(完整版)计算机网络课后作业以及答案(中英文对照)
计算机网络课后习题解答中文版
解答:HDLC 和 PPP 协议的帧标志位 01111110,。0 比特位填充法用来确认一个数 据的的开始和结束。如果这里有五个连续的 1,发送方将会增加一个 0 作为填充 比特。如果接收方接收到 7 个连续的 1,那么在数据帧的尾部一定产生了差错。
因此,D = 2.048 * 5 + 2 * 6 + 1 * 5 + 1.024 * n B / 4Mbps = 27.24 ms + 1.024 * n B/4 Mbps
在电路交换中,总时延: D = 链路建立时延 +传输时延= 2 * 分组持续时间+ 传输时延 = 2 * (Tpkt * 5 + Tp * 6 3; (Tp * 6 + Tt )
CS: 没有影响
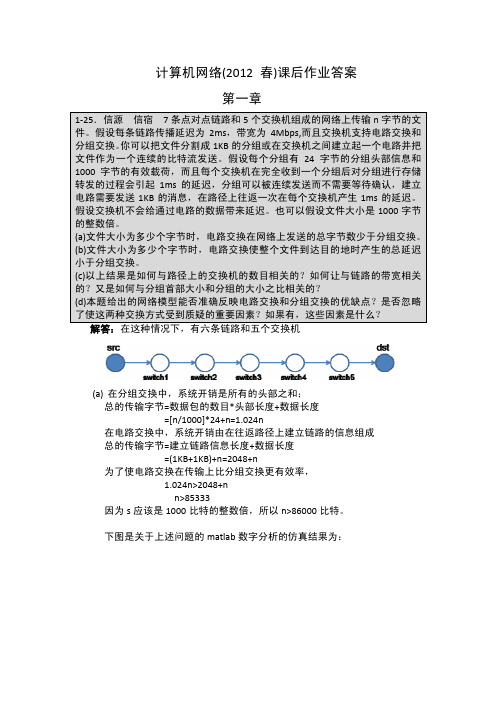
关于上述关于时延的影响的 matlab 仿真结果如下图:
(d)本题给出的网络模型能够准确反映电路交换和分组交换的优缺点。这里也 有很多被忽略了的因素,例如:
(i)交换机的存储量和数据处理能力,这能产生很多的时延; (ii)复杂的网络拓扑结构,这可能带来分组交换的多路径传输。
第二章
2-6.假设一条链路上到达比特序列 1101011111010111110010111110110,给出去掉任
电路交换的时延 = 2 * ((Tp + Tpkt +Ts)*k + (Tp + Tpkt )) + (Tp * (k+1) + Tt ) = (3Tp + 2Ts) * k + 2s*k/b + 2s/b + n/b + 3Tp
总结: (PS=分组交换, CS=电路交换)
计算机网络英文版习题答案

XXXX有限公司信息系统账号和密码管理规定第一章总则第一条为保障XXXX有限公司信息系统的安全,确保合理访问和修改XXXX有限公司数据资源,根据《信息安全技术信息系统安全等级保护基本要求》(GB/T22239-2008),结合XXXX有限公司实际,制定本规定。
第二条本管理规定确立了包括建立、监控、修改、注销和删除公司信息系统账号的规则。
第三条本管理规定适用于XXXX有限公司信息系统的设备、平台等,适用对象是XXXX有限公司内部人员、第三方人员以及其他任何授权使用XXXX有限公司信息系统资源的人员。
第四条信息安全领导小组办公室负责制定信息系统用户账号名策略和密码策略。
第五条平台研发部下属系统运维部门负责XXXX有限公司信息系统账号及密码的分配和统一管理。
第二章账号管理第六条账号名(一)每个系统的账号名需能代表某个系统或应用的用户。
每个账号需要有一个所属人;(二)不允许共享账号身份或账号组身份;(三)账号名基本规则为员工工号。
第七条账号的申请(一)应根据业务的需求申请账号,并根据所属人的权限开通相关账号的功能;(二)账号的申请必须得到业务部门、人力资源部门、系统运维部门负责人关于访问该系统设备或服务的批准;(三)账号的权限应被严格控制。
账号尤其是特别权限的账号应被限制在职责范围内所需工作的最低权限。
超过普通用户的权限,必须基于业务需求,并得到系统运维部门负责人的批准;(四)账号和密码提供给员工之前,需要确认用户的身份。
推荐使用较严格的方式(如,递交给部门经理)来提供拥有特权的账号信息;(五)第三方人员申请信息系统账号时由接口的内部员工代为办理,并需明确其责任和义务。
第八条账号申请流程(一)首先由员工填写《系统账号管理申请单》提出书面申请,详细列出涉及的信息系统设备、所需权限、用途,由其部门负责人和分管领导审批;(二)由人力资源部门及系统运维部门负责人审核申请内容的合理性、安全性;(三)在以上各审批环节中,如任何一个审批人不同意该申请,则退回用户的申请。
计算机网络第四版英文答案
计算机网络第四版英文答案【篇一:《计算机网络(第四版)》习题答案】t>习题答案第 1 章概述1-3 the performance of a client-server system is influenced by two network factors: the bandwidth of the network (how many bits/sec it can transport) and the latency (how many seconds it takes for the first bit to get from the client to the server). give an example of a network that exhibits high bandwidth and high latency. then give an example of one with low bandwidth and low latency.客户-服务器系统的性能会受到两个网络因素的影响:网络的带宽(每秒可以传输多少位数据)和延迟(将第一个数据位从客户端传送到服务器端需要多少秒时间)。
请给出一个网络的例子,它具有高带宽和高延迟。
然后再给出另一个网络的例子,它具有低带宽和低延迟。
答:横贯大陆的光纤连接可以有很多千兆位/秒带宽,但是由于光速度传送要越过数千公里,时延将也高。
相反,使用56 kbps调制解调器呼叫在同一大楼内的计算机则有低带宽和较低的时延。
1-4 besides bandwidth and latency, what other parameter is needed to give a good characterization of the quality of service offered by a network used for digitized voice traffic?除了带宽和延迟以外,针对数字化的语音流量,想要让网络提供很好的服务质量,还需要哪个参数?声音的传输需要相应的固定时间,因此网络时隙数量是很重要的。
计网课后习题答案(英文)
Review Questions第一章1.Which characteristics of a multiterminal system make it different from a computer network?A processing power of multiterminal systems remained fully centralized, whilecomputer networks have a distributed processing power.一个多端系统处理能力仍然完全集中,而计算机网络具有分布式处理能力。
2.When were the first important results achieved in the field of joining computers using long-haul links?In the late 60s在60年代后期3.What is ARPANET?A.A network of supercomputers belonging to military organizations and research institutes in the United StatesB.An international scientific research networkC.The technology of creating WANsA is correct4.When did the first network operating systems appear?In the late 60s60年代后期5.In what order did the events listed here take place?A.The invention of WebB.The development of standard LAN technologiesC.The start of voice transmission in digital form through telephone networksThe invention of World Wide Web互联网的诞生6.Which of the events stimulated LAN development?Appearance of large-scale integrated circuits (LSI devices) resulted in invention of microcomputers which in its turn stimulated a research activity in the area of local computer networks (LANs). The adoption of personal computers was a powerful incentive for the development of LANs.大规模集成电路(LSI器件出现)导致这反过来刺激了研究活动在本地计算机网络(LAN)的微型计算机的发明。
计算机网络课后习题答案完整版
计算机网络课后习题答案完整版一、选择题1. B2. C3. A4. D5. B6. C7. A8. D9. B10. A二、填空题1. 分组交换2. 物理层3. 虚电路4. 数据链路层5. 网络层6. 数据包7. 传输层8. 应用层9. TCP/IP10. HTTP三、简答题1. OSI模型是开放系统互联参考模型,它是一个将计算机网络体系结构分成七个不同功能层的概念模型。
每个层在进行通信时,只需要考虑与该层相邻的上下两个层之间的通信细节,而不需要关心其他层的具体实现。
这样分层的设计旨在提高系统的可靠性、可维护性和可扩展性。
2. 物理层负责传输原始的比特流,是计算机网络的基础。
在物理层中,主要要考虑的问题是如何在传输媒介上传输比特流,并确保传输的可靠性和速度。
3. 虚电路是一种通信方式,其特点是在通信前需要建立连接,并且传输的数据包按照建立连接时分配的路由进行传输。
虚电路具有较高的可靠性和可控性,但建立连接的过程较为复杂,且传输时会有一定的延迟。
4. 数据链路层主要负责将物理层传输的比特流转化为数据帧,并进行错误检测和纠正。
数据链路层还负责对数据进行分组和重新组装,以及对数据的流量控制和传输控制。
5. 网络层负责将数据包从源主机传输到目标主机。
网络层主要要解决的问题是如何选择合适的路径,并进行数据的分组和重组。
IP协议是网络层中最重要的协议之一。
6. 传输层主要负责提供端到端的可靠通信。
传输层主要要解决的问题是如何对数据包进行序列化、分组和重组,并确保数据的可靠传输。
TCP协议是传输层中最常用的协议之一。
7. 应用层是计算机网络体系结构中最靠近用户的一层。
应用层负责处理用户的请求和提供相关的服务,例如HTTP协议用于在Web中传输超文本。
8. TCP/IP是一组用于计算机网络的协议,它是互联网的基础。
TCP/IP协议族由四个层次组成,分别是网络接口层、网络层、传输层和应用层。
9. HTTP是一种应用层协议,它是在Web中传输超文本的主要协议。
计算机网络课后习题参考答案

