最新-ccnp的试题全中文
思科认证CCNA认证试题与答案中文版
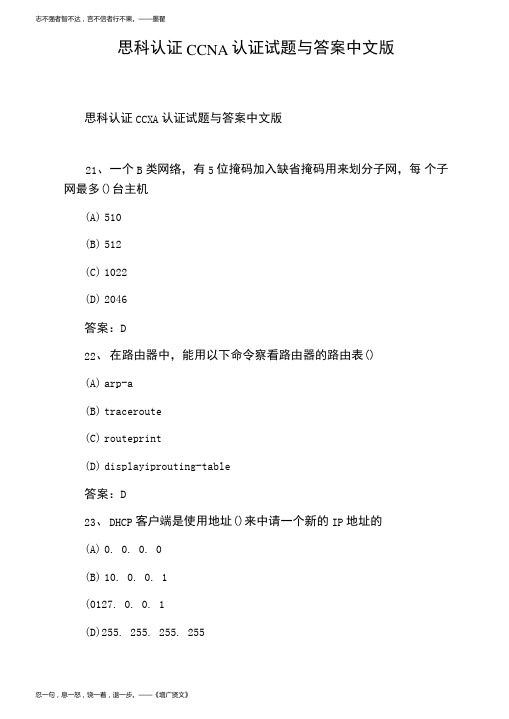
答案:D 注释:这个题目不是太严谨,应该加上子网掩码. A:224. 0. 0. 5 是多播地址 B: 127. 0.0. 0 保留作为测试使用 C:网络地址 26、 设置主接口由 up 转 down 后延迟 30 秒切换到备份接口,主 接口 由 down 转 up 后 60 秒钟切换回主接口的配置为()
忍一句,息一怒,饶一着,退一步。——《增广贤文》
人之为学,不日进则日退,独学无友,则孤陋而难成;久处一方,则习染而不自觉。——《顾炎武》
答案:D 注释:255. 255. 255. 255 是全网广播,DHCP 客户端发送全网广播来 查 找 DHCP 服务器. 24、 下而有关 NAT 叙述正确的是() (A) NAT 是英文“地址转换”的缩写,又称地址翻译 (B) XAT 用来实现私有地址与公用网络地址之间的转换 (C) 当内部网络的主机访问外部网络的时候,一定不需要 NAT (D) 地址转换的提出为解决 IP 地址紧张的问题提供了一个有效途 径 答案:ABD 25、 以下属于正确的主机的 IP 地址的是()
(A) arp-a (B) traceroute (C) routeprint (D) displayiprouting-table
答案:D 23、 D0. 0. 0 (B) 10. 0. 0. 1 (0127. 0. 0. 1 (D)255. 255. 255. 255
192. 168. 1. 1
答案:D 注释:PC 的'默认网关要指向路由器的以太网口的 IP 地址. 28、 ISDNB 信道速率是()
(A) 16kbps (B) 64kbps
思科认证CCNP经典试题

思科认证CCNP经典试题第一部分填空题1、在Cisco体系的IGP协议中,RIP的A-D管理距离是,EIGRP 的域内A-D管理距离是,EIGRP的域外A-D管理距离是OSPF的A-D管理距离是。
BGP 从EBGP学习到的路由学到路由的A-D管理距离是; BGP从IBGP学习到的路由学到路由的A-D管理距离是。
2、BGP的默认MED值为;其中MED越越优选被用于选路;BGP从邻居哪里学到的权重为;BGP自己本路由产生的路由(始发路由)产生权重是;BGP 的默认本地优先级为:。
3、BGP的邻居分为和。
4、OSPF在那个区域(有区域0,区域1,区域2)广播多路访问(比如以太网,没有出现外部网络),在区域0可以看到类LSA。
如果想看到2类LSA,必须在网络类型;在NSSA区域可以看到类LSA,在纯粹的NASS区域内是否有5类LSA?(回答是或者否)。
5、HSRP包括哪六种状态?6、OSPF在MA网络链路类型的HELLO报文作用?(3种)7、IPV6的本地链路地址是;本地站点地址是。
(没有/10的写法)8、在选择STP的角色(身份)有哪些?,默认STP的收敛时间为。
配置了portfast后,收敛时间会小于。
9、OSPF发送hello包的组播地址是,EIGRP组播地址是;HSRP 发送hello包组播地址是;VRRP发送hello 包的组播地址是。
10、目前以太通道最多可以使用条物理线缆逻辑捆绑成一个以太通道接口?形成以太通道方式有。
11、BGP在EBGP中使用属性避免AS间的环路(确保无环),该属性属于BGP的必遵属性,其中还有哪两个是BGP公认必遵属性为和。
第二部分选择1、在对基于CEF的多层交换(MLS)进行排错的时候,例如解决无法到达特定的IP目标等问题,首先需要先查看哪两张表去验证错误?()A、IP路由表和路由表B、IP路由和CEF邻接关系表C、TCAM中的IP CEF FIB和邻接关系表D、IP路由表和ARP表2、EIGRP位一个混合距离矢量协议,在METRIC值中使用K1-K5五个K值,默认情况下,使用K值分别是()A、K1,K2 B K3,K4 C、K1,K5 D、K1,K33、OSPF中router-id能标识一台设备的身份,下面说法正确的是()A、先选举手工配置,然后选择设备loopback地址大的,在选运行了宣告进OSPF最大的物理接口最大的地址。
CCNP最新题库 SWITCH 642-813-2
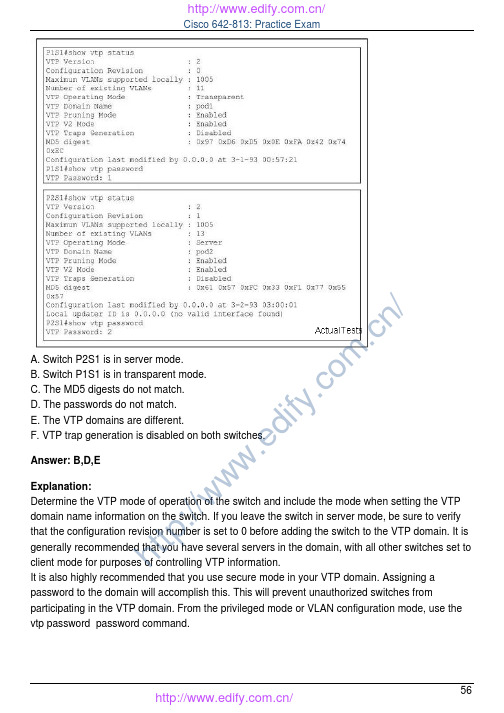
A. Switch P2S1 is in server mode.B. Switch P1S1 is in transparent mode.C. The MD5 digests do not match.D. The passwords do not match.E. The VTP domains are different.F. VTP trap generation is disabled on both switches.Answer: B,D,EExplanation:Determine the VTP mode of operation of the switch and include the mode when setting the VTP domain name information on the switch. If you leave the switch in server mode, be sure to verify that the configuration revision number is set to 0 before adding the switch to the VTP domain. It is generally recommended that you have several servers in the domain, with all other switches set to client mode for purposes of controlling VTP information.It is also highly recommended that you use secure mode in your VTP domain. Assigning a password to the domain will accomplish this. This will prevent unauthorized switches fromparticipating in the VTP domain. From the privileged mode or VLAN configuration mode, use the vtp password password command.h t t p://www.ed if y.co m .cn /QUESTION NO: 75Refer to the exhibit. Based upon the output of show vlan on switch CAT2, what can we conclude about interfaces Fa0/13 and Fa0/14?A. that interfaces Fa0/13 and Fa0/14 are in VLAN 1B. that interfaces Fa0/13 and Fa0/14 are downC. that interfaces Fa0/13 and Fa0/14 are trunk interfacesD. that interfaces Fa0/13 and Fa0/14have a domain mismatch with another switchE. that interfaces Fa0/13 and Fa0/14have a duplex mismatch with another switchAnswer: CExplanation:trunk - This setting places the port in permanent trunking mode. The corresponding switch port at the other end of the trunk should be similarly configured because negotiation is not allowed. You should also manually configure the encapsulation mode.show vlan: This commands shows the vlan, ports belonging to VLAN means that port on access mode. It doesn't shows the port on trunk mode.QUESTION NO: 76Refer to the exhibit. On the basis of the output generated by the show commands, which two statements are true? (Choose two.)h t t p://www.ed if y.co m .cn /A. Because it is configured as a trunk interface, interface gigabitethernet 0/1 does not appear in the show vlan output.B. VLAN 1 will not be encapsulated with an 802.1q header.C. There are no native VLANs configured on the trunk.D. VLAN 2 will not be encapsulated with an 802.1q header.E. All interfaces on the switch have been configured as access ports.F. Because it has not been assigned to any VLAN, interface gigabitethernet 0/1 does not appear in the show vlan output.Answer: A,BExplanation:h t t p://www.ed if y.co m .cn /The IEEE 802.1Q protocol can also carry VLAN associations over trunk links. However, this frame identification method is standardized, allowing VLAN trunks to exist and operate between equipment from multiple vendors.In particular, the IEEE 802.1Q standard defines an architecture for VLAN use, services provided with VLANs, and protocols and algorithms used to provide VLAN services.Like Cisco ISL, IEEE 802.1Q can be used for VLAN identification with Ethernet trunks. Instead of encapsulating each frame with a VLAN ID header and trailer, 802.1Q embeds its tagging information within the Layer 2 frame. This method is referred to as single-tagging or internal tagging .802.1Q also introduces the concept of a native VLAN on a trunk. Frames belonging to this VLAN are not encapsulated with any tagging information. In the event that an end station is connected to an 802.1Q trunk link, the end station can receive and understand only the native VLAN frames.This provides a simple way to offer full trunk encapsulation to the devices that can understand it,while giving normal access stations some inherent connectivity over the trunk.show vlan: This