cisco asa5510-K8防火墙实例教程
2019年思科5510防火墙-范文模板 (14页)
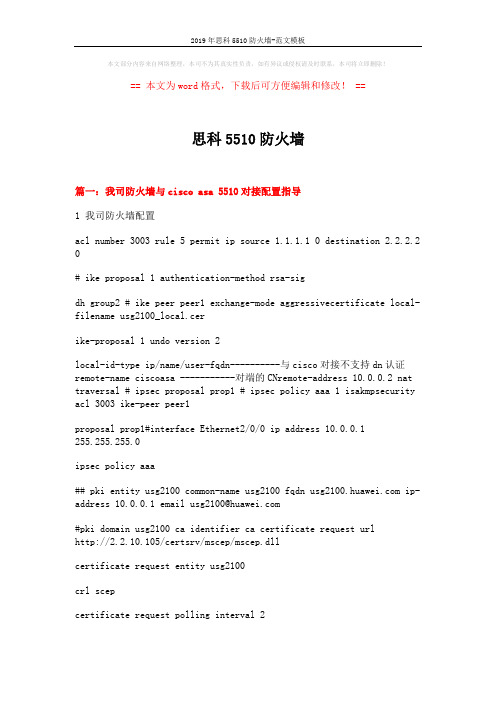
本文部分内容来自网络整理,本司不为其真实性负责,如有异议或侵权请及时联系,本司将立即删除!== 本文为word格式,下载后可方便编辑和修改! ==思科5510防火墙篇一:我司防火墙与cisco asa 5510对接配置指导1 我司防火墙配置acl number 3003 rule 5 permit ip source 1.1.1.1 0 destination 2.2.2.2 0# ike proposal 1 authentication-method rsa-sigdh group2 # ike peer peer1 exchange-mode aggressivecertificate local-filename usg2100_local.cerike-proposal 1 undo version 2local-id-type ip/name/user-fqdn----------与cisco对接不支持dn认证remote-name ciscoasa -----------对端的CNremote-address 10.0.0.2 nat traversal # ipsec proposal prop1 # ipsec policy aaa 1 isakmpsecurity acl 3003 ike-peer peer1proposal prop1#interface Ethernet2/0/0 ip address 10.0.0.1255.255.255.0ipsec policy aaa## pki entity usg2100 common-name usg2100 fqdn ip-address 10.0.0.1 email usg2100@#pki domain usg2100 ca identifier ca certificate request urlhttp://2.2.10.105/certsrv/mscep/mscep.dllcertificate request entity usg2100crl scepcertificate request polling interval 2crl update-period 1crl auto-update enablecrl url http://2.2.10.105/certsrv/mscep/mscep.dll#2 CISCO配置2.1 设备型号Hardware:ASA5510, 256 MB RAM, CPU Pentium 4 Celeron 1600 MHzCisco Adaptive Security Appliance Software Version 8.4(1)版本不同将导致配置略有差别。
CISCOASA5510配置手册

CISCOASA5510 // OKciscoasa#showverCiscoAdaptiveSecurityApplianceSoftwareVersion7.2(4) DeviceManagerVersion5.2(4)CompiledonSun06-Apr-0813:39bybuildersSystemimagefileis"disk0:/asa724-k8.bin" Configfileatbootwas"startup-config"ciscoasaup3mins5secsHardware:ASA5520,512MBRAM,CPUPentium4Celeron2000MHz InternalATACompactFlash,256MBBIOSFlashFirmwareHub@0xffe00000,1024KBEncryptionhardwaredevice:CiscoASA-55x0on-boardaccelerator(revision0x0) Bootmicrocode:CNlite-MC-Boot-Cisco-1.2SSL/IKEmicrocode:CNlite-MC-IPSEC-Admin-3.03IPSecmicrocode:CNlite-MC-IPSECm-MAIN-2.050:Ext:GigabitEthernet0/0:addressisc47d.4f85.1708,irq91:Ext:GigabitEthernet0/1:addressisc47d.4f85.1709,irq92:Ext:GigabitEthernet0/2:addressisc47d.4f85.170a,irq93:Ext:GigabitEthernet0/3:addressisc47d.4f85.170b,irq94:Ext:Management0/0:addressisc47d.4f85.1707,irq115:Int:Notused:irq116:Int:Notused:irq5MaximumVLANs:150InsideHosts:UnlimitedFailover:Active/ActiveVPN-DES:EnabledVPN-3DES-AES:DisabledSecurityContexts:2GTP/GPRS:DisabledVPNPeers:750WebVPNPeers:2ThisplatformhasanASA5520VPNPluslicense.SerialNumber:JMX1406L0Y6RunningActivationKey:0x6a2659550xf07c223d0x2cf345f40xb34478840xc128879b Configurationregisteris0x1Configurationlastmodifiedbyenable_15at12:23:52.072UTCMonSep62010 ciscoasa#showrun:Saved:ASAVersion7.2(4)!hostnameciscoasadomain-namedefault.domain.invalidenablepasswordgfFm2E3sthJOc7bqencryptedpasswd2KFQnbNIdI.2KYOUencryptednames!interfaceGigabitEthernet0/0nameifuntrust!interfaceGigabitEthernet0/1 nameifdmzsecurity-level50ipaddress172.18.19.254255.255.255.0!interfaceGigabitEthernet0/2 nameiftrustsecurity-level100ipaddress172.18.1.1255.255.255.0!interfaceGigabitEthernet0/3nonameifnosecurity-levelnoipaddress!interfaceManagement0/0 nameifmanagementsecurity-level100ipaddress192.168.1.1255.255.255.0 management-only!ftpmodepassivednsserver-groupDefaultDNSdomain-namedefault.domain.invalid access-list102extendedpermiticmpanyany access-list102extendedpermitipanyany pagerlines24loggingenablemtudmz1500mtutrust1500mtumanagement1500nofailovericmpunreachablerate-limit1burst-size1asdmimagedisk0:/ASDM-524.BINnoasdmhistoryenablearptimeout14400global(untrust)1interfacenat(trust)10.0.0.00.0.0.0static(trust,untrust)tcp113.105.88.5786172.18.11.886netmask255.255.255.255static(trust,untrust)tcp113.105.88.575000172.18.11.85000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.586800172.18.11.1306800netmask255.255.255.255 static(trust,untrust)tcp113.105.88.584800172.18.11.1304800netmask255.255.255.255 static(trust,untrust)tcp113.105.88.583306172.18.11.1303306netmask255.255.255.255 static(trust,untrust)udp113.105.88.586800172.18.11.1306800netmask255.255.255.255 static(trust,untrust)udp113.105.88.584800172.18.11.1304800netmask255.255.255.255 static(trust,untrust)udp113.105.88.583306172.18.11.1303306netmask255.255.255.255 static(trust,untrust)tcp113.105.88.5881172.18.11.13081netmask255.255.255.255 