want to send some forms(表单)to Web server using HTTP protocol, the request line method is (3).(3)A.GET B.PA TCH C.MOVE D.POST4.If a TCP segment carries data along with an acknowledgment, this technology is called (4)acknowledgment.(4)A. backpacking B. piggybacking C. piggying D. mother’s help5.TCP is a (5)transport layer protocol that ensure data to be exchanged reliably by(6). So it requires set up connection before data exchanged by ( 7 )-way handshaking.(5)A.connection B.connectionless C.join D.disconnection(6)A.datagrams B.acknowledgements C.data D.segment(7)A.one B.two C.three D.four6.A user requests a Web page that consists of a basic HTML file and 5 JPEG image files. d trans denoting the time to transfer a file. The total time is (8) to request the Web page inNonpersistent connections mode?(8)A. 6(2RTT+ d trans) B. 2RTT+6 d trans C. RTT+6 d trans D.6(RTT+ d trans)7.Host A sends a TCP segment (Seq = 1, ACK = 111) to host B and Host B replies with a TCP segment (Seq = 111, ACK = 81). The payload length of the TCP segment from host A to hostB is ( 9 ) .(9)A.80 bytes. B.81 bytes. C.82 bytes. D.unknown8.As a data packet moves from the lower to the upper layers, header are (10).(10)A. modified B. added C. subtracted D. rearranged二、判断正误(每个问题1分,共5分。
正确的打“√”、错误的打“×”,请将判断结果填入第二题答题卡)1. The DNS defines a distributed, hierarchical database that provides only hostname to IP addressmappings.( × )2. In SR protocol, sender only resends pkts for which ACK not received. ( √ ) 3.If sequence number is k bit, then the send window maximum size of GBN protocol is equal to 2k-1. ( √ ) 4.The UDP header checksum is recomputed at every routers. ( × ) 5.Suppose that the last SampleRTT in a TCP connection is equal to 1 sec. Then Timeout for the connection will necessarily be set to a value >= 1 sec. ( × )三、回答下列问题(每个问题5分,共30分)1.For a communication session between two hosts, which host is the client and which is the server?要点:通信的发起者(请求者)是客户,通信的接受者(服务者)是服务器。
2.What is the difference between persistent HTTP with pipelining and persistent HTTP without pipelining?要点:前者在一个TCP连接期间可以传送多个WEB页面;后者在一个TCP 连接期间只能传送一个WEB页面。
3.What are the two types of services that the Internet provides to its applications? What are important characteristics of each of these services?要点:面向连接的服务(连接管理、正确可靠、按序交互、流控制、拥塞控制);无连接服务(不需建立连接、不可靠、每个报文独立传送,无流控制和拥塞控制)4.Why is it said "out of band" (带外的) that FTP sends control information?要点:TCP 数据连接是主连接,不能提供FTP 命令的传输;TCP 控制连接仅仅是传输FTP 命令和执行状态,因而是数据通道之外的通道,故属于“带外”信道。
5.Please list the main transmission mediums used in the computer network.要点:铜线、光纤、(地面)无线、卫星6.What are the differences Congestion Control and flow control.要点:范围不同(全网;通信双方)、目的不同(防止接收端缓冲区溢出;防止网络拥塞)四、计算题(共25分)1. Suppose host A communicates with host B through TCP, sometime host A sends 120 bytes data to host B, then host B responds with 100bytes data. Analyze the necessary ACK numbers and the Sequence number in the segments sent between host A and host B . Please give the analysis procedure (8 分)要点:ACK 是期望接收的段的序号;当B 收到一个数据为120字节、序号为45的段,就意味着期望接收的下一个段的序号应该是45+120=165;当S 收到来自B 的一个数据为100字节、序号为108的段后,则意味着期望接收的段的序号是108+100=208.2. UDP and TCP use 1's complement sum for their checksums. Suppose you have the following three 16-bit words: 1100100110110101, 1010011101010101, 0110010111011101. What is the 1's complement sum of these words? (7分)结果:Sum 1101011011101000 Checksum0010100100010111计算过程:1 