思科考试CCNA
思科认证CCNA认证试题和答案中文版

思科认证CCNA认证试题和答案中文版思科认证CCNA认证试题和答案中文版想要获得思科认证,首先要参加由思科推荐并授权的培训中心(Cisco Training Partner,简称CTP)所开设的培训课程。
完成学业后再到由全球考试机构Sylvan Prometric授权的.考试中心参加由思科指定的科目的认证考试。
通过指定的系列科目考试后,学员就可以获得相应分支系列等级的资格认证。
下面是店铺为大家搜集的相关试题,供大家参考练习。
16、路由器A串口0配置如下interface serial0link-protocol pppppp pap local-user huawei password simple quidwayip address 2.2.2.1 255.0.0.0路由器B串口及全局配置如下local-user huawei service-type ppp password simple quidway!interface serial0link-protocol pppppp authentication-mode papip address 2.2.2.2 255.0.0.0当两台路由器串口0相连时,两台路由器是否可以连接到对端()(A) 能(B) 不能答案:A17、关于千兆以太网,以下说法正确的是( )(A) IEEE802.3ab定义了千兆以太网(B) 在同一冲突域中,千兆以太网不允许中继器的互连(C) IEEE802.3z专门定义了千兆以太网在双绞线上的传输标准(D) 千兆以太网支持网络速率的自适应,可以与快速以太网自动协商传输速率答案:AB参考知识点:华为3com认证教材第一册3-8页18、高层的协议将数据传递到网络层后,形成( ),而后传送到数据链路层(A) 数据帧(B) 信元(C) 数据包(D) 数据段答案:C参考知识点:华为3com认证教材第一册1-20页19、在路由器上配置帧中继静态map必须指定( )参数(A) 本地的DLCI(B) 对端的DLCI(C) 本地的协议地址(D) 对端的协议地址答案:AD20、路由器的主要性能指标不包括( )(A) 延迟(B) 流通量(C) 帧丢失率(D) 语音数据压缩比答案:D【思科认证CCNA认证试题和答案中文版】。
思科认证CCNA认证试题与答案中文版
答案:D 注释:这个题目不是太严谨,应该加上子网掩码. A:224. 0. 0. 5 是多播地址 B: 127. 0.0. 0 保留作为测试使用 C:网络地址 26、 设置主接口由 up 转 down 后延迟 30 秒切换到备份接口,主 接口 由 down 转 up 后 60 秒钟切换回主接口的配置为()
忍一句,息一怒,饶一着,退一步。——《增广贤文》
人之为学,不日进则日退,独学无友,则孤陋而难成;久处一方,则习染而不自觉。——《顾炎武》
答案:D 注释:255. 255. 255. 255 是全网广播,DHCP 客户端发送全网广播来 查 找 DHCP 服务器. 24、 下而有关 NAT 叙述正确的是() (A) NAT 是英文“地址转换”的缩写,又称地址翻译 (B) XAT 用来实现私有地址与公用网络地址之间的转换 (C) 当内部网络的主机访问外部网络的时候,一定不需要 NAT (D) 地址转换的提出为解决 IP 地址紧张的问题提供了一个有效途 径 答案:ABD 25、 以下属于正确的主机的 IP 地址的是()
(A) arp-a (B) traceroute (C) routeprint (D) displayiprouting-table
答案:D 23、 D0. 0. 0 (B) 10. 0. 0. 1 (0127. 0. 0. 1 (D)255. 255. 255. 255
192. 168. 1. 1
答案:D 注释:PC 的'默认网关要指向路由器的以太网口的 IP 地址. 28、 ISDNB 信道速率是()
(A) 16kbps (B) 64kbps
思科 CCNA 学习试题 答案!!!

思科 CCNA 学习试题答案思科ccna学习试题答案CCNA课程测试一、单项选择题:1.媒体100BaseT的最大传输距离为:()a:10MB:100mc:1000md:500M2、路由器下,由一般用户模式进入特权用户模式的命令是:()a:enableb:configc:interfaced:router3、哪个命令可以成功测试网络:()a:router>ping192.5.5.0b:router#ping192.5.5.30c:router>ping192.5.5.256d:router#ping192.5.5.2554、介质工作在osi的哪一层()a:物理层B:数据链路层C:网络层D:传输层5。
100BaseT的速率为()Mbit/SA:1b:10C:100D:10006、在启用igrp协议时,所需要的参数是:()a:网络掩码b:子网号c:自治系统号d:跳数7、基本ip访问权限表的表号范围是:()a:1―100b:1-99c:100-199d:800-8998、查看路由表的命令是:()a:ShowInterface B:showrunc:showiprouted:showtable9、工作在osi第三层的设备是:()a:网卡b:路由器c:交换机d:集线器10、osi第二层数据封装完成后的名称是:()a:比特b:包c:帧d:段11.为了禁止网络210.93.105.0 FTP到网络223.8.151.0并允许其他信息传输,可以实现此功能的选项有:()a:access-list1deny210 93.105.0.0.0.0.0.0b:access-list100denytcp210.93.105.00.0.0.255223.8.151.00.0.0.255eqftpc:access-List100Permitipanyd:access-list100denytcp210.93.105.00.0.0.255223.8.151.00.0.0.255eqftpaccess-list100permitipanyany12.路由器下“特权用户模式”的标识符为:()a:>b:!c:#d:#配置如果)#13。
网络工程师考什么证比较好
网络工程师考什么证比较好在当今信息时代,网络工程师的需求越来越大,成为了一个备受追捧的职业。
作为一名网络工程师,选择适合自己的证书是非常重要的。
好的证书不仅能够提升个人的技能水平,还能够增加职场竞争力,为个人的职业生涯发展提供更多的机会。
而在网络工程师领域中,有许多证书可以选择,例如CCNA、CCNP、CCIE、JNCIA、JNCIS等等。
那么,网络工程师到底应该考什么证比较好呢?1. CCNA (Cisco Certified Network Associate)CCNA认证是由思科公司提供的全球公认的网络技术认证,它可以帮助网络工程师打下良好的基础。
持有CCNA证书的网络工程师可以证明自己具备构建、连接和维护网络的技能。
CCNA证书被认为是网络工程师入门的基础证书,不仅有助于理解网络的基本原理,还可以帮助网络工程师熟悉思科设备的配置与管理。
2. CCNP (Cisco Certified Network Professional)CCNP是思科网络专业级别证书,持有该证书的网络工程师可以证明自己掌握了中级网络技术,包括对网络规划、配置、调试和运维方面的能力。
相比CCNA,CCNP更加注重对网络更深层次的理解和实践能力的培养。
对于有一定工作经验的网络工程师来说,考取CCNP证书是提升个人技能水平的很好选择。
3. CCIE (Cisco Certified Internetwork Expert)CCIE是思科网络工程师领域中的最高级别认证,持有该证书的网络工程师可以证明自己拥有深入的网络知识和专业技能。
CCIE证书被认为是网络工程师的顶级认证,具有很高的含金量和认可度。
然而,考取CCIE证书难度很大,需要有非常扎实的技术基础和丰富的实战经验。
4. JNCIA (Juniper Networks Certified Internet Associate)JNCIA认证是由Juniper Networks提供的认证,它可以帮助网络工程师了解Juniper网络设备的体系结构和运作原理,提升熟练操作Juniper网络设备的能力。
思科网院-网络工程-CCNA1-2017计算机科学与技术-一到十一章-题库及答案
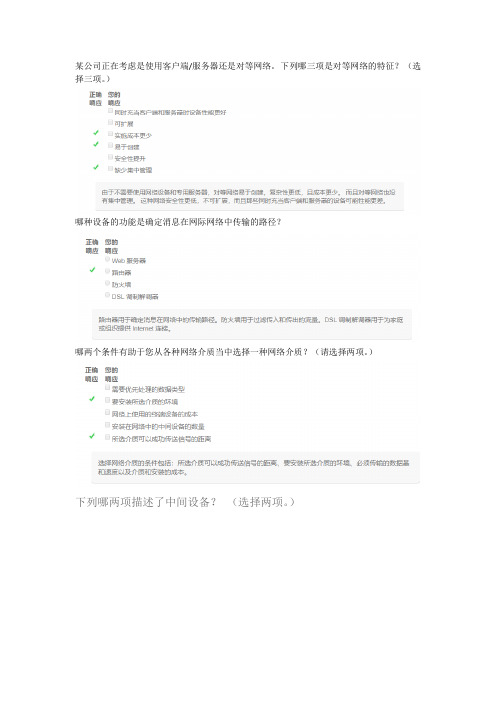
某公司正在考虑是使用客户端/服务器还是对等网络。
下列哪三项是对等网络的特征?(选择三项。
)哪种设备的功能是确定消息在网际网络中传输的路径?哪两个条件有助于您从各种网络介质当中选择一种网络介质?(请选择两项。
)下列哪两项描述了中间设备?(选择两项。
)网络上的终端设备有哪两项功能?(选择两项。
)由于许多学生带着自己的平板电脑和智能手机去学校访问学校资源,大学里的IT 人员最有可能需要重新设计的网络区域是什么?家庭用户必须要有哪种网络类型访问才能进行网上购物?一位分支机构办公室的员工正在为客户创建报价。
为此,该员工需要访问位于总部办公室的内部服务器上的机密定价信息。
该员工将要访问哪种类型的网络?下列哪两种连接选项可以为家庭办公室中的计算机提供始终在线的高带宽Internet 连接?(选择两项。
)下列哪两个Internet 连接选项不需要建筑物铺设物理电缆?(请选择两项。
)以下哪种术语描述了当对网络资源的请求超出可用容量时网络的状态?哪种类型的网络流量需要QoS?以下哪项表述准确定义了术语“带宽”?网络管理员正在实施一种要求复杂强密码的策略。
该策略支持哪种数据保护目标?下列哪种说法正确描述了云计算的特征?什么是Internet?下列哪种说法描述了电力线网络技术的用途?哪种安全侵犯会对家庭用户的生活造成最大损害?一位用户正在一个小型办公室网络上实施安全策略。
以下哪两种操作将为此网络提供求?(选择两项。
)A网络能够通过相同的通信通道传输语音、视频、文本和图形。
填空题。
缩写词是指允许员工在公司办公室中使用其个人设备访问网络和其他资源的策略。
正确答案:byod将每个描述与网络通信形式配对请将每个特征对应的internet连接类型进行匹配将每个定义与安全目标配对操作软件内核的作用是什么?网络管理员与交换机建立远程CLI 连接对其实施管理时,需要确保用户ID、密码和会话内容的保密性。
应当选择哪种访问方法?当在安全环境下执行初始配置时,下列哪个程序可用来访问Cisco 2960 交换机?哪个命令或组合键让用户返回命令层级中的上一级?某台路由器具有有效的操作系统,且NVRAM 中存储有配置文件。
思科考试CCNA

CCNA(1)适用班级:CCNA注意事项:1.在试卷的标封处填写姓名和班级2.考试时间共120分钟3.答案写在答题卡上1. What is the maximum number of IP addresses that can be assigned to hosts on a local subnetthat uses the subnet maskA. 14B. 15C. 16D. 30E. 31F. 622. You have a network that needs 29 subnets while maximizing the number of host addressesavailable on each subnet. How many bits must you borrow from the host field to provide thecorrect subnet maskA. 2B. 3C. 4D. 5E. 6F. 73. What is the subnetwork address for a host with the IP address The network address of provides how many subnets and hostsA. 7 subnets, 30 hosts eachB. 7 subnets, 2,046 hosts eachC. 7 subnets, 8,190 hosts eachD. 8 subnets, 30 hosts eachE. 8 subnets, 2,046 hosts eachF. 8 subnets, 8,190 hosts each5. Which two statements describe the IP address 10.16.3.65/23 (Choose two.)A. The subnet address is 10.16.3.0 The lowest host address in the subnet is 10.16.2.1 The last valid host address in the subnet is 10.16.2.254 The broadcast address of the subnet is 10.16.3.255 The network is not subnetted.6. If a host on a network has the address what is the subnetwork this hostbelongs toA. On a VLSM network, which mask should you use on point-to-point WAN links in order toreduce the waste of IP addressesA. /27B. /28C. /29D. /30E. /318. What is the subnetwork number of a host with an IP address of You have an interface on a router with the IP address of Including the routerinterface, how many hosts can have IP addresses on the LAN attached to the router interfaceA. 