计算机网络课后习题参考答案第 1:计算机网络概述一.填空题1.建立计算机网络的主要目的是资源共享。
2.ISO/OSI 参考模型将网络分为应用层、表示层、会话层、传输层、网络层、数据链路层和物理层。
3.使用分层体系结构,可以把复杂的计算机网络简化,使其容易理解和实现。
4.计算机网络的功能有资源共享、数据通信、实时控制、均衡负载等。
5.计算机网络由通信子网和__资源__子网组成。
6.网络协议的主要要素为语法、语义和同步。
二.选择题1.在TCP/IP 体系结构中,与OSI 参考模型的网络层对应的是。
(B)A.网络接口层 B. 网络互联层 C. 传输层 D. 应用层2.在OSI 参考模型中,保证端到端的可靠性在上实现。
(C)A.数据链路层 B. 网络层 C. 传输层 D. 会话层3.在层与层之间交换数据的接口称之为。
(B)A. PDUB. SAPC. SDUD. UDP4.一个分组被传送到错误的目的站,这种差错发生在OSI/RM 的哪一层?(B)A.运输层 B.网络层 C.数据链路层 D.会话层5.关于 OSI/RM,下列哪一种说法是错误的?(C )A.7 个层次就是 7 个不同功能的子系统B.接口是指同一系统内相邻层之间交换信息的连接点C.运输层协议的执行只须使用网络层提供的服务,跟数据链路层没有关系D.某一层协议的执行通过接口向更高一层提供服务。
6.下列功能中,属于表示层提供的是。
(D)A.交互管理 B.透明传输 C.死锁处理 D.文本压缩7.在OSI/RM 中,同层对等实体间进行信息交换时必须遵守的规则称为(A)。
A.协议B.接口C.服务D.关系8.在 OSI 模型中,第 N 层和其上的 N+1 层的关系是。
(A)A.N 层为 N+1 层提供服务B.N+1 层将为从 N 层接收的信息增加了一个头部C.N 层利用 N+1 层提供的服务D.N层对N+1层没有任何作用9.在两个 OSI 模型的 7 层结构中,能进行直接通信的是。
计算机网络英文版——提供给学生部分习题答案
计算机⽹络英⽂版——提供给学⽣部分习题答案Solution of Selected Exercises from the End of Chapter ExercisesChapter 1 - Introduction And Overview1.4 To what aspects of networking does data communications refer?Answer:Data communications refers to the study of low-level mechanisms and technologies used to send information acrossa physical communication medium, such as a wire, radio wave, or light beam.1.5 What is packet-switching, and why is packet switching relevant to the Internet?Answer: Packet switching divides data into small blocks, called packets, and includes an identification of the intended recipient in each packet. Packet switching changed networking in a fundamental way, and provided the basis for the modern Internet. Packet switching allows multiple senders to transmit data over a shared network.1.8 What is a communication protocol? Conceptually, what two aspects of communication does a protocol specify? Answer: A communication protocol refer to a specification for network communication.Major aspects of a protocol are syntax (format) and semantics (meaning) of the protocol.1.9 What is a protocol suite, and what is the advantage of a suite?Answer:protocols are designed in complete, cooperative sets called suites or families, instead of creating each protocol in isolation. Each protocol in a suite handles one aspect of communication; together, the protocols in a suite cover all aspects of communication. The entire suite is designed to allow the protocols to work together efficiently. 1.11 List the layers in the TCP/IP model, and give a brief explanation of each.(See Textbook)1.14 Give a brief explain of the layers in the ISO Open System Interconnection model.(See Textbook)Chapter 3 - Internet Applications And Network Programming3.1 What are the two basic communication paradigms used in the Internet?Answer: There are various approaches, but according to textbook, we can specify them as Stream Paradigm and Message Paradigm.3.2 Give six characteristics of Internet stream communication.(See Textbook)3.3 Give six characteristics of Internet message communication.(See Textbook)3.4 If a sender uses the stream paradigm and always sends 1024 bytes at a time, what size blocks can the Internet deliverto a receiver?Answer: stream paradigm does not provide any guarantees for block sizes, so all depends on individual transfer.3.6 What are the three surprising aspects of the Internet’s message delivery semantics?Answer:The Internet’s message delivery has the followi ng undesirable characteristics:* Messages can be lost* Messages can be duplicated* Messages can be delivered out-of-order3.8 When two applications communicate over the Internet, which one is the server?Answer: T he application that waits for some other applications to contact is called server, and the application that contact other one is called client.3.14 What two identifiers are used to specify a particular server?Answer: A particular server is identified by the following identifiers:* An identifier for the computer on which a server runs (IP Address)* An identifier for a particular service on the computer (Port Number)Chapter 4 - Traditional Internet Applications4.1 What details does an application protocol specify?(See Textbook)4.3 What are the two key aspects of application protocols, and what does each include?(See Textbook)4.6 What are the four parts of a URL, and what punctuation is used to separate the parts?Answer: The URL into four components: a protocol, a computer name, a document name, and parameters. The computer name and protocol port are used to form a connection to the server on which the page resides. And the document name and parameters are used to request a specific page.4.7 What are the four HTTP request types, and when is each used?