static(trust,untrust)udp113.105.88.5881172.18.11.13081netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601011172.18.11.91011netmask255.255.255.255 static(trust,untrust)udp113.105.88.601011172.18.11.91011netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601018172.18.11.91018netmask255.255.255.255 static(trust,untrust)udp113.105.88.601018172.18.11.91018netmask255.255.255.255 static(trust,untrust)tcp113.105.88.5981172.18.15.99wwwnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.592000172.18.15.992000netmask255.255.255.255 static(trust,untrust)udp113.105.88.592000172.18.15.992000netmask255.255.255.255 static(trust,untrust)udp113.105.88.59www172.18.15.99wwwnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.598080172.18.15.998080netmask255.255.255.255static(trust,untrust)tcp113.105.88.59ftp-data172.18.11.123ftp-datanetmask255.255.255.255 static(trust,untrust)tcp113.105.88.59ftp172.18.11.123ftpnetmask255.255.255.255static(trust,untrust)tcp113.105.88.59telnet172.18.11.123telnetnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.591010172.18.11.1231000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598003172.18.11.1238003netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598010172.18.11.1238010netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598012172.18.11.1238012netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598880172.18.11.1238880netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601012172.18.11.91012netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601013172.18.11.91013netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601014172.18.11.91014netmask255.255.255.255 static(trust,untrust)udp113.105.88.601012172.18.11.91012netmask255.255.255.255 static(trust,untrust)udp113.105.88.601013172.18.11.91013netmask255.255.255.255 static(trust,untrust)udp113.105.88.601014172.18.11.91014netmask255.255.255.255 static(trust,untrust)tcp113.105.88.595000172.18.15.995000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.594000172.18.15.994000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602000172.18.11.92000netmask255.255.255.255 static(trust,untrust)udp113.105.88.602000172.18.11.92000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.592009172.18.15.992009netmask255.255.255.255 static(trust,untrust)udp113.105.88.592009172.18.15.992009netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598081172.18.15.998081netmask255.255.255.255 static(trust,untrust)udp113.105.88.598081172.18.15.998081netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602001172.18.11.92001netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602002172.18.11.92002netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602003172.18.11.92003netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602004172.18.11.92004netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602005172.18.11.92005netmask255.255.255.255static(trust,untrust)tcp113.105.88.602010172.18.11.92010netmask255.255.255.255 static(trust,untrust)udp113.105.88.602001172.18.11.92001netmask255.255.255.255 static(trust,untrust)udp113.105.88.602002172.18.11.92002netmask255.255.255.255 static(trust,untrust)udp113.105.88.602003172.18.11.92003netmask255.255.255.255 static(trust,untrust)udp113.105.88.602004172.18.11.92004netmask255.255.255.255 static(trust,untrust)udp113.105.88.602005172.18.11.92005netmask255.255.255.255 static(trust,untrust)udp113.105.88.602006172.18.11.92006netmask255.255.255.255 static(trust,untrust)udp113.105.88.602007172.18.11.92007netmask255.255.255.255 static(trust,untrust)udp113.105.88.602008172.18.11.92008netmask255.255.255.255 static(trust,untrust)udp113.105.88.602009172.18.11.92009netmask255.255.255.255 static(trust,untrust)udp113.105.88.602010172.18.11.92010netmask255.255.255.255 static(trust,untrust)113.105.88.61172.18.11.10netmask255.255.255.255access-group102ininterfaceuntrustrouteuntrust0.0.0.00.0.0.010.92.8.91routetrust172.18.11.0255.255.255.0172.18.1.21routetrust172.18.12.0255.255.255.0172.18.1.21routetrust172.18.13.0255.255.255.0172.18.1.21routetrust172.18.14.0255.255.255.0172.18.1.21routetrust172.18.15.0255.255.255.0172.18.1.21routetrust172.18.16.0255.255.255.0172.18.1.21routetrust172.18.17.0255.255.255.0172.18.1.21routetrust172.18.18.0255.255.255.0172.18.1.21timeoutxlate3:00:00timeoutconn1:00:00half-closed0:10:00udp0:02:00icmp0:00:02timeoutsunrpc0:10:00h3230:05:00h2251:00:00mgcp0:05:00mgcp-pat0:05:00 