6B. 8C. 30D. 62E. 12610. You need to configure a server that is on the subnet The router has the firstavailable host address. Which of the following should you assign to the serverA. You have an interface on a router with the IP address of What is thebroadcast address the hosts will use on this LANA. You need to subnet a network that has 5 subnets, each with at least 16 hosts. Which classfulsubnet mask would you useA. A network administrator is connecting hosts A and B directly through their Ethernet interfaces,as shown in the illustration. Ping attempts between the hosts are unsuccessful. What can bedone to provide connectivity between the hosts (Choose two.)A. A crossover cable should be used in place of the straight-through cable.B. A rollover cable should be used in place of the straight-through cable.C. The subnet masks should be set to A default gateway needs to be set on each host.E. The subnet masks should be set to Address: Address: Cable164 Chapter 3 Subnetting, VLSMs, and Troubleshooting TCP/IP14. If an Ethernet port on a router were assigned an IP address of what wouldbe the valid subnet address of this hostA. Using the following illustration, what would be the IP address of E0 if you were using theeighth subnet The network ID is and you need to use the last available IPaddress in the range. The zero subnet should not be considered valid for this question.A. Using the illustration from the previous question, what would be the IP address of S0 if you wereusing the first subnet The network ID is and you need to use the last availableIP address in the range. Again, the zero subnet should not be considered valid for this question.A. Which configuration command must be in effect to allow the use of 8 subnets if the Class C subnet mask is Router(config)#ip classlessB. Router(config)#ip version 6C. Router(config)#no ip classfulD. Router(config)#ip unnumberedE. Router(config)#ip subnet-zeroF. Router(config)#ip all-nets18. You have a network with a subnet of Which is the valid host addressA. Your router has the following IP address on Ethernet0: Which of the following can be valid host IDs on the LAN interface attached to the router (Choose two.)A. To test the IP stack on your local host, which IP address would you pingA. 1.0.0.127C. You type show running-config and get this output:[output cut]Line console 0Exec-timeout 1 44Password 7098C0BQRLogin[output cut]What do the two numbers following the exec-timeout command meanA. If no command has been typed in 44 seconds, the console connection will be closed.B. If no router activity has been detected in 1 hour and 44 minutes, the console will be locked out.C. If no commands have been typed in 1 minute and 44 seconds, the console connection willbe closed.D. If you’re connected to the router by a Telnet connection, input must be detected within 1 minute and 44 seconds or the connection will be closed.22. You need to find the broadcast address used on a LAN on your router. What command willyou type into the router from user mode to find the broadcast addressA. show running-configB. show startup-configC. show interfacesD. show protocols23. You want to totally reinitialize the router and replace the current running-config with the current startup-config. What command will you useA. replace run startB. copy run startC. copy start runD. reloadReview Questions 24324. Which command will show you whether a DTE or a DCE cable is plugged into serial 0A. sh int s0B. sh int serial 0C. show controllers s 0D. show serial 0 controllers25. What keystroke will terminate setup modeA. Ctrl+ZB. Ctrl+^C. Ctrl+CD. Ctrl+Shift+^26. You set the console password, but when you display the configuration, the password doesn’t show up; it looks like this:[output cut]Line console 0Exec-timeout 1 44Password 7098C0BQRLogin[output cut]What cause the password to be stored like thisA. encrypt passwordB. service password-encryptionC. service-password-encryptionD. exec-timeout 1 4427. Which of the following commands will configure all the default VTY ports on a routerA. Router#line vty 0 4B. Router(config)#line vty 0 4C. Router(config-if)#line console 0D. Router(config)#line vty all28. Which of the following commands sets the secret password to CiscoA. enable secret password CiscoB. enable secret ciscoC. enable secret CiscoD. enable password Cisco244 Chapter 4 Cisco’s IOS and Security Device Manager29. If you wanted administrators to see a message when logging into the router, which command would you useA. message banner motdB. banner message motdC. banner motdD. message motd30. How many simultaneous Telnet sessions does a Cisco router support by defaultA. 1B. 2C. 3D. 4E. 5F. 631. What command do you type to save the configuration stored in RAM to NVRAMA. Router(config)#copy current to startingB. Router#copy starting to runningC. Router(config)#copy running-config startup-configD. Router#copy run startup32. You try to telnet into SFRouter from router Corp and receive this message:Corp#telnet SFRouterTrying SFRouter (10.0.0.1)…OpenPassword required, but none set[Connection to SFRouter closed by foreign host]Corp#Which of the following sequences will address this problem correctlyA. Corp(config)#line console 0B. SFRemote(config)#line console 0C. Corp(config)#line vty 0 4D. SFRemote(config)#line vty 0 433. Which command will delete the contents of NVRAM on a routerA. delete NVRAMB. delete startup-configC. erase NVRAMD. erase startReview Questions 24534. What is the problem with an interface if you type show interface serial 0 and receive the following messageSerial0 is administratively down, line protocol is downA. The keepalives are different times.B. The administrator has the interface shut down.C. The administrator is pinging from the interface.D. No cable is attached.35. Which of the following commands displays the configurable parameters and statistics of all interfaces on a routerA. show running-configB. show startup-configC. show interfacesD. show versions36. If you delete the contents of NVRAM and reboot the router, what mode will you be inA. Privileged modeB. Global modeC. Setup modeD. NVRAM loaded mode37. You type the following command into the router and receive the following output: Router#show serial 0/0^% Invalid input detected at ‘^’marker.Why was this error message displayedA. You need to be in privileged mode.B. You cannot have a space between serial and 0/0.C. The router does not have a serial0/0 interface.D. Part of the command is missing.38. You type Router#sh ru and receive an % ambiguous command error. Why did you receivethis messageA. The command requires additional options or parameters.B. There is more than one show command that starts with the letters ru.C. There is no show command that starts with ru.D. The command is being executed from the wrong router mode.246 Chapter 4 Cisco’s IOS and Security Device Manager39. Which of the following commands will display the current IP addressing and the layer 1 and2 status of an interface (Choose three.)A. show versionB. show protocolsC. show interfacesD. show controllersE. show ip interfaceF. show running-config40. What layer of the OSI model would you assume the problem is in if you type show interface serial 1 and receive