检索证明范例
论文收录和引用检索证明服务报告委托单【模板】
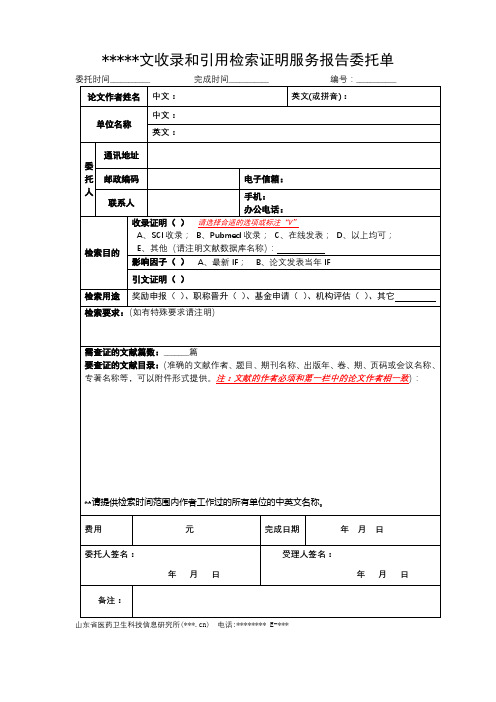
委托时间___________完成时间___________编号:___________
论文作者姓名
中文:
英文(或拼音):
单位名称
中文:
英文:
委托人
通讯地址
邮政编码
电子信箱:
联系人
手机:
办公电话:
检索目的
收录证明( )请选择合适的选项或标注“V”
A、SCI收录; B、Pubmed收录; C、在线发表; D、以上均可;
E、其他(请注明文献数据库名称):
影响因子( )A、最新IF;B、论文发表当年IF
引文证明( )
检索用途
奖励申报( )、职称晋升( )、基金申请( )、机构评估( )、其它
检索要求:(如有特殊要求请注明)
需查证的文献篇数:_______篇
要查证的文献目录:(准确的文献作者、题目、期刊名称、出版年、卷、期、页码或会议名称、专著名称等,可以附件形式提供。注:文献的作者必须和第一栏中的论文作者相一致):
**请提供检索时间范围内作者工作过的所有单位的中英文名称。
费用
元
完成日期
年 月 日
委托人签名:
年 月 日
受理人签名:
年 月 日
备注:
山东省医药卫生科技信息研究所(***.cn)电话:********E-***
检索报告范例_供参考

撰写检索报告的步骤 检索课题名称:
检索词:
检索范围(指检索哪些类型的数据库):
检索年限:
检索式:
检索结果:
筛选出所需文献:
导出选出文献的所需格式:
下载或浏览原文:
检索报告撰写
(范例)
一检索课题名称:本世纪以来海南生态旅游研究
二、检索词:海南、生态、旅游
检索时间条件:2000年1月1日至2012年12月7日三检索工具
1 CNKI平台:期刊库、硕博士学位论文库、会议论文库,成果库;
2万方平台:期刊库、学位论文、会议论文、成果数据库;
3 维普平台:期刊库
四检索式及检索过程(需要截图)
1 CNKI数据库中的检索式及检索过程截图:
检索式:TI=海南*生态and SU=旅游
检索过程截图:
2 万方数据库的检索式及检索过程截图:
检索式:题名=海南and题名或关键词=生态* 旅游检索过程截图:
2 维普数据库的检索式及检索过程:
检索式:T=海南and M=生态* 旅游
检索过程截图:
五检索结果(截出有检索结果篇数的部分)
CNKI检索结果截图:
万方检索结果截图:
维普检索结果截图:
六、筛选出所需文献(任选其中一个数据库筛选,截图)
七、导出查新格式(任选一个数据库导出,截图)
八、浏览其中一篇原文(任选一篇打开截图)。
华电论文检索证明报告模板

论文收录检索证明报告华北电力大学图书馆论文作者: Zhuxiao,Wang; Wang,Zhuxiao论文发表年限: 2012-2015检索数据库: Ei Compendex检索结果 :8篇收录Title:1. An Extension of Distributed Dynamic Description Logics for the Representation of Heterogeneous Mappings2. An architecture description language based on dynamic description logics for self-healing systems3. An architecture description language based on dynamic description logics4. An Architecture Dynamic Modeling Language for Self-Healing Systems5. A Tableau-Based Reasoning Algorithm for Distributed Dynamic Description Logics6.A formal model for attack mutation using dynamic description logics7. Linear cryptanalysis and security tradeoff of block ciphering systems with channel errors8. Research on sentiment analysis in sentence and text levels with priors特此证明!(盖章)检索报告人:年月日附件:收录情况:1. Accession number: 20132016337096Title: An extension of distributed dynamic description logics for the representation of heterogeneous mappingsAuthors: Wang, Zhuxiao1 ; Guo, Jing2 ; Chen, Fei3 ; Wu, Kehe3 ; Wang, Peng4Author affiliation: 1 School of Control and Computer Engineering, State Key Laboratory of Alternate Electrical Power System with Renewable Energy Sources, North China Electric Power University, 102206 Beijing, China2 National Computer Network Emergency Response Technical Team, Coordination Center of China, 100029 Beijing, China3 School of Control and Computer Engineering, North China Electric Power University, 102206 Beijing, China4 Institute of Information Engineering, Chinese Academy of Sciences, 100195 Beijing, China Corresponding author: Wang,Z.(****************.cn)Source title: Journal of SoftwareAbbreviated source title: J. Softw.Volume: 8Issue: 1Issue date: 2013Publication year: 2013Pages: 243-250Language: EnglishISSN: 1796217XDocument type: Journal article (JA)Publisher: Academy Publisher, P.O.Box 40,, OULU, 90571, FinlandAbstract: As a family of dynamic description logics, DDL(X) is constructed by embracing actions into the description logic X, where X represents well-studied description logics ranging from the ALC to the SHOIQ. To efficiently support automated interoperability between ontology-based information systems in distributed environments, we have to design an expressive mapping language to semantically understand resources from remote and heterogeneous systems. Distributed Dynamic Description Logics D3L(X) is a natural generalization of the DDL(X) framework, which is designed to model the distributed dynamically-changing knowledge repositories interconnected by semantic mappings and to accomplish reasoning in distributed, heterogeneous environments. In this paper, we propose an extension of Distributed Dynamic Description Logics D3L(X) and investigate the reasoning mechanisms in D3L(X). © 2013 ACADEMY PUBLISHER.Number of references: 16Main heading: Data descriptionControlled terms: Formal languages - Interoperability - Mapping - Semantics Uncontrolled terms: Distributed Dynamic Description Logics - Distributed reasonings - Dynamic description logic - Semantic mapping - Tableau algorithmClassification code: 716 Telecommunication; Radar, Radio and Television - 717 Optical Communication - 718 Telephone Systems and Related Technologies; Line Communications -723 Computer Software, Data Handling and Applications - 902.1 Engineering Graphics - 903.2 Information DisseminationDOI: 10.4304/jsw.8.1.243-250Database: CompendexCompilation and indexing terms, © 2013 Elsevier Inc.2. Accession number: 20124415623183Title: An