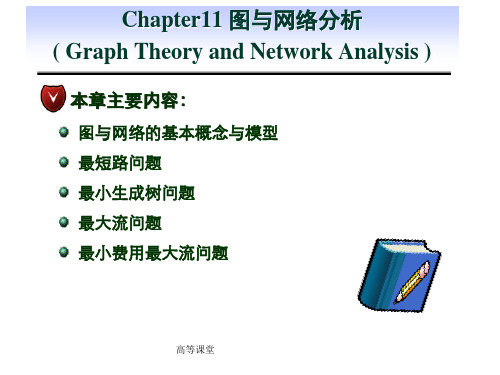
chapter7图与网络
EMC 信息存储与管理(要点总结)
管理 CLARiiON:命令行界面(Naviseccli)、图形用户界面(Navisphere)
Navisphere 套件:
• Navisphere Manager:配置 CLARiiOn,基于 Web 的界面
磁盘驱动器接口
磁盘驱动器的性能(寻道时间、旋转延迟、数据传输速率)
•
寻道时间:读写头在盘面上移动进行定位的时间。(全程时间、平均时间、 相邻磁道时间)
• 旋转延迟:盘片旋转以定位读写头下方的数据所用的时间 • 数据传输速率:每个单位时间磁盘能够传输到 HBA(主机总线配置器)的
平均数据量
影响磁盘性能的基本准则 将磁盘看成两部分:
• 最近最少访问算法(Least Recently Used,LRU):连续地监视数据访问, 识别出长时间没有被访问的页面。
• 最近访问算法(用的页面将被释 放或标记为可重用。
缓存写入数据时,存储系统必须将脏页面刷清以保证或标记为可重用。刷清模式 如下
带有缓存的写操作:一个 I/O 被写入缓存并得到响应比直接写入磁盘所用的时间 要少得多,还可以合并优化。
• 回写缓存:数据被存入缓存,主机立即响应。 • 直接写操作:数据被存入缓存并立即写到磁盘中,然后响应主机。
缓存实现(专用缓存,全局缓存)
缓存管理(为了能够在系统中总是保留一部分页面以及可以在需要时被释放的页 面)
嵌套 RAID(许多数据中心对 RAID 阵列的数据冗余和性能都有需求)
RAID 3(通过存储分带提供高性能,并利用奇偶校验提升容错性)RAID 4(与 RAID 3 类似,支持独立访问)
《网络分析》课件
理解网络的结构和行为,预测网络的 变化,优化网络的性能,解决实际应 用问题。
网络分析的背景与重要性
背景
随着信息技术的发展,网络在各个领域的应用越来越广泛,如社交网络、互联 网、生物网络等。这些网络具有复杂的结构和行为,需要用网络分析的方法进 行研究。
重要性
网络分析是研究复杂网络的重要工具,对于理解网络的本质和规律,预测和控 制网络的行为,优化网络的性能具有重要的意义。
《网络分析》PPT课件
CONTENTS 目录
• 网络分析概述 • 网络分析方法 • 网络分析工具与技术 • 网络分析应用场景 • 网络分析的挑战与未来发展
CHAPTER 01
网络分析概述
网络分析的定义与目的
定义
网络分析是对网络中节点和边的属性 及其关系进行量化的过程,目的是揭 示网络的结构特征和行为规律。
路径分析
路径是连接网络中节点的线段,路径分析是研究网络 中信息流动的重要手段。
输入 标题
详细描述
路径分析主要关注网络中节点之间的连接关系和信息 传递的路径,通过寻找最短路径、最长路径、平均路 径等指标来了解网络的结构和信息传递效率。
总结词
总结词
最短路径问题是寻找两个节点之间距离最短的路径, 常用的算法包括Dijkstra算法和Floyd-Warshall算法
总结词
节点中心性分析是节点分析的重要内容。
详细描述
节点分析主要关注网络中的个体元素,包括节点的属性、 度数、聚类系数等,用于理解节点在网络中的重要性、影 响力以及与其他节点的关联性。
详细描述
节点中心性分析通过计算节点的中心度来评估节点在网络 中的重要程度,常见的中心性指标包括度中心性、介数中 心性、接近中心性等。
密码编码学与网络安全(第五版)答案
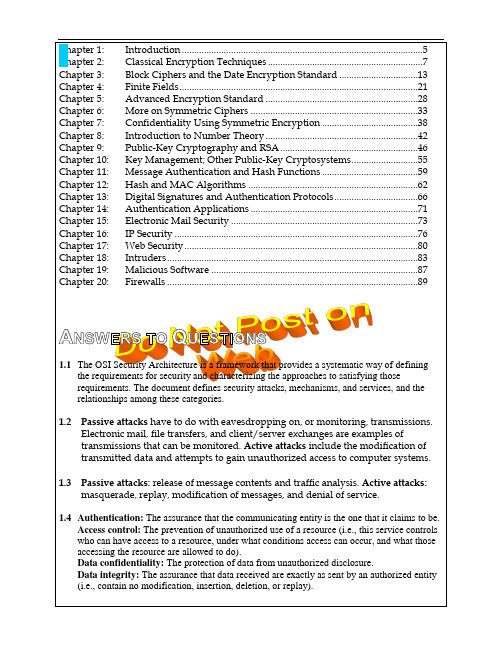
Chapter 1: Introduction (5)Chapter 2: Classical Encryption Techniques (7)Chapter 3: Block Ciphers and the Date Encryption Standard (13)Chapter 4: Finite Fields (21)Chapter 5: Advanced Encryption Standard (28)Chapter 6: More on Symmetric Ciphers (33)Chapter 7: Confidentiality Using Symmetric Encryption (38)Chapter 8: Introduction to Number Theory (42)Chapter 9: Public-Key Cryptography and RSA (46)Chapter 10: Key Management; Other Public-Key Cryptosystems (55)Chapter 11: Message Authentication and Hash Functions (59)Chapter 12: Hash and MAC Algorithms (62)Chapter 13: Digital Signatures and Authentication Protocols (66)Chapter 14: Authentication Applications (71)Chapter 15: Electronic Mail Security (73)Chapter 16: IP Security (76)Chapter 17: Web Security (80)Chapter 18: Intruders (83)Chapter 19: Malicious Software (87)Chapter 20: Firewalls (89)A NSWERS TO Q UESTIONS1.1The OSI Security Architecture is a framework that provides a systematic way of definingthe requirements for security and characterizing the approaches to satisfying thoserequirements. The document defines security attacks, mechanisms, and services, and the relationships among these categories.1.2 Passive attacks have to do with eavesdropping on, or monitoring, transmissions.Electronic mail, file transfers, and client/server exchanges are examples oftransmissions that can be monitored. Active attacks include the modification of transmitted data and attempts to gain unauthorized access to computer systems.1.3 Passive attacks: release of message contents and traffic analysis. Active attacks:masquerade, replay, modification of messages, and denial of service.1.4 Authentication: The assurance that the communicating entity is the one that it claims to be.Access control: The prevention of unauthorized use of a resource (i.e., this service controls who can have access to a resource, under what conditions access can occur, and what those accessing the resource are allowed to do).Data confidentiality: The protection of data from unauthorized disclosure.Data integrity: The assurance that data received are exactly as sent by an authorized entity(i.e., contain no modification, insertion, deletion, or replay).Nonrepudiation: Provides protection against denial by one of the entities involved in a communication of having participated in all or part of the communication.Availability service: The property of a system or a system resource being accessible and usable upon demand by an authorized system entity, according to performancespecifications for the system (i.e., a system is available if it provides services according to the system design whenever users request them).1.5 See Table 1.3.C HAPTER 2C LASSICAL E NCRYPTION T ECHNIQUESR2.1 Plaintext, encryption algorithm, secret key, ciphertext, decryption algorithm.2.2 Permutation and substitution.2.3 One key for symmetric ciphers, two keys for asymmetric ciphers.2.4 A stream cipher is one that encrypts a digital data stream one bit or one byte at atime. A block cipher is one in which a block of plaintext is treated as a whole and used to produce a ciphertext block of equal length.2.5 Cryptanalysis and brute force.2.6 Ciphertext only. One possible attack under these circumstances is the brute-forceapproach of trying all possible keys. If the key space is very large, this becomesimpractical. Thus, the opponent must rely on an analysis of the ciphertext itself, generally applying various statistical tests to it. Known plaintext. The analyst may be able to capture one or more plaintext messages as well as their encryptions.With this knowledge, the analyst may be able to deduce the