the following messageSerial1 is down, line protocol is downA. Physical layerB. Data Link layerC. Network layerD. None; it is a router problem.41. What does the command o/r 0x2142 provideA. It is used to restart the router.B. It is used to bypass the configuration in NVRAM.C. It is used to enter ROM Monitor mode.D. It is used to view the lost password.42. Which command will copy the IOS to a backup host on your networkA. transfer IOS to copy run startC. copy tftp flashD. copy start tftpE. copy flash tftp43. You are troubleshooting a connectivity problem in your corporate network and want to isolate the problem. You suspect that a router on the route to an unreachable network is at fault.What IOS user exec command should you issueA. Router>pingB. Router>traceC. Router>show ip routeD. Router>show interfaceE. Router>show cdp neighbors44. You copy a configuration from a network host to a router’s RAM. The configuration looks correct, yet it is not working at all. What could the problem beA. You copied the wrong configuration into RAM.B. You copied the configuration into flash memory instead.C. The copy did not override the shutdown command in running-config.D. The IOS became corrupted after the copy command was initiated.45. A network administrator wants to upgrade the IOS of a router without removing the image currently installed. What command will display the amount of memory consumed by the currentIOS image and indicate whether there is enough room available to hold both the currentand new imagesA. show versionB. show flashC. show memoryD. show buffersE. show running-config46. The corporate office sends you a new router to connect, but upon connecting the console cable,you see that there is already a configuration on the router. What should be done before a new configuration is entered in the routerA. RAM should be erased and the router restarted.B. Flash should be erased and the router restarted.C. NVRAM should be erased and the router restarted.D. The new configuration should be entered and saved.47. Which command loads a new version of the Cisco IOS into a routerA. copy flash ftpB. copy ftp flashC. copy flash tftpD. copy tftp flash48. Which command will show you the IOS version running on your routerA. sh IOSB. sh flashC. sh versionD. sh running-config49. What should the configuration register value be after you successfully complete the password recovery procedure and return the router to normal operationA. 0x2100B. 0x2101C. 0x2102D. 0x214250. You save the configuration on a router with the copy running-config startup-configcommand and reboot the router. The router, however, comes up with a blank configuration.What can the problem beA. You didn’t boot the router with the correct command.B. NVRAM is corrupted.C. The configuration register setting is incorrect.D. The newly upgraded IOS is not compatible with the hardware of the router.E. The configuration you save is not compatible with the hardware.51. If you want to have more than one Telnet session open at the same time, what keystroke combination would you useA. Tab+spacebarB. Ctrl+X, then 6C. Ctrl+Shift+X, then 6D. Ctrl+Shift+6, then X52. You are unsuccessful in telnetting into a remote device. What could the problem be (Choose two.)A. IP addresses are incorrect.B. Access control list is filtering Telnet.C. There is a defective serial cable.D. The VTY password is missing.53. What information is displayed by the show hosts command (Choose two.)A. Temporary DNS entriesB. The names of the routers created using the hostname commandC. The IP addresses of workstations allowed to access the routerD. Permanent name-to-address mappings created using the ip host commandE. The length of time a host has been connected to the router via Telnet54. Which three commands can be used to check LAN connectivity problems on a router(Choose three.)A. show interfacesB. show ip routeC. tracertD. pingE. dns lookups55. You telnet to a router and make your necessary changes; now you want to end the Telnet session. What command do you type inA. closeB. disableC. disconnectD. exit56. You telnet into a remote device and type debug ip rip, but no output from the debug command is seen. What could the problem beA. You must type the show ip rip command first.B. IP addressing on the network is incorrect.C. You must use the terminal monitor command.D. Debug output is sent only to the console.57. Which command displays the configuration register settingA. show ip routeB. show boot versionC. show versionD. show flash58. You need to gather the IP address of a remote switch that is located in Hawaii. What can youdo to find the addressA. Fly to Hawaii, console into the switch, then relax and have a drink with an umbrella in it.B. Issue the show ip route command on the router connected to the switch.C. Issue the show cdp neighbor command on the router connected to the switch.D. Issue the show ip arp command on the router connected to the switch.E. Issue the show cdp neighbors detail command on the router connected to the switch.59. You have your laptop directly connected into a router’s Ethernet port. Which of the following are among the requirements for the copy flash tftp command to be successful (Choose three.)A. TFTP server software must be running on the router.B. TFTP server software must be running on your laptop.C. The Ethernet cable connecting the laptop directly into the router’s Ethernet port mu st bea straight-through cable.D. The laptop must be on the same subnet as the router’s Ethernet interface.E. The copy flash tftp command must be supplied the IP address of the laptop.F. There must be enough room in the flash memory of the router to accommodate the file tobe copied.60. The configuration register setting of 0x2102 provides what function to a routerA. Tells the router to boot into ROM monitor modeB. Provides password recoveryC. Tells the router to look in NVRAM for the boot sequenceD. Boots the IOS from a TFTP serverE. Boots an IOS image stored in ROM61. A receiving host has failed to receive all of the segments that it should acknowledge. What can the host do to improve the reliability of this communication sessionA. Send a different source port number.B. Restart the virtual circuit.C. Decrease the sequence number.D. Decrease the window size.62. Which fields are contained within an IEEE Ethernet frame header (Choose two.)A. Source and destination MAC addressB. Source and destination network addressC. Source and destination MAC address and source and destination network addressD. FCS field63. Which layer 1 devices can be used to enlarge the area covered by a single LAN segment (Choose two.)A. SwitchB. NICC. HubD. RepeaterE. RJ45 transceiver64. Segmentation of a data stream happens at which layer of the OSI modelA. PhysicalB. Data LinkC. NetworkD. Transport65. Which of the following describe router functions (Choose four.)A. Packet switchingB. Collision preventionC. Packet filteringD. Broadcast domain enlargementE. Internetwork communicationF. Broadcast forwardingG. Path selection66. Routers operate at layer __. LAN switches operate at layer __. Ethernet hubs operate at layer __. Word processing operates at layer __.A. 3, 3, 1, 7B. 3, 2, 1, noneC. 