ASA5510防火墙配置手册
2019年思科5510防火墙-范文模板 (14页)
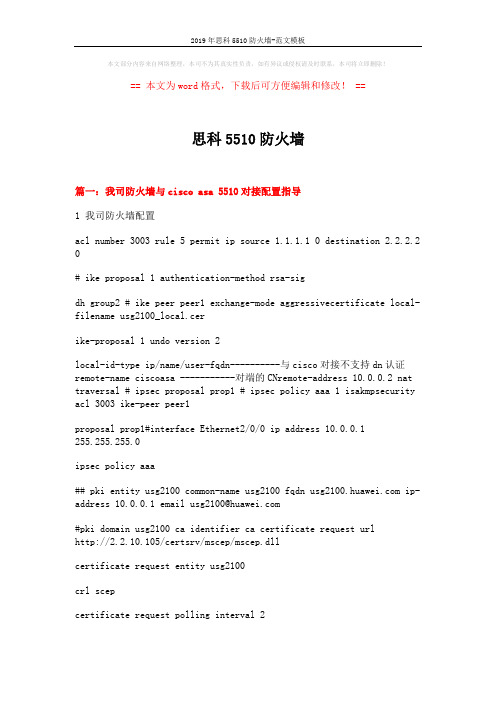
本文部分内容来自网络整理,本司不为其真实性负责,如有异议或侵权请及时联系,本司将立即删除!== 本文为word格式,下载后可方便编辑和修改! ==思科5510防火墙篇一:我司防火墙与cisco asa 5510对接配置指导1 我司防火墙配置acl number 3003 rule 5 permit ip source 1.1.1.1 0 destination 2.2.2.2 0# ike proposal 1 authentication-method rsa-sigdh group2 # ike peer peer1 exchange-mode aggressivecertificate local-filename usg2100_local.cerike-proposal 1 undo version 2local-id-type ip/name/user-fqdn----------与cisco对接不支持dn认证remote-name ciscoasa -----------对端的CNremote-address 10.0.0.2 nat traversal # ipsec proposal prop1 # ipsec policy aaa 1 isakmpsecurity acl 3003 ike-peer peer1proposal prop1#interface Ethernet2/0/0 ip address 10.0.0.1255.255.255.0ipsec policy aaa## pki entity usg2100 common-name usg2100 fqdn ip-address 10.0.0.1 email usg2100@#pki domain usg2100 ca identifier ca certificate request urlhttp://2.2.10.105/certsrv/mscep/mscep.dllcertificate request entity usg2100crl scepcertificate request polling interval 2crl update-period 1crl auto-update enablecrl url http://2.2.10.105/certsrv/mscep/mscep.dll#2 CISCO配置2.1 设备型号Hardware:ASA5510, 256 MB RAM, CPU Pentium 4 Celeron 1600 MHzCisco Adaptive Security Appliance Software Version 8.4(1)版本不同将导致配置略有差别。
CISCOASA5510配置手册

CISCOASA5510 // OKciscoasa#showverCiscoAdaptiveSecurityApplianceSoftwareVersion7.2(4) DeviceManagerVersion5.2(4)CompiledonSun06-Apr-0813:39bybuildersSystemimagefileis"disk0:/asa724-k8.bin" Configfileatbootwas"startup-config"ciscoasaup3mins5secsHardware:ASA5520,512MBRAM,CPUPentium4Celeron2000MHz InternalATACompactFlash,256MBBIOSFlashFirmwareHub@0xffe00000,1024KBEncryptionhardwaredevice:CiscoASA-55x0on-boardaccelerator(revision0x0) Bootmicrocode:CNlite-MC-Boot-Cisco-1.2SSL/IKEmicrocode:CNlite-MC-IPSEC-Admin-3.03IPSecmicrocode:CNlite-MC-IPSECm-MAIN-2.050:Ext:GigabitEthernet0/0:addressisc47d.4f85.1708,irq91:Ext:GigabitEthernet0/1:addressisc47d.4f85.1709,irq92:Ext:GigabitEthernet0/2:addressisc47d.4f85.170a,irq93:Ext:GigabitEthernet0/3:addressisc47d.4f85.170b,irq94:Ext:Management0/0:addressisc47d.4f85.1707,irq115:Int:Notused:irq116:Int:Notused:irq5MaximumVLANs:150InsideHosts:UnlimitedFailover:Active/ActiveVPN-DES:EnabledVPN-3DES-AES:DisabledSecurityContexts:2GTP/GPRS:DisabledVPNPeers:750WebVPNPeers:2ThisplatformhasanASA5520VPNPluslicense.SerialNumber:JMX1406L0Y6RunningActivationKey:0x6a2659550xf07c223d0x2cf345f40xb34478840xc128879b Configurationregisteris0x1Configurationlastmodifiedbyenable_15at12:23:52.072UTCMonSep62010 ciscoasa#showrun:Saved:ASAVersion7.2(4)!hostnameciscoasadomain-namedefault.domain.invalidenablepasswordgfFm2E3sthJOc7bqencryptedpasswd2KFQnbNIdI.2KYOUencryptednames!interfaceGigabitEthernet0/0nameifuntrust!interfaceGigabitEthernet0/1 nameifdmzsecurity-level50ipaddress172.18.19.254255.255.255.0!interfaceGigabitEthernet0/2 nameiftrustsecurity-level100ipaddress172.18.1.1255.255.255.0!interfaceGigabitEthernet0/3nonameifnosecurity-levelnoipaddress!interfaceManagement0/0 nameifmanagementsecurity-level100ipaddress192.168.1.1255.255.255.0 management-only!ftpmodepassivednsserver-groupDefaultDNSdomain-namedefault.domain.invalid access-list102extendedpermiticmpanyany access-list102extendedpermitipanyany pagerlines24loggingenablemtudmz1500mtutrust1500mtumanagement1500nofailovericmpunreachablerate-limit1burst-size1asdmimagedisk0:/ASDM-524.BINnoasdmhistoryenablearptimeout14400global(untrust)1interfacenat(trust)10.0.0.00.0.0.0static(trust,untrust)tcp113.105.88.5786172.18.11.886netmask255.255.255.255static(trust,untrust)tcp113.105.88.575000172.18.11.85000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.586800172.18.11.1306800netmask255.255.255.255 