key on the basis of the way in which the known plaintext is transformed. Chosen plaintext. If the analyst is able to choose the messages to encrypt, the analyst may deliberately pickpatterns that can be expected to reveal the structure of the key.2.7 An encryption scheme is unconditionally secure if the ciphertext generated by thescheme does not contain enough information to determine uniquely thecorresponding plaintext, no matter how much ciphertext is available. Anencryption scheme is said to be computationally secure if: (1) the cost of breaking the cipher exceeds the value of the encrypted information, and (2) the timerequired to break the cipher exceeds the useful lifetime of the information.2.8 The Caesar cipher involves replacing each letter of the alphabet with the letterstanding k places further down the alphabet, for k in the range 1 through 25.2.9 A monoalphabetic substitution cipher maps a plaintext alphabet to a ciphertextalphabet, so that each letter of the plaintext alphabet maps to a single unique letter of the ciphertext alphabet.2.10 The Playfair algorithm is based on the use of a 5 5 matrix of letters constructedusing a keyword. Plaintext is encrypted two letters at a time using this matrix.2.11 A polyalphabetic substitution cipher uses a separate monoalphabetic substitutioncipher for each successive letter of plaintext, depending on a key.2.12 1. There is the practical problem of making large quantities of random keys. Anyheavily used system might require millions of random characters on a regularbasis. Supplying truly random characters in this volume is a significant task.2. Even more daunting is the problem of key distribution and protection. For everymessage to be sent, a key of equal length is needed by both sender and receiver.Thus, a mammoth key distribution problem exists.2.13 A transposition cipher involves a permutation of the plaintext letters.2.14 Steganography involves concealing the existence of a message.2.1 a. No. A change in the value of b shifts the relationship between plaintext lettersand ciphertext letters to the left or right uniformly, so that if the mapping isone-to-one it remains one-to-one.b. 2, 4, 6, 8, 10, 12, 13, 14, 16, 18, 20, 22, 24. Any value of a larger than 25 isequivalent to a mod 26.c. The values of a and 26 must have no common positive integer factor other than1. This is equivalent to saying that a and 26 are relatively prime, or that thegreatest common divisor of a and 26 is 1. To see this, first note that E(a, p) = E(a,q) (0 ≤ p≤ q < 26) if and only if a(p–q) is divisible by 26. 1. Suppose that a and26 are relatively prime. Then, a(p–q) is not divisible by 26, because there is noway to reduce the fraction a/26 and (p–q) is less than 26. 2. Suppose that a and26 have a common factor k > 1. Then E(a, p) = E(a, q), if q = p + m/k≠ p.2.2 There are 12 allowable values of a (1, 3, 5, 7, 9, 11, 15, 17, 19, 21, 23, 25). There are 26allowable values of b, from 0 through 25). Thus the total number of distinct affine Caesar ciphers is 12 26 = 312.2.3 Assume that the most frequent plaintext letter is e and the second most frequentletter is t. Note that the numerical values are e = 4; B = 1; t = 19; U = 20. Then we have the following equations:1 = (4a + b) mod 2620 = (19a + b) mod 26Thus, 19 = 15a mod 26. By trial and error, we solve: a = 3.Then 1 = (12 + b) mod 26. By observation, b = 15.2.4 A good glass in the Bishop's hostel in the Devil's seat—twenty-one degrees andthirteen minutes—northeast and by north—main branch seventh limb east side—shoot from the left eye of the death's head— a bee line from the tree through the shot fifty feet out. (from The Gold Bug, by Edgar Allan Poe)2.5 a.The first letter t corresponds to A, the second letter h corresponds to B, e is C, sis D, and so on. Second and subsequent occurrences of a letter in the keysentence are ignored. The resultciphertext: SIDKHKDM AF HCRKIABIE SHIMC KD LFEAILAplaintext: basilisk to leviathan blake is contactb.It is a monalphabetic cipher and so easily breakable.c.The last sentence may not contain all the letters of the alphabet. If the firstsentence is used, the second and subsequent sentences may also be used untilall 26 letters are encountered.2.6The cipher refers to the words in the page of a book. The first entry, 534, refers topage 534. The second entry, C2, refers to column two. The remaining numbers are words in that column. The names DOUGLAS and BIRLSTONE are simply words that do not appear on that page. Elementary! (from The Valley of Fear, by Sir Arthur Conan Doyle)2.7 a.2 8 10 7 9 63 14 54 2 8 1056 37 1 9ISRNG BUTLF RRAFR LIDLP FTIYO NVSEE TBEHI HTETAEYHAT TUCME HRGTA IOENT TUSRU IEADR FOETO LHMETNTEDS IFWRO HUTEL EITDSb.The two matrices are used in reverse order. First, the ciphertext is laid out incolumns in the second matrix, taking into account the order dictated by thesecond memory word. Then, the contents of the second matrix are read left toright, top to bottom and laid out in columns in the first matrix, taking intoaccount the order dictated by the first memory word. The plaintext is then read left to right, top to bottom.c.Although