3, 2, 1, 7D. 2, 3, 1, 7E. 3, 3, 2, none67. When data is encapsulated, which is the correct orderA. Data, frame, packet, segment, bitB. Segment, data, packet, frame, bitC. Data, segment, packet, frame, bitD. Data, segment, frame, packet, bit68. Why does the data communication industry use the layered OSI reference model (Choose two.)A. It divides the network communication process into smaller and simpler components, thus aiding component development, design, and troubleshooting.B. It enables equipment from different vendors to use the same electronic components, thus saving research and development funds.C. It supports the evolution of multiple competing standards and thus provides business opportunities for equipment manufacturers.D. It encourages industry standardization by defining what functions occur at each layer ofthe model.E. It provides a framework by which changes in functionality in one layer require changes inother layers.69. What are two purposes for segmentation with a bridgeA. To add more broadcast domainsB. To create more collision domainsC. To add more bandwidth for usersD. To allow more broadcasts for users70. Which of the following are unique characteristics of half-duplex Ethernet when compared tofull-duplex Ethernet (Choose two.)A. Half-duplex Ethernet operates in a shared collision domain.B. Half-duplex Ethernet operates in a private collision domain.C. Half-duplex Ethernet has higher effective throughput.D. Half-duplex Ethernet has lower effective throughput.E. Half-duplex Ethernet operates in a private broadcast domain.58 Chapter 1 Internetworking71. You want to implement a network medium that is not susceptible to EMI. Which type of cabling should you useA. Thicknet coaxB. Thinnet coaxC. Category 5 UTP cableD. Fiber-optic cable72. Acknowledgments, sequencing, and flow control are characteristics of which OSI layerA. Layer 2B. Layer 3C. Layer 4D. Layer 773. Which of the following are types of flow control (Choose all that apply.)A. BufferingB. Cut-throughC. WindowingD. Congestion avoidanceE. VLANs74. Which of the following types of connections can use full duplex (Choose three.)A. Hub to hubB. Switch to switchC. Host to hostD. Switch to hubE. Switch to host75. What is the purpose of flow controlA. To ensure that data is retransmitted if an acknowledgment is not receivedB. To reassemble segments in the correct order at the destination deviceC. To provide a means for the receiver to govern the amount of data sent by the senderD. To regulate the size of each segment76. Which three statements are true about the operation of a full-duplex Ethernet networkA. There are no collisions in full-duplex mode.B. A dedicated switch port is required for each full-duplex node.C. Ethernet hub ports are preconfigured for full-duplex mode.D. In a full-duplex environment, the host network card must check for the availability of the network media before transmitting.E. The host network card and the switch port must be capable of operating in full-duplex mode. Review Questions 5977. What type of RJ45 UTP cable is used between switchesA. Straight-throughB. Crossover cableC. Crossover with a CSU/DSUD. Crossover with a router in between the two switches78. How does a host on an Ethernet LAN know when to transmit after a collision has occurred (Choose two.)A. In a CSMA/CD collision domain, multiple stations can successfully transmit data simultaneously.B. In a CSMA/CD collision domain, stations must wait until the media is not in use before transmitting.C. You can improve the CSMA/CD network by adding more hubs.D. After a collision, the station that detected the collision has first priority to resend thelost data.E. After a collision, all stations run a random backoff algorithm. When the backoff delay period has expired, all stations have equal priority to transmit data.F. After a collision, all stations involved run an identical backoff algorithm and then synchronize with each other prior to transmitting data.79. What type of RJ45 UTP cable do you use to connect a PC’s COM port to a router or switch console portA. Straight-throughB. Crossover cableC. Crossover with a CSU/DSUD. Rolled80. You have the following binary number:What are the decimal and hexadecimal equivalentsA. 69/0x2102B. 183/B7C. 173/A6D. 83/0xC581. What are the decimal and hexadecimal equivalents of the binary number(Choose two.)A. 159B. 157C. 185D. 0x9DE. 0xD9F. 0x15982. Which of the following allows a router to respond to an ARP request that is intended for a remote hostA. Gateway DPB. Reverse ARP (RARP)C. Proxy ARPD. Inverse ARP (IARP)E. Address Resolution Protocol (ARP)83. You want to implement a mechanism that automates the IP configuration, including IP address, subnet mask, default gateway, and DNS information. Which protocol will you useto accomplish thisA. SMTPB. SNMPC. DHCPD. ARP84. What protocol is used to find the hardware address of a local deviceA. RARPB. ARPC. IPD. ICMPE. BootP85. Which of the following are layers in the TCP/IP model (Choose three.)A. ApplicationB. SessionC. TransportD. InternetE. Data LinkF. Physical86. Which class of IP address provides a maximum of only 254 host addresses per network IDA. Class AB. Class BC. Class CD. Class DE. Class E87. Which of the following describe the DHCP Discover message (Choose two.)A. It uses FF:FF:FF:FF:FF:FF as a layer 2 broadcast.B. It uses UDP as the Transport layer protocol.C. It uses TCP as the Transport layer protocol.D. It does not use a layer 2 destination address.8. Which layer 4 protocol is used for a Telnet connectionA. IPB. TCPC. TCP/IPD. UDPE. ICMP89. Which statements are true regarding ICMP packets (Choose two.)A. They acknowledge receipt of a TCP segment.B. They guarantee datagram delivery.C. They can provide hosts with information about network problems.D. They are encapsulated within IP datagrams.E. They are encapsulated within UDP datagrams.90. Which of the following services use TCP (Choose three.)A. DHCPB. SMTPC. SNMPD. FTPE. HTTPF. TFTP91. Which of the following services use UDP (Choose three.)A. DHCPB. SMTPC. SNMPD. FTPE. HTTPF. TFTP92. Which of the following are TCP/IP protocols used at the Application layer of the OSI model (Choose three.)A. IPB. TCPC. TelnetD. FTPE. TFTP93. The following illustration shows a data structure header. What protocol is this header fromA. IPB. ICMPC. TCPD. UDPE. ARPF. RARP94. If you use either Telnet or FTP, which is the highest layer you are using to transmit dataA. ApplicationB. PresentationC. SessionD. Transport95. The DoD model (also called the TCP/IP stack) has four layers. Which layer of the DoD model is equivalent to the Network layer of the OSI modelA. ApplicationB. Host-to-HostC. InternetD. Network Access96. Which two of the following are private IP addressesA. 