static(trust,untrust)tcp113.105.88.584800172.18.11.1304800netmask255.255.255.255 static(trust,untrust)tcp113.105.88.583306172.18.11.1303306netmask255.255.255.255 static(trust,untrust)udp113.105.88.586800172.18.11.1306800netmask255.255.255.255 static(trust,untrust)udp113.105.88.584800172.18.11.1304800netmask255.255.255.255 static(trust,untrust)udp113.105.88.583306172.18.11.1303306netmask255.255.255.255 static(trust,untrust)tcp113.105.88.5881172.18.11.13081netmask255.255.255.255 static(trust,untrust)udp113.105.88.5881172.18.11.13081netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601011172.18.11.91011netmask255.255.255.255 static(trust,untrust)udp113.105.88.601011172.18.11.91011netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601018172.18.11.91018netmask255.255.255.255 static(trust,untrust)udp113.105.88.601018172.18.11.91018netmask255.255.255.255 static(trust,untrust)tcp113.105.88.5981172.18.15.99wwwnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.592000172.18.15.992000netmask255.255.255.255 static(trust,untrust)udp113.105.88.592000172.18.15.992000netmask255.255.255.255 static(trust,untrust)udp113.105.88.59www172.18.15.99wwwnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.598080172.18.15.998080netmask255.255.255.255static(trust,untrust)tcp113.105.88.59ftp-data172.18.11.123ftp-datanetmask255.255.255.255 static(trust,untrust)tcp113.105.88.59ftp172.18.11.123ftpnetmask255.255.255.255static(trust,untrust)tcp113.105.88.59telnet172.18.11.123telnetnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.591010172.18.11.1231000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598003172.18.11.1238003netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598010172.18.11.1238010netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598012172.18.11.1238012netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598880172.18.11.1238880netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601012172.18.11.91012netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601013172.18.11.91013netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601014172.18.11.91014netmask255.255.255.255 static(trust,untrust)udp113.105.88.601012172.18.11.91012netmask255.255.255.255 static(trust,untrust)udp113.105.88.601013172.18.11.91013netmask255.255.255.255 static(trust,untrust)udp113.105.88.601014172.18.11.91014netmask255.255.255.255 static(trust,untrust)tcp113.105.88.595000172.18.15.995000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.594000172.18.15.994000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602000172.18.11.92000netmask255.255.255.255 static(trust,untrust)udp113.105.88.602000172.18.11.92000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.592009172.18.15.992009netmask255.255.255.255 static(trust,untrust)udp113.105.88.592009172.18.15.992009netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598081172.18.15.998081netmask255.255.255.255 static(trust,untrust)udp113.105.88.598081172.18.15.998081netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602001172.18.11.92001netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602002172.18.11.92002netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602003172.18.11.92003netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602004172.18.11.92004netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602005172.18.11.92005netmask255.255.255.255static(trust,untrust)tcp113.105.88.602010172.18.11.92010netmask255.255.255.255 