this is a weak method, it may have use with time-sensitiveinformation and an adversary without immediate access to good cryptanalysis(e.g., tactical use). Plus it doesn't require anything more than paper and pencil,and can be easily remembered.2.8 SPUTNIK2.9 PT BOAT ONE OWE NINE LOST IN ACTION IN BLACKETT STRAIT TWOMILES SW MERESU COVE X CREW OF TWELVE X REQUEST ANYINFORMATION2.10 a.b.2.11 a. UZTBDLGZPNNWLGTGTUEROVLDBDUHFPERHWQSRZb.UZTBDLGZPNNWLGTGTUEROVLDBDUHFPERHWQSRZc. A cyclic rotation of rows and/or columns leads to equivalent substitutions. Inthis case, the matrix for part a of this problem is obtained from the matrix ofProblem 2.10a, by rotating the columns by one step and the rows by three steps.2.12 a. 25! ≈ 284b. Given any 5x5 configuration, any of the four row rotations is equivalent, for atotal of five equivalent configurations. For each of these five configurations,any of the four column rotations is equivalent. So each configuration in factrepresents 25 equivalent configurations. Thus, the total number of unique keysis 25!/25 = 24!2.13 A mixed Caesar cipher. The amount of shift is determined by the keyword, whichdetermines the placement of letters in the matrix.2.14 a. Difficulties are things that show what men are.b. Irrationally held truths may be more harmful than reasoned errors.2.15 a. We need an even number of letters, so append a "q" to the end of the message.Then convert the letters into the corresponding alphabetic positions:The calculations proceed two letters at a time. The first pair:The first two ciphertext characters are alphabetic positions 7 and 22, whichcorrespond to GV. The complete ciphertext:GVUIGVKODZYPUHEKJHUZWFZFWSJSDZMUDZMYCJQMFWWUQRKRb. We first perform a matrix inversion. Note that the determinate of theencryption matrix is (9 ⨯ 7) – (4 ⨯ 5) = 43. Using the matrix inversion formulafrom the book:Here we used the fact that (43)–1 = 23 in Z26. Once the inverse matrix has beendetermined, decryption can proceed. Source: [LEWA00].2.16 Consider the matrix K with elements k ij to consist of the set of column vectors K j,where:andThe ciphertext of the following chosen plaintext n-grams reveals the columns of K:(B, A, A, …, A, A) ↔ K1(A, B, A, …, A, A) ↔ K2:(A, A, A, …, A, B) ↔ K n2.17 a.7 ⨯ 134b.7 ⨯ 134c.134d.10 ⨯ 134e.24⨯ 132f.24⨯(132– 1) ⨯ 13g. 37648h.23530i.1572482.18 key: legleglegleplaintext: explanationciphertext: PBVWETLXOZR2.19 a.b.2.20your package ready Friday 21st room three Please destroy this immediately.2.21 y the message out in a matrix 8 letters across. Each integer in the key tellsyou which letter to choose in the corresponding row. Result:He sitteth between the cherubims. The isles may be gladthereof. As the rivers in the south.b.Quite secure. In each row there is one of eight possibilities. So if the ciphertextis 8n letters in length, then the number of possible plaintexts is 8n.c. Not very secure. Lord Peter figured it out. (from The Nine Tailors)3.1 Most symmetric block encryption algorithms in current use are based on the Feistelblock cipher structure. Therefore, a study of the Feistel structure reveals theprinciples behind these more recent ciphers.3.2 A stream cipher is one that encrypts a digital data stream one bit or one byte at atime. A block cipher is one in which a block of plaintext is treated as a whole and used to produce a ciphertext block of equal length.3.3 If a small block size, such as n = 4, is used, then the system is equivalent to aclassical substitution cipher. For small n, such systems are vulnerable to a statistical analysis of the plaintext. For a large block size, the size of the key, which is on the order of n 2n, makes the system impractical.3.4 In a product cipher, two or more basic ciphers are performed in sequence in such away that the final result or product is cryptographically stronger than any of the component ciphers.3.5 In diffusion, the statistical structure of the plaintext is dissipated into long-rangestatistics of the ciphertext. This is achieved by having each plaintext digit affect thevalue of many ciphertext digits, which is equivalent to saying that each ciphertext digit is affected by many plaintext digits. Confusion seeks to make the relationship between the statistics of the ciphertext and the value of the encryption key ascomplex as possible, again to thwart attempts to discover the key. Thus, even if the attacker can get some handle on the statistics of the ciphertext, the way in which the key was used to produce that ciphertext is so complex as to make it difficult todeduce the key. This is achieved by the use of a complex substitution algorithm. 