commands shows the vlan, ports belonging to VLAN means that port on access mode. It doesn't show the port on trunk mode.QUESTION NO: 77Refer to the exhibit and the show interfaces fastethernet0/1 switchport outputs. Users in VLAN 5on switch SW_A complain that they do not have connectivity to the users in VLAN 5 on switch SW_B. What should be done to fix the problem?A. Configure the same number of VLANs on both switches.h t t p://www.ed if y.co m .cn /B. Create switch virtual interfaces (SVI) on both switches to route the traffic.C. Define VLAN 5 in the allowed list for the trunk port on SW_A.D. Disable pruning for all VLANs in both switches.E. Define VLAN 5 in the allowed list for the trunk port on SW_BAnswer: CExplanation:switchport trunk allowed vlan , defines which VLANs can be trunked over thelink . By default, a switch transports all active VLANs (1 to 4094) over a trunk link. There might be times when the trunk link should not carry all VLANs. For example, broadcasts are forwarded to every switch port on a VLAN-including the trunk link because it, too, is a member of the VLAN.If the VLAN does not extend past the far end of the trunk link, propagating broadcasts across the trunk makes no sense.Section 8: Document results of VLAN implementation and verification (0 Questions)QUESTION NO: 78Refer to the exhibit. An attacker is connected to interface Fa0/11 on switch A-SW2 and attempts to establish a DHCP server for a man-in-middle attack. Which recommendation, if followed, would mitigate this type of attack?A. All switch ports in the Building Access block should be configured as DHCP untrusted ports.B. All switch ports in the Building Access block should be configured as DHCP trusted ports.h t t p://www.ed if y.co m .cn /C. All switch ports connecting to servers in the Server Farm block should be configured as DHCP untrusted ports.D. All switch ports connecting to hosts in the Building Access block should be configured as DHCP trusted ports.E. All switch ports in the Server Farm block should be configured as DHCP untrusted ports.F. All switch ports connecting to hosts in the Building Access block should be configured as DHCP untrusted ports.Answer: FExplanation:One of the ways that an attacker can gain access to network traffic is to spoof responses that would be sent by a valid DHCP server. The DHCP spoofing device replies to client DHCPrequests. The legitimate server may reply also, but if the spoofing device is on the same segment as the client, its reply to the client may arrive first.The intruder's DHCP reply offers an IP address and supporting information that designates the intruder as the default gateway or Domain Name System (DNS) server. In the case of a gateway,the clients will then forward packets to the attacking device, which will in turn send them to the desired destination. This is referred to as a "man-in-the-middle" attack, and it may go entirely undetected as the intruder intercepts the data flow through the network.Untrusted ports are those that are not explicitly configured as trusted. A DHCP binding table is built for untrusted ports. Each entry contains the client MAC address, IP address, lease time,binding type, VLAN number, and port ID recorded as clients make DHCP requests. The table is then used to filter subsequent DHCP traffic. From a DHCP snooping perspective, untrusted access ports should not send any DHCP server responses, such as DHCPOFFER, DHCPACK,DHCPNAK .QUESTION NO: 79You are responsible for increasing the security within the Company LAN. Of the following choices listed below, which is true regarding layer 2 security and mitigation techniques?A. Enable root guard to mitigate ARP address spoofing attacks.B. Configure DHCP spoofing to mitigate ARP address spoofing attacks.C. Configure PVLANs to mitigate MAC address flooding attacks.D. Enable root guard to mitigate DHCP spoofing attacks.E. Configure dynamic APR inspection (DAI) to mitigate IP address spoofing on DHCP untrusted ports.F. Configure port security to mitigate MAC address floodingG. None of the other alternatives applyAnswer: Fh t t p://www.ed if y.co m .cn /Explanation:Use the port security commands to mitigate MAC-spoofing attacks. The port security command provides the capability to specify the MAC address of the system connected to a particular port.The command also provides the ability to specify an action to take if a port-security violationoccurs. However, as with the CAM table-overflow attack mitigation, specifying a MAC address on every port is an unmanageable solution. Hold-down timers in the interface configuration menu can be used to mitigate ARP spoofing attacks by setting the length of time an entry will stay in the ARP cache.Reference: /networksecurity/NetworkSecurity.htmlSection 2: Create an implementation plan for the Security solution (3 Questions)QUESTION NO: 80You work as a network technician at . Your boss, Mrs. Tess King, is interested in switch spoofing. She asks you how an attacker would collect information with VLAN hoping through switch spoofing. You should tell her that the attacking station...A. es VTP to collect VLAN information that is sent out and then tags itself with the domain information in order to capture the data.B. ...will generate frames with two 802.1Q headers to cause the switch to forward the frames to a VLAN that would be inaccessible to the attacker through legitimate means.C. es DTP to negotiate trunking with a switch port and captures all traffic that is allowed on the trunk.D. ...tags itself with all usable VLANs to capture data that is passed