(See Textbook)4.12 When a user requests an FTP directory listing, how many TCP connections are formed? Explain.Answer: FTP uses two types of connections to perform its functionality, namely* A control connection is reserved for commands. Each time the server needs to download or upload a file, the server opens a new connection.* A data connection is used to transfer files.4.16 List the three types of protocols used with email, and describe each.(See Textbook)4.17 What are the characteristics of SMTP?(See Textbook)4.20 What are the two main email access protocols?Answer: Two major email access protocols are:* Post Office Protocol (POP)* Internet Mail Access Protocol (IMAP)Chapter 6- Information Sources and Signals6.4 State and describe the four fundamental characteristics of a sine wave.(See Textbook)6.9 What is the analog bandwidth of a signal?Answer: Analog bandwidth of signal can be defined as to be the difference between the highest and lowest frequencies of the constituent parts (i.e., the highest and lowest frequencies obtained by Fourier analysis)6.11 Suppose an engineer increases the number of possible signal levels from two to four. How many more bits can be sent in the same amount of time? Explain.Answer: The number of levels that can be represented by n bits is given by 2n . So if number of levels changes from 2→4, it means number of bits goes from 1→2612. What is the definition of baud?Answer: Baud is defined as the number of times that a signal can change per second.6.14 What is the bandwidth of a digital signal? Explain.Answer: According to the definition of analog bandwidth, a digital signal has infinite bandwidth because Fourier analysis of a digital signal produces an infinite set of sine waves with frequencies that grow to infinity.6.18 What is the chief advantage of a Differential Manchester Encoding?Answer: The most important property of differential encoding is that the encoding works correctly even if the two wires carrying the signal are accidentally reversed.6.20 If the maximum frequency audible to a human ear is 20,000 Hz, at what rate must the analog signal from a microphone be sampled when converting it to digital?Answer: The sampling rate = 2 × f max, so the signal should be sampled at 2x20,000 = 40,000 HzChapter 7 - Transmission Media7.2 What are the three energy types used when classifying physical media according to energy used?Answer: Three types of energy used when classifying physical media are electrical, electromechanical (radio), and light7.4 What three types of wiring are used to reduce interference form noise?(See Textbook)7.10 List the three forms of optical fiber, and give the general properties of each.(See Textbook)7.21 What is the relationship between bandwidth, signal levels, and data rate?Answer: If a transmission system uses K possible signal levels and has an anal og bandwidth B, Nyquist’s Theorem states that the maximum data rate in bits per second, D, is: D = 2 B log2K7.22 If two signal levels are used, what is the data rate that can be sent over a coaxial cable that has an analog bandwidthof 6.2 MHz?Answer: Using the D= 2 B log2 K relationship, D = 2*6.2*log22 = 2*6.2*1 = 12.4 Mbps7.24 If a system has an input power level of 9000, and an output power level of 3000, what is the difference when expressed in dB?Answer: Decibel is expressed as 10log10(P out/P in) → 10log10(3,000/9,000) = to be determined by reader7.23 If a system has an average power level of 100, an average noise level of 33.33, and a bandwidth of 100 MHz, whatis the effective limit on channel capacity?Answer: Shannon theorem specify the maximum data rate that could be achieved over a transmission system that experiences noise: C = Blog2 (1 + S/N) = 100,000,000 * log2 (1 + 100/33.33) = 100,000,000 * log24 = 200,000,000 = 200 Mbps7.25 If a telephone system can be created with a signal-to-noise ratio of 40 dB and an analog bandwidth of 3000 Hz, how many bits per second could be transmitted?Answer: First we should convert 40 dB to a real number, namely if 40 = 10 log10S/N→S/N = 10,000 , Using the Shannon’s capacity expression C = B log2(1 + S/N) → C = 3,000 log2 (1+ 10,000) = to be determined by readerCh 8 - Reliability And Channel Coding8.1 List and explain the three main sources of transmission errors.(See Textbook)8.3 In a burst error, how is burst length measured?Answer: For a burst error, the burst size, or length, is defined as the number of bits from the start of the corruption to the end of the corruption.8.4 What is a codeword?Answer: We can define the set of all possible messages to be a set of datawords, and define the set of all possible encoded versions to be a set of codewords. So each possible code sequence is considered to be a codeword.8.8 Compute the Hamming distance for the following pairs: (0000, 0001), (0101, 0001), (1111, 1001), and ( 0001, 1110). (See Textbook)8.11 Generate a RAC parity matrix for a (20, 12) coding of the dataword 100011011111.