3.6 Block size: Larger block sizes mean greater security (all other things being equal)but reduced encryption/decryption speed. Key size: Larger key size means greater security but may decrease encryption/decryption speed. Number of rounds: The essence of the Feistel cipher is that a single round offers inadequate security but that multiple rounds offer increasing security. Subkey generation algorithm:Greater complexity in this algorithm should lead to greater difficulty ofcryptanalysis. Round function: Again, greater complexity generally means greater resistance to cryptanalysis. Fast software encryption/decryption: In many cases, encryption is embedded in applications or utility functions in such a way as topreclude a hardware implementation. Accordingly, the speed of execution of the algorithm becomes a concern. Ease of analysis: Although we would like to make our algorithm as difficult as possible to cryptanalyze, there is great benefit inmaking the algorithm easy to analyze. That is, if the algorithm can be concisely and clearly explained, it is easier to analyze that algorithm for cryptanalyticvulnerabilities and therefore develop a higher level of assurance as to its strength.3.7 The S-box is a substitution function that introduces nonlinearity and adds to thecomplexity of the transformation.3.8 The avalanche effect is a property of any encryption algorithm such that a smallchange in either the plaintext or the key produces a significant change in theciphertext.3.9 Differential cryptanalysis is a technique in which chosen plaintexts with particularXOR difference patterns are encrypted. The difference patterns of the resultingciphertext provide information that can be used to determine the encryption key.Linear cryptanalysis is based on finding linear approximations to describe thetransformations performed in a block cipher.3.1 a. For an n-bit block size are 2n possible different plaintext blocks and 2n possibledifferent ciphertext blocks. For both the plaintext and ciphertext, if we treat theblock as an unsigned integer, the values are in the range 0 through 2n– 1. For amapping to be reversible, each plaintext block must map into a uniqueciphertext block. Thus, to enumerate all possible reversible mappings, the blockwith value 0 can map into anyone of 2n possible ciphertext blocks. For anygiven mapping of the block with value 0, the block with value 1 can map intoany one of 2n– 1 possible ciphertext blocks, and so on. Thus, the total numberof reversible mappings is (2n)!.b. In theory, the key length could be log2(2n)! bits. For example, assign eachmapping a number, from 1 through (2n)! and maintain a table that shows themapping for each such number. Then, the key would only require log2(2n)! bits, but we would also require this huge table. A more straightforward way todefine the key is to have the key consist of the ciphertext value for eachplaintext block, listed in sequence for plaintext blocks 0 through 2n– 1. This iswhat is suggested by Table 3.1. In this case the key size is n⨯ 2n and the hugetable is not required.3.2 Because of the key schedule, the round functions used in rounds 9 through 16 aremirror images of the round functions used in rounds 1 through 8. From this fact we see that encryption and decryption are identical. We are given a ciphertext c.Let m' = c. Ask the encryption oracle to encrypt m'. The ciphertext returned by the oracle will be the decryption of c.3.3 a.We need only determine the probability that for the remaining N – t plaintextsP i, we have E[K, P i] ≠ E[K', P i]. But E[K, P i] = E[K', P i] for all the remaining P iwith probability 1 – 1/(N–t)!.b.Without loss of generality we may assume the E[K, P i] = P i since E K(•) is takenover all permutations. It then follows that we seek the probability that apermutation on N–t objects has exactly t' fixed points, which would be theadditional t' points of agreement between E(K, •) and E(K', •). But apermutation on N–t objects with t' fixed points is equal to the number of wayst' out of N–t objects can be fixed, while the remaining N–t–t' are not fixed.Then using Problem 3.4 we have thatPr(t' additional fixed points) = ⨯Pr(no fixed points in N – t – t' objects)=We see that this reduces to the solution to part (a) when t' = N–t.3.4Let be the set of permutations on [0, 1, . . ., 2n– 1], which is referredto as the symmetric group on 2n objects, and let N = 2n. For 0 ≤ i≤ N, let A i be all mappings for which π(i) = i. It follows that |A i| = (N– 1)! and= (N–k)!. The inclusion-exclusion principle states thatPr(no fixed points in π)=== 1 – 1 + 1/2! – 1/3! + . . . + (–1)N⨯ 1/N!= e–1 +Then since e–1≈ 0.368, we find that for even small values of N, approximately37% of permutations contain no fixed points.3.53.6 Main key K = 111…111 (56 bits)Round keys K1 = K2=…= K16 = 1111..111 (48 bits)Ciphertext C = 1111…111 (64 bits)Input to the first round of decryption =LD0RD0 = RE16LE16 = IP(C) = 1111...111 (64 bits)LD0 = RD0 = 1111...111 (32 bits)Output of the first round of decryption = LD1RD1LD1 = RD0= 1111…111 (32 bits)Thus, the bits no. 1 and 16 of the output are equal to ‘1’.RD1 = LD0 F(RD0, K16)We are looking for bits no. 1 and 16 of RD1 (33 and 48 of the entire output).Based on the analysis of the permutation P, bit 1 of F(RD0, K16) comes from thefourth output of the S-box S4, and bit 16 of F(RD0, K16) comes from the second output of the S-box S3. These bits are XOR-ed with 1’s from the correspondingpositions of LD0.Inside of the function F,E(RD0) ≈ K16= 0000…000 (48 bits),and thus inputs to all eight S-boxes are equal to “000000”.Output from the S-box S4 = “0111”, and thus the fourth