timeoutsip0:30:00sip_media0:02:00sip-invite0:03:00sip-disconnect0:02:00 timeoutsip-provisional-media0:02:00uauth0:05:00absolutenosnmp-serverlocationnosnmp-servercontactsnmp-serverenabletrapssnmpauthenticationlinkuplinkdowncoldstart telnet0.0.0.00.0.0.0trusttelnettimeout5ssh0.0.0.00.0.0.0untrustsshtimeout30consoletimeout0usernameadminpasswordf3UhLvUj1QsXsuK7encrypted!!prompthostnamecontextCryptochecksum:634aa0023e75546939c8b013c69a61b7:endciscoasa#showstartciscoasa#showstartup-config:Saved:Writtenbyenable_15at12:24:22.081UTCMonSep62010!ASAVersion7.2(4)!hostnameciscoasadomain-namedefault.domain.invalidenablepasswordgfFm2E3sthJOc7bqencryptedpasswd2KFQnbNIdI.2KYOUencryptednames!interfaceGigabitEthernet0/0nameifuntrust!interfaceGigabitEthernet0/1 nameifdmzsecurity-level50ipaddress172.18.19.254255.255.255.0!interfaceGigabitEthernet0/2 nameiftrustsecurity-level100ipaddress172.18.1.1255.255.255.0!interfaceGigabitEthernet0/3nonameifnosecurity-levelnoipaddress!interfaceManagement0/0 nameifmanagementsecurity-level100ipaddress192.168.1.1255.255.255.0 management-only!ftpmodepassivednsserver-groupDefaultDNSdomain-namedefault.domain.invalid access-list102extendedpermiticmpanyany access-list102extendedpermitipanyany pagerlines24loggingenablemtudmz1500mtutrust1500mtumanagement1500nofailovericmpunreachablerate-limit1burst-size1asdmimagedisk0:/ASDM-524.BINnoasdmhistoryenablearptimeout14400global(untrust)1interfacenat(trust)10.0.0.00.0.0.0static(trust,untrust)tcp113.105.88.5786172.18.11.886netmask255.255.255.255static(trust,untrust)tcp113.105.88.575000172.18.11.85000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.586800172.18.11.1306800netmask255.255.255.255 static(trust,untrust)tcp113.105.88.584800172.18.11.1304800netmask255.255.255.255 static(trust,untrust)tcp113.105.88.583306172.18.11.1303306netmask255.255.255.255 static(trust,untrust)udp113.105.88.586800172.18.11.1306800netmask255.255.255.255 static(trust,untrust)udp113.105.88.584800172.18.11.1304800netmask255.255.255.255 static(trust,untrust)udp113.105.88.583306172.18.11.1303306netmask255.255.255.255 static(trust,untrust)tcp113.105.88.5881172.18.11.13081netmask255.255.255.255 static(trust,untrust)udp113.105.88.5881172.18.11.13081netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601011172.18.11.91011netmask255.255.255.255 static(trust,untrust)udp113.105.88.601011172.18.11.91011netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601018172.18.11.91018netmask255.255.255.255 static(trust,untrust)udp113.105.88.601018172.18.11.91018netmask255.255.255.255 static(trust,untrust)tcp113.105.88.5981172.18.15.99wwwnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.592000172.18.15.992000netmask255.255.255.255 static(trust,untrust)udp113.105.88.592000172.18.15.992000netmask255.255.255.255 static(trust,untrust)udp113.105.88.59www172.18.15.99wwwnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.598080172.18.15.998080netmask255.255.255.255static(trust,untrust)udp113.105.88.598000172.18.11.1238000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.596999172.18.11.1236999netmask255.255.255.255 static(trust,untrust)tcp113.105.88.59ftp-data172.18.11.123ftp-datanetmask255.255.255.255 static(trust,untrust)tcp113.105.88.59ftp172.18.11.123ftpnetmask255.255.255.255static(trust,untrust)tcp113.105.88.59telnet172.18.11.123telnetnetmask255.255.255.255 static(trust,untrust)tcp113.105.88.591010172.18.11.1231000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598003172.18.11.1238003netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598010172.18.11.1238010netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598012172.18.11.1238012netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598880172.18.11.1238880netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601012172.18.11.91012netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601013172.18.11.91013netmask255.255.255.255 static(trust,untrust)tcp113.105.88.601014172.18.11.91014netmask255.255.255.255 