1 0 0 1 0 0 1 1 0 1 1 0 1 0 1 + 1 0 1 0 0 1 1 1 0 1 0 1 0 1 0 1 1 0 1 1 1 0 0 0 1 0 0 0 0 1 0 1 0 1 0 1 1 1 0 0 0 1 0 0 0 0 1 0 1 1 + 0 1 1 0 0 1 0 1 1 1 0 1 1 1 0 1 0 1 1 0 1 0 1 1 0 1 1 1 0 1 0 0 0 + 0 sum 1 1 0 1 0 1 1 0 1 1 1 0 1 0 0 0 checksum 0 0 1 0 1 0 0 1 0 0 0 10 1 1 13.Consider two hosts, Host A and B, connected by a single link of rate R bps. Suppose that the two hosts are separated by m meters, and suppose the propagation speed along the link is s meters/second, and the size of packet is L bits. (10分)(1)Express the propagation delay, d prop in terms of m and s.d prop=m/s(2)Determine the transmission delay d trans in terms L and R.d trans =L/R(3)If R=1000 Mbps, m=270km, s=3 108m/s and L=1500 Bytes, please compute:d prop=(270×103m)/(3×108m/s)=9×104/108s=9×10-4s=0.9ms=900μsd trans=(1500×8)/(1000×106)s=12000/109s=12μs=0.012ms=1.2×10-5s五、综合题(共30分)1.Match the following tasks to one of the TCP/IP layers: (7分)(1)Transmission of Data Segment ( 传送层)(2)ASCII changed to EBCDIC ( 应用层)(3)Transmission of data frame ( 链路层)(4)Provides log-in and logout procedures ( 应用层)(5)Selects a destination network ( 网络层)(6)Provides services for the network applications ( 应用层)(7)Provides E-mail and file transfer services ( 应用层)3. Please answer the following questions.(1) Consider the following HTTP GET message. Answer the following questions, indicatingwhere in the message below you find the answer. ( 4分)GET /info/2012-10-18/0-1-411.html http/1.1Host: User-agent: Mozilla/4.0Accept-language: enKeep-Alive:300Connection:keep-alive<cr><lf>Questions:a.What is the URL of the document requested by the browser?b.What version of HTTP is the browser running?c.Does the browser request a non-persistent or a persistent connection?d.What is domain name of the server?要点:a. /info/2012-10-18/0-1-411.html (绝对URL)b. http 1.1c. persistent connectiond. or (2)The text below shows the reply sent from the server in response the to the HTTP GET messagein the question above(1). Answer the following questions, indicating where in the message below you find the answer. (4 points)HTTP/1.1 200 OKContent-Length: 19572Content-Type: text/htmlLast-Modified: Sun, 30 Sep 2012 07:23:15 GMTAccept-Ranges: bytesServer: Microsoft-IIS/6.0X-Powered-By: Date: Thu, 25 Oct 2012 21:26:48 GMTConnection: Keep-Alive<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN"/TR/xhtml1/DTD/xhtml1-transitional.dtd"><html xmlns="/1999/xhtml"><head><Much more document text following here(not shown)>……Questions:a.Was the server able to successfully find the document or not?b.What time was the document reply provided?c.When was the document last modified?d.How many bytes are there in the document being returned?要点:a. yesb. Thu, 25 Oct 2012 21:26:48 GMTc. Sun, 30 Sep 2012 07:23:15 GMTd. 19572 bytes3.The below figure is the Selective-Repeat protocol’s sender and receiver views of slide windows and the algorithm of sender of SR prot ocol. (15分)(1) Please analyse what does the SR protocol differ from the GBN protocol.(2) Please analyse what actions does the sender take when(a) timeout event occurring;(b) the sender received ACK packet from the receiver?(3) Please give the FSM of SR sender.Fig 1 views of slide windowsFig 2 the algorithm of sender of SR protocol要点:(1)窗口尺寸不同;定时方式不同(单独、最小);超时重传不同(单独、回退重传);接收缓冲不同;确认方式不同(单独、累计)(2)(a)重传超时的包;(b)标记对应的包为已确认的包;如果是窗口下沿的包的确认,则推进窗口到未被确认的序号最低的包。
