Cisco ASA5545-k8透明模式案例
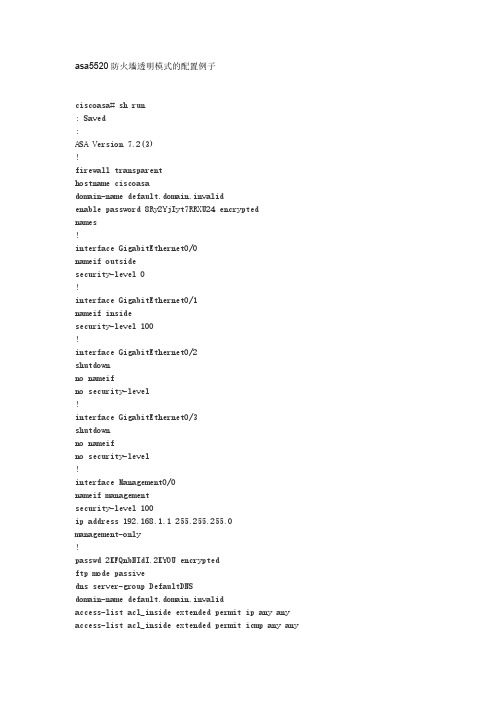
asa5520防火墙透明模式的配置例子

asa5520防火墙透明模式的配置例子ciscoasa# sh run: Saved:ASA Version 7.2(3)!firewall transparenthostname ciscoasadomain-name default.domain.invalidenable password 8Ry2YjIyt7RRXU24 encryptednames!interface GigabitEthernet0/0nameif outsidesecurity-level 0!interface GigabitEthernet0/1nameif insidesecurity-level 100!interface GigabitEthernet0/2shutdownno nameifno security-level!interface GigabitEthernet0/3shutdownno nameifno security-level!interface Management0/0nameif managementsecurity-level 100ip address 192.168.1.1 255.255.255.0management-only!passwd 2KFQnbNIdI.2KYOU encryptedftp mode passivedns server-group DefaultDNSdomain-name default.domain.invalidaccess-list acl_inside extended permit ip any any access-list acl_inside extended permit icmp any anyaccess-list acl_outside extended permit tcp any any eq 3306access-list acl_outside extended permit tcp any any eq wwwaccess-list acl_outside extended permit tcp any any eq 8080access-list acl_outside extended permit tcp any any eq httpsaccess-list acl_outside extended permit tcp any any eq sqlnetaccess-list acl_outside extended permit tcp any any eq ftpaccess-list acl_outside extended permit tcp any any eq 1433access-list acl_outside extended permit esp any anyaccess-list acl_outside extended permit udp any any eq isakmpaccess-list acl_outside extended permit tcp any any eq pop3access-list acl_outside extended permit tcp any any eq smtpaccess-list acl_outside extended permit icmp any anypager lines 24mtu outside 1500mtu inside 1500mtu management 1500ip address 172.16.177.208 255.255.255.0no failovericmp unreachable rate-limit 1 burst-size 1asdm image disk0:/ASDM-523.BINno asdm history enablearp timeout 14400access-group acl_outside in interface outsideaccess-group acl_inside in interface insidetimeout xlate 3:00:00timeout conn 0:20:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout uauth 0:05:00 absolutehttp server enablehttp 192.168.1.0 255.255.255.0 managementhttp 0.0.0.0 0.0.0.0 insideno snmp-server locationno snmp-server contactsnmp-server enable traps snmp authentication linkup linkdown coldstarttelnet timeout 5ssh timeout 5console timeout 0!class-map inspection_defaultmatch default-inspection-traffic!!policy-map type inspect dns preset_dns_mapparametersmessage-length maximum 512policy-map global_policyclass inspection_defaultinspect dns preset_dns_mapinspect ftpinspect h323 h225inspect h323 rasinspect rshinspect rtspinspect esmtpinspect sqlnetinspect skinnyinspect sunrpcinspect xdmcpinspect sipinspect netbiosinspect tftpinspect pptp!service-policy global_policy globalusername cisco password 3USUcOPFUiMCO4Jk encryptedprompt hostname contextCryptochecksum:4682fd668f251c28d32a0cb82a3ac5f3: endciscoasa#注意点:语句ip address 172.16.177.208 255.255.255.0是在interface GigabitEthernet0/0下配的,自己跑到外面来了,如果不配这个,好像ping不通。
Cisco ASA5505防火墙详细配置教程及实际配置案例