static(trust,untrust)udp113.105.88.601012172.18.11.91012netmask255.255.255.255 static(trust,untrust)udp113.105.88.601013172.18.11.91013netmask255.255.255.255 static(trust,untrust)udp113.105.88.601014172.18.11.91014netmask255.255.255.255 static(trust,untrust)tcp113.105.88.595000172.18.15.995000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.594000172.18.15.994000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602000172.18.11.92000netmask255.255.255.255 static(trust,untrust)udp113.105.88.602000172.18.11.92000netmask255.255.255.255 static(trust,untrust)tcp113.105.88.592009172.18.15.992009netmask255.255.255.255 static(trust,untrust)udp113.105.88.592009172.18.15.992009netmask255.255.255.255 static(trust,untrust)tcp113.105.88.598081172.18.15.998081netmask255.255.255.255 static(trust,untrust)udp113.105.88.598081172.18.15.998081netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602001172.18.11.92001netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602002172.18.11.92002netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602003172.18.11.92003netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602004172.18.11.92004netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602005172.18.11.92005netmask255.255.255.255static(trust,untrust)tcp113.105.88.602008172.18.11.92008netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602009172.18.11.92009netmask255.255.255.255 static(trust,untrust)tcp113.105.88.602010172.18.11.92010netmask255.255.255.255 static(trust,untrust)udp113.105.88.602001172.18.11.92001netmask255.255.255.255 static(trust,untrust)udp113.105.88.602002172.18.11.92002netmask255.255.255.255 static(trust,untrust)udp113.105.88.602003172.18.11.92003netmask255.255.255.255 static(trust,untrust)udp113.105.88.602004172.18.11.92004netmask255.255.255.255 static(trust,untrust)udp113.105.88.602005172.18.11.92005netmask255.255.255.255 static(trust,untrust)udp113.105.88.602006172.18.11.92006netmask255.255.255.255 static(trust,untrust)udp113.105.88.602007172.18.11.92007netmask255.255.255.255 static(trust,untrust)udp113.105.88.602008172.18.11.92008netmask255.255.255.255 static(trust,untrust)udp113.105.88.602009172.18.11.92009netmask255.255.255.255 static(trust,untrust)udp113.105.88.602010172.18.11.92010netmask255.255.255.255 static(trust,untrust)113.105.88.61172.18.11.10netmask255.255.255.255access-group102ininterfaceuntrustrouteuntrust0.0.0.00.0.0.010.92.8.91routetrust172.18.11.0255.255.255.0172.18.1.21routetrust172.18.12.0255.255.255.0172.18.1.21routetrust172.18.13.0255.255.255.0172.18.1.21routetrust172.18.14.0255.255.255.0172.18.1.21routetrust172.18.15.0255.255.255.0172.18.1.21routetrust172.18.16.0255.255.255.0172.18.1.21routetrust172.18.17.0255.255.255.0172.18.1.21routetrust172.18.18.0255.255.255.0172.18.1.21timeoutxlate3:00:00timeoutconn1:00:00half-closed0:10:00udp0:02:00icmp0:00:02timeoutsunrpc0:10:00h3230:05:00h2251:00:00mgcp0:05:00mgcp-pat0:05:00 timeoutsip0:30:00sip_media0:02:00sip-invite0:03:00sip-disconnect0:02:00 timeoutsip-provisional-media0:02:00uauth0:05:00absolutehttpserverenablehttp0.0.0.00.0.0.0trustnosnmp-serverlocationnosnmp-servercontactsnmp-serverenabletrapssnmpauthenticationlinkuplinkdowncoldstart telnet0.0.0.00.0.0.0trusttelnettimeout5ssh0.0.0.00.0.0.0untrustsshtimeout30consoletimeout0usernameadminpasswordf3UhLvUj1QsXsuK7encrypted!!prompthostnamecontextCryptochecksum:634aa0023e75546939c8b013c69a61b7 ciscoasa#。
Cisco ASA5505防火墙详细配置教程及实际配置案例
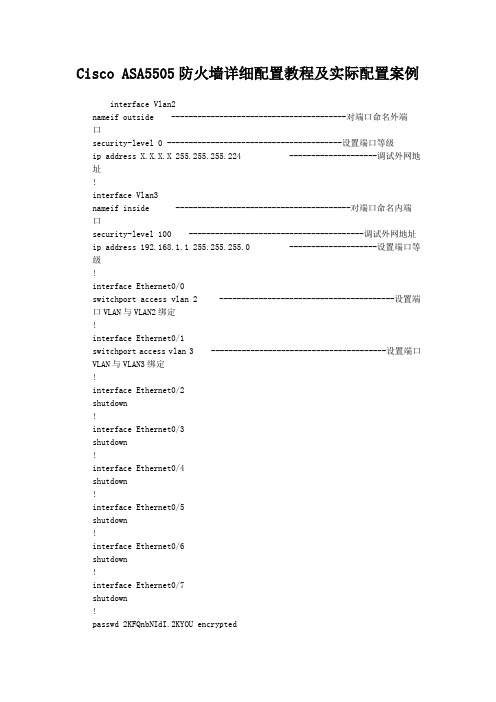
Cisco ASA5505防火墙详细配置教程及实际配置案例interface Vlan2nameif outside ----------------------------------------对端口命名外端口security-level 0 ----------------------------------------设置端口等级ip address X.X.X.X 255.255.255.224 --------------------调试外网地址!interface Vlan3nameif inside ----------------------------------------对端口命名内端口security-level 100 ----------------------------------------调试外网地址ip address 192.168.1.1 255.255.255.0 --------------------设置端口等级!interface Ethernet0/0switchport access vlan 2 ----------------------------------------设置端口VLAN与VLAN2绑定!interface Ethernet0/1switchport access vlan 3 ----------------------------------------设置端口VLAN与VLAN3绑定!interface