static(trust,untrust)udp113.105.88.602001172.18.11.92001netmask255.255.255.255 static(trust,untrust)udp113.105.88.602002172.18.11.92002netmask255.255.255.255 static(trust,untrust)udp113.105.88.602003172.18.11.92003netmask255.255.255.255 static(trust,untrust)udp113.105.88.602004172.18.11.92004netmask255.255.255.255 static(trust,untrust)udp113.105.88.602005172.18.11.92005netmask255.255.255.255 static(trust,untrust)udp113.105.88.602006172.18.11.92006netmask255.255.255.255 static(trust,untrust)udp113.105.88.602007172.18.11.92007netmask255.255.255.255 static(trust,untrust)udp113.105.88.602008172.18.11.92008netmask255.255.255.255 static(trust,untrust)udp113.105.88.602009172.18.11.92009netmask255.255.255.255 static(trust,untrust)udp113.105.88.602010172.18.11.92010netmask255.255.255.255 static(trust,untrust)113.105.88.61172.18.11.10netmask255.255.255.255access-group102ininterfaceuntrustrouteuntrust0.0.0.00.0.0.010.92.8.91routetrust172.18.11.0255.255.255.0172.18.1.21routetrust172.18.12.0255.255.255.0172.18.1.21routetrust172.18.13.0255.255.255.0172.18.1.21routetrust172.18.14.0255.255.255.0172.18.1.21routetrust172.18.15.0255.255.255.0172.18.1.21routetrust172.18.16.0255.255.255.0172.18.1.21routetrust172.18.17.0255.255.255.0172.18.1.21routetrust172.18.18.0255.255.255.0172.18.1.21timeoutxlate3:00:00timeoutconn1:00:00half-closed0:10:00udp0:02:00icmp0:00:02timeoutsunrpc0:10:00h3230:05:00h2251:00:00mgcp0:05:00mgcp-pat0:05:00 timeoutsip0:30:00sip_media0:02:00sip-invite0:03:00sip-disconnect0:02:00 timeoutsip-provisional-media0:02:00uauth0:05:00absolutenosnmp-serverlocationnosnmp-servercontactsnmp-serverenabletrapssnmpauthenticationlinkuplinkdowncoldstart telnet0.0.0.00.0.0.0trusttelnettimeout5ssh0.0.0.00.0.0.0untrustsshtimeout30consoletimeout0usernameadminpasswordf3UhLvUj1QsXsuK7encrypted!!prompthostnamecontextCryptochecksum:634aa0023e75546939c8b013c69a61b7:endciscoasa#showstartciscoasa#showstartup-config:Saved:Writtenbyenable_15at12:24:22.081UTCMonSep62010!ASAVersion7.2(4)!hostnameciscoasadomain-namedefault.domain.invalidenablepasswordgfFm2E3sthJOc7bqencryptedpasswd2KFQnbNIdI.2KYOUencryptednames!interfaceGigabitEthernet0/0nameifuntrust!interfaceGigabitEthernet0/1 nameifdmzsecurity-level50ipaddress172.18.19.254255.255.255.0!interfaceGigabitEthernet0/2 nameiftrustsecurity-level100ipaddress172.18.1.1255.255.255.0!interfaceGigabitEthernet0/3nonameifnosecurity-levelnoipaddress!interfaceManagement0/0 nameifmanagementsecurity-level100ipaddress192.168.1.1255.255.255.0 management-only!ftpmodepassivednsserver-groupDefaultDNSdomain-namedefault.domain.invalid access-list102extendedpermiticmpanyany access-list102extendedpermitipanyany pagerlines24loggingenablemtudmz1500mtutrust1500mtumanagement1500nofailovericmpunreachablerate-limit1burst-size1asdmimagedisk0:/ASDM-524.BINnoasdmhistoryenablearptimeout14400global(untrust)1interfacenat(trust)10.0.0.00.0.0.0static(trust,untrust)tcp113.105.88.5786172.18.11.886netmask255.255.255.255static(trust,untrust)tcp113.105.88.575000172.18.11.85000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.586800172.18.11.1306800netmask255.255.255.255 static(trust,untrust)tcp113.105.88.584800172.18.11.1304800netmask255.255.255.255 static(trust,untrust)tcp113.105.88.583306172.18.11.1303306netmask255.255.255.255 static(trust,untrust)udp113.105.88.586800172.18.11.1306800netmask255.255.255.255 