(See Textbook)8.15 Express the two values in the previous exercise as polynomials.Answer:X10+ X7 + X5 + X3 + XX4+ X2+ 1Ch 9 - Transmission Modes9.1 Describe the difference between serial and parallel transmission.Answer: Transmission modes can be divided into two fundamental categories:* Serial: one bit is sent at a time* Parallel: multiple bits are sent at the same time9.2 What are the advantages of parallel transmission? What is the chief disadvantage?Answer: A parallel mode of transmission has two chief advantages:* High speed: Because it can send N bits at the same time, a parallel interface can operate N times faster than an equivalent serial interface.* Match to underlying hardware: Internally, computer and communication hardware uses parallel circuitry.Thus, a parallel interface matches the internal hardware well.The main disadvantage of parallel transmission is number of cables required, for long distance communication, this is an important consideration.9.4 What is the chief characteristic of asynchronous transmission?Answer:Asynchronous transmission can occur at any time, with an arbitrary delay between the transmission of two data items, it allows the physical medium to be idle for an arbitrary time between two transmissions.Chapter 11 - Multiplexing And Demultiplexing11.2 What are the four basic types of multiplexing?(See Textbook)11.4 What is a guard band?Answer: For proper communication without interference, we should choose a set of carrier frequencies with a gap between them known as a guard band. The guard band reduces or eliminates the possible interference between neighboring carrier signals.11.8 Explain how a range of frequencies can be used to increase data rate.Answer:To increase the overall data rate, a sender divides the frequency range of the channel into K carriers, and sends 1 /K of the data over each carrier.11.12 Suppose N users compete using a statistical TDM system, and suppose the underlying physical transport can sendK bits per second. What is the minimum and maximum data rate that an individual user can experience?Answer: If we neglect the overhead generated by statistical TDM, a system will have two possibilities: * Minimum: If all channels have equal data then the rate will be K/N bps* Maximum: If only one channel active and the others are passive, then rate will be K bpsChapter 13 - Local Area Networks: Packets, Frames, And Topologies13.1 What is circuit switching, and what are its chief characteristics?Answer: The term circuit switching refers to a communication mechanism that establishes a path between a sender and receiver with guaranteed isolation from paths used by other pairs of senders and receivers. The circuit switching has the following main characteristics:* Point-to-point communication* Separate steps for circuit creation, use, and termination* Performance equivalent to an isolated physical path13.3 In a packet switching system, how does a sender transfer a large file?Answer: The packet switching system requires a sender to divide each message into blocks of data that are known as packets . The size of a packet varies; each packet switching technology defines a maximum packet size. So, a large file will be divided into smaller pieces and sent.13.5 What are the characteristics of LANs, MANs, and W ANs?Answer: There are lots of details that can be said and discussed for categorization of network types based on geography, few points are highlighted below:* Local Area Network (LAN): Least expensive; spans a single room or a single building* Metropolitan Area Network (MAN) Medium expense; spans a major city or a metroplex* Wide Area Network (WAN) Most expensive; spans sites in multiple cities13.6 Name the two sublayers of Layer 2 protocols defined by IEEE, and give the purpose of each.Answer: The Layer 2 protocols defined by IEEE defines two sub-layers as mentioned below:* Logical Link Control (LLC) Addressing and demultiplexing* Media Access Control (MAC) Access to shared media13.8 What are the four basic LAN topologies?Answer: The four basic LAN topologies are star, ring, mesh and bus.13.10 In a mesh network, how many connections are required among 20 computers?Answer: The expression to calculate number of connections in a mesh network is given by n (n-1)/2. So for 20 computers then number of connections required will be = 20 (20 – 1)/2 =19013.15 Give a definition of the term frame .Answer: In a packet-switched network, each frame corresponds to a packet processed at data link layer.Chapter 14 - The IEEE MAC Sub-Layer14.1 Explain the three basic approaches used to arbitrate access to a shared medium.