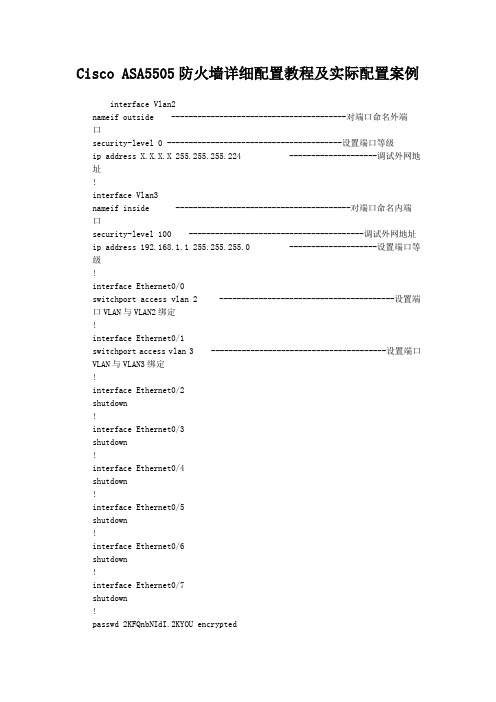
Cisco ASA5505防火墙详细配置教程及实际配置案例interface Vlan2nameif outside ----------------------------------------对端口命名外端口security-level 0 ----------------------------------------设置端口等级ip address X.X.X.X 255.255.255.224 --------------------调试外网地址!interface Vlan3nameif inside ----------------------------------------对端口命名内端口security-level 100 ----------------------------------------调试外网地址ip address 192.168.1.1 255.255.255.0 --------------------设置端口等级!interface Ethernet0/0switchport access vlan 2 ----------------------------------------设置端口VLAN与VLAN2绑定!interface Ethernet0/1switchport access vlan 3 ----------------------------------------设置端口VLAN与VLAN3绑定!interface Ethernet0/2shutdown!interface Ethernet0/3shutdown!interface Ethernet0/4shutdown!interface Ethernet0/5shutdown!interface Ethernet0/6shutdown!interface Ethernet0/7shutdown!passwd 2KFQnbNIdI.2KYOU encryptedftp mode passivedns domain-lookup insidedns server-group DefaultDNSname-server 211.99.129.210name-server 202.106.196.115access-list 102 extended permit icmp any any ------------------设置ACL列表(允许ICMP全部通过)access-list 102 extended permit ip anyany ------------------设置ACL列表(允许所有IP全部通过)pager lines 24mtu outside 1500mtu inside 1500icmp unreachable rate-limit 1 burst-size 1no asdm history enablearp timeout 14400global (outside) 1 interface ----------------------------------------设置NAT地址映射到外网口nat (inside) 1 0.0.0.0 0.0.0.0 0---------------------------------NAT地址池(所有地址)0无最大会话数限制access-group 102 in interface outside ------------------―――设置ACL列表绑定到外端口route outside 0.0.0.0 0.0.0.0 x.x.x.x 1 ------------------设置到外网的默认路由timeout xlate 3:00:00timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout uauth 0:05:00 absoluteno snmp-server locationno snmp-server contactsnmp-server enable traps snmp authentication linkup linkdown coldstart telnet 0.0.0.0 0.0.0.0 inside ----------------------------------------设置TELNET所有地址进入telnet timeout 5ssh 0.0.0.0 0.0.0.0 outside ----------------------------------------设置SSH所有地址进入ssh timeout 30ssh version 2console timeout 0!dhcpd address 192.168.1.100-192.168.1.199inside ------------------设置DHCP服务器地址池dhcpd dns 211.99.129.210 202.106.196.115 interfaceinside ------------------设置DNS服务器到内网端口dhcpd enableinside --------------------------------------------------------------设置DHCP应用到内网端口!前几天去客户那调试CISCO-ASA-5505设备,第一次摸,跟PIX一样,呵呵.没有技术含量,都是最基本的.其他业务配置暂时没配,会及时更新的.Cisco ASA5505配置cisco, config, telnet, 防火墙, Cisco1.配置防火墙名ciscoasa> enableciscoasa# configure terminalciscoasa(config)# hostname asa55052.配置telnetasa5505(config)#telnet 192.168.1.0 255.255.255.0 inside ↑//允许内部接口192.168.1.0网段telnet防火墙3.配置密码asa5505(config)# password cisco ------------------远程密码asa5505(config)# enable password cisco ------------------特权模式密码4.配置IPasa5505(config)# interface vlan 2 ------------------进入vlan2asa5505(config-if)# ip address 218.16.37.222 255.255.255.192 ------------------vlan2配置IPasa5505(config)#show ip address vlan2 ------------------验证配置5.