Ethernet0/2shutdown!interface Ethernet0/3shutdown!interface Ethernet0/4shutdown!interface Ethernet0/5shutdown!interface Ethernet0/6shutdown!interface Ethernet0/7shutdown!passwd 2KFQnbNIdI.2KYOU encryptedftp mode passivedns domain-lookup insidedns server-group DefaultDNSname-server 211.99.129.210name-server 202.106.196.115access-list 102 extended permit icmp any any ------------------设置ACL列表(允许ICMP全部通过)access-list 102 extended permit ip anyany ------------------设置ACL列表(允许所有IP全部通过)pager lines 24mtu outside 1500mtu inside 1500icmp unreachable rate-limit 1 burst-size 1no asdm history enablearp timeout 14400global (outside) 1 interface ----------------------------------------设置NAT地址映射到外网口nat (inside) 1 0.0.0.0 0.0.0.0 0---------------------------------NAT地址池(所有地址)0无最大会话数限制access-group 102 in interface outside ------------------―――设置ACL列表绑定到外端口route outside 0.0.0.0 0.0.0.0 x.x.x.x 1 ------------------设置到外网的默认路由timeout xlate 3:00:00timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout uauth 0:05:00 absoluteno snmp-server locationno snmp-server contactsnmp-server enable traps snmp authentication linkup linkdown coldstart telnet 0.0.0.0 0.0.0.0 inside ----------------------------------------设置TELNET所有地址进入telnet timeout 5ssh 0.0.0.0 0.0.0.0 outside ----------------------------------------设置SSH所有地址进入ssh timeout 30ssh version 2console timeout 0!dhcpd address 192.168.1.100-192.168.1.199inside ------------------设置DHCP服务器地址池dhcpd dns 211.99.129.210 202.106.196.115 interfaceinside ------------------设置DNS服务器到内网端口dhcpd enableinside --------------------------------------------------------------设置DHCP应用到内网端口!前几天去客户那调试CISCO-ASA-5505设备,第一次摸,跟PIX一样,呵呵.没有技术含量,都是最基本的.其他业务配置暂时没配,会及时更新的.Cisco ASA5505配置cisco, config, telnet, 防火墙, Cisco1.配置防火墙名ciscoasa> enableciscoasa# configure terminalciscoasa(config)# hostname asa55052.配置telnetasa5505(config)#telnet 192.168.1.0 255.255.255.0 inside ↑//允许内部接口192.168.1.0网段telnet防火墙3.配置密码asa5505(config)# password cisco ------------------远程密码asa5505(config)# enable password cisco ------------------特权模式密码4.配置IPasa5505(config)# interface vlan 2 ------------------进入vlan2asa5505(config-if)# ip address 218.16.37.222 255.255.255.192 ------------------vlan2配置IPasa5505(config)#show ip address vlan2 ------------------验证配置5.端口加入vlanasa5505(config)# interface e0/3 ------------------进入接口e0/3asa5505(config-if)# switchport access vlan 3 ------------------接口e0/3加入vlan3asa5505(config)# interface vlan 3 ------------------进入vlan3asa5505(config-if)# ip address 10.10.10.36 255.255.255.224 ------------------vlan3配置IPasa5505(config-if)# nameif dmz ------------------vlan3名asa5505(config-if)# no shutdown ------------------开启asa5505(config-if)# show switch vlan ------------------验证配置6.最大传输单元MTUasa5505(config)#mtu inside 1500 ------------------inside最大传输单元1500字节asa5505(config)#mtu outside 1500 ------------------outside最大传输单元1500字节asa5505(config)#mtu dmz 1500 ------------------dmz最大传输单元1500字节7.配置arp表的超时时间asa5505(config)#arp timeout 14400 ------------------arp表的超时时间14400秒8.FTP模式asa5505(config)#ftp mode passive ------------------FTP被动模式9.配置域名asa5505(config)#domain-name 10.启动日志asa5505(config)#logging enable ------------------启动日志asa5505(config)#logging asdm informational ------------------启动asdm报告日志asa5505(config)#Show logging ------------------验证配置11.启用http服务asa5505(config)#http server enable ------------------启动HTTP server,便于ASDM连接。
Cisco_ASA5500_firewall_配置技巧及实例

一、思科ASA防火墙精华配置总结思科防火墙PIX ASA 配置总结一(基础):下面是我工作以来的配置总结,有些东西是6.3版本的,但不影响在7.*版本的配置。
一:6个基本命令:nameif、interface、ip address 、nat、global、route。
二:基本配置步骤:step1: 命名接口名字nameif ethernet0 outside security0nameif ethernet1 inside security100nameif ethernet2 dmz security50**7版本的配置是先进入接口再命名。
step2:配置接口速率interface ethernet0 10full autointerface ethernet1 10full autointerface ethernet2 10fullstep3:配置接口地址ip address outside 218.106.185.82ip address inside 192.168.100.1 255.255.255.0ip address dmz 192.168.200.1 255.255.255.0step4:地址转换(必须)* 安全高的区域访问安全低的区域(即内部到外部)需NAT和global;nat(inside) 1 192.168.1.1 255.255.255.0global(outside) 1 222.240.254.193 255.255.255.248***nat (inside) 0 192.168.1.1 255.255.255.255 表示192.168.1.1这个地址不需要转换。
直接转发出去。