output is equal to ‘1’,Output from the S-box S3 = “1010”, and thus the second output is equal to ‘0’.From here, after the XOR, the bit no. 33 of the first round output is equal to ‘0’, and the bit no. 48 is equal to ‘1’.3.7 In the solution given below the following general properties of the XOR functionare used:A ⊕ 1 = A'(A ⊕ B)' = A' ⊕ B = A ⊕ B'A' ⊕ B' = A ⊕ BWhere A' = the bitwise complement of A.a. F (R n, K n+1) = 1We haveL n+1 = R n; R n+1 = L n⊕ F (R n, K n+1) = L n⊕ 1 = L n'ThusL n+2 = R n+1 = L n' ; R n+2 = L n+1 = R n'i.e., after each two rounds we obtain the bit complement of the original input,and every four rounds we obtain back the original input:L n+4 = L n+2' = L n ; R n+2 = R n+2' = R nTherefore,L16 = L0; R16 = R0An input to the inverse initial permutation is R16 L16.Therefore, the transformation computed by the modified DES can berepresented as follows:C = IP–1(SWAP(IP(M))), where SWAP is a permutation exchanging the positionof two halves of the input: SWAP(A, B) = (B, A).This function is linear (and thus also affine). Actually, this is a permutation, the product of three permutations IP, SWAP, and IP–1. This permutation ishowever different from the identity permutation.b. F (R n, K n+1) = R n'We haveL n+1 = R n; R n+1 = L n⊕ F(R n, K n+1) = L n⊕ R n'L n+2 = R n+1 = L n⊕ R n'R n+2 = L n+1⊕ F(R n+1, K n+2) = R n≈ (L n⊕ R n')' = R n⊕ L n⊕ R n'' = L nL n+3 = R n+2 = L nR n+3 = L n+2⊕ F (R n+2, K n+3) = (L n≈ R n') ⊕ L n' = R n' ⊕1 = R ni.e., after each three rounds we come back to the original input.L15 = L0; R15 = R0andL16 = R0(1)R16 = L0⊕ R0' (2)An input to the inverse initial permutation is R16 L16.A function described by (1) and (2) is affine, as bitwise complement is affine,and the other transformations are linear.The transformation computed by the modified DES can be represented asfollows:C = IP–1(FUN2(IP(M))), where FUN2(A, B) = (A ⊕ B', B).This function is affine as a product of three affine functions.In all cases decryption looks exactly the same as encryption.3.8 a. First, pass the 64-bit input through PC-1 (Table 3.4a) to produce a 56-bit result.Then perform a left circular shift separately on the two 28-bit halves. Finally,pass the 56-bit result through PC-2 (Table 3.4b) to produce the 48-bit K1.:in binary notation: 0000 1011 0000 0010 0110 01111001 1011 0100 1001 1010 0101in hexadecimal notation: 0 B 0 2 6 7 9 B 4 9 A 5b. L0, R0 are derived by passing the 64-plaintext through IP (Table 3.2a):L0 = 1100 1100 0000 0000 1100 1100 1111 1111R0 = 1111 0000 1010 1010 1111 0000 1010 1010c. The E table (Table 3.2c) expands R0 to 48 bits:E(R0) = 01110 100001 010101 010101 011110 100001 010101 010101d. A = 011100 010001 011100 110010 111000 010101 110011 110000e. (1110) = (14) = 0 (base 10) = 0000 (base 2)(1000) = (8) = 12 (base 10) = 1100 (base 2)(1110) = (14) = 2 (base 10) = 0010 (base 2)(1001) = (9) = 1 (base 10) = 0001 (base 2)(1100) = (12) = 6 (base 10) = 0110 (base 2)(1010) = (10) = 13 (base 10) = 1101 (base 2)(1001) = (9) = 5 (base 10) = 0101 (base 2)(1000) = (8) = 0 (base 10) = 0000 (base 2)f. B = 0000 1100 0010 0001 0110 1101 0101 0000g. Using Table 3.2d, P(B) = 1001 0010 0001 1100 0010 0000 1001 1100h. R1 = 0101 1110 0001 1100 1110 1100 0110 0011i. L1 = R0. The ciphertext is the concatenation of L1 and R1. Source: [MEYE82]3.9The reasoning for the Feistel cipher, as shown in Figure 3.6 applies in the case ofDES. We only have to show the effect of the IP and IP–1 functions. For encryption, the input to the final IP–1 is RE16|| LE16. The output of that stage is the ciphertext.On decryption, the first step is to take the ciphertext and pass it through IP. Because IP is the inverse of IP–1, the result of this operation is just RE16|| LE16, which isequivalent to LD0|| RD0. Then, we follow the same reasoning as with the Feistel cipher to reach a point where LE0 = RD16 and RE0 = LD16. Decryption is completed by passing LD0|| RD0 through IP–1. Again, because IP is the inverse of IP–1, passing the plaintext through IP as the first step of encryption yields LD0|| RD0, thusshowing that decryption is the inverse of encryption.3.10a.Let us work this from the inside out.T16(L15|| R15) = L16|| R16T17(L16|| R16) = R16|| L16IP [IP–1 (R16|| L16)] = R16|| L16TD1(R16|| L16) = R15|| L15b.T16(L15|| R15) = L16|| R16IP [IP–1 (L16|| R16)] = L16|| R16TD1(R16 || L16) = R16|| L16 f(R16, K16)≠ L15|| R153.11PC-1 is essentially the same as IP with every eighth bit eliminated. This wouldenable a similar type of implementation. Beyond that, there does not appear to be any particular cryptographic significance.3.13a.The equality in the hint can be shown by listing all 1-bit possibilities:We also need the equality A ⊕ B = A' ⊕ B', which is easily seen to be true. Now, consider the two XOR operations in Figure 3.8. If the plaintext and key for anencryption are complemented, then the inputs to the first XOR are alsocomplemented. The output, then, is the same as for the uncomplementedinputs. Further down, we see that only one of the two inputs to the secondXOR is complemented, therefore, the output is the complement of the outputthat would be generated by uncomplemented