static(trust,untrust)udp113.105.88.584800172.18.11.1304800netmask255.255.255.255 static(trust,untrust)udp113.105.88.583306172.18.11.1303306netmask255.255.255.255 static(trust,untrust)tcp113.105.88.5881172.18.11.13081netmask255.255.255.255 static(trust,untrust)udp113.105.88.5881172.18.11.13081netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601011172.18.11.91011netmask255.255.255.255 static(trust,untrust)udp113.105.88.601011172.18.11.91011netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601018172.18.11.91018netmask255.255.255.255 static(trust,untrust)udp113.105.88.601018172.18.11.91018netmask255.255.255.255 static(trust,untrust)tcp113.105.88.5981172.18.15.99wwwnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.592000172.18.15.992000netmask255.255.255.255 static(trust,untrust)udp113.105.88.592000172.18.15.992000netmask255.255.255.255 static(trust,untrust)udp113.105.88.59www172.18.15.99wwwnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.598080172.18.15.998080netmask255.255.255.255static(trust,untrust)udp113.105.88.598000172.18.11.1238000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.596999172.18.11.1236999netmask255.255.255.255 static(trust,untrust)tcp113.105.88.59ftp-data172.18.11.123ftp-datanetmask255.255.255.255 static(trust,untrust)tcp113.105.88.59ftp172.18.11.123ftpnetmask255.255.255.255static(trust,untrust)tcp113.105.88.59telnet172.18.11.123telnetnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.591010172.18.11.1231000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598003172.18.11.1238003netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598010172.18.11.1238010netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598012172.18.11.1238012netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598880172.18.11.1238880netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601012172.18.11.91012netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601013172.18.11.91013netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601014172.18.11.91014netmask255.255.255.255 static(trust,untrust)udp113.105.88.601012172.18.11.91012netmask255.255.255.255 static(trust,untrust)udp113.105.88.601013172.18.11.91013netmask255.255.255.255 static(trust,untrust)udp113.105.88.601014172.18.11.91014netmask255.255.255.255 static(trust,untrust)tcp113.105.88.595000172.18.15.995000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.594000172.18.15.994000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602000172.18.11.92000netmask255.255.255.255 static(trust,untrust)udp113.105.88.602000172.18.11.92000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.592009172.18.15.992009netmask255.255.255.255 static(trust,untrust)udp113.105.88.592009172.18.15.992009netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598081172.18.15.998081netmask255.255.255.255 static(trust,untrust)udp113.105.88.598081172.18.15.998081netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602001172.18.11.92001netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602002172.18.11.92002netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602003172.18.11.92003netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602004172.18.11.92004netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602005172.18.11.92005netmask255.255.255.255static(trust,untrust)tcp113.105.88.602008172.18.11.92008netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602009172.18.11.92009netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602010172.18.11.92010netmask255.255.255.255 