through the switch, regardless of the VLAN to which the data belongs.E. None of the other alternatives applyAnswer: CExplanation:DTP should be disabled for all user ports on a switch. If the port is left with DTP auto-configured (default on many switches), an attacker can connect and arbitrarily cause the port to start trunking and therefore pass all VLAN information.Reference:/en/US/solutions/ns340/ns517/ns224/ns376/net_design_guidance0900aecd800ebd1e.pdfQUESTION NO: 81h t t p://www.ed if y.co m .cn /The Company security administrator is concerned with layer 2 network attacks. Which two statements about these attacks are true? (Select two)A. ARP spoofing attacks are attempts to redirect traffic to an attacking host by encapsulating a false 802.1Q header on a frame and causing traffic to be delivered to the wrong VLAN.B. ARP spoofing attacks are attempts to redirect traffic to an attacking host by sending an ARP message with a forged identity to a transmitting host.C. MAC address flooding is an attempt to force a switch to send all information out every port by overloading the MAC address table.D. ARP spoofing attacks are attempts to redirect traffic to an attacking host by sending an ARP packet that contains the forged address of the next hop router.E. MAC address flooding is an attempt to redirect traffic to a single port by associating that port with all MAC addresses in the VLAN.Answer: B,CExplanation:Content Addressable Memory ( CAM ) Table Overflow (MAC address Flooding)Content Addressable Memory (CAM) tables are limited in size. If enough entries are entered into the CAM table before other entries are expired, the CAM table fills up to the point that no new entries can be accepted. Typically, a network intruder floods the switch with a large number of invalid source Media Access Control (MAC) addresses until the CAM table fills up. When thatoccurs, the switch floods all ports with incoming traffic because it cannot find the port number for a particular MAC address in the CAM table. The switch, in essence, acts like a hub. If the intruder does not maintain the flood of invalid-source MAC addresses, the switch eventually times out older MAC address entries from the CAM table and begins to act like a switch again. CAM tableoverflow only floods traffic within the local VLAN so the intruder only sees traffic within the local VLAN to which he or she is connected.The CAM table overflow attack can be mitigated by configuring port security on the switch. This option provides for either the specification of the MAC addresses on a particular switch port or the specification of the number of MAC addresses that can be learned by a switch port. When an invalid MAC address is detected on the port, the switch can either block the offending MAC address or shut down the port. The specification of MAC addresses on switch ports is far too unmanageable a solution for a production environment. A limit of the number of MAC addresses on a switch port is manageable. A more administratively scalable solution is the implementation of dynamic port security at the switch. In order to implement dynamic port security, specify a maximum number of MAC addresses that will be learned.Address Resolution Protocol (ARP) SpoofingARP is used to map IP addressing to MAC addresses in a local area network segment where hosts of the same subnet reside. Normally, a host sends out a broadcast ARP request to find the MAC address of another host with a particular IP address, and an ARP response comes from the host whose address matches the request. The requesting host then caches this ARP response.Within the ARP protocol, another provision is made for hosts to perform unsolicited ARP replies.h t t p://www.ed if y.co m .cn /The unsolicited ARP replies are called Gratuitous ARP (GARP). GARP can be exploited maliciously by an attacker to spoof the identity of an IP address on a LAN segment. This istypically used to spoof the identity between two hosts or all traffic to and from a default gateway in a "man-in-the-middle" attack.When an ARP reply is crafted, a network attacker can make his or her system appear to be the destination host sought by the sender. The ARP reply causes the sender to store the MACaddress of the network attacker's system in the ARP cache. This MAC address is also stored by the switch in its CAM table. In this way, the network attacker has inserted the MAC address of his or her system into both the switch CAM table and the ARP cache of the sender. This allows the network attacker to intercept frames destined for the host that he or she is spoofing.Reference:/en/US/products/hw/switches/ps5023/products_configuration_example09186a00807c4101.shtmlQUESTION NO: 82The Company security administrator wants to prevent DHCP spoofing. Which statement is true about DHCP spoofing operation?A. DHCP spoofing and SPAN cannot be used on the same port of a switch.B. To prevent a DHCP spoofing, the DHCP server must create a static ARP entry that cannot be updated by a dynamic ARP packet.C. To prevent a DHCP spoofing, the switch must have DHCP server services disabled and a static entry pointing towards the DHCP server.D. DHCP spoofing can be prevented by placing all unused ports in an unused VLAN.E. None of the other alternatives apply.Answer: BExplanation:About DHCP Spoofing:Suppose that an attacker could bring up a rogue DHCP server on a machine in the same subnet as that same client PC. Now when the client broadcasts its DHCP request, the rogue server could send a carefully crafted DHCP reply with its own IP address