inputs.b.In a chosen plaintext attack, if for chosen plaintext X, the analyst can obtain Y1= E[K, X] and Y2 = E[K, X'], then an exhaustive key search requires only 255rather than 256 encryptions. To see this, note that (Y2)' = E[K', X]. Now, pick atest value of the key T and perform E[T, X]. If the result is Y1, then we knowthat T is the correct key. If the result is (Y2)', then we know that T' is the correctkey. If neither result appears, then we have eliminated two possible keys withone encryption.3.14 The result can be demonstrated by tracing through the way in which the bits areused. An easy, but not necessary, way to see this is to number the 64 bits of the key as follows (read each vertical column of 2 digits as a number):2113355-1025554-0214434-1123334-0012343-2021453-0202435-0110454- 1031975-1176107-2423401-7632789-7452553-0858846-6836043-9495226-The first bit of the key is identified as 21, the second as 10, the third as 13, and so on.The eight bits that are not used in the calculation are unnumbered. The numbers 01 through 28 and 30 through 57 are used. The reason for this assignment is to clarify the way in which the subkeys are chosen. With this assignment, the subkey for the first iteration contains 48 bits, 01 through 24 and 30 through 53, in their naturalnumerical order. It is easy at this point to see that the first 24 bits of each subkey will always be from the bits designated 01 through 28, and the second 24 bits of each subkey will always be from the bits designated 30 through 57.3.15 For 1 ≤ i ≤ 128, take c i∈ {0, 1}128 to be the string containing a 1 in position i andthen zeros elsewhere. Obtain the decryption of these 128 ciphertexts. Let m1,m2, . . . , m128 be the corresponding plaintexts. Now, given any ciphertext c which does not consist of all zeros, there is a unique nonempty subset of the c i’s which we can XOR together to obtain c. Let I(c) ⊆ {1, 2, . . . , 128} denote this subset.ObserveThus, we obtain the plaintext of c by computing . Let 0 be the all-zerostring. Note that 0 = 0⊕0. From this we obtain E(0) = E(0⊕0) = E(0) ⊕ E(0) = 0.Thus, the plaintext of c = 0 is m = 0. Hence we can decrypt every c ∈ {0, 1}128.3.16a. This adds nothing to the security of the algorithm. There is a one-to-onereversible relationship between the 10-bit key and the output of the P10function. If we consider the output of the P10 function as a new key, then thereare still 210 different unique keys.b. By the same reasoning as (a), this adds nothing to the security of the algorithm.3.17s = wxyz + wxy + wyz + wy + wz + yz + w + x + zt = wxz + wyz + wz + xz + yz + w + y3.18OK4.1 A group is a set of elements that is closed under a binary operation and that isassociative and that includes an identity element and an inverse element.4.2 A ring is a set of elements that is closed under two binary operations, addition andsubtraction, with the following: the addition operation is a group that iscommutative; the multiplication operation is associative and is distributive over the addition operation.C HAPTER 4F INITE F IELDS。
8.4 网络最大流问题

所有指向为vs→vt的弧,称为前向弧,记作μ +;
所有指向为vt →vs的弧,称为后向弧,记做μ
-,
增广链:设 f 是一个可行流,μ是从vs 到 vt 的一条链,若μ满 足下列条件,称之为(关于可行流 f 的)增广链。
1)在(vi , vj)∈μ+上,0≤fij<cij,即μ+中的弧都是非饱和弧。
2)在(vi,vj)∈μ-上,0<fij≤cij,即μ-中的弧都是非零流弧。
§8.4 网络最大流问题
Page 22
(3) 检查与v3点相邻的未标号的点,因f3t<c3t,故对vt 标 l(vt)=min{l(v3), c3t-f3t } =min{1, 1}= 1 找到一条增广链 vs→v1→v2 →v3 →vt ( v , 1) 2 (-v v12, 1) (4,3) v4 (3,3) (5,3) (1,1) (1,1) (3,0)
v ( f ) f s1 f s 2 f 4 t f 3 t 5
§8.4 网络最大流问题
Page 25
例8.10 用标号算法求下图中vs→vt的最大流量,并找出最小 截。 v1 9(3) v3 8(7)
5(4) 5(4)
2(0)
vs
7(5)
6(1)
●
vt
10(8) v2 9(9) v4
§8.4 网络最大流问题
基本方法: (1)找出第一个可行流(例如所有弧的流量fij =0);
Page 14
(2)用标号的方法找一条增广链:
首先给发点vs标号(0,+∞),第一个数字表示标号从哪一点得到;
第二个数字表示允许的最大调整量。
选择一个点 vi 已标号且另一端未标号的弧沿着某条链向收
运筹学完整版(OperationsResearch)

本课程的特点和要求
先修课:高等数学,基础概率、线性代数 特点:系统整体优化;多学科的配合;模型方法的应用 运筹学的研究的主要步骤:
真实系统
数据准备
系统分析 问题描述
模型建立 与修改
模型求解 与检验
结果分析与 实施
本课程授课方式与考核
讲授为主,结合习题作业
学科总成绩
平时成绩 (40%)
期末成绩 (60%)
2. 线性规划的数学模型由三个要素构成
决策变量 目标函数 约束条件
Decision variables Objective function Constraints
怎样辨别一个模型是线性规划模型?
其特征是: (1)问题的目标函数是多个决策变量的线性函数, 通常是求最大值或最小值; (2)问题的约束条件是一组多个决策变量的线性不 等式或等式。
线性规划问题的数学模型
4. 建模步骤
(1) 确定决策变量:即需要我们作出决策或选择的量。一般 情况下,题目问什么就设什么为决策变量; (2) 找出所有限定条件:即决策变量受到的所有的约束; (3) 写出目标函数:即问题所要达到的目标,并明确是max 还是 min。
线性规划问题的数学模型
5. 线性规划数学模型的一般形式
3x1 +x2 +x3 +2 x4 ≤180
x1、x2 、x3 、x4 ≥0
线性规划问题的数学模型
例1.5 某航运局现有船只种类、数量以及计划期内各条航 线的货运量、货运成本如下表所示:
航线号
船队 类型
1 1
2
3 2
4
拖轮
1 1 2 1
编队形式 A型 驳船 2 — 2 —
B型 驳船 —
运筹学-图与网络模型以及最小费用最大流(高级课堂)
v4
v5
高等课堂 7
图与网络的基本概念与模型
环, 多重边, 简单图
e1
如果边e的两个端点相重,称该边为 环。如右图中边e1为环。如果两个点 v2
e2
e4 v1e3
v3
之间多于一条,称为多重边,如右图
e5
中的e4和e5,对无环、无多重边的图
e6
e7
e8
称作简单图。
v4
v5
高等课堂 8
图与网络的基本概念与模型
的长度(单位:公里)。
17
v2
5
6
15
6 v4
V1
(甲地)
43
10
4
4
2
v5
v6
解:这是一个求v3无向图的最短路的问题。可以把无向图的每一边
(vi,vj)都用方向相反的两条弧(vi,vj)和(vj,vi)代替,就化为有向图,
即可用Dijkstra算法来求解。也可直接在无向图中用Dijkstra算法来求解。
最短路问题
最短路问题:对一个赋权的有向图D中的指定的两个点Vs和Vt找 到一条从 Vs 到 Vt 的路,使得这条路上所有弧的权数的总和最小, 这条路被称之为从Vs到Vt的最短路。这条路上所有弧的权数的总 和被称为从Vs到Vt的距离。
• 求最短路有两种算法:
狄克斯屈拉(Dijkstra)(双标号)算法 逐次逼近算法
• 图论中图是由点和边构成,可以反映一些对象之间的关系。 • 一般情况下图中点的相对位置如何、点与点之间联线的长短曲
直,对于反映对象之间的关系并不是重要的。
图的定义(P230)
若用点表示研究的对象,用边表示这些对象之间的联系,则图 G可以定义为点和边的集合,记作:
CCNA完整知识点.