architecture description language based on dynamic description logics for self-healing systemsAuthors: Wang, Zhuxiao1 ; Peng, Hui2 ; Guo, Jing3 ; Wu, Kehe4 ; Cui, Wenchao4 ; Wang, Xiaofeng5Author affiliation: 1 School of Control and Computer Engineering, State Key Laboratory of Alternate Electrical Power System with Renewable Energy Sources, North China Electric Power University, Beijing 102206, China2 Education Technology Center, Beijing International Studies University, Beijing 100024, China3 National Computer Network Emergency Response Technical Team/Coordination Center of China, Beijing 100029, China4 School of Control and Computer Engineering, Institute of Electric Information Security Engineering Research Center of Power Information, North China Electric Power University, Beijing 102206, China5 Institute of Computing Technology, Chinese Academy of Sciences, Beijing 100190, China Corresponding author: Wang,Z.(****************.cn)Source title: International Journal of Advancements in Computing Technology Abbreviated source title: Intl. J. Adv. Comput. Technolog.Volume: 4Issue: 18Issue date: October 2012Publication year: 2012Pages: 89-96Language: EnglishISSN: 20058039E-ISSN: 22339337Document type: Journal article (JA)Publisher: Advanced Institute of Convergence Information Technology, Myoungbo Bldg 3F,, Bumin-dong 1-ga, Seo-gu, Busan, 602-816, Korea, Republic ofAbstract: As biological systems exhibit adaptation, healing and robustness in the face of changing environmental behavior, this paradigm has actuated research dealing with the concept of self-healing systems, which attempt to heal themselves in the sense of recovering from malicious attacks and rectifying of system faults. The goal of self-healing systems is to provide survivable systems that require high dependability, robustness, adaptability, and availability. Such systems maintain one or more models, whether external or internal, at run time as a basis for identifying problems and resolving them. This article describes an architectural description language, called ADML, which is being developed as a new formal language and/or conceptual model forrepresenting evolving software architectures. The ADML embraces dynamic change as a fundamental consideration, supports a broad class of adaptive changes at the architectural level, and offers a uniform way to represent and reason about both static and dynamic aspects of self-healing systems. Because the ADML is based on the Dynamic Description Logic DDL(SHON (D)), which can represent both dynamic semantics and static semantics under a unified logical framework, architectural ontology entailment for the ADML languages can be reduced to knowledge base satisfiability in DDL(SHON (D)), and dynamic description logic algorithms and implementations can be used to provide reasoning services for ADML. In this article, we present the syntax of ADML, explain its underlying semantics using the Dynamic Description Logic DDL(SHON (D)), and exemplify our approach by applying it to the domain of load balancing a wireless remote-access system; the preliminary results certify the potential of the approach. Number of references: 14Main heading: Data descriptionControlled terms: Formal languages - Knowledge based systems - Knowledge representation - Semantics - Software architectureUncontrolled terms: Architecture description languages - Dynamic adaptations - Dynamic description logic - Knowledge representation and reasoning - Self-healing systemsClassification code: 723 Computer Software, Data Handling and Applications - 903.2 Information DisseminationDOI: 10.4156/ijact.vol4.issue 18.11Database: CompendexCompilation and indexing terms, © 2013 Elsevier Inc.3. Accession number: 20125015790730Title: An architecture description language based on dynamic description logicsAuthors: Wang, Zhuxiao1 ; Peng, Hui2 ; Guo, Jing3 ; Zhang, Ying1 ; Wu, Kehe1 ; Xu, Huan1 ; Wang, Xiaofeng4Author affiliation: 1 School of Control and Computer Engineering, State Key Laboratory of Alternate Electrical Power System with Renewable Energy Sources, North China Electric Power University, Beijing 102206, China2 Education Technology Center, Beijing International Studies University, Beijing 100024, China3 National Computer Network Emergency Response Technical Team/Coordination Center of China, Beijing 100029, China4 Institute of Computing Technology, Chinese Academy of Sciences, Beijing 100190, China Corresponding author: Wang,Z.