static(trust,untrust)udp113.105.88.602001172.18.11.92001netmask255.255.255.255 static(trust,untrust)udp113.105.88.602002172.18.11.92002netmask255.255.255.255 static(trust,untrust)udp113.105.88.602003172.18.11.92003netmask255.255.255.255 static(trust,untrust)udp113.105.88.602004172.18.11.92004netmask255.255.255.255 static(trust,untrust)udp113.105.88.602005172.18.11.92005netmask255.255.255.255 static(trust,untrust)udp113.105.88.602006172.18.11.92006netmask255.255.255.255 static(trust,untrust)udp113.105.88.602007172.18.11.92007netmask255.255.255.255 static(trust,untrust)udp113.105.88.602008172.18.11.92008netmask255.255.255.255 static(trust,untrust)udp113.105.88.602009172.18.11.92009netmask255.255.255.255 static(trust,untrust)udp113.105.88.602010172.18.11.92010netmask255.255.255.255 static(trust,untrust)113.105.88.61172.18.11.10netmask255.255.255.255access-group102ininterfaceuntrustrouteuntrust0.0.0.00.0.0.010.92.8.91routetrust172.18.11.0255.255.255.0172.18.1.21routetrust172.18.12.0255.255.255.0172.18.1.21routetrust172.18.13.0255.255.255.0172.18.1.21routetrust172.18.14.0255.255.255.0172.18.1.21routetrust172.18.15.0255.255.255.0172.18.1.21routetrust172.18.16.0255.255.255.0172.18.1.21routetrust172.18.17.0255.255.255.0172.18.1.21routetrust172.18.18.0255.255.255.0172.18.1.21timeoutxlate3:00:00timeoutconn1:00:00half-closed0:10:00udp0:02:00icmp0:00:02timeoutsunrpc0:10:00h3230:05:00h2251:00:00mgcp0:05:00mgcp-pat0:05:00 timeoutsip0:30:00sip_media0:02:00sip-invite0:03:00sip-disconnect0:02:00 timeoutsip-provisional-media0:02:00uauth0:05:00absolutehttpserverenablehttp0.0.0.00.0.0.0trustnosnmp-serverlocationnosnmp-servercontactsnmp-serverenabletrapssnmpauthenticationlinkuplinkdowncoldstart telnet0.0.0.00.0.0.0trusttelnettimeout5ssh0.0.0.00.0.0.0untrustsshtimeout30consoletimeout0usernameadminpasswordf3UhLvUj1QsXsuK7encrypted!!prompthostnamecontextCryptochecksum:634aa0023e75546939c8b013c69a61b7 ciscoasa#。
ASA5510防火墙配置手册
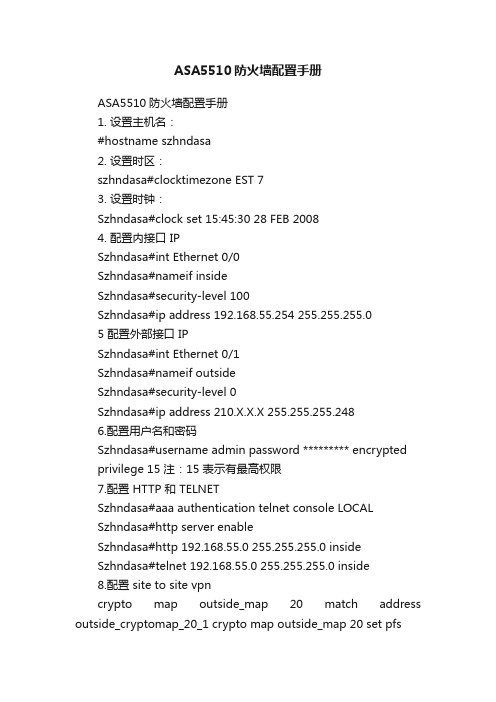
ASA5510防火墙配置手册ASA5510防火墙配置手册1. 设置主机名:#hostname szhndasa2. 设置时区:szhndasa#clocktimezone EST 73. 设置时钟:Szhndasa#clock set 15:45:30 28 FEB 20084. 配置内接口 IPSzhndasa#int Ethernet 0/0Szhndasa#nameif insideSzhndasa#security-level 100Szhndasa#ip address 192.168.55.254 255.255.255.05 配置外部接口 IPSzhndasa#int Ethernet 0/1Szhndasa#nameif outsideSzhndasa#security-level 0Szhndasa#ip address 210.X.X.X 255.255.255.2486.配置用户名和密码Szhndasa#username admin password ********* encryptedprivilege 15 注:15 表示有最高权限7.配置 HTTP 和 TELNETSzhndasa#aaa authentication telnet console LOCALSzhndasa#http server enableSzhndasa#http 192.168.55.0 255.255.255.0 insideSzhndasa#telnet 192.168.55.0 255.255.255.0 inside8.配置 site to site vpncrypto map outside_map 20 match address outside_cryptomap_20_1 crypto map outside_map 20 set pfscrypto map outside_map 20 set peer 210.75.1.Xcrypto map outside_map 20 set transform-set ESP-3DES-SHAcrypto map outside_map 20 set nat-t-disablecrypto map outside_map interface outside注:还可通过 http 方式用 ASDM 管理软件图形化配置 ASA[原创] CISCO ASA 防火墙 IOS恢复与升级简明教程!客户的误操作,把ios给删了,这下麻烦到我了。
asa5510限速等配置

gametuzi(config)# hostname gametuzi5510 新的名字
gametuzi5510(config)# int e0/0 进入E0/0 接口
gametuzi5510(config-if)# security-level 0 配置安全级别 因为是外部接口,安全级别为最高
拓扑图如下:
限速配置如下:
access-list rate_limit_1 extended permit ip any host 192.168.1.2 //(限制192.168.1.2下载)
access-list rate_limit_1 extended permit ip host 192.168.1.2 any //(限制192.168.1.2上传)
gametuzi5510# conf t
gametuzi5510(config)# global (outside) 1 interface PAT地址转换!