(See Textbook)14.3 List the three main types of channelization and the characteristics of each.(See Textbook)14.6 What is a token, and how are tokens used to control network access?Answer: A special control message is called a token. In a token passing system, when no station has any packets to send, the token circulates among all stations continuously. When a station captures the token, it sends its data, and when transmission completed, it releases the token.14.8 Expand the acronym CSMA/CD, and explain each part.Answer: The acronym CSMA/CD stands for Carrier Sense Multi-Access with Collision Detection, which means the following: * Carrier Sense: Instead of allowing a station to transmit whenever a packet becomes ready, Ethernet requires each station to monitor the cable to detect whether another transmission is already in progress.* Multiple Access: The system allows multiple users/hosts to make use of a common/shared media* Collision Detection. A collision can occur if two stations wait for a transmission to stop, find the cable idle, and both start transmitting.14.10 Why does CSMA/CD use a random delay? (Hint: think of many identical computers on a network.)Answer: Randomization is used to avoid having multiple stations transmit simultaneously as soon as the cable is idle.That is, the standard specifies a maximum delay, d, and requires each station to choose a random delay less than d after a collision occurs. In most cases, when two stations each choose a random value, the station that chooses the smallest delay willChapter 15 - Wired LAN Technology (Ethernet And 802.3)15.1 How large is the maximum Ethernet frame, including the CRC?Answer: According to Fig. 15.1 a conventional Ethernet frame has the following fields:* Header: 14 bytes (fixed)* Payload: 46-1500 bytes (there is a minimum frame size because of collision detection)* CRC: 4 bytes (fixed)Accordingly an Ethernet frame will be maximum 1518 bytes and minimum 64 bytes15.3 In an 802.3 Ethernet frame, what is the maximum payload size?Answer: The 802.3 Ethernet makes use of 8-bytes of the original/conventional Ethernet for Logical Link Control / Sub-Network Attachment Point (LLC / SNAP) header instead of extending/increasing the header. This is for sake of backward compatibility. So the maximum pay load is reduced from 1500 bytes to 1492 bytes.15.6 How did a computer attach to a Thicknet Ethernet?Answer: Hardware used with Thicknet was divided into two major parts:* Transceiver: A network interface card (NIC) handled the digital aspects of communication, and a separate electronic device called a transceiver connected to the Ethernet cable and handled carrier detection, conversion of bits into appropriate voltages for transmission, and conversion of incoming signals to bits.* AUI: A physical cable known as an Attachment Unit Interface (AUI) connected a transceiver to a NIC in a computer. A transceiver was usually remote from a computer.15.7 How were computers attached to a Thinnet Ethernet?Answer: Thinnet Ethernet (formally named 10Base2) uses a thinner coaxial cable that was more flexible than Thicknet. The wiring scheme differed dramatically from Thicknet. Instead of using AUI connections between a computer and a transceiver, Thinnet integrates a transceiver directly on the NIC, and runs a coaxial cable from one computer to another.15.8 What is an Ethernet hub, and what wiring is used with a hub?Answer: An electronic device that serves as the central interconnection is known as a hub. Hubs were available in a variety of sizes, with the cost proportional to size. The hubs are becoming old-fashioned, and being replaced with switches.15.3 What category of twisted pair wiring is needed for a 10 Mbps network? 100 Mbps? 1000 Mbps?Answer: The three major categories of Ethernet and their wiring is listed below:* 10 Mbps: 10BaseT (Ethernet) Category 5* 100 Mbps: 100BaseT (Ethernet Fast) Category 5E* 1 Gbps: 1000BaseT (Gigabit Ethernet) Category 6Chapter 20 - Internetworking: Concepts, Architecture, and Protocols20.2 Will the Internet be replaced by a single networking technology? Why or why not?Answer: Incompatibilities make it impossible to form a large network merely by interconnecting the wires among networks. The beauty of the Internet is interconnection of wide range of technologies from various manufacturers.Diversity of the products and solutions is a richness instead of limitation as long as they all adopt the same set of protocols.20.3 What are the two reasons an organization does not use a single router to connect all its networks?Answer:An organization seldom uses a single router to connect all of its networks. There are two major reasons: * Because the router must forward each packet, the processor in a given router is insufficient to handle the traffic passing among an arbitrary number of networks.