(****************.cn)Source title: IFIP Advances in Information and Communication TechnologyAbbreviated source title: IFIP Advances in Information and Communication Technology Volume: 385 AICTMonograph title: Intelligent Information Processing VI - 7th IFIP TC 12 International Conference, IIP 2012, ProceedingsIssue date: 2012Publication year: 2012Pages: 157-166Language: EnglishISSN: 18684238ISBN-13: 9783642328909Document type: Conference article (CA)Conference name: 7th IFIP International Conference on Intelligent Information Processing, IIP 2012Conference date: October 12, 2012 - October 15, 2012Conference location: Guilin, ChinaConference code: 94249Sponsor: IFIP TC12; Guilin University of Electronic Technology; Chinese Academy of Sciences, Institute of Computing TechnologyPublisher: Springer New York, 233 Spring Street, New York, NY 10013-1578, United States Abstract: ADML is an architectural description language based on Dynamic Description Logic for defining and simulating the behavior of system architecture. ADML is being developed as a new formal language and/or conceptual model for representing the architectures of concurrent and distributed systems, both hardware and software. ADML embraces dynamic change as a fundamental consideration, supports a broad class of adaptive changes at the architectural level, and offers a uniform way to represent and reason about both static and dynamic aspects of systems. Because the ADML is based on the Dynamic Description Logic DDL( (D)), which can represent both dynamic semantics and static semantics under a unified logical framework, architectural ontology entailment for the ADML languages can be reduced to knowledge base satisfiability in DDL( (D)), and dynamic description logic algorithms and implementations can be used to provide reasoning services for ADML. In this article, we present the syntax of ADML, explain its underlying semantics using the Dynamic Description Logic DDL( (D)), and describe the core architecture description features of ADML. © 2012 IFIP International Federation for Information Processing.Number of references: 14Main heading: Data descriptionControlled terms: Formal languages - Knowledge based systems - Knowledge representation - Semantics - Software architectureUncontrolled terms: Architectural description languages - Architectural levels - Architecture description - Architecture description languages - Conceptual model - Distributed systems - Dynamic adaptations - Dynamic changes - Dynamic description logic - Dynamic semantic - Hardware and software - Knowledge base - Knowledge representation and reasoning - Logical frameworks - ON dynamics - Satisfiability - Static and dynamic - Static semantics - System architecturesClassification code: 723 Computer Software, Data Handling and Applications - 903.2 Information DisseminationDOI: 10.1007/978-3-642-32891-6_21Database: CompendexCompilation and indexing terms, © 2013 Elsevier Inc.4. Accession number: 20121214883239Title: An architecture dynamic modeling language for self-healing systemsAuthors: Wang, Zhuxiao1 ; Guo, Jing2; Wu, Kehe1; He, Hui1; Chen, Fei1Author affiliation: 1 School of Control and Computer Engineering, State Key Laboratory of Alternate Electrical Power System with Renewable Energy Sources, North China Electric Power University, Beijing 102206, China2 National Computer Network Emergency Response Technical Team, Coordination Center of China, Beijing 100029, ChinaCorresponding author: Wang,Z.(****************.cn)Source title: Procedia EngineeringAbbreviated source title: Procedia Eng.Volume: 29Monograph title: 2012 International Workshop on Information and Electronics Engineering Issue date: 2012Publication year: 2012Pages: 3909-3913Language: EnglishISSN: 18777058Document type: Conference article (CA)Conference name: 2012 International Workshop on Information and Electronics Engineering, IWIEE 2012Conference date: March 10, 2012 - March 11, 2012Conference location: Harbin, ChinaConference code: 89020Sponsor: Harbin University of Science and Technology; International Science and Engineering Research CenterPublisher: Elsevier Ltd, Langford Lane, Kidlington, Oxford, OX5 1GB, United Kingdom Abstract: As modern software-based systems increase in complexity, recovery from malicious attacks and rectification of system faults become more difficult, labor-intensive, and error-prone. These factors have actuated research dealing with the concept of self-healing systems, which employ architectural models to monitor system behavior and use inputs obtaining therefore to adapt themselves to the run-time environment. Numerous architectural description languages (ADLs) have been developed, each providing complementary capabilities for architectural development and