12.0.0.1B. What layer in the TCP/IP stack is equivalent to the Transport layer of the OSI model A. ApplicationB. Host-to-HostC. InternetD. Network Access98. Which statements are true regarding ICMP packets (Choose two)A. ICMP guarantees datagram delivery.B. ICMP can provide hosts with information about network problems.C. ICMP is encapsulated within IP datagrams.D. ICMP is encapsulated within UDP datagrams.99. What is the address range of a Class B network address in binaryA. 01xxxxxxB. 0xxxxxxxC. 10xxxxxxD. 110xxxxx100. Which of the following protocols uses both TCP and UDPA. FTPB. SMTPC. TelnetD. DNS答题卡。
网络工程师CCNA证书考试题库

网络工程师CCNA证书考试题库网络工程师是当今社会上一种备受青睐的职业,具备CCNA证书是成为一名合格网络工程师的基本要求之一。
CCNA(Cisco Certified Network Associate)是思科公司提供的一种权威的网络证书,考试内容涵盖了网络基础知识、路由器和交换机配置、网络安全等方面的内容。
下面将为大家整理一份网络工程师CCNA证书考试题库,供大家参考和复习。
一、网络基础知识1. OSI参考模型中,哪一层负责确定数据如何在网络中传输?A. 应用层B. 传输层C. 网络层D. 数据链路层2. IP地址的子网掩码用来做什么?A. 区分网络地址和主机地址B. 确定网络的物理拓扑C. 控制网络访问权限D. 提高网络安全性3. TCP协议是一种什么类型的协议?A. 面向连接型B. 面向无连接型C. 面向消息型D. 面向数据流型4. 下面哪种传输介质是最适合用于在大楼内部连接不同楼层的网络设备?A. 双绞线B. 同轴电缆C. 光纤D. 无线电波二、路由器和交换机配置1. 在路由器上配置静态路由需要设置哪些参数?A. 出接口B. 下一跳地址C. 网关地址D. 子网掩码2. 交换机的VLAN技术主要用来实现什么功能?A. 提高网络传输速度B. 划分不同的广播域C. 增加网络安全性D. 实现无线网络连接3. 在路由器上配置NAT技术的目的是什么?A. 增加网络带宽B. 实现内网主机与外网通信C. 提高网络可靠性D. 实现跨平台数据传输4. 交换机端口默认是属于哪个VLAN?A. VLAN1B. VLAN10C. VLAN100D. VLAN1000三、网络安全1. 以下哪种加密算法用于保护传输过程中的数据机密性?A. DESB. MD5C. RSAD. SHA2. 防火墙的作用是什么?A. 限制网络带宽的使用B. 监控网络流量C. 阻止非法入侵D. 加快网络数据传输速度3. 在网络安全方面,ACL(访问控制列表)主要用来控制什么?A. 网络拓扑B. 主机访问权限C. 广播域D. 数据传输速度4. DDos攻击是指什么?A. 拒绝服务攻击B. 数据泄露攻击C. 蠕虫攻击D. 恶意代码攻击通过以上网络工程师CCNA证书考试题库的复习,相信大家可以更加全面地了解CCNA考试的内容要求,提升自己的备考水平。
ccna考试题库最新版
ccna考试题库最新版CCNA(Cisco Certified Network Associate)认证是全球范围内最受欢迎的网络工程师认证之一,具备CCNA认证可以证明一个人在建立、规划、运行、安装和配置中等规模的局域网和广域网方面的专业知识。
为了帮助广大考生顺利通过CCNA考试,不断更新的CCNA考试题库至关重要。
以下是最新版本的CCNA考试题库,希望对考生们有所帮助。
第一部分:网络基础知识1. 什么是OSI七层模型?简要介绍每一层的功能。
2. TCP和UDP之间有哪些区别?请分别举例说明。
3. 什么是IP地址?IP地址的类型有哪些?请列举并简要介绍各自的特点。
4. 什么是子网掩码?为什么在网络中使用子网掩码?5. 简述常见的网络设备有哪些,以及各自的功能与作用。
第二部分:路由和交换技术1. 路由器和交换机之间有何区别?请进行比较并指出各自的优势和劣势。
2. 什么是VLAN?VLAN的作用及在网络中的应用场景是什么?3. OSPF和EIGRP是两种常见的路由协议,请比较它们的特点并举例说明。
4. 请解释静态路由和动态路由的概念以及在网络中的应用。
5. 交换机在网络中扮演什么角色?交换机的MAC地址表是如何工作的?第三部分:网络安全和管理1. 网络安全的重要性是什么?请列举几种常见的网络安全威胁并介绍应对策略。
2. 什么是ACL(访问控制列表)?ACL的作用是什么?请给出一个ACL的配置示例。
3. VPN是什么?VPN的工作原理及在企业网络中的应用。
4. SNMP是网络管理中常用的协议,它的作用是什么?请解释SNMP中的几个重要概念。
5. 如何保护无线网络的安全?请列举几种方法。
第四部分:WAN技术1. 什么是WAN?WAN的主要特点是什么?2. PPP协议和HDLC协议分别是什么?请比较它们的异同。
3. 什么是Frame Relay?Frame Relay的工作原理及在WAN中的应用。
4. 请解释T1和E1的概念,以及它们在传输速率和应用方面的差异。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
CCNA(1)适用班级:CCNA注意事项:1.在试卷的标封处填写姓名和班级2.考试时间共120分钟3.答案写在答题卡上1. What is the maximum number of IP addresses that can be assigned to hosts on a local subnetthat uses the subnet maskA. 14B. 15C. 16D. 30E. 31F. 622. You have a network that needs 29 subnets while maximizing the number of host addressesavailable on each subnet. How many bits must you borrow from the host field to provide thecorrect subnet maskA. 2B. 3C. 4D. 5E. 6F. 73. What is the subnetwork address for a host with the IP address The network address of provides how many subnets and hostsA. 7 subnets, 30 hosts eachB. 7 subnets, 2,046 hosts eachC. 7 subnets, 8,190 hosts eachD. 8 subnets, 30 hosts eachE. 8 subnets, 2,046 hosts eachF. 8 subnets, 8,190 hosts each5. Which two statements describe the IP address 10.16.3.65/23 (Choose two.)A. The subnet address is 10.16.3.0 The lowest host address in the subnet is 10.16.2.1 The last valid host address in the subnet is 10.16.2.254 The broadcast address of the subnet is 10.16.3.255 The network is not subnetted.6. If a host on a network has the address what is the subnetwork this hostbelongs toA. On a VLSM network, which mask should you use on point-to-point WAN links in order toreduce the waste of IP addressesA. /27B. /28C. /29D. /30E. /318. What is the subnetwork number of a host with an IP address of You have an interface on a router with the IP address of Including the routerinterface, how many hosts can have IP addresses on the LAN attached to the router interfaceA. 6B. 8C. 30D. 62E. 12610. You need to configure a server that is on the subnet The router has the firstavailable host address. Which of the following should you assign to the serverA. You have an interface on a router with the IP address of What is thebroadcast address the hosts will use on this LANA. You need to subnet a network that has 5 subnets, each with at least 16 hosts. Which classfulsubnet mask would you useA. A network administrator is connecting hosts A and B directly through their Ethernet interfaces,as shown in the illustration. Ping attempts between the hosts are unsuccessful. What can bedone to provide connectivity between the hosts (Choose two.)A. A crossover cable should be used in place of the straight-through cable.B. A rollover cable should be used in place of the straight-through cable.C. The subnet masks should be set to A default gateway needs to be set on each host.E. The subnet masks should be set to Address: Address: Cable164 Chapter 3 Subnetting, VLSMs, and Troubleshooting TCP/IP14. If an Ethernet port on a router were assigned an IP address of what wouldbe the valid subnet address of this hostA. Using the following illustration, what would be the IP address of E0 if you were using theeighth subnet The network ID is and you need to use the last available IPaddress in the range. The zero subnet should not be considered valid for this question.A. Using the illustration from the previous question, what would be the IP address of S0 if you wereusing the first subnet The network ID is and you need to use the last availableIP address in the range. Again, the zero subnet should not be considered valid for this question.A. Which configuration command must be in effect to allow the use of 8 subnets if the Class C subnet mask is Router(config)#ip classlessB. Router(config)#ip version 6C. Router(config)#no ip classfulD. Router(config)#ip unnumberedE. Router(config)#ip subnet-zeroF. Router(config)#ip all-nets18. You have a network with a subnet of Which is the valid host addressA. Your router has the following IP address on Ethernet0: Which of the following can be valid host IDs on the LAN interface attached to the router (Choose two.)A. To test the IP stack on your local host, which IP address would you pingA. 