substituted as the default gateway.When the client receives the reply, it begins using the spoofed gateway address. Packets destined for addresses outside the local subnet then go to the attacker's machine first. The attacker can forward the packets to the correct destination, but in the meantime, it can examine every packet that it intercepts. In effect, this becomes a type of man-in-the-middle attack; the attacker is wedged into the path and the client doesn't realize it.About ARP:h t t p://www.ed if y.co m .cn /Hosts normally use the Address Resolution Protocol (ARP) to resolve an unknown MAC address when the IP address is known. If a MAC address is needed so that a packet can be forwarded at Layer 2, a host broadcasts an ARP request that contains the IP address of the target in question.If any other host is using that IP address, it responds with an ARP reply containing its MAC address.To prevent a DHCP spoofing, the DHCP server must create a static ARP entry that cannot be updated by a dynamic ARP packetSection 3: Create a verification plan for the Security solution (4 Questions)QUESTION NO: 83Refer to the exhibit. What will happen to traffic within VLAN 14 with a source address of 172.16.10.5?A. The traffic will be forwarded to the router processor for further processing.B. The traffic will be dropped.C. The traffic will be forwarded to the TCAM for further processing.D. The traffic will be forwarded without further processing.Answer: BExplanation:VLAN maps, also known as VLAN ACLs or VACLs, can filter all traffic traversing a switch. VLAN maps can be configured on the switch to filter all packets that are routed into or out of a VLAN, or are bridged within a VLAN. VLAN maps are used strictly for security packet filtering. Unlike routerh t t p://www.ed if y.co m .cn /ACLs, VLAN maps are not defined by direction (input or output).To create a VLAN map and apply it to one or more VLANs, perform these steps: Create the standard or extended IP ACLs or named MAC extended ACLs to be applied to the VLAN. This access-list will select the traffic that will be either forwarded or dropped by the access-map. Only traffic matching the 'permit' condition in an access-list will be passed to the access-map for further processing. Enter the vlan access-map access-map-name [ sequence ] global configuration command to create a VLAN ACL map entry. Each access-map can have multiple entries. The order of these entries is determined by the sequence . If no sequence number is entered, access-map entries are added with sequence numbers in increments of 10. In access map configuration mode, optionally enter an action forward or action drop . The default is to forward traffic. Also enter the match command to specify an IP packet or a non-IP packet (with only a known MAC address),and to match the packet against one or more ACLs (standard or extended). Use the vlan filter access-map-name vlan-list vlan-list global configuration command to apply a VLAN map to one or more VLANs. A single access-map can be used on multiple VLANs.QUESTION NO: 84Company is implementing 802.1X in order to increase network security. In the use of 802.1X access control, which three protocols are allowed through the switch port before authentication takes place? (Select three)A. EAP-over-LANB. EAP MD5C. STPD. protocols not filtered by an ACLE. CDPF. TACACS+Answer: A,C,EExplanation:The IEEE 802.1x standard defines a port-based access control and authentication protocol that restricts unauthorized workstations from connecting to a LAN through publicly accessible switch ports. The authentication server authenticates each workstation that is connected to a switch port before making available any services offered by the switch or the LAN. Until the workstation is authenticated, 802.1x access control allows only Extensible Authentication Protocol over LAN (EAPOL) traffic through the port to which the workstation is connected. After authentication succeeds, normal traffic can pass through the port.The Authentication server performs the actual authentication of the client. The authentication server validates the identity of the client and notifies the switch whether or not the client is authorized to access the LAN and switch services. Because the switch acts as the proxy, theh t t p://www.ed if y.co m .cn /authentication service is transparent to the client. In this release, the Remote Authentication Dial-In User Service (RADIUS) security system with Extensible Authentication Protocol (EAP)extensions is the only supported authentication server; it is available in Cisco Secure Access Control Server version 3.0. RADIUS operates in a client/server model in which secureauthentication information is exchanged between the RADIUS server and one or more RADIUS clients.Spanning-Tree Protocol (STP) is a Layer 2 protocol that utilizes a special-purpose algorithm to discover physical loops in a network and effect a logical loop-free topology. STP creates a loop-free tree structure consisting of leaves and branches that span the entire Layer 2 network. The actual mechanics of how bridges communicate and how the STP algorithm works will be discussed at length in the following topics. Note that the terms bridge and switch are used interchangeably when discussing STP. In addition, unless otherwise indicated, connections between switches are assumed to be trunks.CDP is a Cisco proprietary protocol that operates at the Data Link layer. One unique feature about operating at Layer 2 is that CDP functions regardless of what Physical layer media you are using (UTP, fiber, and