analysis. Unfortunately, few ADLs embrace dynamic change as a fundamental consideration and support a broad class of adaptive changes at the architectural level. The Architecture Dynamic Modeling Language (ADML) is being developed as a new formal language and/or conceptual model for representing dynamic software architectures. The ADML couple the static information provided by the system requirements and the dynamic knowledge provided by tactics, and offer a uniform way to represent and reason about both static and dynamic aspects of self-healing systems. Because the ADML is based on the Dynamic Description Logic DDL, architectural ontology entailment for the ADML languages can be reduced to knowledge base satisfiability in DDL. © 2011 Published by Elsevier Ltd.Number of references: 10Main heading: ArchitectureControlled terms: Data description - Electronics engineering - Embedded systems -Formal languages - Knowledge based systems - Knowledge representation - Software architectureUncontrolled terms: Architecture description languages - Dynamic adaptation - Dynamic description logic - Knowledge representation and reasoning - Self-healing systemsClassification code: 723 Computer Software, Data Handling and Applications - 722 Computer Systems and Equipment - 718 Telephone Systems and Related Technologies; Line Communications - 717 Optical Communication - 716 Telecommunication; Radar, Radio and Television - 715 Electronic Equipment, General Purpose and Industrial - 714 Electronic Components and Tubes - 713 Electronic Circuits - 402 Buildings and TowersDOI: 10.1016/j.proeng.2012.01.593Database: CompendexCompilation and indexing terms, © 2013 Elsevier Inc.5. Accession number: 20124315590040Title: A tableau-based reasoning algorithm for distributed dynamic description logics Authors: Wang, Zhuxiao1 ; Guan, Zhitao1 ; Li, Wei1 ; Wu, Kehe1 ; Guo, Jing2 ; Tian, Guanhua3Author affiliation: 1 School of Control and Computer Engineering, State Key Laboratory of Alternate Electrical Power System with Renewable Energy Sources, North China Electric Power University, 102206 Beijing, China2 National Computer Network Emergency Response Technical Team, Coordination Center of China, 100029 Beijing, China3 Institute of Automation, Chinese Academy of Sciences, 100190 Beijing, China Corresponding author: Wang,Z.(****************.cn)Source title: Communications in Computer and Information ScienceAbbreviated source title: Commun. Comput. Info. Sci.Volume: 307 CCISIssue: PART 1Monograph title: Information Computing and Applications - Third International Conference, ICICA 2012, ProceedingsIssue date: 2012Publication year: 2012Pages: 192-199Language: EnglishISSN: 18650929ISBN-13: 9783642340376Document type: Conference article (CA)Conference name: 3rd International Conference on Information Computing and Applications, ICICA 2012Conference date: September 14, 2012 - September 16, 2012Conference location: Chengde, ChinaConference code: 93206Sponsor: National Science Foundation of China; Hunan Institute of Engineering; YanshanUniversity; Northeastern University at Qinhuangdao; Chengde Petroleum CollegePublisher: Springer Verlag, Tiergartenstrasse 17, Heidelberg, D-69121, Germany Abstract: As a family of dynamic description logics, DDL(X) is constructed by embracing actions into the description logic X, where X represents well-studied description logics ranging from the ALC to the SHOIQ. The usage of distributed computation techniques in reasoning is an important premise for the adoption of Dynamic Description Logics in a real-world setting. Practical scalability of DDL(X) reasoning inspired recently a proposal of Distributed Dynamic Description Logics (D3L) framework. D3L is a natural generalization of the DDL(X) framework, which is designed to model the distributed dynamically-changing knowledge repositories interconnected by semantic mappings and to accomplish reasoning in distributed, heterogeneous environments. In this paper, we investigate the reasoning mechanisms in D3L and propose a tableau-based reasoning algorithm for D3L, built as a composition of the state of the art tableaux reasoners for DDL(X). © 2012 Springer-Verlag.Number of references: 15Main heading: Data descriptionControlled terms: Algorithms - Formal languages - Inference engines - Semantics Uncontrolled terms: Description logic - Distributed computations - Distributed dynamics - Distributed Reasoning - Dynamic description logic - Heterogeneous environments - Knowledge repository - Natural generalization - Reasoning algorithms - Reasoning mechanism - Semantic mapping - State of the art - Tableau algorithm - Tableaux reasonersClassification code: 723 Computer Software, Data Handling and Applications - 903.2 Information Dissemination - 921 MathematicsDOI: 10.1007/978-3-642-34038-3_27Database: CompendexCompilation and indexing terms, © 2013 Elsevier Inc.6. Accession number: 20150400451745Title: A formal model for attack mutation using dynamic description logicsAuthors: Wang, Zhuxiao1 Email author ****************.cn;Guo, Jing2 Email ********************************;Shi,******************************.cn;He,Hui1Email author ***************.cn;Zhang, Ying1 Email author *******************.cn;Peng, Hui3 ***************************.cn;Tian,*************************************.cn Author affiliation: 1 School of Control and Computer Engineering, State Key Laboratory of Alternate Electrical Power System with Renewable Energy Sources, North China Electric Power University, Beijing, China2 National Computer Network Emergency Response Technical Team/Coordination Center of China, Beijing, China3 Education Technology Center, Beijing International Studies University, Beijing, China4 Institute of Automation, Chinese Academy of Sciences, Beijing, ChinaCorresponding author: Wang, ZhuxiaoSource title: IFIP Advances in Information and Communication TechnologyAbbreviated source title: IFIP Advances in Information and Communication Technology V olume: 432V olume title: Intelligent Information Processing VII - 8th IFIP TC 12 International Conference, IIP 2014, ProceedingsIssue date: 2014Publication year: 2014Pages: 303-311Language: EnglishISSN: 18684238ISBN-13: 9783662449790Document type: Journal article (JA)Publisher: Springer New York LLCAbstract: All currently available Network-based Intrusion Detection Systems (NIDS) rely upon passive protocol analysis which is fundamentally flawed as an attack can evade detection by exploiting ambiguities in the traffic stream as seen by the NIDS. We observe that different attack variations can be derived from the original attack using simple transformations. This paper proposes a semantic model for attack mutation based on dynamic description logics (DDL(X)), extensions of description logics (DLs) with a dynamic dimension, and explores the possibility of using DDL(X) as a basis for evasion composition. The attack mutation model describes all the possible transformations and how they can be applied to the original attack to generate a large number of attack variations. Furthermore, this paper presents a heuristics planning algorithm for the automation of evasion composition at the functional level based on DDL(X). Our approach employs classical DL-TBoxes to capture the constraints of the domain, DL-ABoxes to present the attack, and DL-formulas to encode the objective sequence of packets respectively. In such a way, the evasion composition problem is solved by a decidable tableau procedure. The preliminary results certify the potential of the approach. © IFIP International Federation for Information Processing 2014.Number of references: 9Main heading: Data descriptionControlled terms: Algorithms - Formal languages - Intrusion detection - Knowledge representation - SemanticsUncontrolled terms: Advanced evasion techniques - Dynamic description logic - Intrusion detection/prevention systems - Knowledge representation and reasoning - MultiprotocolsClassification code: 723 Computer Software, Data Handling and Applications - 903.2 Information DisseminationDatabase: CompendexCompilation and indexing terms, © 2015 Elsevier Inc.7. Accession number: 20130115855490Title: Linear cryptanalysis and security tradeoff of block ciphering systems with channel errorsAuthors: Guo, Jing1 ; Wang, Zhuxiao2Author affiliation: 1 National Computer Network Emergency Response Technical Team/Coordination Center of China (CNCERT/CC), Beijing 100029, China2 School of Control and Computer Engineering, State Key Laboratory of Alternate Electrical Power System with Renewable Energy Sources, North China Electric Power University, Beijing 102206, ChinaCorresponding author: Guo,J.