1.0.0.127C. You type show running-config and get this output:[output cut]Line console 0Exec-timeout 1 44Password 7098C0BQRLogin[output cut]What do the two numbers following the exec-timeout command meanA. If no command has been typed in 44 seconds, the console connection will be closed.B. If no router activity has been detected in 1 hour and 44 minutes, the console will be locked out.C. If no commands have been typed in 1 minute and 44 seconds, the console connection willbe closed.D. If you’re connected to the router by a Telnet connection, input must be detected within 1 minute and 44 seconds or the connection will be closed.22. You need to find the broadcast address used on a LAN on your router. What command willyou type into the router from user mode to find the broadcast addressA. show running-configB. show startup-configC. show interfacesD. show protocols23. You want to totally reinitialize the router and replace the current running-config with the current startup-config. What command will you useA. replace run startB. copy run startC. copy start runD. reloadReview Questions 24324. Which command will show you whether a DTE or a DCE cable is plugged into serial 0A. sh int s0B. sh int serial 0C. show controllers s 0D. show serial 0 controllers25. What keystroke will terminate setup modeA. Ctrl+ZB. Ctrl+^C. Ctrl+CD. Ctrl+Shift+^26. You set the console password, but when you display the configuration, the password doesn’t show up; it looks like this:[output cut]Line console 0Exec-timeout 1 44Password 7098C0BQRLogin[output cut]What cause the password to be stored like thisA. encrypt passwordB. service password-encryptionC. service-password-encryptionD. exec-timeout 1 4427. Which of the following commands will configure all the default VTY ports on a routerA. Router#line vty 0 4B. Router(config)#line vty 0 4C. Router(config-if)#line console 0D. Router(config)#line vty all28. Which of the following commands sets the secret password to CiscoA. enable secret password CiscoB. enable secret ciscoC. enable secret CiscoD. enable password Cisco244 Chapter 4 Cisco’s IOS and Security Device Manager29. If you wanted administrators to see a message when logging into the router, which command would you useA. message banner motdB. banner message motdC. banner motdD. message motd30. How many simultaneous Telnet sessions does a Cisco router support by defaultA. 1B. 2C. 3D. 4E. 5F. 631. What command do you type to save the configuration stored in RAM to NVRAMA. Router(config)#copy current to startingB. Router#copy starting to runningC. Router(config)#copy running-config startup-configD. Router#copy run startup32. You try to telnet into SFRouter from router Corp and receive this message:Corp#telnet SFRouterTrying SFRouter (10.0.0.1)…OpenPassword required, but none set[Connection to SFRouter closed by foreign host]Corp#Which of the following sequences will address this problem correctlyA. Corp(config)#line console 0B. SFRemote(config)#line console 0C. Corp(config)#line vty 0 4D. SFRemote(config)#line vty 0 433. Which command will delete the contents of NVRAM on a routerA. delete NVRAMB. delete startup-configC. erase NVRAMD. erase startReview Questions 24534. What is the problem with an interface if you type show interface serial 0 and receive the following messageSerial0 is administratively down, line protocol is downA. The keepalives are different times.B. The administrator has the interface shut down.C. The administrator is pinging from the interface.D. No cable is attached.35. Which of the following commands displays the configurable parameters and statistics of all interfaces on a routerA. show running-configB. show startup-configC. show interfacesD. show versions36. If you delete the contents of NVRAM and reboot the router, what mode will you be inA. Privileged modeB. Global modeC. Setup modeD. NVRAM loaded mode37. You type the following command into the router and receive the following output: Router#show serial 0/0^% Invalid input detected at ‘^’marker.Why was this error message displayedA. You need to be in privileged mode.B. You cannot have a space between serial and 0/0.C. The router does not have a serial0/0 interface.D. Part of the command is missing.38. You type Router#sh ru and receive an % ambiguous command error. Why did you receivethis messageA. The command requires additional options or parameters.B. There is more than one show command that starts with the letters ru.C. There is no show command that starts with ru.D. The command is being executed from the wrong router mode.246 Chapter 4 Cisco’s IOS and Security Device Manager39. Which of the following commands will display the current IP addressing and the layer 1 and2 status of an interface (Choose three.)A. show versionB. show protocolsC. show interfacesD. show controllersE. show ip interfaceF. show running-config40. What layer of the OSI model would you assume the problem is in if you type show interface serial 1 and receive the following messageSerial1 is down, line protocol is downA. Physical layerB. Data Link layerC. Network layerD. None; it is a router problem.41. What does the command o/r 0x2142 provideA. It is used to restart the router.B. It is used to bypass the configuration in NVRAM.C. It is used to enter ROM Monitor mode.D. It is used to view the lost password.42. Which command will copy the IOS to a backup host on your networkA. transfer IOS to copy run startC. copy tftp flashD. copy start tftpE. copy flash tftp43. You are troubleshooting a connectivity problem in your corporate network and want to isolate the problem. You suspect that a router on the route to an unreachable network is at fault.What IOS user exec command should you issueA. Router>pingB. Router>traceC. Router>show ip routeD. Router>show interfaceE. Router>show cdp neighbors44. You copy a configuration from a network host to a router’s RAM. The configuration looks correct, yet it is not working at all. What could the problem beA. You copied the wrong configuration into RAM.B. You copied the configuration into flash memory instead.C. The copy did not override the shutdown command in running-config.D. The IOS became corrupted after the copy command was initiated.45. A network administrator wants to upgrade the IOS of a router without removing the