chapter 1L1:物理层PDU:bits 比特流作用:传输比特流(01000100101010...)介质:同轴电缆: coaxial cable 传输距离 500米双绞线(TP):twisted-pair cable 传输距离 100米非屏蔽双绞线(UTP):室内屏蔽双绞线(STP):室外(环境干扰强)直通线:AA BB 链接异性端口:pc-hub pc-sw sw-router交叉线:AB 链接同性端口:pc-pc router-router pc-router sw-sw反线:1-8 8-1 用于本地连接的console 控制线网线的两种制作方式:568A:白绿绿白橙篮白蓝橙白棕棕568B:白橙橙白绿篮白蓝绿白棕棕 1236 网线使用DCE:数据终端设备,需要配置clock rate DTE:数据终结设备对应传输介质的支持传输距离:1)1000base-cx 使用的是铜缆。
最大传输距离25米2)100Base-Tx/Fx100Base-Tx以5类非屏蔽双绞线为传输介质(最大传输距离是100米)100Base-Fx以光纤为传输介质(2000米)。
3)1000base-SX(MMF多模):最长传输距离是550米4)1000base-LX:可以使用单模光纤也可以使用多模光纤使用多模光纤的最大传输距离为550m,使用单模光纤的最大传输距离为3千米5)1000base-zx(单模):最长传输距离是70KM以太网 Ethernent传输模式:单工:只能发或者收半双工:即可以收也可以发,但是同一时间只能收或者发列如对讲机全双工:同一时间既可以收也可以发列如手机Auto:中继器(Repeater):对信号放大,双绞线的传输距离只有100M,使用中继器可以延长传输距离。
hub :多口中继,一个数据帧从一个入口进,会发送到HUB的所有其他端口而不进行过滤。
L2:数据链路层PDU:frame 帧作用:成帧,差错控制设备:网桥(bridge):基于MAC地址转发,根据mac-port表,数据包只发到和MAC地址相对应的port端口交换机(switch):多口网桥,独享带宽L2层编制:MAC地址MAC地址构成:48bit,12位十六进制数可以通过ipconfig/all 查询电脑的mac地址L2表:MAC-port表(mac地址表)冲突域:不可避免的数据冲突范围,由中继、hub链接构成并扩大,见到L2层端口截止,每一个交换机端口形成一个冲突域HUB:所有端口都在一个冲突域,是增加了冲突域的范围交换机:没一个端口都是一个冲突域,是增加了冲突域的数量,减少了冲突域的范围HUB:是共享带宽 10M 所有端口共享10M交换机:独享带宽 10M 每个端口同时有10ML3:网络层 PDU:packet 包作用:逻辑编制:ip地址、路由(路径的选择)IP地址与mac地址的区别?Mac地址通信:同一个网络,mac通信跨网络通信:ip地址IP地址:版本v4;32bit;点分是进制法 192.168.0.1IP=网络位+主机位掩码:mask:连续的1+连续的0,来确定IP地址的网络位+主机位,1位对应网络位,0位对应主机位。
组织结构与组织基础

团队制优 点
团队制缺点
双重忠诚与冲突 时间与资源花费在
开会上 散漫的分权
虚拟网络制 的优点
可以利用全球的知识
01
02
高度的灵活性和响应能力
03
管理成本降低
网络制缺点
控制匮乏,边界脆弱 员工忠诚度削弱
对管理者要求高
组织结构的进化史
任务小组,团队 & 项目管理
01
单击此处添加小标题
任务小组: 用来解决涉及几个部门 的短期问题临时团队或者委员会
不正确搭配: 确定环境下的横向结构 太松散的结构
图7-10 环境与组织结构的关系
7.4.3 结构适应技术
• 1、伍德沃德的制造技术
生产技术的复杂性 组织结构: 形式化 集权化 最高行政人员的比例 间接人工与直接人工的比例 基层主管的控制跨度 沟通: 书面(纵向) 口头(横向) 总体结构
制造技术 小批量生产 低
是职权硬币的另一面
员工完成被分派的任务 或工作的义务
管理者被授予的职权和 所担负的职责是一致的
责任制
职权和职责相联系的 机制
要求向其指挥链上的 上级汇报工作结果
是组织结构的一部分
202X
授权
管理者用于转授职权和职责的过程 管理者 应该 转授职权
直线职权与参谋职权
直线职权 – 管理者享有指挥和控制其直接下属 的正式正式权力
04 网 络 制 结 构 , 并 说 明 组 织
运用这些结构的理由.
学习目标 (续.)
解释为什么组织需要进行跨部门的横向协调和化层级 结构的纵向协调,并表述协调机制.
说明如何运用组织结构来实现组织的战略目标. 举例说明如何设计组织结构以适应环境的不确定性. 定义生产技术(制造技术、服务技术和数字技术),
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
相关概念: 相关概念:
图论中的图由点和点及之间的连线(带箭头、不带箭头)构成。 有向图:由点和弧(带箭头的连线)构成,关联边有方向. 有向图:由点和弧(带箭头的连线)构成
D=(V,A),V表示有向图 的点的集合,A表示有向图 , 表示有向图 的点的集合, 表示有向图 表示有向图D的点的集合 D的弧的集合 的 路与回路 2 4 6 1 3 5
30,2 22,6 v7 乙地
6 v6 16,5
2
v2 15 v1 甲地 10 v3 4 3 6
17 5 v4 4 2 v5
v7 乙地 6 v6
距离22 最短路径为 v1—v3—v5 — v6 — v7 ,距离
求解最短路问题示例
算法求点1到点 例3:用Dijkstra算法求点 到点 的最短路 : 算法求点 到点6的最短路
OBJECTIVE FUNCTION VALUE 1) 19.00000 VARIABLE VALUE REDUCED COST X12 1.000000 7.000000 X13 0.000000 6.000000 X24 0.000000 13.000000 X25 1.000000 9.000000 X34 0.000000 15.000000 X35 0.000000 11.000000 X46 0.000000 4.000000 X56 1.000000 3.000000
7 4
5
2 8 1 6 3 10 12 11
7 4
5
2 8 1 6 3 10 11
7 4
5
2 8 1 6 3 11
7 4
5
例1:
某大学准备对其所属的7个学院的办公室计算机联网,可能 的连图如下,请设计一个网络能连通7个学院,并使总的线 路长度最短。 1
3 3 4 2 3 10 4 5 7
8
1 3 3 7 2 3 5
﹏﹏ ﹏ ﹏ ﹏ ﹏ ﹏
﹏ ﹏
欧拉回路与一笔画: 欧拉回路与一笔画: 连通图G中若存在一条道路(回路), 连通图G中若存在一条道路(回路), 过每边一次且仅一次, 过每边一次且仅一次,当且仅当该 图无奇点或只有两个奇点。 图无奇点或只有两个奇点。
2、最小生成树(支撑树)问题 、最小生成树(支撑树)
例2:电信公司准备在甲、乙两地沿路架设光缆 :电信公司准备在甲、 问如何架设使其光缆线路最短? 线,问如何架设使其光缆线路最短?