so on) and what Network layer routed protocols you are running (IP, IPX,AppleTalk, and so on). CDP is enabled on all Cisco devices by default, and is multicast every 60seconds out of all functioning interfaces, enabling neighbor Cisco devices to collect information about each other. Although this is a multicast message, Cisco switches do not flood that out to all their neighbors as they do a normal multicast or broadcast.For STP, CDP and EAP-over-LAN are allowed before Authentication.QUESTION NO: 85Refer to the exhibit. The web servers WS_1 and WS_2 need to be accessed by external and internal users. For security reasons, the servers should not communicate with each other,although they are located on the same subnet. The servers do need, however, to communicate with a database server located in the inside network. What configuration will isolate the servers from each other?h t t p://www.ed if y.co m .cn /A. The switch ports 3/1 and 3/2 will be defined as secondary VLAN community ports. The ports connecting to the two firewalls will be defined as primary VLAN promiscuous ports.B. The switch ports 3/1 and 3/2 and the ports connecting to the two firewalls will be defined as primary VLAN promiscuous ports.C. The switch ports 3/1 and 3/2 and the ports connecting to the two firewalls will be defined as primary VLAN community ports.D. The switch ports 3/1 and 3/2 will be defined as secondary VLAN isolated ports. The ports connecting to the two firewalls will be defined as primary VLAN promiscuous ports.Answer: DExplanation:Service providers often have devices from multiple clients, in addition to their own servers, on a single Demilitarized Zone (DMZ) segment or VLAN. As security issues proliferate, it becomes necessary to provide traffic isolation between devices, even though they may exist on the same Layer 3 segment and VLAN. Catalyst 6500/4500 switches implement PVLANs to keep some switch ports shared and some switch ports isolated, although all ports exist on the same VLAN.The 2950 and 3550 support "protected ports," which are functionality similar to PVLANs on a per-switch basis.A port in a PVLAN can be one of three types:Isolated: An isolated port has complete Layer 2 separation from other ports within the same PVLAN, except for the promiscuous port. PVLANs block all traffic to isolated ports, except the traffic from promiscuous ports. Traffic received from an isolated port is forwarded to only promiscuous ports.Promiscuous: A promiscuous port can communicate with all ports within the PVLAN, including the community and isolated ports. The default gateway for the segment would likely be hosted on a promiscuous port, given that all devices in the PVLAN will need to communicate with that port. Community: Community ports communicate among themselves and with their promiscuous ports.These interfaces are isolated at Layer 2 from all other interfaces in other communities, or in isolated ports within their PVLAN.QUESTION NO: 86VLAN maps have been configured on switch R1. Which of the following actions are taken in a VLAN map that does not contain a match clause?A. Implicit deny feature at end of list.B. Implicit deny feature at start of list.C. Implicit forward feature at end of listD. Implicit forward feature at start of list.Answer: Ah t t p://www.ed if y.co m .cn /Explanation:Each VLAN access map can consist of one or more map sequences, each sequence with a match clause and an action clause. The match clause specifies IP, IPX, or MAC ACLs for traffic filtering and the action clause specifies the action to be taken when a match occurs. When a flow matches a permit ACL entry the associated action is taken and the flow is not checked against theremaining sequences. When a flow matches a deny ACL entry, it will be checked against the next ACL in the same sequence or the next sequence. If a flow does not match any ACL entry and at least one ACL is configured for that packet type, the packet is denied.Reference:/en/US/products/hw/switches/ps700/products_configuration_guide_chapter09186a008007f4d4.htmlSection 4: Configure port security features (6 Questions)QUESTION NO: 87A Company switch was configured as shown below:switchport mode access switchport port-securityswitchport port-security maximum 2switchport port-security mac-address 0002.0002.0002switchport port-security violation shutdownGiven the configuration output shown above, what happens when a host with the MAC address of 0003.0003.0003 is directly connected to the switch port?A. The host will be allowed to connect.B. The port will shut down.C. The host can only connect through a hub/switch where 0002.0002.0002 is already connected.D. The host will be refused access.E. None of the other alternatives applyAnswer: AExplanation:Steps of Implementing Port Security:h t t p://www.ed if y.co m .cn /In Exhibit two MAC addresses are allowed so that host will be allowed to connect.QUESTION NO: 88Refer to the exhibit. Which interface or interfaces on switch SW_A can have the port security feature enabled?A. Ports 0/1 and 0/2B. The trunk port 0/22 and the EtherChannel portsh t t p://www.ed if y.co m .cn /C. Ports 0/1, 0/2 and 0/3D. Ports 0/1, 0/2, 0/3, the trunk port 0/22 and the EtherChannel portsE. Port 0/1F. Ports 0/1, 0/2, 0/3 and the trunk port 0/22Answer: CExplanation:Port security is a feature supported on Cisco Catalyst switches that restricts a switch port to a specific set or number of MAC addresses. Those addresses can be learned dynamically or configured statically. The port will then provide access to frames from only those