* 如果内部有服务器需要映像到公网地址(外网访问内网)则需要static和conduit或者acl.static (inside, outside) 222.240.254.194 192.168.1.240static (inside, outside) 222.240.254.194 192.168.1.240 10000 10后面的10000为限制连接数,10为限制的半开连接数。
asa5510限制客户端并发连接数和流量

近期公司网站遭到大量攻击,内网ping网站ip 丢包很严重。
查看asa 状态如图:01.asdm 上面看到的攻击状态:02. 连接状态如下:03. 在服务器上看到的出现大量time waite 状态的连接(全是无效连接),导致web服务器很卡,严重丢包,cpu和内存正常。
04. 处理办法:a.检测是不是web服务器有没有大量的对外的连接(非80端口)是不是中毒之类的。
b.在asa防火墙上限制客户端的并发连接数和流量:第一种:hostname(config)# access-list allip permit ip any any 设置需限制的访问列表hostname(config)# class-map c_all_ip 设置类别图hostname(config-cmap)# match access-list allip 匹配访问列表alliphostname(config)# policy-map p_all_ip 设置策略图p_all_iphostname(config-pmap)# class c_all_ip 使用类别c_all_iphostname(config-pmap-c)# set connection per-client-max 50 (限制每客户端连接数最大50)hostname(config-pmap-c)# police output 250000 限制此类别速率bit/shostname(config)# service-policy p_all_ip interface outside(将策略应用到接口,每个接口只能用一个策略图policy-map)注:在policy-map里面使用命令set connection conn-max 10 现实最大连接数10个set connection embryonic-conn-max 5 限制最大的半打开连接时5个set connection per-client-max 10 限制每用户最大连接数10个set connection per-client-embryonic-max 5 限制每用户最大半打开连接数5个police output 10000 20000 conform-action drop 出口速率10000B,允许爆发到20000,违反规则丢弃数据包例子:access-list 101 extended permit tcp any host 192.168.0.115 eq wwwclass-map c_all_ipmatch access-list 101policy-map p_call_ipclass c_all_ipset connection embryonic-conn-max 60 per-client-max 60service-policy p_call_ip interface outside超过60个连接,在asa日志上可以看到以下内容:说明已经生效了。
ASA5510防火墙配置手册
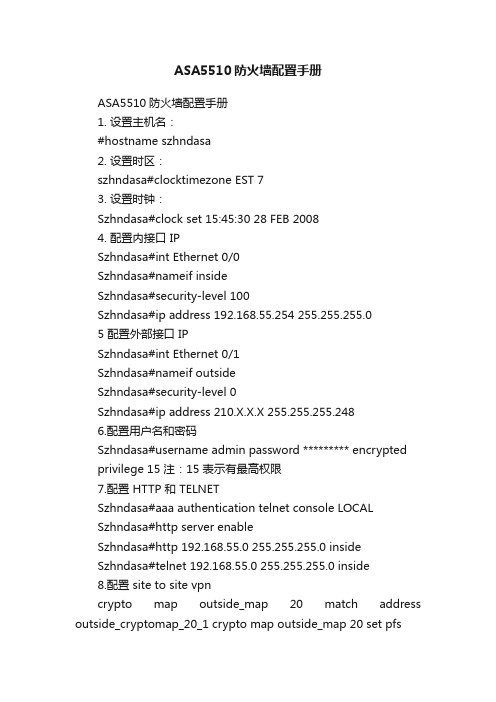
ASA5510防火墙配置手册ASA5510防火墙配置手册1. 设置主机名:#hostname szhndasa2. 设置时区:szhndasa#clocktimezone EST 73. 设置时钟:Szhndasa#clock set 15:45:30 28 FEB 20084. 配置内接口 IPSzhndasa#int Ethernet 0/0Szhndasa#nameif insideSzhndasa#security-level 100Szhndasa#ip address 192.168.55.254 255.255.255.05 配置外部接口 IPSzhndasa#int Ethernet 0/1Szhndasa#nameif outsideSzhndasa#security-level 0Szhndasa#ip address 210.X.X.X 255.255.255.2486.配置用户名和密码Szhndasa#username admin password ********* encryptedprivilege 15 注:15 表示有最高权限7.配置 HTTP 和 TELNETSzhndasa#aaa authentication telnet console LOCALSzhndasa#http server enableSzhndasa#http 192.168.55.0 255.255.255.0 insideSzhndasa#telnet 192.168.55.0 255.255.255.0 inside8.配置 site to site vpncrypto map outside_map 20 match address outside_cryptomap_20_1 crypto map outside_map 20 set pfscrypto map outside_map 20 set peer 210.75.1.Xcrypto map outside_map 20 set transform-set ESP-3DES-SHAcrypto map outside_map 20 set nat-t-disablecrypto map outside_map interface outside注:还可通过 http 方式用 ASDM 管理软件图形化配置 ASA[原创] CISCO ASA 防火墙 IOS恢复与升级简明教程!客户的误操作,把ios给删了,这下麻烦到我了。
ASA虚拟防火墙综合实训
ASA虚拟防火墙综合实训
一、实训目的:
1.理解ASA虚拟防火墙概念
3.掌握ASA防火墙的虚拟化配置
二.实训环境
CISCO ASA 防火墙、路由器、GNS3、计算机
三.实验拓扑
虚拟网络拓扑
真实物理拓扑
四.实训内容:
1.建立如图所示网络拓扑
2.虚拟化防火墙配置
a)在ASA5510上建立管理虚拟防火墙,名字为admin;然后划分出两个虚拟防火墙,
名字分别为c1和c2(注意大小写敏感)
c)启用NAT control,要求R1和R3、R2和R3的loopback0口之间都能够互相ping通
(做NAT的地址池自己定义,如果需要也可以考虑使用PAT)
d)做路由,要求R1和R2的loopback0口之间都能够互相ping通
e)要求R1能够telnet到R2上;
实训要求
1.5人一组,每班9组
2.实训成绩按照平时出勤(20分)+实训结果(50分)+实训报告(30分)计算
3.提交实训报告,要求
a)格式正确,字体为小四,行间距为1,段间距为0.5
b)实训报告内容包括
c)网络拓扑图
d)IP地址规划
e)防火墙配置各步骤(截图或命令以及适当的说明)
f)防火墙配置各步骤测试结果
g)实训总结。
ASA5510配置实例1
配置设备介绍:(只为做实验实际应用请根据自己具体情况更改相关参数即可)核心交换机 4507提供VLAN3 网关地址:192.168.3.254提供 DNS 服务器连接:192.168.0.1接入交换机 2960提供 VLAN3 TURNK 连接,可用IP 地址为192.168.3.0-192.168.3.240掩码:255.255.255.0网关:192.168.3.254DNS: 192.168.0.1内网实验防火墙 CISCO ASA 5510E0/0 IP:192.168.3.234E0/1 IP 10.1.1.1实现配置策略1. 动态内部 PC1 DHCP 自动获得IP 地址,可访问INTERNET,并PING 通外部网关。
PC1 Ethernet adapter 本地连接:Connection-specific DNS Suffix . : gametuziDescription . . . . . . . . . . . : Broadcom 440x rollerPhysical Address. . . . . . . . . : 00-13-77-04-9Dhcp Enabled. . . . . . . . . . . : YesAutoconfiguration Enabled . . . . : YesIP Address. . . . . . . . . . . . : 10.1.1.20Subnet Mask . . . . . . . . . . . : 255.255.0.0Default Gateway . . . . . . . . . : 10.1.1.1DHCP Server . . . . . . . . . . . : 10.1.1.1DNS Servers . . . . . . . . . . . : 192.168.0.12. 静态内部 PC2 手动分配地址,可访问 INTERNET ,并PING 通外部网关。
网络设计 CISCO防火墙
防火墙基础—转发规则
接口1 接口2
Local区域
In Out
In Out
Trust区域
In Out
DMZ区域
In Out
UnTrust区域
接口4
接口3
本域内不同接口间不过滤直接转发 进、出接口相同的报文被丢弃 接口没有加入域之前不能转发报文
防火墙基础—模式分类
•路由模式 •透明模式 •混合模式
防火墙基础—路由模式
防火墙基础—双机热备
什么是双机热备? 什么是双机热备?