gametuzi5510(config)# end
gametuzi5510# conf t
gametuzi5510(config)# route outside 0.0.0.0 0.0.0.0 192.168.3.254 默认路由 访问所有外部地址从192.168.3.254 流出。
Ciscoasa(config)#access-group 100 in intercae outside per-user-override
访问必须调用ACL
备注如果,只是需要将内网一个服务器映射到公网可以这样做
ciscoasa(config)#static (inside, outside) 219.139.*.* 192.168.16.254
ASA5510配置实例1
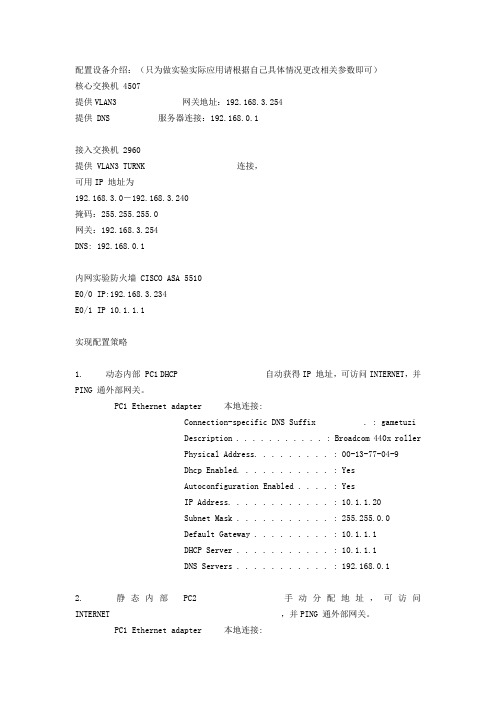
配置设备介绍:(只为做实验实际应用请根据自己具体情况更改相关参数即可)核心交换机 4507提供VLAN3 网关地址:192.168.3.254提供 DNS 服务器连接:192.168.0.1接入交换机 2960提供 VLAN3 TURNK 连接,可用IP 地址为192.168.3.0-192.168.3.240掩码:255.255.255.0网关:192.168.3.254DNS: 192.168.0.1内网实验防火墙 CISCO ASA 5510E0/0 IP:192.168.3.234E0/1 IP 10.1.1.1实现配置策略1. 动态内部 PC1 DHCP 自动获得IP 地址,可访问INTERNET,并PING 通外部网关。
PC1 Ethernet adapter 本地连接:Connection-specific DNS Suffix . : gametuziDescription . . . . . . . . . . . : Broadcom 440x rollerPhysical Address. . . . . . . . . : 00-13-77-04-9Dhcp Enabled. . . . . . . . . . . : YesAutoconfiguration Enabled . . . . : YesIP Address. . . . . . . . . . . . : 10.1.1.20Subnet Mask . . . . . . . . . . . : 255.255.0.0Default Gateway . . . . . . . . . : 10.1.1.1DHCP Server . . . . . . . . . . . : 10.1.1.1DNS Servers . . . . . . . . . . . : 192.168.0.12. 静态内部 PC2 手动分配地址,可访问 INTERNET ,并PING 通外部网关。
ASA防火墙配置

ASA防火墙初始配置1.模式介绍“>”用户模式firewall>enable 由用户模式进入到特权模式password:“#”特权模式firewall#config t 由特权模式进入全局配置模式“(config)#”全局配置模式防火墙的配置只要在全局模式下完成就可以了。
2.接口配置(以5510以及更高型号为例,5505接口是基于VLAN的):interface Ethernet0/0nameif inside (接口的命名,必须!)security-level 100(接口的安全级别)ip address 10.0.0.10 255.255.255.0no shutinterface Ethernet0/1nameif outsidesecurity-level 0ip address 202.100.1.10 255.255.255.0no shut3.路由配置:默认路由:route outside 0 0 202.100.1.1 (0 0 为0.0.0.0 0.0.0.0)静态路由:route inside 192.168.1.0 255.255.255.0 10.0.0.15505接口配置:interface Ethernet0/0!interface Ethernet0/1switchport access vlan 2interface Vlan1nameif insidesecurity-level 100ip address 192.168.6.1 255.255.255.0!interface Vlan2nameif outsidesecurity-level 0ip address 202.100.1.10ASA防火墙NAT配置内网用户要上网,我们必须对其进行地址转换,将其转换为在公网上可以路由的注册地址,防火墙的nat和global是同时工作的,nat定义了我们要进行转换的地址,而global定义了要被转换为的地址,这些配置都要在全局配置模式下完成,Nat配置:firewall(config)# nat (inside) 1 0 0上面inside代表是要被转换得地址,1要和global 后面的号对应,类似于访问控制列表号,也是从上往下执行,0 0 代表全部匹配(第一个0代表地址,第二个0代表掩码),内部所有地址都回进行转换。
ASA5500-X身份防火墙与CDA配置指南
ASA5500-X身份防火墙与CDA配置指南一、目的 (1)二、网络拓扑 (1)三、CDA的安装与配置 (2)四、ASA5515-X安装CX模块 (4)五、Windows 2008 R2的配置 (8)六、ASA-CX的策略配置 (17)七、ASA-CX功能验证 (26)一、目的本文介绍了在ASA5515-X防火墙上,通过与思科Context Directory Agent(简称CDA)软件协同工作,实现基于身份的访问策略与控制。
主要内容包括以下几个部分::ASA5515-X上CX模块的安装与配置步骤。
CDA的安装与配置步骤。
Windows 2008 R2服务器与CDA配合时,需要的修改哪些内容。
二、网络拓扑以下是本次配置实例的网络拓扑图:三、CDA的安装与配置思科Context Directory Agent(简称CDA)是一套软件,ASA5515-X的CX模块通过CDA能够获取IP地址与用户身份的映射关系,从而可以在ASA-CX上实现基于用户身份的安全访问策略。
通过思科CCO可以下载获取CDA的ISO格式的软件。
CDA软件本身包含了操作系统,它可以安装在一台专用的x86服务器上,或者VMware的ESX或ESXi虚拟机上。
在VMWare 虚拟机上安装时,注意Guest OS类型要选择:Linux CentOS 4/5 32bit。
以下是将CDA安装在ESXi5.0服务器上的安装和配置步骤:步骤1:在CCO下载CDA软件:/download/type.html?mdfid=284143128&flowid=31442步骤2:在VMware ESXi5.0上安装CDA。
步骤3:完成安装后,在login提示符下输入setup,进行基本配置。