addresses. If,however, the number of addresses is limited to four but no specific MAC addresses areconfigured, the port will allow any four MAC addresses to be learned dynamically, and port access will be limited to those four dynamically learned addresses. A port security feature called "sticky learning," available on some switch platforms, combines the features of dynamically learned and statically configured addresses. When this feature is configured on an interface, the interface converts dynamically learned addresses to "sticky secure" addresses. This adds them to the running configuration as if they were configured using the switchport port-security mac-address command.QUESTION NO: 89Refer to the exhibit. Based on the running configuration that is shown for interface FastEthernet0/2, what two conclusions can be deduced? (Choose two.)A. Connecting a host with MAC address 0000.0000.4147 will move interface FastEthernet0/2 into error disabled state.B. The host with address 0000.0000.4141 is removed from the secure address list after 5 seconds of inactivity.h t t p://www.ed if y.co m .cn /。
最新CCNP-思科认证题目

网络系统构建技术总复习一、不定项选择题1、在Windows 2003/2008 的TCP/IP 网络中,IP 地址有两种设定方法,它们分别是(B、D)。
A. 通过DHCP 和DNS 设定B. 通过DHCP 及人工指定C. 通过子网掩码和缺省网关给定D. 通过网络自动生成2、如果所在的局域网中存在DHCP 服务器,那么在Windows 平台下安装TCP/IP网络时,就可以(B )。
A. 去掉IP 地址的设置B. 从DHCP 服务器中自动获得一个IP 地址C. 设置一个有效的固定IP 地址D. 任意设置一个IP 地址3、如果用户所安装的TCP/IP 网络与其他网络或与Internet 相连,则必须(D )。
A. 设定DHCPB. 设置WINSC. 给定任意一个IP 地址D. 指定缺省网关4.在Windows 2003/2008 的TCP/IP 网络中,要求各个连网计算机的IP 地址在本域范围内( B )。
A. 使用同一个IP 地址B. 惟一C. 任意设定D. 不惟一5、在设置静态ip地址时,(A、C、D )参数有时是可以不设置的。
(选择三项)A. 网关B. 子网掩码C. 首选域名服务器D. 备用域名服务器6、在邮件地址mackenzre@中,(B)表示域名。
(选择一项)A. MackenzreB. C. mackenzre@7、一台服务器准备作为网络的文件服务器,管理员正在对该服务器的硬盘进行规划。
如果用户希望读写速度最快,他应将硬盘规划为(C ),如果用户希望对系统分区进行容错,他应将硬盘规划为(D ),如果用户希望对数据进行容错,并保证较高的磁盘利用率,他应将硬盘规划为( E )。
A. 简单卷B. 跨区卷C. 带区卷D. 镜像卷E. RAID-5卷8、使用域控制器来集中管理域账户,你安装域控制器必须具备以下条件(A、B )。
(选择二项)A. 操作系统版本是Windows server 2003或者Windows Server 2008B. 本地磁盘至少有一个NTFS分区C. 本地磁盘必须全部是NTFS分区D. 有相应的DNS服务器支持9、一位系统管理员在安装Windows Server 2003/2008的过程中,在安装向导的网络设置页面中选择了“典型设置”,那么当服务器安装完成后将其连接到公司的网络,它的IP地址会( B )。
CCNP 试题

唐钢集团CCNP课程培训测试题姓名:成绩:一、选择题:(单选,共20题,每题4分)1.如下图所示,拓扑表中,数字3011840 和3128695 代表什么?-------------------------()A.应用于该路由器EIGRP 路由的路由度量B.路由信息来源的可信度C.到目的网络的跳数和带宽的复合度量D.由EIGRP 邻居通告的网络总度量2.请参见图示。
该公司在编号为10 的自治系统中使用EIGRP。
路由器A 和路由器B 所连接网络上的主机能够相互ping 通。
但是,192.168.3.0 网络上的用户无法访问192.168.1.32 网络上的用户。
此问题最可能的原因是什么?---------------------------------------------------()A启用了无类IP,从而导致数据包被丢弃。
B路由器C 上未使用network 192.168.1.32 命令。
C没有将路由器配置在相同的EIGRP 路由域中。
D网络自动总结导致各子网的路由被丢弃。
3.请参见图示。
网络192.168.0.0/28 断开。
Router2 会立即向Router1 和Router3 发送什么类型的数据包?---------------------------------------------------------------------------------------------------()A查询网络192.168.0.0/28 的查询数据包B到224.0.0.9 的确认数据包C发送到255.255.255.255 的更新数据包D包含R2 新路由表的数据包发送到192.168.1.1 和192.168.2.1 的单播更新数据包4.请参见图示。
所有接口都已配置为如图所示的带宽。
假设所有路由器都是使用默认的EIGRP 配置作为路由协议,那么从172.16.1.0/16 网络发往192.168.200.0/24 网络的数据包会采用哪一条路径?--------------------------------------------------------------------------------------------------------------------()A. A-B-EB. A-C-EC. A-D-ED.数据包会在A、B、E 和A、C、E 路径之间实施负载均衡。
ccnp题库

FCAPSFault Management ‐‐‐‐‐‐‐‐‐‐‐‐‐‐‐‐‐ FConfiguration Management ‐‐‐‐‐‐‐ CAccounting Management ‐‐‐‐‐‐‐‐‐‐ AQuestion 2FCAPS–model defined by the International Organization for Standardization (ISO).ITIL–framework for it profTNM–network management model is the Telecommunications Standardization Sector’s (ITU-T) Cisco lifecycle–model is often referred to as the PPDIOO modelQuestion 3EEM .IP SLA‐‐‐‐‐‐‐‐‐‐‐‐‐‐ CLISDM .CNA‐‐‐‐‐‐‐‐‐‐‐‐‐‐ GUIFTP ,TFTP,SCP‐‐‐‐‐‐‐‐‐‐‐‐‐‐ BackupCLI(command-line interface,命令行界面)GUI(Graphical User Interface,图形用户界面)SDM(Security Device Manager)是Cisco公司提供的全新图形化路由器管理工具;EEM(Embeded Event Manager)是Cisco IOS的嵌入式事件管理器;1)FCAPS (network maintenance model defined by the ISO)F – FaultC – ConfigA – Accounting2) What happens when running the command: logging console warnings.1-2- warning, notification, error, debugging…3- just warning logging4- warning, critical, alert, emergenciesAnswer:warning, critical, alert, emergencies(Notice this line doesn’t have the word “error”)3) what will be alternative for:ip ftp username xxxxxxip ftp password yyyyyyAnswer:ip http client username xxxxxxip http client password yyyyyy4) Network Maintenance: Choose from the list 2 network maintaining types.Answer:Structured and Interrupt Driven5) access-list 199 permit tcp host 10.1.1.1 host 172.16.1.1access-list 199 permit tcp host 172.16.1.1 host 10.1.1.1debug ip packet 199What would be the output shown on the console?Only communication between host 10.1.1.1 and host 172.16.1.16) what will happen if u configure two router as NTP server (something like that )Answer:The router will choose the best reliable server and will synchronise with it.7) The interface is up and protocol is up. When do u get these messages.