v2 15 v1 甲地 10 v3 4 v5 3 4 2 v6 6 17 5 v4 6 v7 乙地
15,1 13,3 v2 15 v1 0,s 甲地 10 v3 10,1 3 4 6 17 19,2 v4 18,5 4 v5 14,3 5
7,1
2 7 9 13
20,2 21,3
4 4 6
0,s 1
6 3 15 3 11 5
19,5
6,1
16,2 17,3
有向图用0-1规划求解 规划求解。用0-1变量xij表示从i点到j点的 有向图用 规划求解 弧(边)是否被采用,为1表示采用,为0表示不采用,则
min ∑ d ij xij ∑ xij = 1 , 对于起点i j ∑ xij = 1 , 对于终点j s.t. i ∑ xik = ∑ xkj , 对于其他点k j i xij为0-1变量
二、图与网络的典型问题
欧拉回路与道路问题(1763年发表的图 论问题的第一篇论文,解决了著名的哥 尼斯堡七桥问题。 ) 最小生成树问题 最短路问题 最大流问题 最小费用(最大)流问题
1、欧拉回路与道路问题 、
一个散步者能否走过七座桥,且每座桥只走过一次,最后 回到出发点。 欧拉归结为一笔画问题 每个点都只与奇数条线 奇数条线相关联 奇数条线
运筹学
第七章 图与网络
YU Junli
解决的问题:
图论解决运输系统设计、信息系统设计、 工程项目进度安排等。 运输系统设计
运输理论中运输、配置、转载问题,也是网 络问题,网络由点、弧组成。
最短路线问题、最小支撑树问题、最大 流问题、项目安排。
一、图与网络的基本概念
从实例引出图: 从实例引出图: 5个人之间认识关系:1与2,3与4,2与4,1与3 个人之间认识关系: 相互认识; 认识5 认识2 认识4 相互认识;3认识5,5认识2,5认识4。
OBJECTIVE FUNCTION VALUE 1) 22.00000 VARIABLE VALUE REDUCED COST F12 0.000000 15.000000 F13 1.000000 10.000000 F23 0.000000 3.000000 F24 0.000000 6.000000 F35 1.000000 4.000000 F27 0.000000 17.000000 F47 0.000000 5.000000 F45 0.000000 4.000000 F56 1.000000 2.000000 F67 1.000000 6.000000 K1 1.000000 0.000000 K2 0.000000 0.000000 K3 1.000000 0.000000 K4 0.000000 0.000000 K5 1.000000 0.000000
3、最短路问题 、
对于赋权的有向图或无向图,求其中一点到另 一点的最短路径。 “双标号法”(Dijkstra算法) 算法) 双标号法” 算法
做法: 做法:对图中的点vj赋予两个标号(lj,kj),第一个 标号lj表示起点vs至vj的最短路的长度 最短路的长度,第二个标号kj 最短路的长度 表示在vs至vj的最短路上vj前面一个邻点的下标 邻点的下标,从而 邻点的下标 找到vs到vt的最短路及vs到vt的距离。
无向图用0-1规划求解 规划求解: 无向图用 规划求解 用0-1变量xij表示从i点到j点的弧(边)是否被采用, 为1表示采用,为0表示不采用,则
min ∑ d ij xij
m , 对于起点 i ∑ xij = 1 j n , 对于终点 j ∑ xij = 1 s.t . i x - 2 y = 0 , 对于其他点 k , l = 1,2, L , ( j i ) l ∑ ij xij , yl 为0-1变量
4
8
4
1 3 3 7 2 3 5
4
4
1 3 3 7 2 34来自41 3 3 7 2 3
4
1 3 3 2 3 7
总长度=19百米 百米 总长度
破圈法举例
4 7 1 4 3 7 3 2 3 5 6 2 4 5 1 2 6 2 4 7
避圈法举例
4 7 1 4 3 7 3 2 3 5 6 2 4 5 1 2 6 2 4 7
无向图:由点和边构成的图 无向图:由点和边构成的图,关联边没有方向。
G=(V, E),V表示图 的点集合,E表示 表示图G的点集合 表示图 的点集合, 表示 的图G的 集合。 的图 的边集合。 链与圈
2 4 1 3 5 6
赋权图:边或弧相关有相应的指标(权重), 例如距离、费用等等。(网络图) 悬挂点、孤立点、奇点、偶点 链、边、连通图(无向图中两点之间,至少存 在一条链)、回路(路的第一点和最后一点相 同)、网络(有起点和发点的赋权有向图,称 为网络) 树(无圈的连通图)、图的生成树
一个乡有九个自然村,其间道路见下图:要以v0 村为中心建有线电视网络,如何架线,费用最低?
v1
1
4
v2
1
v3
3 1
2
1
v8
5
4 5
v0
2 4
4
v4
5
v7
3
v6
2
v5
树: 如某单位的组织结构
树:无圈的连通图 得到图的生成子图 边数=点数-1 例:高速公路建设;光缆通讯线路铺设 最小生成树问题就是在一个赋权的连通的无 向图上找出一个生成树,并使这个生成树的 所有边的权数之和最小。
定理一: 定理一:所有顶点次数之和等于所有边数 的2倍。 定理二: 定理二:在任一图中,奇点的个数必为偶 数。 定理三(树的性质)六种等价描述。 定理三 设:边数 q , 顶点数 p .
1、无圈连通图; 2、边数q = 顶点数p - 1; 3、连通,且 q = p - 1; 4、无圈,但加一边则得到唯一的圈; 5、连通,但若去一边则图不连通; 6、每对顶点之间有且仅有一条链。
链:由两两相邻的点及其相关联的边构成的点边序列。 圈:出起点和终点外链中所含的点均不相同的闭链。 路:若有从 u 到 v 不考虑方向的链,且各方向一致,则称之为从 u
到 v 的路。 路 闭链或回路 回路:路的第一点和最后一点相同则称为闭链 回路 闭链 回路,否则称该链 为开链。 赋权图:边或弧相关有相应的指标(权重)。 赋权图 奇点: 偶点: 奇点:与点连的边(弧)的个数为奇数; 偶点:d(v)=偶数; 悬挂点: 悬挂边: 悬挂点:d(v)=1;悬挂边:与悬挂点连接的边, 悬挂边 空图:E = ,无边图。 孤立点: 空图 孤立点:d(v)=0;空图 连通图:图中任意两点之间均至少有一条通路,否则称作不连通图。 连通图 网络:有起点和发点的赋权有向图,称为网络。 网络 树:无圈连通图;无圈图又称为树林,子连通图是树。
最小生成树的算法(贪心算法)
方法: 方法:避圈法
在不形成圈的前提下,按从小到大 从小到大的顺序依 从小到大 次加入边。 7 2
8 1 6 3 14 10 12 5 11 4
进入顺序: 进入顺序: 6 :1 -3 7 :2 -4 8 :1 -2 10: 10:3-4 成圈, 成圈,不进 11: 11:2-5 完成
例题:
某台机器可连续工作4年,也可于每年末 卖掉,换一台新的,已知于各年初 年初购置一 年初 台新机器的价格及不同役龄机器年末 年末的处 年末 理价格如下表所示。又新机器第一年运行 及维修费为0.3万元,使用1至3年后的机 器每年运行及维修费用分别为0.8,1.5, 2万元。请确定该机器的最优更新策略, 使4年内购买、更换、及运行维修的总费 用为最少。