以下为配置举例:localhost.localdomain login: setupPress ‘Ctrl-C’ to abort setupEnter Hostname[]: cda-serverEnter IP address []: 10.10.10.83Enter IP netmask []: 255.255.255.0Enter IP default gateway []: 10.10.10.3Enter default DNS domain []: Enter primary nameserver []: 10.10.10.80Enter secondary nameserver? Y/N: nEnter primary NTP server []: 10.10.10.80Enter secondary NTP server? Y/N: nEnter system timezone [UTC]: Asia/ShanghaiEnter username [admin]: adminEnter password:Enter password again:Bringing up the network interface...Pinging the gateway...Pinging the primary nameserver...Do not use ‘Ctrl-C’ from this point on...Installing applications...Installing cda...Pre installPost InstallApplication bundle (cda) installed successfully=== Initial setup for application: cda ===Generating configuration...Rebooting...步骤4:打开浏览器,输入https://10.10.10.83,输入已经创建好的用户名和密码,登陆CDA的GUI页面。
cisco-asa-5505基本配置
cisco-asa-5505基本配置interface Vlan2nameif outside —--——---—------—-———-—————----—-—-—-—-—-对端口命名外端口security-level 0 --—-————-——-—--—-———-—-—————-----———----设置端口等级ip address X.X.X.X 255.255.255.224 ----—--——--————----—调试外网地址!interface Vlan3nameif inside -—---———---——----———————-—----———-----——对端口命名内端口security-level 100 ———-——----—-——-—---——-——--—-———--—-———--调试外网地址ip address 192。
168.1。
1 255.255.255。
0 ——-————--—————-----—设置端口等级!interface Ethernet0/0switchport access vlan 2 —-—-—-———-—--—--—-——----——--——-——-—-—---设置端口VLAN与VLAN2绑定!interface Ethernet0/1switchport access vlan 3 —-————--—----——-—-------——-—-—--——-——--—设置端口VLAN与VLAN3绑定!interface Ethernet0/2shutdown!interface Ethernet0/3shutdown!interface Ethernet0/4shutdown!interface Ethernet0/5shutdown!interface Ethernet0/6shutdown!interface Ethernet0/7shutdown!passwd 2KFQnbNIdI。
5510防火墙配置(尚阳)
.255.0
access-list nonat extended permit ip 10.1.1.0 255.255.255.0 192.168.25.0
255.255 .255.0
access-list nonat extended permit ip 10.80.1.0 255.255.255.0 192.168.25.0 255.25
ip address 10.1.5.1 255.255.255.248
!
interface Ethernet0/2
description to_Dianxing
nameif outside1
security-level 0
ip address 183.62.194.98 255.255.255.248
access-list split-ssl standard permit 10.1.7.0 255.255.255.0
access-list split-ssl standard permit 10.1.1.0 255.255.255.0
access-list split-ssl standard permit 10.10.1.0 255.255.255.0
!
interface Ethernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
nameif management
security-level 100
ip address 192.168.1.1 255.255.255.0management-only !
cisco ASA5510配置实例
cisco ASA5510配置实例2008年11月11日 07:52ASA5510# SHOW RUN: Saved:ASA Version 7.0(6)!hostname ASA5510enable password 2KFQnbNIdI.2KYOU encryptednamesdns-guard!interface Ethernet0/0 此接口为外部网络接口nameif outside 设置为 OUTSIDE 外部接口模式security-level 0 外部接口模式安全级别为最低 0ip address 192.168.3.234 255.255.255.0 添加外部IP地址(一般为电信/网通提供)!interface Ethernet0/1此接口为内部网络接口nameif inside设置为 INSIDE 内部接口模式security-level 100内部接口模式安全级别最高为 100ip address 10.1.1.1 255.255.0.0添加内部IP地址!interface Ethernet0/2 没用到shutdownno nameifno security-levelno ip address!interface Management0/0nameif managementsecurity-level 100ip address 192.168.1.1 255.255.255.0 没用,用网线连接管理的端口。