(**************************)Source title: Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics)Abbreviated source title: Lect. Notes Comput. Sci.Volume: 7645 LNCSMonograph title: Network and System Security - 6th International Conference, NSS 2012, ProceedingsIssue date: 2012Publication year: 2012Pages: 405-416Language: EnglishISSN: 03029743E-ISSN: 16113349ISBN-13: 9783642346002Document type: Conference article (CA)Conference name: 6th International Conference on Network and System Security, NSS 2012 Conference date: November 21, 2012 - November 23, 2012Conference location: Wuyishan, Fujian, ChinaConference code: 94688Publisher: Springer Verlag, Tiergartenstrasse 17, Heidelberg, D-69121, Germany Abstract: Channel errors are usually treated as an obstacle in designing an encrypted wireless system. So we are supposed to reduce them as much as possible due to the potential error bursts contributed by an avalanche effect of block ciphers. In this paper, we propose that channel errors are to be explored for the benefit of security enhancement as they could be translated to additional efforts in cryptanalysis for an adversary node. To achieve this, a system with an outer block channel coder and an inner block cipher is presented. A framework for linear cryptanalysis is established under which an eavesdropper takes advantage of linear relationship among coded symbols, as well as linear approximation of ciphers. Also presented is an analysis on the tradeoff between security enhancement and performance degradation in the presence of channel errors. © 2012 Springer-Verlag.Number of references: 13Main heading: CryptographyControlled terms: Commerce - Errors - Network securityUncontrolled terms: Avalanche effects - Block ciphers - Channel error - Coded symbols - Linear approximations - Linear cryptanalysis - Linear relationships - Performance degradation - Potential errors - Security enhancements - Wireless systems Classification code: 723 Computer Software, Data Handling and Applications - 731 Automatic Control Principles and Applications - 911.2 Industrial Economics - 921 MathematicsDOI: 10.1007/978-3-642-34601-9_31Database: CompendexCompilation and indexing terms, © 2013 Elsevier Inc.8. Accession number: 20123915464951Title: Research on sentiment analysis in sentence and text levels with priorsAuthors: He, Hui1, 3 ; Chen, Bo2 ; Wang, Zhuxiao3Author affiliation: 1 School of Control and Computer Engineering, North China Electric Power University, Beijing, China2 Beijing University of Posts and Telecommunications, Beijing, China3 Postdoctoral Working Station, China United Network Communications Group Company Limited, Beijing, ChinaCorresponding author: He,H.(****************)Source title: International Journal of Digital Content Technology and its Applications Abbreviated source title: Int. J. Digit. Content Technol. Appl.Volume: 6Issue: 15Issue date: August 2012Publication year: 2012Pages: 518-525Language: EnglishISSN: 19759339E-ISSN: 22339310Document type: Journal article (JA)Publisher: Advanced Institute of Convergence Information Technology, 707 Seokjang-dong, Gyeongju, BI Center, Room 207, Gyeongju, Gyeongbuk, 780-714, Korea, Republic of Abstract: Recently, sentiment analysis of text is becoming a hotspot in the study of natural language processing, which has drawn interesting attention due to its research value and extensive applications. This paper introduces a sentiment analysis system, which is to satisfy two aspects of sentiment analysis requirement in sentence and text levels. They are sentence orientation analysis and text sentiment retrieval. An improved Maximum Entropy (MaxEnt) with priors is used to judge the sentence orientation, which combined with Indri is used to retrieve sentiment texts according to interested terms. This sentiment analysis system has been applied in Chinese Opinion Analysis Evaluation (COAE). Promising results and analysis are presented at the end of this paper. Number of references: 26Main heading: Maximum entropy methodsControlled terms: Computational linguistics - Data mining - Information retrieval - Natural language processing systemsUncontrolled terms: Hot spot - Indri - Maximum entropy - NAtural language processing - Opinion analysis - Orientation analysis - Prior - Sentiment analysis Classification code: 716.1 Information Theory and Signal Processing - 721.1 Computer Theory, Includes Formal Logic, Automata Theory, Switching Theory, Programming Theory - 723.2 Data Processing and Image Processing - 723.5 Computer ApplicationsDOI: 10.4156/jdcta.vol6.issue15.59Database: CompendexCompilation and indexing terms, © 2013 Elsevier Inc.。
论文收录引用检索证明报告

论文收录引用检索证明报告
报告编号:JS200905008
论文收录引用
检索证明报告
教育部科技查新工作站(G07)南京航空航天大学查新检索咨询中心
二零零九年五月八日
检索证明报告
委托人单位:南京航空航天大学
委托人:张三
检索要求:1、检索作者近五年发表的论文或专著被SCI、EI、ISTP收录情况。
2、检索作者近五年发表的论文或专著被他引情况。
检索日期:2009年05月08日
检索数据库:
1.SCI EXPANDED网络版(ISI Web of Science,1998 - 2009)
2.EI COMPENDEX 网络版(Engineering Village 2,1969 - 2009)
3.ISTP网络版(ISI Proceedings,1991 - 2009)
检索结果:
经检索,作者近五年发表的论文或专著被以上数据库收录和引用情况如下:
1. SCI收录:作者有5篇论文被SCI收录(均同时被EI收录)。
2. EI收录:作者有5篇期刊论文被EI收录。
3. ISTP收录:作者有5篇会议论文被ISTP收录。
4. SCI引用:作者有4篇文献被他人引用11次。
(此处“他引”是指文献被除作者及合作者以外其他人的引用)。
说明:数据会有遗漏(详见附件)
特此证明!