%LINEPROTO‐5‐UPDOWN: Line protocol on Interface FastEthernet0/14, changed state to up %LINKDOWN‐3‐SERIAL:Answer:Emergency 0 Alerts 1 Critical 2 Errors 3 Warning4Notification 5 Informational 6 Debugging 78)Serial line is up,protocol is also up?But cdp neighbor not working?Answer:Data link layer.T1:ospf authentication1.Client is unable to ping R1’s serial interface from the client.Problem was disable authentification on R1, check where authentication is not given under router ospf of R1. (use ipv4 Layer 3)conf R1 was:interface Serial0/0.12 point-to-pointip address 10.1.1.1 255.255.255.252ip nat insideip ospf message-digest-key 1 md5 TSHOOTrouter ospf 1log-adjacency-changesnetwork 10.1.1.0 0.0.0.3 area 12default-information originate alwaysconf R2 was:interface Serial0/0.12 point-to-pointip address 10.1.1.2 255.255.255.252ip ospf authentication message-digestip ospf message-digest-key 1 md5 TSHOOTAnswer: on R1 need comand in router modearea 12 authentication message-digestAns1) R1Ans2) ipv4 OSPFAns3) ip ospf authentication message-digest command must be given on s0/0/0T2:HSRP TRACKHSRP: DSW1 does not become active.conf on dw1:track 1 ip route 10.1.21.128 255.255.0.0 metric thresholdthreshold metric up 1 down 2track 10 ip route 10.2.21.128 255.255.255.0 metric thresholdthreshold metric up 63 down 64interface Vlan10ip address 10.2.1.1 255.255.255.0standby 10 ip 10.2.1.254standby 10 priority 200standby 10 preemptstandby 10 track 1 decrement 60Answer: (use IPv4 Layer 3 Topology)On dsw 1 interface vlan 10 mode run:no standby 10 track 1 decrement 60standby 10 track 10 decrement 60(ip for track command not exact for real exam)Ans1) DSW1Ans2) HSRPAns3) delete the command with track 1 and enter the command with track 10.T3:BGP NeighborProblem: R1 is not able to ping 209.65.200.226.configuration on R1:router bgp 65001no synchronizationbgp log-neighbor-changesnetwork 209.65.200.224 mask 255.255.255.252neighbor 209.56.200.226 remote-as 65002no auto-summarycheck bgp neighborship. **** show ip bgp sum****The neighbor’s address in the neighbor command is wrong under router BGP. (use ipv4 Layer 3) Answer: need change on router mode on R1 neighbor 209.65.200.226Ans1) R1Ans2) BGPAns3) delete the wrong neighbor statement and enter the correct neighbor address in the neighbor command (change 209.56.200.226 to 209.65.200.226)T4:NAT ACLClient is not able to ping the web server, but the routers can ping the server. NA T problem. (use ipv4 Layer 3)problem on R1 Nat aclAnswer:add to acl 1 permit ip 10.2.1.0 0.0.0.255Ans1) R1Ans2) IP NA TAns3) under NA T access list, enter the command permit 10.2.0.0 0.0.255.255T5:R1 ACLClient is not able to ping the server. Except for R1, no one else can ping the server. (use ipv4 Layer 3)Problem:on R1 acl blocking ipacl something like this:deny 10.2.1.0deny 10.1.4.0deny 10.1.1.0Answer: add permit 209.65.200.224 0.0.0.3command to R1′s ACLAns1) R1Ans2) IPv4 Layer3 SecurityAns3) Add permit 209.65.200.224 0.0.0.3 to R1′s ACLT6: VLAN filterClient 1 is not able to ping the server. Unable to ping DSW1(Use L2 Diagram).Vlan Access map is applied on DSW1 blocking the ip address of client 10.2.1.3Ans1) DSW1Ans2) Vlan access mapAns3)No vlan filter 10T7:Port SecurityClient 1 is not able to ping the serverSituation: Unable to ping DSW1(User layer 2).On ASW1 portsecurity mac 0000.0000.0001, interface in err-disable stateAnswer:on asw1 delele portsecurity & do on interfaces shutdown, no shutdownAns1)ASW1Ans2)Port securityAns3)On fa1/0/1 and fa1/0/2 do disable port security and do shut, no shut.T8:SWItchport vlan 10Client 1 is not able to ping the serverSituation: Unable to ping DSW1 & in port channel configuratioin of ASW1 vlan 10 is not allowed. (Use L2 Diagram)On ASW1, on interfaces fa0/1, fa0/2 switchport access vlan 1Answer: on ASW1 change switchport access vlan 1 to switchport access vlan 10Ans1)ASW1Ans2)Access vlanAns3)give command: interface range fa1/0/1-/2 switchport access vlan 10T9:Switchport trunk.cant ping to web server 209.65.200.241Situation: Unable to ping DSW1 & in port channel configuratioin of ASW1 vlan 10 is not allowed. (Use L2 Diagram)question was about EtherChanelclient can’t obtain ip address(169.x.x.x)on ASW1 trunks allow vlan 20,200Answ: on port channel 13, 23 disables all vlans and give switchport trunk allowed vlan 10,200 Ans1)ASW1Ans2)Switch to switch connectivityAns3)int range portchannel13,portchannel23switchport trunk allowed vlan noneswitchport trunl allowed vlan 10,200T10:Eigrp asClient 1 is not able to ping the serverSituation: Unable to ping R4 fast ethernet port from dsw1.Check ip eigrp neighbors from DSW1 you will not see R4 as neighbor.(use ipv4 Layer 3)On DSW1 & DWS2 the EIGRP AS number is 10 (router eigrp 10) but on R4 it is 1 (router eigrp 1)Answ: change router AS on R4 from 1 to 10Ans1) R4Ans2) IP4 EIGRPAns3) Change eigrp AS number from 1 to 10T11:eitrp to ospfClient 1 is not able to ping the serverSituation: Unable to ping serial interface of R4 from the clients.On R4 in router eigrp:redistribute ospf 1 route-map EIGRP_to_OSPFBUT route-map was named:route-map EIGRP->OSPFAnswer:change in router eigrp router-map nameAns1) R4Ans2) route redistributionAns3) change the name of the route-map under the router EIGRP or router OSPF process from ‘to’to ‘->’.T12:IPV6 ospfIPV6 loopback of R2 cannot be pinged from DSW1’s loopback.Situation: ipv6 ospf was not enabled on R2’s serial interface connecting to R3. (use ipv6 Layer 3) Answer:interface configuration mode:ipv6 ospf 6 area 12Ans1) R2Ans2) IPV6 ospfAns3) on the serial interface of R2, enter the command ipv6 ospf 6 area 0 (make sure to check the IPV6 topology before choose Answer 3 because the options look similar)Device Error DescriptionASW11. Access port not in VLAN 102. Port Channel not allowing VLAN 103. Port SecurityDSW1 1. HSRP track 102. VLAN filterR1 1. Wrong IP of BGP neighbor2. NAT – Access list3. Redistribute access-listR2 1. IPv6: enable OSPF2. OSPF AuthenticationR4 1. EIGRP – wrong AS2. Redistribute (“to” & -> )1、access vlan的vlan 给错了2、port-security导致端口被errdisable3、V ACL4、EIGRP的AS号配置错误5、OSPF的authentication有问题,6、OSPF到EIGRP的redistribut的route-map名字写过了7、NA T的inside pool没有包含client的网段8、BGP的neighbor ip写错了,209.65.200.226写成了209.56.200.2269、到ISP的出接口的ACL少了一条permit10、其中一台接入交换机的Trunk allowed的VLAN少了VLAN 1011、HSRP的track语句指定有问题12、IPV6,R2的其中一个接口没有enable IPV6 OSPF。