所谓双机热备其实是双机状态备份,当两台防火墙,在确定主从防火墙后, 所谓双机热备其实是双机状态备份,当两台防火墙,在确定主从防火墙后,由主 防火墙进行业务的转发,而从防火墙处于监控状态, 防火墙进行业务的转发,而从防火墙处于监控状态,同时主防火墙会定时向从防 火墙发送状态信息和需要备份的信息,当主防火墙出现故障后, 火墙发送状态信息和需要备份的信息,当主防火墙出现故障后,从防火墙会及时 接替主防火墙上的业务运行。 接替主防火墙上的业务运行。
• 透明模式的防火墙则可以被看作一台以太网 交换机。防火墙的接口不能配IP地址,整个 设备处于现有的子网内部,对于网络中的其 他设备,防火墙是透明的。报文转发的出接 口,是通过查找桥接的转发表得到的。在确 定域间之后,安全模块的内部仍然使用报文 的IP地址进行各种安全策略的匹配。
ciscoASA虚拟防火墙配置
ciscoASA虚拟防火墙配置
cisco ASA虚拟防火墙配置
可以把物理的一个防火墙配置出多个虚拟的防火墙,每个防火墙称为context,这样一个防火墙就支持两种工作模式:single-context 和multiple-context,处于后者工作模式的防火墙被分为三个功能模块:system execution space(虽然没有context的功能,但是是所有的基础),administrative context(被用来管理物理的防火墙) 和user contexts(虚拟出来的防火墙,所有配置防火墙的命令都适用)配置:
首先使用show activation-key来验证是否有multiple-context 的许可,然后通过mode multiple和mode single命令在这两个模式之间进行切换,当然也可以用show mode来验证现在工作在什么模式下。
在不同context下进行切换使用Firewall# changeto {system | context name[/i]},
总结配置如下几条:
1、进入多模工作模式 mode multiple
2、创建主防火墙 admin_context___(命名)
3、进入主防火墙:admin_context
(1)、命名:context admin
4、添加端口allocate-interface (物理端口)
5、创建存储文件 config-url disk0 :// admin.cfg 文件名
6、要创建虚拟的防护墙 context 名称
其他步骤同上!
7、各个防火墙之间切换:changto context xxxx,各个防火墙之间独立工作。
彼此不影响!。
- 1、下载文档前请自行甄别文档内容的完整性,平台不提供额外的编辑、内容补充、找答案等附加服务。
- 2、"仅部分预览"的文档,不可在线预览部分如存在完整性等问题,可反馈申请退款(可完整预览的文档不适用该条件!)。
- 3、如文档侵犯您的权益,请联系客服反馈,我们会尽快为您处理(人工客服工作时间:9:00-18:30)。
cisco ASA5510配置实例2008年11月11日 07:52ASA5510# SHOW RUN: Saved:ASA Version 7.0(6)!hostname ASA5510enable password 2KFQnbNIdI.2KYOU encryptednamesdns-guard!interface Ethernet0/0 此接口为外部网络接口nameif outside 设置为 OUTSIDE 外部接口模式security-level 0 外部接口模式安全级别为最低 0ip address 192.168.3.234 255.255.255.0 添加外部IP地址(一般为电信/网通提供)!interface Ethernet0/1此接口为内部网络接口nameif inside设置为 INSIDE 内部接口模式security-level 100内部接口模式安全级别最高为 100ip address 10.1.1.1 255.255.0.0添加内部IP地址!interface Ethernet0/2 没用到shutdownno nameifno security-levelno ip address!interface Management0/0nameif managementsecurity-level 100ip address 192.168.1.1 255.255.255.0 没用,用网线连接管理的端口。
management-only!passwd 2KFQnbNIdI.2KYOU encryptedftp mode passivepager lines 24logging asdm informationalmtu outside 1500mtu inside 1500mtu management 1500no asdm history enablearp timeout 14400global (outside) 1 interface 一定要打表示 PAT端口扩展:“1”为其NAT ID nat (inside) 1 10.1.0.0 255.255.0.0 转换所有10.1.0.0 的内部地址route outside 0.0.0.0 0.0.0.0 192.168.3.254 1 缺省路由timeout xlate 3:00:00timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00timeout mgcp-pat 0:05:00 sip 0:30:00 sip_media 0:02:00timeout uauth 0:05:00 absolutehttp server enable 打开http serverhttp 192.168.1.0 255.255.255.0 management 限定能通过http方式访问防火墙的机器no snmp-server locationno snmp-server contactsnmp-server enable traps snmp authentication linkup linkdown coldstart telnet timeout 5ssh timeout 5console timeout 0dhcpd address 10.1.1.30-10.1.1.200 inside DHCP 自动提供分配范围为10.1.1.30-200dhcpd address 192.168.1.2-192.168.1.254 managementdhcpd dns 192.168.0.1 DNS 添加:可以是电信网通提供直接添加,或者自己的DNS服务器地址。
dhcpd lease 3600dhcpd ping_timeout 50dhcpd domain suzhou.jy 域名dhcpd enable inside 打开内部网段自动分配dhcpd enable managementCryptochecksum:6148633dac00f8f7a3418833f98d5ad4access-group icmp_in in interface outside 这两句表示,access-list icmp_in extended permit icmp any any 允许PING包发送或接收: end关于CISCO asa5510防火墙端口映射配置2009-05-21 14:18先进思科防火墙,telnet 192.168.1.254输入密码:系统变成ciscoasa>再输入en回车后再次输入密码系统变成ciscoasa#这个时候输入show running-config回车后可以看到端口E0/0配的外网地址是多少,e0/配的内网地址是多少,和没有配的端口地址。
还能看见访问列表access-list。
再往下看可以看到具体的网络映射地址。
可以看到公网地址的那个端口具体映射到内网地址的那个端口。
回到ciscoasa#后在里面输入conf t回车后变成ciscoasa(config)#在到端口里面,再输入int e0/0命令后就到e0/0端口命令下面状态就变成ciscoasa(config-if)#在此状态下再次输入static (inside,outside) tcp 125.76.115.136 5222 192.168.1.132 5222 netmask 255.255.255.255意思就是公网的5222端口映射到内网的192.168.1.132 的5222端口下面.这个时候命令符又变回ciscoasa(config)#这个状态。
这个时候你再次输入sh ru回车后就能看到自己编辑的端口映射了。
然后再次做个访问列表。