检索证明人:
教育部科技查新工作站(G07)
南京航空航天大学查新检索咨询中心2009-05-08。
论文收录检索证明

论文收录检索证明尊敬的读者:作者:所属机构:大学发表时间:2022年5月收录情况:1. 收录数据库:中国知网(CNKI)2. 检索情况:该论文已被中国知网收录,并在其数据库中进行检索。
3. 影响因子:该论文在CNKI数据库中的影响因子为2.5。
4. 引用情况:截至目前,该论文已被引用20次。
证明人:职务:大学图书馆馆长日期:2022年10月10日特此证明。
论文收录检索证明尊敬的读者:作者:所属机构:大学发表时间:2022年5月收录情况:1. 收录数据库:中国知网(CNKI)2. 检索情况:该论文已被中国知网收录,并在其数据库中进行检索。
3. 影响因子:该论文在CNKI数据库中的影响因子为2.5。
4. 引用情况:截至目前,该论文已被引用20次。
证明人:职务:大学图书馆馆长日期:2022年10月10日特此证明。
该论文在学术界引起了广泛关注,得到了同行的高度评价。
论文中的研究成果为图像识别技术的发展提供了有力支持,对于推动相关领域的研究具有重要意义。
论文收录检索证明尊敬的读者:作者:所属机构:大学发表时间:2022年5月收录情况:1. 收录数据库:中国知网(CNKI)2. 检索情况:该论文已被中国知网收录,并在其数据库中进行检索。
3. 影响因子:该论文在CNKI数据库中的影响因子为2.5。
4. 引用情况:截至目前,该论文已被引用20次。
证明人:职务:大学图书馆馆长日期:2022年10月10日特此证明。
该论文在学术界引起了广泛关注,得到了同行的高度评价。
论文中的研究成果为图像识别技术的发展提供了有力支持,对于推动相关领域的研究具有重要意义。
谢谢!大学图书馆2022年10月10日。
文献检索证明附表样例

序号
论文名称
作者排名
文中单位
发表刊物
(名称、年卷期、页码)
收录
类型
影响因子
大类分区
1.
第一作者
1.华南农业大学;2.中山大学
……
SCI
3.536(发文当年,如2012年)
生物2区(发文当年)
2.
3.
4.
……
通讯作者
华南农业大学
……
EI
/
/
5.
……
注:(1)文中单位写中文,如果某作者文中单位有多个,需按顺序均填上;
0
2
合计
122
3
27
114
3
26
去重后:总引146次
去重后:他引137次
注:“大类分区”和“影响因子”查看中科院JCR分区在线平台检索结果页;“被引频次”查看SCI引用检索结果页。
收录
类型
IF2012
大类分区
(2011)
被引频次
SCIE
总引
CPCI
总引
CSCD
总引
SCIE
他引
CPCI
他引
CSCD
他引
1
......
第一作者
SOIL BIOLOGY & BIOCHEMISTRY
2008, 41(4): 965-978
SCI
3.504
农林科学1区
12
0
4
12
0
4
2
......