* Redundancy improves internet reliability. To avoid a single point of failure, protocol software continuously monitors internet connections and instructs routers to send traffic along alternative paths when a network or router fails.20.6 In the 5-layer reference model used with the TCP/IP Internet protocols, what is the purpose of each of the five layers?(See 1.11)Chapter 21- IP: Internet Addressing21.3 In the original classful address scheme, was it possible to determine the class of an address from the address itself? Explain.Answer:Yes, since in the classful addressing scheme initial bit(s) gives indication about the class being used.21.7 If an ISP assigned you a /28 address block, how many computers could you assign an address?Answer: When an organization is assigned /28 CIDR address, it means 28 bits out of 32 bits are fixed, so 32-28 = 4 bits available for user space. So number of users 24-2 = 4, since the all 0s and all 1s address are having special use and can’t be assigned to a user.21.8 If an ISP offers a / 17 address block for N dollars per month and a / 16 address block for 1.5 N dollars per month,which has the cheapest cost per computer?Answer: Number of addresses in /17 block 232-17 = 215Price per address: N /215 = N / 215Number of addresses in /16 block 232-16 = 216Price per address: 1.5N /216 = 0.75N/215 So /16 address block will be cheaper in comparison with the price given for /17 block.21.10 Suppose you are an ISP with a / 24 address block. Explain whether you accommodate a request from a customer who needs addresses for 255 computers. (Hint: consider the special addresses.)Answer: For a/24 address block, number of available addresses will be 232-24 = 28 = 256. However, a suffix with all 0s address is reserved for network ID and a suffix with all 1s address is reserved for broadcast address, so number of addresses that can be assigned to computers/hosts will be 256 -2 = 254.21.11 Suppose you are an ISP that owns a / 22 address block. Show the CIDR allocation you would use to allocateaddress blocks to four customers who need addresses for 60 computers each.Answer: The /22 address block can be assigned as follows:ddd.ddd.ddd.00/26ddd.ddd.ddd.01/26ddd.ddd.ddd.10/26ddd.ddd.ddd.11/26Chapter 22- Datagram Forwarding22.1 What are the two basic communication paradigms that designers consider when designing an internet?Answer:* Connection-oriented service * Connectionless service22.2 How does the Internet design accommodate heterogeneous networks that each have their own packet format?Answer: To overcome heterogeneity, the Internet Protocol defines a packet format that is independent of the underlying hardware. The result is a universal, virtual packet that can be transferred across the underlying hardware intact. The Internet packet format is not tied directly to any hardware. The underlying hardware does not understand or recognize an Internet packet.22.5 What is the maximum length of an IP datagram?In the current version of the Internet Protocol (IP version 4), a datagram can contain at most 64 K (65535) octets, including the header.22.7 If a datagram contains one 8-bit data value and no header options, what values will be found in header fields H.LEN and TOTAL LENGTH?Answer: H. LEN indicated header in 32-quantities, since no options, then this value will be 5. The TOTAL LENGTH indicated the number of bytes in a datagram including the header. This means 5x4 bytes + 1 (8-bits) = 21 bytesChapter 23 - Support Protocols And Technologies23.1 When a router uses a forwarding table to look up a next-hop address, the result is an IP address. What must happenbefore the datagram can be sent?Answer: Each router along the path uses the destination IP address in the datagram to select a next-hop address, encapsulates the datagram in a hardware frame, and transmits the frame across one network. A crucial step of the forwarding process requires a translation: forwarding uses IP addresses, and a frame transmitted across a physical network must contain the MAC address of the next hop.23.2 What term is used to describe the mapping between a protocol address and a hardware address?Answer: Translation from a computer’s IP address to an equivalent hardware address is known as address resolution, and an IP address is said to be resolved to the correct MAC address. The TCP/IP protocol being used for this is called Address Resolution Protocol (ARP). Address resolution is local to a network.23.5 How many octets does an ARP message occupy when used with IP and Ethernet addresses?Answer: According to Fig 23.3 an ARP message has 7-lines of each being 32-bit (4 bytes or octets), therefore,number of octets in an ARP can be determined as 7x4 = 28 octets23.10 What types of addresses are used in layers below ARP?Answer:ARP forms a conceptual boundary in the protocol stack; layers above ARP use IP addresses, and layers below ARP use MAC addresses.23.17 What is the chief difference between BOOTP and DHCP?Answer:The main difference is that the BOOTP protocol required manual administration. So before a computer could use BOOTP to obtain an address, a network administrator had to configure a BOOTP server to know the computer’s I P address. Chapter 24 - The Future IP (IPv6)24.3 List the major features of IPv6, and give a short description of each.