端口加入vlanasa5505(config)# interface e0/3 ------------------进入接口e0/3asa5505(config-if)# switchport access vlan 3 ------------------接口e0/3加入vlan3asa5505(config)# interface vlan 3 ------------------进入vlan3asa5505(config-if)# ip address 10.10.10.36 255.255.255.224 ------------------vlan3配置IPasa5505(config-if)# nameif dmz ------------------vlan3名asa5505(config-if)# no shutdown ------------------开启asa5505(config-if)# show switch vlan ------------------验证配置6.最大传输单元MTUasa5505(config)#mtu inside 1500 ------------------inside最大传输单元1500字节asa5505(config)#mtu outside 1500 ------------------outside最大传输单元1500字节asa5505(config)#mtu dmz 1500 ------------------dmz最大传输单元1500字节7.配置arp表的超时时间asa5505(config)#arp timeout 14400 ------------------arp表的超时时间14400秒8.FTP模式asa5505(config)#ftp mode passive ------------------FTP被动模式9.配置域名asa5505(config)#domain-name 10.启动日志asa5505(config)#logging enable ------------------启动日志asa5505(config)#logging asdm informational ------------------启动asdm报告日志asa5505(config)#Show logging ------------------验证配置11.启用http服务asa5505(config)#http server enable ------------------启动HTTP server,便于ASDM连接。
cisco防火墙透明模式是怎么样的
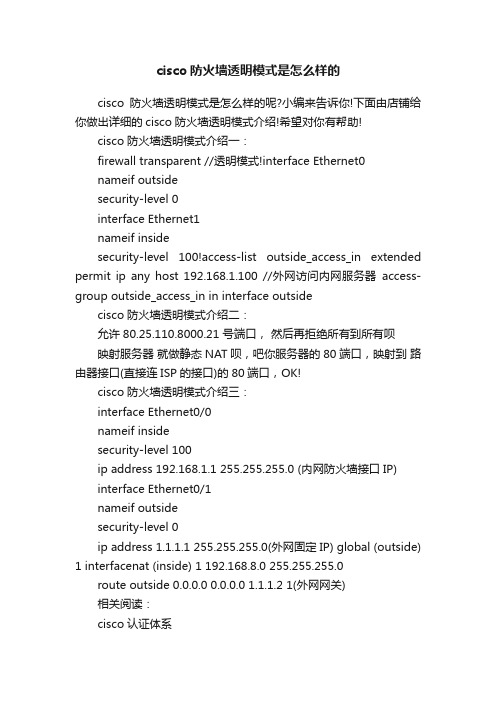
cisco防火墙透明模式是怎么样的cisco防火墙透明模式是怎么样的呢?小编来告诉你!下面由店铺给你做出详细的cisco防火墙透明模式介绍!希望对你有帮助!cisco防火墙透明模式介绍一:firewall transparent //透明模式!interface Ethernet0nameif outsidesecurity-level 0interface Ethernet1nameif insidesecurity-level 100!access-list outside_access_in extended permit ip any host 192.168.1.100 //外网访问内网服务器access-group outside_access_in in interface outsidecisco防火墙透明模式介绍二:允许80.25.110.8000.21 号端口,然后再拒绝所有到所有呗映射服务器就做静态NAT呗,吧你服务器的80端口,映射到路由器接口(直接连ISP的接口)的80端口,OK!cisco防火墙透明模式介绍三:interface Ethernet0/0nameif insidesecurity-level 100ip address 192.168.1.1 255.255.255.0 (内网防火墙接口IP)interface Ethernet0/1nameif outsidesecurity-level 0ip address 1.1.1.1 255.255.255.0(外网固定IP) global (outside) 1 interfacenat (inside) 1 192.168.8.0 255.255.255.0route outside 0.0.0.0 0.0.0.0 1.1.1.2 1(外网网关)相关阅读:cisco认证体系CCA思科认证构架师(Cisco Certified Architect ,CCA)CCIE思科认证网络专家(Cisco Certified Internetwork Expert) CCDE思科网络设计专家级别(Cisco Certified Design Expert)CCNP思科认证资深网络工程师(Cisco Certified Network Professional)CCDP思科认证资深设计工程师(Cisco Certified Design Professional)CCIP思科认证资深互联网工程师(Cisco Certified Internetwork Professional)CCSP思科认证资深安全工程师(Cisco Certified Security Professional)CCVP思科认证资深语音工程师(Cisco Certified Voice Professional)CCNA思科认证网络工程师(Cisco Certified Network Associate) CCDA思科认证设计工程师(Cisco Certified Design Associate)。
CiscoASA防火墙详细图文配置实例
Cisco ASA 防火墙图文配置实例本文是基于ASA5540 和ASA5520 的配置截图所做的一篇配置文档,从最初始的配置开始:1、连接防火墙登陆与其他的Cisco 设备一样,用Console 线连接到防火墙,初始特权密码为空。
2、配置内部接口和IP 地址进入到接口配置模式,配置接口的IP 地址,并指定为inside。
防火墙的地址配置好后,进行测试,确认可以和防火墙通讯。
3、用dir 命令查看当前的Image 文件版本。
4、更新Image 文件。
准备好TFTP 服务器和新的Image 文件,开始更新。
5、更新ASDM。
6、更新完成后,再用dir 命令查看8、存盘,重启9、用sh version 命令验证启动文件,可以发现当前的Image 文件就是更新后的10、设置允许用图形界面来管理ASA 防火墙表示内部接口的任意地址都可以通过http 的方式来管理防火墙。