最新IT认证 CCNP 642-813认证考试题库

pdf文档可能在WAP端浏览体验不佳。建议您优先选择TXT,或下载源文件到本机查看。
The safer , easier way to help you pass any IT exams.
3/9
The safer , easier way to help you pass any IT exams.
A. 20 percent of the traffic on a network segment should be local B. no more than 20 percent of the network traffic should be able to move across a backbone. C. no more than 80 percent of the network traffic should be able to move across a backbone. D. 80 percent of the traffic on a network segment should be local Answer: B,D 8.The Company LAN is becoming saturated with broadcasts and multicast traffic. What could you do to help a network with many multicasts and broadcasts? A. Creating smaller broadcast domains by implementing VLANs. B. Separate nodes into different hubs. C. Creating larger broadcast domains by implementing VLANs. D. Separate nodes into different switches. E. All of the above. Answer: A 9.The Company LAN switches are being configured to support the use of Dynamic VLANs. Which of the following are true of dynamic VLAN membership? (Select all that apply) A. VLAN membership of a user always remains the same even when he/she is moved to another location. B. VLAN membership of a user always changes when he/she is moved to another location. C. Membership can be static or dynamic. D. Membership can be static only. E. None of the other alternatives apply. Answer: A,C 10.The Company LAN switches are being configured to support the use of Dynamic VLANs. What should be considered when implementing a dynamic VLAN solution? (Select two) A. Each switch port is assigned to a specific VLAN. B. Dynamic VLANs require a VLAN Membership Policy Server. C. Devices are in the same VLAN regardless of which port they attach to. D. Dynamic VLAN assignments are made through the command line interface. Answer: B,C 11.In the three-layer hierarchical network design model; what's associated with the access layer? (Select two) A. optimized transport structure B. high port density C. boundary definition D. data encryption E. local VLANs F. route summaries Answer: B,E 12.You are assigning VLANs to the ports of switch R1. What VLAN number value is an assigned to
CCNP测试题(修改版)
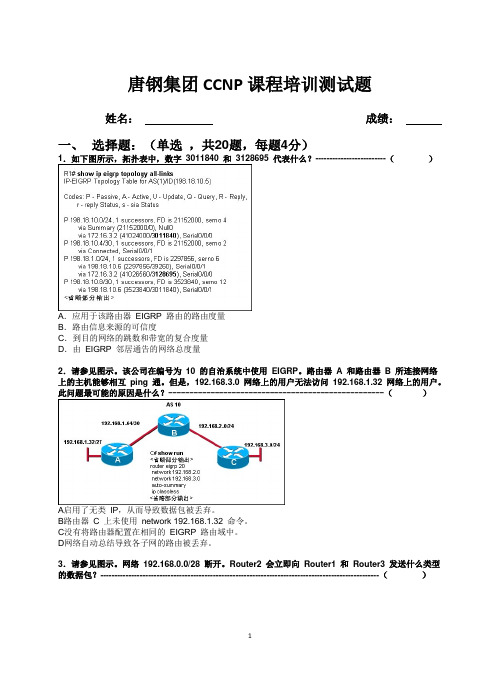
唐钢集团CCNP课程培训测试题姓名:成绩:一、选择题:(单选,共20题,每题4分)1.如下图所示,拓扑表中,数字3011840 和3128695 代表什么?-------------------------()A.应用于该路由器EIGRP 路由的路由度量B.路由信息来源的可信度C.到目的网络的跳数和带宽的复合度量D.由EIGRP 邻居通告的网络总度量2.请参见图示。
该公司在编号为10 的自治系统中使用EIGRP。
路由器A 和路由器B 所连接网络上的主机能够相互ping 通。
但是,192.168.3.0 网络上的用户无法访问192.168.1.32 网络上的用户。
此问题最可能的原因是什么?---------------------------------------------------()A启用了无类IP,从而导致数据包被丢弃。
B路由器C 上未使用network 192.168.1.32 命令。
C没有将路由器配置在相同的EIGRP 路由域中。
D网络自动总结导致各子网的路由被丢弃。
3.请参见图示。
网络192.168.0.0/28 断开。
Router2 会立即向Router1 和Router3 发送什么类型的数据包?---------------------------------------------------------------------------------------------------()A查询网络192.168.0.0/28 的查询数据包B到224.0.0.9 的确认数据包C发送到255.255.255.255 的更新数据包D包含R2 新路由表的数据包发送到192.168.1.1 和192.168.2.1 的单播更新数据包4.请参见图示。
所有接口都已配置为如图所示的带宽。
假设所有路由器都是使用默认的EIGRP 配置作为路由协议,那么从172.16.1.0/16 网络发往192.168.200.0/24 网络的数据包会采用哪一条路径?--------------------------------------------------------------------------------------------------------------------()A. A-B-EB. A-C-EC. A-D-ED.数据包会在A、B、E 和A、C、E 路径之间实施负载均衡。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
CCNP级别网络工程师知识点汇总
------------------------------面试题
1、解决路由环问题的方法有(ABD) A. 水平分割 B. 路由保持法 C. 路由器重启
D. 定义路由权的最大值
2、下面哪一项正确描述了路由协议(C) A. 允许数据包在主机间传送的一种协议 B. 定义数据包中域的格式和用法的一种方式
C. 通过执行一个算法来完成路由选择的一种协议
D. 指定MAC地址和IP地址捆绑的方式和时间的一种协议 3、以下哪些内容是路由信息中所不包含的(A) A. 源地址 B. 下一跳 C. 目标网络
D. 路由权值
4、以下说法那些是正确的(BD)
A. 路由优先级与路由权值的计算是一致的
B. 路由权的计算可能基于路径某单一特性计算,也可能基于路径多种属性
C. 如果几个动态路由协议都找到了到达同一目标网络的最佳路由,这几条路由都会被加入路由表中
D. 动态路由协议是按照路由的路由权值来判断路由的好坏,并且每一种路由协议的判断方法都是不一样的 5、IGP的作用范围是(C) A. 区域内 B. 局域网内 C. 自治系统内 D. 自然子网范围内
6、距离矢量协议包括(AB) A. RIP B. BGP C. IS-IS D. OSPF
7、关于矢量距离算法以下那些说法是错误的(A) A. 矢量距离算法不会产生路由环路问题 B. 矢量距离算法是靠传递路由信息来实现的
C. 路由信息的矢量表示法是(目标网络,metric)
D. 使用矢量距离算法的协议只从自己的邻居获得信息
求职胜经/简历亮出你的精彩简历写作技巧,...面试前准备才是...
8、如果一个内部网络对外的出口只有一个,那么最好配置(A) A. 缺省路由 B. 主机路由 C. 动态路由 9、BGP是在(D)之间传播路由的协议 A. 主机 B. 子网
C. 区域(area)
D. 自治系统(AS)
10、在路由器中,如果去往同一目的地有多条路由,则决定最佳路由的因素有(AC) A. 路由的优先级 B. 路由的发布者 C. 路由的metirc值 D. 路由的生存时间 11、在RIP协议中,计算metric值的参数是(D) A. MTU B. 时延 C. 带宽
D. 路由跳数
12、路由协议存在路由自环问题(A) A. RIP B. BGP C. OSPF D. IS-IS
13、下列关于链路状态算法的说法正确的是:(bc ) A. 链路状态是对路由的描述
B. 链路状态是对网络拓扑结构的描述
C. 链路状态算法本身不会产生自环路由
D. OSPF 和RIP都使用链路状态算法
14、在OSPF同一区域(区域A)内,下列说法正确的是(d ) A. 每台路由器生成的LSA都是相同的
B. 每台路由器根据该最短路径树计算出的路由都是相同的
C. 每台路由器根据该LSDB 计算出的最短路径树都是相同的
D. 每台路由器的区域A的LSDB(链路状态数据库)都是相同的 15、在一个运行OSPF的自治系统之内:(ad ) A. 骨干区域自身也必须是连通的 B. 非骨干区域自身也必须是连通的
C. 必须存在一个骨干区域 ( 区域号为0 )
D. 非骨干区域与骨干区域必须直接相连或逻辑上相连
16、下列关于OSPF协议的说法正确的是:(abd ) A. OSPF支持基于接口的报文验证
B. OSPF支持到同一目的地址的多条等值路由
C. OSPF是一个基于链路状态算法的边界网关路由协议
D. OSPF发现的路由可以根据不同的类型而有不同的优先级 17、禁止 RIP 协议的路由聚合功能的命令是(c ) A. undo rip B. auto-summany
C. undo auto-summany
D. undo network 10.0.0.0
18、下列静态路由配置正确的是
(d) A. ip route 129.1.0.0 16 serial 0 B. ip route 10.0.0.2 16 129.1.0.0 C. ip route 129.1.0.0 16
10.0.0.2
D. ip route 129.1.0.0 255.255.0.0 10.0.0.2 19、以下不属于动态路由协议的是(d) A. RIP B. ICMP C. IS-IS
D. OSPf
20、三种路由协议RIP 、OSPF 、BGP和静态路由各自得到了一条到达目标网络,在华为路由器默认情况下,最终选选定(b) 路由作为最优路由 A. RIP B. OSPF C. BGP
D. 静态路由 21、IGP 包括如下哪些协议(acd) A. RIP B. BGP C. IS-IS D. OSPF
22、路由环问题会引起(abd ) A. 慢收敛 B. 广播风暴 C. 路由器重起
D. 路由不一致
23、以下哪些路由表项要由网络管理员手动配置(a ) A. 静态路由
B. 直接路由
C. 动态路由
D. 以上说法都不正确
24、在运行Windows98的计算机中配置网关,类似于在路由器中配置(a) A. 直接路由 B. 默认路由 C. 动态路由 D. 间接路由
25、关于RIP协议,下列说法正确的有:(ac ) A. RIP协议是一种IGP B. RIP协议是一种EGP
C. RIP协议是一种距离矢量路由协议
D. RIP协议是一种链路状态路由协议。