image currently installed. What command will display the amount of memory consumed by the currentIOS image and indicate whether there is enough room available to hold both the currentand new imagesA. show versionB. show flashC. show memoryD. show buffersE. show running-config46. The corporate office sends you a new router to connect, but upon connecting the console cable,you see that there is already a configuration on the router. What should be done before a new configuration is entered in the routerA. RAM should be erased and the router restarted.B. Flash should be erased and the router restarted.C. NVRAM should be erased and the router restarted.D. The new configuration should be entered and saved.47. Which command loads a new version of the Cisco IOS into a routerA. copy flash ftpB. copy ftp flashC. copy flash tftpD. copy tftp flash48. Which command will show you the IOS version running on your routerA. sh IOSB. sh flashC. sh versionD. sh running-config49. What should the configuration register value be after you successfully complete the password recovery procedure and return the router to normal operationA. 0x2100B. 0x2101C. 0x2102D. 0x214250. You save the configuration on a router with the copy running-config startup-configcommand and reboot the router. The router, however, comes up with a blank configuration.What can the problem beA. You didn’t boot the router with the correct command.B. NVRAM is corrupted.C. The configuration register setting is incorrect.D. The newly upgraded IOS is not compatible with the hardware of the router.E. The configuration you save is not compatible with the hardware.51. If you want to have more than one Telnet session open at the same time, what keystroke combination would you useA. Tab+spacebarB. Ctrl+X, then 6C. Ctrl+Shift+X, then 6D. Ctrl+Shift+6, then X52. You are unsuccessful in telnetting into a remote device. What could the problem be (Choose two.)A. IP addresses are incorrect.B. Access control list is filtering Telnet.C. There is a defective serial cable.D. The VTY password is missing.53. What information is displayed by the show hosts command (Choose two.)A. Temporary DNS entriesB. The names of the routers created using the hostname commandC. The IP addresses of workstations allowed to access the routerD. Permanent name-to-address mappings created using the ip host commandE. The length of time a host has been connected to the router via Telnet54. Which three commands can be used to check LAN connectivity problems on a router(Choose three.)A. show interfacesB. show ip routeC. tracertD. pingE. dns lookups55. You telnet to a router and make your necessary changes; now you want to end the Telnet session. What command do you type inA. closeB. disableC. disconnectD. exit56. You telnet into a remote device and type debug ip rip, but no output from the debug command is seen. What could the problem beA. You must type the show ip rip command first.B. IP addressing on the network is incorrect.C. You must use the terminal monitor command.D. Debug output is sent only to the console.57. Which command displays the configuration register settingA. show ip routeB. show boot versionC. show versionD. show flash58. You need to gather the IP address of a remote switch that is located in Hawaii. What can youdo to find the addressA. Fly to Hawaii, console into the switch, then relax and have a drink with an umbrella in it.B. Issue the show ip route command on the router connected to the switch.C. Issue the show cdp neighbor command on the router connected to the switch.D. Issue the show ip arp command on the router connected to the switch.E. Issue the show cdp neighbors detail command on the router connected to the switch.59. You have your laptop directly connected into a router’s Ethernet port. Which of the following are among the requirements for the copy flash tftp command to be successful (Choose three.)A. TFTP server software must be running on the router.B. TFTP server software must be running on your laptop.C. The Ethernet cable connecting the laptop directly into the router’s Ethernet port mu st bea straight-through cable.D. The laptop must be on the same subnet as the router’s Ethernet interface.E. The copy flash tftp command must be supplied the IP address of the laptop.F. There must be enough room in the flash memory of the router to accommodate the file tobe copied.60. The configuration register setting of 0x2102 provides what function to a routerA. Tells the router to boot into ROM monitor modeB. Provides password recoveryC. Tells the router to look in NVRAM for the boot sequenceD. Boots the IOS from a TFTP serverE. Boots an IOS image stored in ROM61. A receiving host has failed to receive all of the segments that it should acknowledge. What can the host do to improve the reliability of this communication sessionA. Send a different source port number.B. Restart the virtual circuit.C. Decrease the sequence number.D. Decrease the window size.62. Which fields are contained within an IEEE Ethernet frame header (Choose two.)A. Source and destination MAC addressB. Source and destination network addressC. Source and destination MAC address and source and destination network addressD. FCS field63. Which layer 1 devices can be used to enlarge the area covered by a single LAN segment (Choose two.)A. SwitchB. NICC. HubD. RepeaterE. RJ45 transceiver64. Segmentation of a data stream happens at which layer of the OSI modelA. PhysicalB. Data LinkC. NetworkD. Transport65. Which of the following describe router functions (Choose four.)A. Packet switchingB. Collision preventionC. Packet filteringD. Broadcast domain enlargementE. Internetwork communicationF. Broadcast forwardingG. Path selection66. Routers operate at layer __. LAN switches operate at layer __. Ethernet hubs operate at layer __. Word processing operates at layer __.A. 3, 3, 1, 7B. 3, 2, 1, noneC. 