11、打开浏览器,在地址栏输入防火墙内部接口的IP 地址选择“是”按钮。
12、出现安装ASDM 的画面选择“Install ASDM Launcher and Run ASDM”按钮,开始安装过程。
13、安装完成后会在程序菜单中添加一个程序组14、运行ASDM Launcher,出现登陆画面15、验证证书单击“是”按钮后,开始登陆过程16、登陆进去后,出现防火墙的配置画面,就可以在图形界面下完成ASA 防火墙的配置17、选择工具栏的“Configuration”按钮18、选择“Interface”,对防火墙的接口进行配置,这里配置g0/3接口选择g0/3 接口,并单击右边的“Edit”按钮19、配置接口的IP 地址,并将该接口指定为outside单击OK 后,弹出“Security Level Change”对话框,单击OK 20、编辑g0/1 接口,并定义为DMZ 区域21、接口配置完成后,要单击apply 按钮,以应用刚才的改变,这一步一定不能忘22、设置静态路由单击Routing->Static Route->Add23、设置enable 密码24、允许ssh 方式登录防火墙25、增加用户定义ssh 用本地数据库验证26、用ssh 登录测试登录成功27、建立动态NAT 转换选择Add Dynamic NAT RuleInterface 选择inside,Source 处输入any 单击Manage 按钮单击add,增加一个地址池Interface 选择Outside,选择PAT,单击Add 按钮单击OK完成了添加动态NAT 转换28、静态NAT 转换由于笔者2009 年离开了原单位,有些配置的截图没有做,新单位又没有ASA 防火墙,只好参考《ASA8.0/ASDM6.0 测试报告》的截图和文档来完成本文,并将该文档中部分常用的配置联接在本文后,对该文的作者表示感谢。
实验四 cisco思科asa 5505 从内网访问DMZ服务器(真实防火墙)

实验四 ASA 5505 从内网访问DMZ区服务器(真实防火墙)一、实验目标在这个实验中朋友你将要完成下列任务:1.创建vlan2.给vlan命名3.给vlan分配IP4.把接口加入到相应的VLAN,并配置接口的速率、双工(半工)5.配置内部转化地址池(nat)外部转换地址globla6.配置WWW和FTP服务器二、实验拓扑------------------------------------------------------------------------------------------------------------------------三、实验过程1. ASA 5505基本配置:ciscoasa>ciscoasa> enablePassword:ciscoasa#ciscoasa# configure terminalciscoasa(config)# interface vlan44 *建立ID为44的虚拟局域网(vlan)ciscoasa(config-if)# nameif dmz *把vlan44的接口名称配置为dmzciscoasa(config-if)# security-level 50 *配置dmz 安全级别为50ciscoasa(config-if)# ip address 11.0.0.1 255.0.0.0 *给vlan44配置IP地址ciscoasa(config-if)# interface vlan33 *建立ID为33的虚拟局域网(vlan)ciscoasa(config-if)# nameif inside *把vla33的接口名称配置为inside,并指定安全级别,安全级别取值范围为1~100,数字越大安全级别越高。
在默认情况下,inside安全级别为100。
INFO: Security level for "inside" set to 100 by default.ciscoasa(config-if)# ip address 192.168.0.211 255.255.255.0 *给vlan33配置IP地址ciscoasa(config-if)# exitciscoasa(config)# interface ethernet0/2 *进入e0/2接口的配置模式ciscoasa(config-if)# switchport access vlan 44 *把e0/2接口划分到vlan22中ciscoasa(config-if)# speed auto *设置e0/2接口的速率为自动协商ciscoasa(config-if)# duplex auto *设置e0/2接口的工作模式为自动协商ciscoasa(config-if)# no shutdown *打开e0/2接口ciscoasa(config-if)# interface e0/0 *进入e0/1接口的配置模式ciscoasa(config-if)# switchport access vlan 33 *把e0/0接口划分到vlan33中ciscoasa(config-if)# speed auto *设置e0/0接口的速率为自动协商ciscoasa(config-if)# duplex auto *设置e0/0接口的工作模式为自动协商ciscoasa(config-if)# no shutdown *打开e0/0接口ciscoasa(config-if)# exitciscoasa(config)#2. ASA 5505本身接口的连通性测试①测试防火墙本身vlan44接口连通性ciscoasa# ping 11.0.0.1Sending 5, 100-byte ICMP Echos to 11.0.0.1, timeout is 2 seconds:Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/1 ms②测试防火墙本身vlan33接口连通性ciscoasa# ping 192.168.0.211Type escape sequence to abort.Sending 5, 100-byte ICMP Echos to 192.168.0.211, timeout is 2 seconds:3. 配置PC:具体网络参数如拓扑图所示。
【免费下载】asa5520防火墙透明模式的配置例子