management-only!passwd 2KFQnbNIdI.2KYOU encryptedftp mode passivepager lines 24logging asdm informationalmtu outside 1500mtu inside 1500mtu management 1500no asdm history enablearp timeout 14400global (outside) 1 interface 一定要打表示 PAT端口扩展:“1”为其NAT ID nat (inside) 1 10.1.0.0 255.255.0.0 转换所有10.1.0.0 的内部地址route outside 0.0.0.0 0.0.0.0 192.168.3.254 1 缺省路由timeout xlate 3:00:00timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00timeout mgcp-pat 0:05:00 sip 0:30:00 sip_media 0:02:00timeout uauth 0:05:00 absolutehttp server enable 打开http serverhttp 192.168.1.0 255.255.255.0 management 限定能通过http方式访问防火墙的机器no snmp-server locationno snmp-server contactsnmp-server enable traps snmp authentication linkup linkdown coldstart telnet timeout 5ssh timeout 5console timeout 0dhcpd address 10.1.1.30-10.1.1.200 inside DHCP 自动提供分配范围为10.1.1.30-200dhcpd address 192.168.1.2-192.168.1.254 managementdhcpd dns 192.168.0.1 DNS 添加:可以是电信网通提供直接添加,或者自己的DNS服务器地址。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
ASA5510防火墙配置手册
1. 设置主机名:
#hostname szhndasa
2. 设置时区:
szhndasa#clock timezone EST 7
3. 设置时钟:
Szhndasa#clock set 15:45:30 28 FEB 2008
4. 配置内接口 IP
Szhndasa#int Ethernet 0/0
Szhndasa#nameif inside
Szhndasa#security-level 100
Szhndasa#ip address 192.168.55.254 255.255.255.0
5 配置外部接口 IP
Szhndasa#int Ethernet 0/1
Szhndasa#nameif outside
Szhndasa#security-level 0
Szhndasa#ip address 210.X.X.X 255.255.255.248
6.配置用户名和密码
Szhndasa#username admin password ********* encrypted
privilege 15 注:15 表示有最高权限
7.配置 HTTP 和 TELNET
Szhndasa#aaa authentication telnet console LOCAL
Szhndasa#http server enable
Szhndasa#http 192.168.55.0 255.255.255.0 inside
Szhndasa#telnet 192.168.55.0 255.255.255.0 inside
8.配置 site to site vpn
crypto map outside_map 20 match address outside_cryptomap_20_1 crypto map outside_map 20 set pfs
crypto map outside_map 20 set peer 210.75.1.X
crypto map outside_map 20 set transform-set ESP-3DES-SHA
crypto map outside_map 20 set nat-t-disable
crypto map outside_map interface outside
注:还可通过 http 方式用 ASDM 管理软件图形化配置 ASA
[原创] CISCO ASA 防火墙 IOS恢复与升级简明教程!
客户的误操作,把ios给删了,这下麻烦到我了。
说来恢复也不难,晚上找的一大堆,不过自己真正用来才发现有很多细节需要注意的。
小弟愚钝,花了2小时才搞定(QQ远程借助,我在北京,客户在包头),特把经验共享给大家。
1.从tftp上的ios启动防火墙
防火墙启动后 ,按“ESC”键进入监控模式
rommon #2> ADDRESS=192.168.1.116
rommon #3> GATEWAY=192.168.1.1
rommon #4> IMAGE=asa803-k8.bin
rommon #5> SERVER=192.168.1.1
rommon #6> sync
rommon #7> ping 192.168.1.1
Link is UP
Sending 20, 100-byte ICMP Echoes to 192.168.1.1, timeout is 4 seconds:
Success rate is 95 percent (20/20)
rommon #8> tftpdnld
tftp *********************.1.1 via 192.168.1.1
这就表明第一步成功了,等待从tftp进入防火墙吧。
2.把IOS从tftp考进防火墙
此时IOS也没有装入ASA,而是从tftp引导启动设备。
这一点当设备启动完毕后可以用show version命令看到:
System image file is "t ftp://192.168.1.1/asa803-k8.bin"
启动完毕后需要将tftp server连接到除带外管理接口以外的其它接口,然后再升级IOS 注意:配置IP地址。
命令很简单不用说了
但就是这接口需要注意一下
必须配置成 inside口
才能让你升级的,我在管理接口下折腾了半天都没搞好,换了口就OK了。
Asa#conf t
Asa(config)#int e0/0
Asa(config-if)#nameif inside
Asa(config-if)#ip add 192.168.1.116 255.255.255.0
Asa(config-if)#no sh
Asa#ping 192.168.1.1
通后就可以升级ios了
Asa5510#copy tftp: flash:
Tftp server IP address:192.168.1.1
Source file name:asa803-k8.bin
Destination file name:asa803-k8.bin
Asa5510#copy tftp: flash:
Tftp server IP address:192.168.1.1
Source file name:asdm-608.bin
Destination file name:asdm-608.bin
到这一步并没有结束,此时还需要进行boot system的设置
使用命令
Asa(config)#boot system disk0:/asa808-k8.bin
Asa(config)#asdm image disk0:/asdm-608.bin
Asa(config)#wr
然后reload一下就可以了
重启之后在dir查看一下,基本上就大功告成了。