3, 2, 1, 7D. 2, 3, 1, 7E. 3, 3, 2, none67. When data is encapsulated, which is the correct orderA. Data, frame, packet, segment, bitB. Segment, data, packet, frame, bitC. Data, segment, packet, frame, bitD. Data, segment, frame, packet, bit68. Why does the data communication industry use the layered OSI reference model (Choose two.)A. It divides the network communication process into smaller and simpler components, thus aiding component development, design, and troubleshooting.B. It enables equipment from different vendors to use the same electronic components, thus saving research and development funds.C. It supports the evolution of multiple competing standards and thus provides business opportunities for equipment manufacturers.D. It encourages industry standardization by defining what functions occur at each layer ofthe model.E. It provides a framework by which changes in functionality in one layer require changes inother layers.69. What are two purposes for segmentation with a bridgeA. To add more broadcast domainsB. To create more collision domainsC. To add more bandwidth for usersD. To allow more broadcasts for users70. Which of the following are unique characteristics of half-duplex Ethernet when compared tofull-duplex Ethernet (Choose two.)A. Half-duplex Ethernet operates in a shared collision domain.B. Half-duplex Ethernet operates in a private collision domain.C. Half-duplex Ethernet has higher effective throughput.D. Half-duplex Ethernet has lower effective throughput.E. Half-duplex Ethernet operates in a private broadcast domain.58 Chapter 1 Internetworking71. You want to implement a network medium that is not susceptible to EMI. Which type of cabling should you useA. Thicknet coaxB. Thinnet coaxC. Category 5 UTP cableD. Fiber-optic cable72. Acknowledgments, sequencing, and flow control are characteristics of which OSI layerA. Layer 2B. Layer 3C. Layer 4D. Layer 773. Which of the following are types of flow control (Choose all that apply.)A. BufferingB. Cut-throughC. WindowingD. Congestion avoidanceE. VLANs74. Which of the following types of connections can use full duplex (Choose three.)A. Hub to hubB. Switch to switchC. Host to hostD. Switch to hubE. Switch to host75. What is the purpose of flow controlA. To ensure that data is retransmitted if an acknowledgment is not receivedB. To reassemble segments in the correct order at the destination deviceC. To provide a means for the receiver to govern the amount of data sent by the senderD. To regulate the size of each segment76. Which three statements are true about the operation of a full-duplex Ethernet networkA. There are no collisions in full-duplex mode.B. A dedicated switch port is required for each full-duplex node.C. Ethernet hub ports are preconfigured for full-duplex mode.D. In a full-duplex environment, the host network card must check for the availability of the network media before transmitting.E. The host network card and the switch port must be capable of operating in full-duplex mode. Review Questions 5977. What type of RJ45 UTP cable is used between switchesA. Straight-throughB. Crossover cableC. Crossover with a CSU/DSUD. Crossover with a router in between the two switches78. How does a host on an Ethernet LAN know when to transmit after a collision has occurred (Choose two.)A. In a CSMA/CD collision domain, multiple stations can successfully transmit data simultaneously.B. In a CSMA/CD collision domain, stations must wait until the media is not in use before transmitting.C. You can improve the CSMA/CD network by adding more hubs.D. After a collision, the station that detected the collision has first priority to resend thelost data.E. After a collision, all stations run a random backoff algorithm. When the backoff delay period has expired, all stations have equal priority to transmit data.F. After a collision, all stations involved run an identical backoff algorithm and then synchronize with each other prior to transmitting data.79. What type of RJ45 UTP cable do you use to connect a PC’s COM port to a router or switch console portA. Straight-throughB. Crossover cableC. Crossover with a CSU/DSUD. Rolled80. You have the following binary number:What are the decimal and hexadecimal equivalentsA. 69/0x2102B. 183/B7C. 173/A6D. 83/0xC581. What are the decimal and hexadecimal equivalents of the binary number(Choose two.)A. 159B. 157C. 185D. 0x9DE. 0xD9F. 0x15982. Which of the following allows a router to respond to an ARP request that is intended for a remote hostA. Gateway DPB. Reverse ARP (RARP)C. Proxy ARPD. Inverse ARP (IARP)E. Address Resolution Protocol (ARP)83. You want to implement a mechanism that automates the IP configuration, including IP address, subnet mask, default gateway, and DNS information. Which protocol will you useto accomplish thisA. SMTPB. SNMPC. DHCPD. ARP84. What protocol is used to find the hardware address of a local deviceA. RARPB. ARPC. IPD. ICMPE. BootP85. Which of the following are layers in the TCP/IP model (Choose three.)A. ApplicationB. SessionC. TransportD. InternetE. Data LinkF. Physical86. Which class of IP address provides a maximum of only 254 host addresses per network IDA. Class AB. Class BC. Class CD. Class DE. Class E87. Which of the following describe the DHCP Discover message (Choose two.)A. It uses FF:FF:FF:FF:FF:FF as a layer 2 broadcast.B. It uses UDP as the Transport layer protocol.C. It uses TCP as the Transport layer protocol.D. It does not use a layer 2 destination address.8. Which layer 4 protocol is used for a Telnet connectionA. IPB. TCPC. TCP/IPD. UDPE. ICMP89. Which statements are true regarding ICMP packets (Choose two.)A. They acknowledge receipt of a TCP segment.B. They guarantee datagram delivery.C. They can provide hosts with information about network problems.D. They are encapsulated within IP datagrams.E. They are encapsulated within UDP datagrams.90. Which of the following services use TCP (Choose three.)A. DHCPB. SMTPC. SNMPD. FTPE. HTTPF. TFTP91. Which of the following services use UDP (Choose three.)A. DHCPB. SMTPC. SNMPD. FTPE. HTTPF. TFTP92. Which of the following are TCP/IP protocols used at the Application layer of the OSI model (Choose three.)A. IPB. TCPC. TelnetD. FTPE. TFTP93. The following illustration shows a data structure header. What protocol is this header fromA. IPB. ICMPC. TCPD. UDPE. ARPF. RARP94. If you use either Telnet or FTP, which is the highest layer you are using to transmit dataA. ApplicationB. PresentationC. SessionD. Transport95. The DoD model (also called the TCP/IP stack) has four layers. Which layer of the DoD model is equivalent to the Network layer of the OSI modelA. ApplicationB. Host-to-HostC. InternetD. Network Access96. Which two of the following are private IP addressesA. 12.0.0.1B. What layer in the TCP/IP stack is equivalent to the Transport layer of the OSI model A. ApplicationB. Host-to-HostC. InternetD. Network Access98. Which statements are true regarding ICMP packets (Choose two)A. ICMP guarantees datagram delivery.B. ICMP can provide hosts with information about network problems.C. ICMP is encapsulated within IP datagrams.D. ICMP is encapsulated within UDP datagrams.99. What is the address range of a Class B network address in binaryA. 01xxxxxxB. 0xxxxxxxC. 10xxxxxxD. 110xxxxx100. Which of the following protocols uses both TCP and UDPA. FTPB. SMTPC. TelnetD. DNS答题卡。