(See Textbook)24.4 How large is the smallest IPv6 datagram header?Answer: IPv6 datagram header consists of a base header + zero or more extension header. Since, smallest header is being asked, we assume zero extension header and consider IPv6 will have only base header. If we look at IPv6 header format in Fig. 24.3, it shows that 10x4 bytes = 40 bytes.Chapter 26 - TCP: Reliable Transport Service26.2 List the features of TCP.(See Textbook)26.6 When using a sliding window of size N, how many packets can be sent without requiring a single ACK to be received?Answer: If the size of the window is N, then it means a sender can transmit up to N packets without waiting for an ACK, as long as other controls are in place.26.9 What is the chief cause of packet delay and loss in the Internet?Answer: The main cause of packet delay and loss in the Internet is congestion.Chapter 28 - Network Performance (QoS and DiffServ)28.1 List and describe the three primary measures of network performance.(See Textbook)28.2 Give five types of delay along with an explanation of each.(See Textbook)Chapter 30 - Network Security30.1 List the major security problems on the Internet, and give a short description of each.(See Textbook)30.2 Name the technique used in security attacks.(See Textbook)30.8 List and describe the eight basic security techniques.(See Textbook)。
计算机网络课后习题及答案
计算机网络课后习题及答案一、选择题1. 计算机网络的定义是()。
A. 将计算机连接起来形成一个巨大的网络B. 利用通信设备和帮助计算机实现异地通信和资源共享的软件系统C. 将计算机与其他设备连接起来形成一个网络D. 以上答案均不正确答案:B2. 在计算机网络中,「协议」是()。
A. 双方各自对自己表示的理解的统称B. 双方对彼此要求的统称C. 参与通信双方所要共同遵循的规则D. 以上答案均不正确答案:C3. 「网络拓扑」是指()。
A. 网络中的设备之间的物理连接方式B. 网络中的设备之间的逻辑连接方式C. 网络中不同设备的排列方式D. 以上答案均不正确答案:A4. 在计算机网络中,「互联网」是指()。
A. 全球范围内的所有网络的集合B. 企事业单位内部的网络C. 家庭或个人内部的网络D. 以上答案均不正确答案:A5. 「IP地址」是用来()。
A. 标识互联网上的终端设备B. 标识一个网络C. 标识一个计算机D. 以上答案均不正确答案:A二、填空题1. 计算机网络中,「URL」的全称是__________。
答案:统一资源定位符2. 在计算机网络中,「HTTP」的全称是__________。
答案:超文本传输协议3. 在计算机网络中,「DNS」的全称是__________。
答案:域名系统4. 计算机网络中,「FTP」的全称是__________。
答案:文件传输协议5. 在计算机网络中,「TCP」的全称是__________。
答案:传输控制协议三、简答题1. 请解释「OSI参考模型」的七层结构。
答:「OSI参考模型」,全称为Open System Interconnection Reference Model,是一个由国际标准化组织(ISO)提出的概念框架,用于理解和描述计算机网络中不同层次的功能和关系。
该模型分为七层,从物理层到应用层分别是:物理层、数据链路层、网络层、传输层、会话层、表示层和应用层。
计算机网络课后答案(全部)
计算机网络习题解答教材计算机网络谢希仁编著第一章概述习题1-01 计算机网络的发展可划分为几个阶段?每个阶段各有何特点?答: 计算机网络的发展过程大致经历了四个阶段。
第一阶段:(20世纪60年代)以单个计算机为中心的面向终端的计算机网络系统。
这种网络系统是以批处理信息为主要目的。
它的缺点是:如果计算机的负荷较重,会导致系统响应时间过长;单机系统的可靠性一般较低,一旦计算机发生故障,将导致整个网络系统的瘫痪。
第二阶段:(20世纪70年代)以分组交换网为中心的多主机互连的计算机网络系统。
为了克服第一代计算机网络的缺点,提高网络的可靠性和可用性,人们开始研究如何将多台计算机相互连接的方法。
人们首先借鉴了电信部门的电路交换的思想。
所谓“交换”,从通信资源的分配角度来看,就是由交换设备动态地分配传输线路资源或信道带宽所采用的一种技术。
电话交换机采用的交换技术是电路交换(或线路交换),它的主要特点是:①在通话的全部时间内用户独占分配的传输线路或信道带宽,即采用的是静态分配策略;②通信双方建立的通路中任何一点出现了故障,就会中断通话,必须重新拨号建立连接,方可继续,这对十分紧急而重要的通信是不利的。
显然,这种交换技术适应模拟信号的数据传输。
然而在计算机网络中还可以传输数字信号。
数字信号通信与模拟信号通信的本质区别在于数字信号的离散性和可存储性。
这些特性使得它在数据传输过程中不仅可以间断分时发送,而且可以进行再加工、再处理。
③计算机数据的产生往往是“突发式”的,比如当用户用键盘输入数据和编辑文件时,或计算机正在进行处理而未得出结果时,通信线路资源实际上是空闲的,从而造成通信线路资源的极大浪费。
据统计,在计算机间的数据通信中,用来传送数据的时间往往不到10%甚至1%。
另外,由于各异的计算机和终端的传输数据的速率各不相同,采用电路交换就很难相互通信。
为此,必须寻找出一种新的适应计算机通信的交换技术。
1964年,巴兰(Baran)在美国兰德(Rand)公司“论分布式通信”的研究报告中提出了存储转发(store and forward)的概念。
计算机网络课后习题答案(仅供参考)
计算机网络习题解答教材计算机网络谢希仁编著第一章概述习题1-01 计算机网络的发展可划分为几个阶段?每个阶段各有何特点?答: 计算机网络的发展过程大致经历了四个阶段。
第一阶段:(20世纪60年代)以单个计算机为中心的面向终端的计算机网络系统。
这种网络系统是以批处理信息为主要目的。
它的缺点是:如果计算机的负荷较重,会导致系统响应时间过长;单机系统的可靠性一般较低,一旦计算机发生故障,将导致整个网络系统的瘫痪。
第二阶段:(20世纪70年代)以分组交换网为中心的多主机互连的计算机网络系统。
为了克服第一代计算机网络的缺点,提高网络的可靠性和可用性,人们开始研究如何将多台计算机相互连接的方法。
人们首先借鉴了电信部门的电路交换的思想。
所谓“交换”,从通信资源的分配角度来看,就是由交换设备动态地分配传输线路资源或信道带宽所采用的一种技术。
电话交换机采用的交换技术是电路交换(或线路交换),它的主要特点是:①在通话的全部时间内用户独占分配的传输线路或信道带宽,即采用的是静态分配策略;②通信双方建立的通路中任何一点出现了故障,就会中断通话,必须重新拨号建立连接,方可继续,这对十分紧急而重要的通信是不利的。
显然,这种交换技术适应模拟信号的数据传输。
然而在计算机网络中还可以传输数字信号。
数字信号通信与模拟信号通信的本质区别在于数字信号的离散性和可存储性。
这些特性使得它在数据传输过程中不仅可以间断分时发送,而且可以进行再加工、再处理。
③计算机数据的产生往往是“突发式”的,比如当用户用键盘输入数据和编辑文件时,或计算机正在进行处理而未得出结果时,通信线路资源实际上是空闲的,从而造成通信线路资源的极大浪费。
据统计,在计算机间的数据通信中,用来传送数据的时间往往不到10%甚至1%。
另外,由于各异的计算机和终端的传输数据的速率各不相同,采用电路交换就很难相互通信。
为此,必须寻找出一种新的适应计算机通信的交换技术。
1964年,巴兰(Baran)在美国兰德(Rand)公司“论分布式通信”的研究报告中提出了存储转发(store and forward)的概念。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