通讯作者
(2)“发表刊物”、“发表年月”和“文献类型”,可在SCI/EI检索结果页中拷贝,EI数据库中未标注发表年月者,可以不填;大类分区和影响因子查看中科院JCR分区在线平台检索结果页。
法律案件检索报告范文(3篇)

第1篇一、案件基本信息案件名称:张三诉李四合同纠纷案案号:(2022)XX民初XX号审理法院:XX市XX区人民法院起诉时间:2022年4月1日开庭时间:2022年5月15日判决时间:2022年6月10日二、案件背景原告张三与被告李四于2021年5月签订了一份《房屋租赁合同》,约定张三将位于XX市XX区的一套房屋出租给李四,租赁期限为一年,租金每月XX元。
合同签订后,李四按时支付了第一个月的租金。
然而,自第二个月起,李四未再支付租金,且在原告多次催要下仍不支付。
原告张三遂向法院提起诉讼,要求被告李四支付剩余租金及违约金。
三、法律依据1. 《中华人民共和国合同法》第二十二条:当事人应当履行合同约定的义务,不得擅自变更或者解除合同。
第二十三条:当事人一方不履行合同义务或者履行合同义务不符合约定的,应当承担继续履行、采取补救措施或者赔偿损失等违约责任。
2. 《中华人民共和国民法典》第七百零九条:当事人一方未支付价款或者报酬的,对方可以请求其支付价款或者报酬。
第七百一十一条:当事人一方不履行合同义务或者履行合同义务不符合约定的,应当承担继续履行、采取补救措施或者赔偿损失等违约责任。
四、案件检索结果1. 案例一:(2021)XX民初XX号,原告王某诉被告李某租赁合同纠纷案判决结果:法院判决被告李某支付原告王某剩余租金及违约金。
本案与本案案情相似,法院判决支持了原告的诉讼请求,对本案具有参考价值。
2. 案例二:(2020)XX民初XX号,原告赵某诉被告钱某租赁合同纠纷案判决结果:法院判决被告钱某支付原告赵某剩余租金及违约金。
本案与本案案情相似,法院判决支持了原告的诉讼请求,对本案具有参考价值。
3. 案例三:(2019)XX民初XX号,原告孙某诉被告周某租赁合同纠纷案判决结果:法院判决被告周某支付原告孙某剩余租金及违约金。
本案与本案案情相似,法院判决支持了原告的诉讼请求,对本案具有参考价值。
五、案件分析通过检索上述案例,可以看出在租赁合同纠纷案件中,法院普遍认为租赁合同双方当事人应当履行合同约定的义务。
国家图书馆检索证明 (7页)

本文部分内容来自网络整理,本司不为其真实性负责,如有异议或侵权请及时联系,本司将立即删除!== 本文为word格式,下载后可方便编辑和修改! ==国家图书馆检索证明篇一:国家图书馆论文收录引用检索申请单国家图书馆论文收录引用检索申请单联系方式:电话010-********传真010-********E_mail:kjck@ 篇二:国家图书馆馆藏文献复制证明委托单国家图书馆馆藏文献复制证明委托单国家图书馆馆藏文献复制证明收费标准(自201X年3月1日起实施)一、证明费:100元。
二、附件费用:1. 纸本书籍、报纸、期刊:中文文献30元/篇;外文文献50元/篇。
2. 数据库文献:中文文献20元/篇;外文文献50元/篇。
3. 纸本图片类广告:50元/条。
三、成本费用:1. 报纸保存本扫描:A3 4元/张,A4 3元/张2. 复印费:A4 0.2元/张3. 打印费:A4 0.5元/张4. 快递费:北京地区15元起,外埠25元起;四、加急费:5篇以内的馆藏文献复制证明服务,用户需要当天完成的,收取总费用的100%的加急费;超过5篇文献原则上当天不提供检索报告,具体完成时间根据实际情况双方约定,用户需要在约定时间前完成咨询的,收取总费用的50%-100%的加急费。
五、其他费用:其他特殊情况,用户可通过邮件或电话向咨询馆员咨询。
国家图书馆科技查新中心篇三:《文献信息检索》习题答案文献信息检索(答案)《文献信息检索》习题答案一、单选题1、文献是记录有知识的(A)A.载体B.纸张C.光盘 D.磁盘2、如果需要检索某位作者的文献被引用的情况,应该使用(C)检索。
A.分类索引 B.作者索引 C.引文索引D.主题索引3、下列哪种文献属于二次文献( D.)A.专利文献B.学位论文C.会议文献D.目录4、纸质信息源的载体是(D)A.光盘B.缩微平片C.感光材料D.纸张5、《中国图书馆分类法》(简称《中图法》)将图书分成( A.)A.5大部分22个大类B.5大部分26个大类C.6大部分22个大类D.6大部分26个大类6、利用文献末尾所附参考文献进行检索的方法是(C)A.倒查法B.顺查法C.引文追溯法D.抽查法7、广义的信息检索包含两个过程(B)A.检索与利用B.存储与检索C.存储与利用D.检索与报道8、中国国家标准的代码是(A)A.GB. B.CB.C.ZGD.CG9、( D )是报道文献出版或收藏信息为主要功能的工具。