parameters message-length maximum 512 policy-map global_policy class inspection_default inspect dns preset_dns_map inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect esmtp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp inspect pptp ! service-policy global_policy global username cisco password 3USUcOPFUiMCO4Jk encrypted prompt hostname context Cryptochecksum:4682fd668f251c28d32a0cb82a3ac5f3 : end ciscoasa#
access-list acl_outside extended permit tcp any any eq 3306 access-list acl_outside extended permit tcp any any eq www access-list acl_outside extended permit tcp any any eq 8080 access-list acl_outside extended permit tcp any any eq https access-list acl_outside extended permit tcp any any eq sqlnet access-list acl_outside extended permit tcp any any eq ftp access-list acl_outside extended permit tcp any any eq 1433 access-list acl_outside extended permit esp any any access-list acl_outside extended permit udp any any eq isakmp access-list acl_outside extended permit tcp any any eq pop3 access-list acl_outside extended permit tcp any any eq smtp access-list acl_outside extended permit icmp any any pager lines 24 mtu outside 1500 mtu inside 1500 mtu management 1500 ip address 172.16.177.208 255.255.255.0 no failover icmp unreachable rate-limit 1 burst-size 1 asdm image disk0:/ASDM-523.BIN no asdm history enable arp timeout 14400 access-group acl_outside in interface outside access-group acl_inside in interface inside timeout xlate 3:00:00 timeout conn 0:20:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout uauth 0:05:00 absolute http server enable http 192.168.1.0 255.255.255.0 management http 0.0.0.0 0.0.0.0 inside no snmp-server location no snmp-server contact snmp-server enable traps snmp authentication linkup linkdown coldstart telnet timeout 5 ssh timeout 5 console timeout 0 ! class-map inspection_fault match default-inspection-traffic ! ! policy-map type inspect dns preset_dns_map
ASA透明模式防火墙技术介绍
ASA透明模式防火墙技术介绍首先,透明模式和其它模式的pk: 路由模式VS透明模式路由模式,防火墙扮演一个三层设备,基于目的IP地址转发数据包。
透明模式,防火墙扮演一个二层设备,如同桥或交换机,基于目的MAC地址转发以太网??桥模式VS透明模式需要注意的是,虽然透明模式防火墙首先,透明模式和其它模式的pk:路由模式VS透明模式路由模式,防火墙扮演一个三层设备,基于目的IP地址转发数据包。
透明模式,防火墙扮演一个二层设备,如同桥或交换机,基于目的MAC地址转发以太网帧。
桥模式VS透明模式需要注意的是,虽然透明模式防火墙工作在第二层,但是,它的工作方式并不完全与二层交换机或桥相同。
透明模式防火墙在处理流量时仍然与交换机有一些不同。
交换机三个主要功能1. 学习与每个端口匹配的MAC地址,并将它们存储在MAC地址表中(有时一叫做CAM表)。
智能地使用MAC地址表转发流量,但是会泛洪未知目的的单播、组播、广播地址。
3. 使用生成树协议(STP)来打破第二层环路,保证在源和目的之间只有一条活动路径存在。
像交换机一样,透明模式防火墙也会完成第一点:当一个帧进入一个接口,设备会比较帧中的源MAC地址,并且把它添加到MAC地址表中(如果MAC地址表中没有这个地址)。
防火墙同样使用MAC地址表,智能地基于帧的目的MAC地址进行转发;但是,防火墙不会泛洪MAC地址表不存在的未知的目的单播MAC地址。
防火墙假设,如果设备使用TCP/IP,可以通过ARP进程来发现与三层IP地址相匹配的目的MAC地址。
如果一台设备打破了这个预期(准则),并且使用了一个防火墙没有学到(动态或静态)的MAC地址,防火墙将丢弃未知的目的MAC地址。
简单的说,就是不泛洪未知的目的MAC地址。
第二点与二层设备不同的是,防火墙不参与生成树(STP)。
因此,必须保证在使用透明模式防火墙时,不能故意增加二层环路。
如果有环路,你会很快的该设备和交换机的CPU利用率会增加到100%。
Cisco FWSM防火墙透明模式配置例子