Chapter11-11.What are two reasons for using layered protocols?(请说出使用分层协议的两个理由)答:通过协议分层可以把设计问题划分成较小的易于处理的片段。
分层意味着某一层的协议的改变不会影响高层或低层的协议。
1-13. What is the principal difference between connectionless communication and connection-oriented communication?(在无连接通信和面向连接的通信两者之间,最主要的区别是什么?)答:主要的区别有两条。
其一:面向连接通信分为三个阶段,第一是建立连接,在此阶段,发出一个建立连接的请求。
只有在连接成功建立之后,才能开始数据传输,这是第二阶段。
接着,当数据传输完毕,必须释放连接。
而无连接通信没有这么多阶段,它直接进行数据传输。
其二:面向连接的通信具有数据的保序性,而无连接的通信不能保证接收数据的顺序与发送数据的顺序一致。
1-20. A system has an n-layer protocol hierarchy. Applications generate messages of length M bytes. At each of the layers, an h-byte header is added. What fraction of the network bandwidth is filled with headers?(一个系统有n层协议的层次结构。
应用程序产生的消息的长度为M字节。
在每一层上需要加上一个h字节的头。
请问,这些头需要占用多少比例的网络带宽)答:hn/(hn+m)*100%1-28. An image is 1024 x 768 pixels with 3 bytes/pixel. Assume the image is uncompressed. How long does it take to transmit it over a 56-kbps modem channel? Over a 1-Mbps cable modem? Over a 10-Mbps Ethernet? Over 100-Mbps Ethernet?(一幅图像的分辨率为1024 x 768像素,每个像素用3字节来表示。
假设该图像没有被压缩。
请问,通过56kbps的调制解调器信道来传输这幅图像需要多长时间?通过1Mbps的电缆调制解调器呢?通过10Mbps的以太网呢?通过100Mbps的以太网呢?)答:The image is 1024*768*3 bytes or 2359296 bytes.This is 18874368 bit. At 56,000 bits/sec, it takes about 337.042 sec. At 1,000,000 bits/sec, it takes about 18.874 sec. At 10,000,000 bits/sec, it takes about 1.887 sec. At 100,000,000 bits/sec, it takes about 0.189 sec.Chapter22-2. A noiseless 4-kHz channel is sampled every 1 msec. What is the maximum data rate?(一条无噪声4kHz信道按照每1ms一次进行采样,请问最大数据传输率是多少?)答:无噪声信道最大数据传输率公式:最大数据传输率=2Hlog2V b/s。
因此最大数据传输率决定于每次采样所产生的比特数,如果每次采样产生16bits,那么数据传输率可达128kbps;如果每次采样产生1024bits,那么可达8.2Mbps。
注意这是对无噪声信道而言的,实际信道总是有噪声的,其最大数据传输率由香农定律给出。
2-4. If a binary signal is sent over a 3-kHz channel whose signal-to-noise ratio is 20 dB, what is the maximum achievable data rate?(如果在一条3kHz的信道上发送一个二进制信号,该信道的信噪比为20dB,则最大可达到的数据传输率为多少?)答:信噪比为20 dB 即 S/N =100由于 log101≈6.658,由香农定理,该信道2的信道容量为3log(1+100)=19.98kbps。
2又根据乃奎斯特定理,发送二进制信号的3kHz 信道的最大数据传输速率为2*3*log22=6kbps。
所以可以取得的最大数据传输速率为6kbps。
2-5. What signal-to-noise ratio is needed to put a T1 carrier on a 50-kHz line?(在50kHz的线路上使用1T线路需要多大的信噪比?)答:为发送T1 信号,我们需要所以,在50kHz 线路上使用T1 载波需要93dB 的信噪比。
2-34. A signal is transmitted digitally over a 4-kHz noiseless channel with one sample every 125 µsec. How many bits per second are actually sent for each of these encoding methods?(a) CCITT 2.048 Mbps standard.(b) DPCM with a 4-bit relative signal value.(c) Delta modulation.(一个信号在4kHz的无噪声信道上以数字方式进行传输,没125us采样一次。
请问,按照以下的编码方法,每秒钟实际发送多少位?(a)CCITT 2.048Mbps标准。
(b)有4位相对信号值的DPCM。
(c)增量调制。
)答:a.CCITT 2.048Mbps 标准用32 个8 位数据样本组成一个125的基本帧,30 个信道用于传信息,2 个信道用于传控制信号。
在每一个4kHz 信道上发送的数据率就是8*8000=64kbps。
b.差分脉码调制(DPCM)是一种压缩传输信息量的方法,它发送的不是每一次抽样的二进制编码值,而是两次抽样的差值的二进制编码。
现在相对差值是4 位,所以对应每个4kHz 信道实际发送的比特速率为4*8000=32bps。
c.增量调制的基本思想是:当抽样时间间隔s t 很短时,模拟数据在两次抽样之间的变化很小,可以选择一个合适的量化值作为阶距。
把两次抽样的差别近似为不是增加一个就是减少一个。
这样只需用1bit 二进制信息就可以表示一次抽样结果,而不会引入很大误差。
因此,此时对应每个4kHz 信道实际发送的数据速率为1*8000=8kHz。
2-43. Suppose that x bits of user data are to be transmitted over a k-hop path in a packet-switched network as a series of packets, each containing p data bits and h header bits,with x >> p+h.The bit rate of the lines is b bps and the propagation delay is negligible.What value of p minimizes the total delay?(假定x位用户数据将以一系列分组形式,在一个分组交换网络中沿着一条共有k跳的路径向前传播,每个分组包含p位数据和h位的头,这里x>>p+h。
线路的传输率为b bps,传播延迟忽略不计。
请问,什么样的p值使总延迟最小?) 答:所需要的分组总数是x /p,因此总的数据加上头信息交通量为(p+h)*x/p 位。
源端发送这些位需要时间为(p+h)*x/pb中间的路由器重传最后一个分组所花的总时间为(k-1)*(p+h)/ b因此我们得到的总的延迟为对该函数求p 的导数,得到令得到因为p>0,所以故时能使总的延迟最小。
2-53. A CDMA receiver gets the following chips: (-1 +1 -3 +1 -1 -3 +1 +1). Assuming the chip sequences defined in Fig. 2-45(b), which stations transmitted, and which bits did each one send?(一个CDMA接收器得到了下面的时间片:(-1 +1 -3 +1 -1 -3 +1 +1)。
假设时间片序列如图2.45(b)中所定义,请问哪些移动站传输了数据?每个站发送了什么位?)答:Just compute the four normalized inner products:(1+1 3+1 1 3+1+1)d(1 1 1+1+1 1+1+1)/8=1(1+1 3+1 1 3+1+1)d(1 1+1 1+1+1+1 1)/8=1(1+1 3+1 1 3+1+1)d(1+1 1+1+1+1 1 1)/8=0(1+1 3+1 1 3+1+1)d(1+1 1 1 1 1+1 1)/8=1The result is that A and D sent 1 bits, B sent a 0 bit, and C was silent. Chapter33-3.The following data fragment occurs in the middle of a data stream for which the byte-stuffing algorithm described in the text is used: A B ESC C ESC FLAG FLAG D. What is the output after stuffing?(数据片断(A B ESC C ESC FLAG FLAG D)出现在一个数据流的中间,而成帧方式采用的是本章介绍的字节填充算法,请问经过填充之后的输出时什么?) 答:After stuffing, we get A B ESC ESC C ESC ESC ESC FLAG ESC FLAG D.3-15. A bit stream 10011101 is transmitted using the standard CRC method described in the text. The generator polynomial is x3 + 1. Show the actual bit string transmitted. Suppose the third bit from the left is inverted during transmission. Show that this error is detected at the receiver's end.(利用本章中介绍的标准多项式CRC方法来传输位流1001101。