Cisco FWSM防火墙透明模式配置例子透明模式配置例子以下内容需要回复才能看到hostname Farscapepassword passw0rdenable password chr1cht0ninterface vlan 4interface vlan 5interface vlan 6interface vlan 7interface vlan 150interface vlan 151interface vlan 152interface vlan 153admin-context admincontext adminallocate-interface vlan150allocate-interface vlan4config-url disk://admin.cfgmember defaultcontext customerAdescription This is the context for customer A allocate-interface vlan151allocate-interface vlan5config-url disk://contexta.cfgmember goldcontext customerBdescription This is the context for customer B allocate-interface vlan152allocate-interface vlan6config-url disk://contextb.cfgmember silvercontext customerCdescription This is the context for customer Callocate-interface vlan153allocate-interface vlan7config-url disk://contextc.cfgmember bronzeChangeto context adminfirewall transparentpasswd secret1969enable password h1andl0interface vlan 150nameif outsidesecurity-level 0bridge-group 1interface vlan 4nameif insidesecurity-level 100bridge-group 1interface bvi 1ip address 10.1.1.1 255.255.255.0route outside 0 0 10.1.1.2 1ssh 10.1.1.75 255.255.255.255 insidearp outside 10.1.1.2 0009.7cbe.2100arp inside 10.1.1.3 0009.7cbe.1000arp-inspection inside enable floodarp-inspection outside enable floodaccess-list INTERNET remark -Allows all inside hosts to access the outside access-list INTERNET extended permit ip any anyaccess-group INTERNET in interface insideaccess-list RETURN remark -Allows OSPF backaccess-list RETURN extended permit 89 any anyaccess-list RETURN remark -Allows DHCP backaccess-list RETURN extended permit udp any any eq 68access-group RETURN in interface outsideChangeto context afirewall transparentpasswd hell0!enable password enter55interface vlan 151nameif outsidesecurity-level 0bridge-group 45interface vlan 5nameif insidesecurity-level 100bridge-group 45interface bvi 45ip address 10.1.2.1 255.255.255.0route outside 0 0 10.1.2.2 1access-list INTERNET remark -Allows all inside hosts to access the outside access-list INTERNET extended permit ip any anyaccess-group INTERNET in interface insideaccess-list RETURN remark -Allows OSPF backaccess-list RETURN extended permit 89 any anyaccess-list RETURN remark -Allows DHCP backaccess-list RETURN extended permit udp any any eq 68access-group RETURN in interface outsideChangeto context bfirewall transparentpasswd tenac10usenable password defen$einterface vlan 152nameif outsidesecurity-level 0bridge-group 1interface vlan 6nameif insidesecurity-level 100bridge-group 1interface bvi 1ip address 10.1.3.1 255.255.255.0route outside 0 0 10.1.3.2 1access-list INTERNET remark -Allows all inside hosts to access the outside access-list INTERNET extended permit ip any anyaccess-group INTERNET in interface insideaccess-list RETURN remark -Allows OSPF backaccess-list RETURN extended permit 89 any anyaccess-list RETURN remark -Allows DHCP backaccess-list RETURN extended permit udp any any eq 68access-group RETURN in interface outsideChangeto context cfirewall transparentpasswd fl0werenable password treeh0u$einterface vlan 153nameif outsidesecurity-level 0bridge-group 100interface vlan 7nameif insidesecurity-level 100bridge-group 100interface bvi 100ip address 10.1.4.1 255.255.255.0route outside 0 0 10.1.4.2 1access-list INTERNET remark -Allows all inside hosts to access the outside access-list INTERNET extended permit ip any anyaccess-group INTERNET in interface insideaccess-list RETURN remark -Allows OSPF backaccess-list RETURN extended permit 89 any anyaccess-list RETURN remark -Allows DHCP backaccess-list RETURN extended permit udp any any eq 68access-group RETURN in interface outside。
Cisco ASA-5525 X Firepower Services安装实践案例说明书
FirePOWER Management Center (FMC) https:///download/home/286261232/type/286271056 Image and Package installers https:///download/home/286271172/type/286277393/
Passive: A copy of the traffic is sent to the module for inspection, alerting and logging but no action is taken while the original packet is sent to its destination. This mode is typically chosen for an initial system like the one described in this IBM Redpaper. In-Line: Traffic is sent to the module for inspection and acted upon before being forwarded. This mode is required for a true Intrusion Prevention system.
Redpaper
思科ASA5505防火墙配置成功实例
˼¿ÆASA5505·À»ðǽÅäÖóɹ¦ÊµÀý×÷Õߣºjx_wangl¡- ÎÄÕÂÀ´Ô´£º±¾Õ¾Ô-´´ µã»÷Êý£º1357 ¸üÐÂʱ¼ä£º2009-12-14 ÅäÖÃÒªÇó£º1¡¢ ·Ö±ð»®·Öinside£¨ÄÚÍø£©¡¢outside£¨ÍâÍø£©¡¢dmz£¨°²È«Çø£©Èý¸öÇøÓò¡£2¡¢ ÄÚÍø¿É·ÃÎÊÍâÍø¼°dmzÄÚ·þÎñÆ÷£¨web£©£¬ÍâÍø¿É·ÃÎÊdmzÄÚ·þÎñÆ÷£¨web£©¡£3¡¢ Dmz·þÎñÆ÷·Ö±ð¿ª·Å80¡¢21¡¢3389¶Ë¿Ú¡£ËµÃ÷£ºÓÉÓÚ·À»ðǽÐí¿ÉÏÞÖÆ¡°no forward interface Vlan1¡±dmzÄÚ·þÎñÆ÷ÎÞ·¨·ÃÎÊÍâÍø¡£¾ßÌåÅäÖÃÈçÏ£ºÏ£Íû¶ÔÐèÒªµÄÅóÓÑÓÐËù°ïÖúASA Version 7.2(4)!hostname asa5505enable password tDElRpQcbH/qLvnn encryptedpasswd 2KFQnbNIdI.2KYOU encryptednames!interface Vlan1nameif outsidesecurity-level 0ip address ÍâÍøIP ÍâÍøÑÚÂë!interface Vlan2nameif insidesecurity-level 100ip address 192.168.1.1 255.255.255.0 !interface Vlan3no forward interface Vlan1nameif dmzsecurity-level 50ip address 172.16.1.1 255.255.255.0 !interface Ethernet0/0description outside!interface Ethernet0/1description insideswitchport access vlan 2!interface Ethernet0/2description dmzswitchport access vlan 3!interface Ethernet0/3description insideswitchport access vlan 2!interface Ethernet0/4shutdown!interface Ethernet0/5shutdown!interface Ethernet0/6shutdown!interface Ethernet0/7shutdown!ftp mode passiveobject-group service outside-to-dmz tcpport-object eq wwwport-object eq ftpport-object eq 3389access-list aaa extended permit tcp any host ÍâÍøIP object-group outside- to-dmzaccess-list bbb extended permit tcp host 172.16.1.2 192.168.1.0 255.255.255.0 ob ject-group outside-to-dmzpager lines 24mtu outside 1500mtu inside 1500mtu dmz 1500icmp unreachable rate-limit 1 burst-size 1asdm image disk0:/asdm-524.binno asdm history enablearp timeout 14400global (outside) 1 interfaceglobal (dmz) 1 172.16.1.10-172.16.1.254 netmask 255.255.255.0nat (inside) 1 192.168.1.0 255.255.255.0nat (dmz) 1 172.16.1.0 255.255.255.0alias (inside) 221.203.36.86 172.16.1.2 255.255.255.255static (dmz,outside) tcp interface www 172.16.1.2 www netmask 255.255.255.255 d nsstatic (dmz,outside) tcp interface ftp 172.16.1.2 ftp netmask 255.255.255.255 d nsstatic (dmz,outside) tcp interface 3389 172.16.1.2 3389 netmask 255.255.255.255 dnsstatic (inside,dmz) 172.16.1.2 192.168.1.0 netmask 255.255.255.255 dnsaccess-group aaa in interface outsideaccess-group bbb in interface dmzroute outside 0.0.0.0 0.0.0.0 ÍâÍøÍø¹Ø 1timeout xlate 3:00:00timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absoluteno snmp-server locationno snmp-server contactsnmp-server enable traps snmp authentication linkup linkdown coldstarttelnet timeout 5ssh timeout 5console timeout 0!class-map inspection_defaultmatch default-inspection-traffic!!policy-map type inspect dns preset_dns_mapparametersmessage-length maximum 512policy-map global_policyclass inspection_defaultinspect dns preset_dns_mapinspect ftpinspect h323 h225inspect h323 rasinspect netbiosinspect rshinspect rtspinspect skinnyinspect esmtpinspect sqlnetinspect sunrpcinspect tftpinspect sipinspect xdmcpinspect http!service-policy global_policy globalprompt hostname contextCryptochecksum:9d2a6010d4fc078cf026f98dcec96007: endasa5505(config)#。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
ciscoasa# show run
ciscoasa# show running-config
: Saved
:
ASA Version 8.2(5)
!
firewall transparent
hostname ciscoasa
enable password 8Ry2YjIyt7RRXU24 encrypted passwd 2KFQnbNIdI.2KYOU encrypted names
!
interface GigabitEthernet0/0
nameif outside
security-level 0
!
interface GigabitEthernet0/1
nameif inside
security-level 100
!
interface GigabitEthernet0/2
shutdown
no nameif
no security-level
!
interface GigabitEthernet0/3
shutdown
no nameif
no security-level
!
interface Management0/0
shutdown
no nameif
no security-level
management-only
!
ftp mode passive
access-list out-in extended permit ip any any
access-list out-in extended permit tcp any any
access-list out-in extended permit icmp any any
pager lines 24
mtu outside 1500
mtu inside 1500
ip address 13.84.2.4 255.255.255.0
no failover
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
access-group out-in in interface outside
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec security-association lifetime seconds 28800 crypto ipsec security-association lifetime kilobytes 4608000 telnet timeout 5
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect rtsp
inspect esmtp
inspect sqlnet
inspect skinny
inspect sunrpc
inspect xdmcp
inspect sip
inspect netbios
inspect tftp
inspect ip-options
!
service-policy global_policy global
prompt hostname context
call-home reporting anonymous prompt 2 Cryptochecksum:6fae7ccfbe0303270444551fa25a4cf7
: end
1.默认不含密码进去en模式直接回车
2.首先需要把防火墙模式设置为firewall transparent保存并且重启
3.conf 模式下配置全局地址必须为上下游同一vlan地址
4.接口设置nameif 和 security-level
5.设置access-list
6调用access-group out-in in interface outside。