在ciscoasa(config)#下面输入access-list outside-inside extended permit tcp any host 125.76.115.136 eq 5222这个时候你就可以把内网的地址的5222端口映射到公网去了再输入wr写入并保存后,在输入exit就可以退出了如果端口映射错了,也可以删除掉,具体做法是在ciscoasa(config)#模式下输入no access-list outside-inside extended permit tcp any host 125.76.115.136 eq 5222就可以先将地址列表中的5222端口删除掉再到ciscoasa(config)#进入e0/0端口下面输入 int e0/0模式就变成e0/0端口编辑状态下cisco asa(asa5510 设置)防火墙的配置详解2010-02-08 10:02asa5510(config)#asa5510(config)# show run: Saved:ASA Version 7.0(7)!hostname asa5510主机名domain-name 域名enable password FgQ836L.2fG/AEir encrypted ASDM的登陆密码namesdns-guard!interface Ethernet0/0 外部接口nameif outside 接口名security-level 0ip address X.X.X.X 255.255.255.248 IP地址!interface Ethernet0/1内部接口nameif insidesecurity-level 100ip address 192.168.1.1 255.255.255.0 ip地址,内部电脑的网关!interface Ethernet0/2shutdownno nameifno security-levelno ip address!interface Management0/0nameif managementsecurity-level 100ip address 1.1.1.1 255.255.255.0management-only 管理接口可以关闭默认192.168.1.1!passwd WXjstPgDOxFTLAaA encryptedftp mode passiveobject-group network Public 定义一个IP组组名为Public (做ACL的时候可以方便减少ACL条目、这里做的是IP组,其实还可以基于服务来做个组,)network-object host 192.168.1.2定义组内的IPnetwork-object host 192.168.1.3network-object host 192.168.1.4network-object host 192.168.1.5network-object host 192.168.1.6network-object host 192.168.1.7 这些组里的IP在后面将被引用access-list 102 extended permit icmp any anyaccess-list 102 extended permit ip any any定义AClaccess-list 111 extended permit ip host 192.168.1.16 anyaccess-list 111 extended permit ip object-group Public any 定义ACL 注意这里的源地址引用的是一个我们前面定义的地址组,access-list 111 extended deny ip any any 这里是拒绝所有,大家应该知道我的ACL的意思了吧,拒绝所有人上网。
上面允许的除外pager lines 24logging asdm informationalmtu outside 1500mtu inside 1500mtu management 1500asdm image disk0:/asdm-507.bin 指定ASDM路径,开启ASDM的命令之一,至于ASDM版本,大家可以DIR的命令来查看到,no asdm history enablearp timeout 14400global (outside) 1 interfacenat (inside) 1 0.0.0.0 0.0.0.0 nAT转换,吧内部接口的所有IP转换到外部的公网IP,让所有内部IP可以上网,access-group 102 in interface outsideaccess-group 111 in interface inside 这2个是引用前面定义的ACL一个外部接口一个内部接口如果没和我一样的只允许部分IP上网的需求的可以不要INSIDE的ACL以及ACL 111的条目route outside 0.0.0.0 0.0.0.0 xx.x.x.x 1外部的默认路由 x.x.x.x为公网的网关timeout xlate 3:00:00timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00timeout mgcp-pat 0:05:00 sip 0:30:00 sip_media 0:02:00timeout uauth 0:05:00 absoluteusername cisco1 password W0ATeFBkCO3ErmVn encrypted privilege 15(asdm SSH登陆用户名和密码)aaa authentication ssh console LOCAL (SSH 登陆启用本地认证,就是上面的cisco1)http server enable(激活ASDM)http 0.0.0.0 0.0.0.0 outsidehttp 0.0.0.0 0.0.0.0 inside(在外部和内部借口上启用ASDM)no snmp-server locationno snmp-server contactsnmp-server enable traps snmp authentication linkup linkdown coldstart telnet 0.0.0.0 0.0.0.0 inside启用内部的TELNETtelnet timeout 5ssh 0.0.0.0 0.0.0.0 outsidessh 0.0.0.0 0.0.0.0 inside(起用内部和外部接口的SSH) ssh timeout 30ssh version 2 SSH版本2console timeout 0!class-map inspection_defaultmatch default-inspection-traffic!!policy-map global_policyclass inspection_defaultinspect dns maximum-length 512inspect ftpinspect h323 h225inspect h323 rasinspect rshinspect rtspinspect esmtpinspect sqlnetinspect skinnyinspect sunrpcinspect xdmcpinspect sipinspect netbiosinspect tftp!service-policy global_policy global Cryptochecksum:5ee69c74afd48da59841097fe14670ad: endASA 5510 基本配置caihuashe# show versionCisco Adaptive Security Appliance Software Version 7.2(3)Detected an old ASDM version.You will need to upgrade it before using ASDM.Compiled on Wed 15-Aug-07 16:08 by buildersSystem image file is "disk0:/asa723-k8.bin"Config file at boot was "startup-config"caihuashe up 358 days 0 hoursHardware: ASA5510, 256 MB RAM, CPU Pentium 4 Celeron 1600 MHz Internal ATA Compact Flash, 256MBBIOS Flash M50FW080 @ 0xffe00000, 1024KBEncryption hardware device : Cisco ASA-55x0 on-board accelerator (revision 0x0)Boot microcode : CNlite-MC-Boot-Cisco-1.2SSL/IKE microcode: CNlite-MC-IPSEC-Admin-3.03IPSec microcode : CNlite-MC-IPSECm-MAIN-2.040: Ext: Ethernet0/0 : address is 001d.70df.2cfc, irq 91: Ext: Ethernet0/1 : address is 001d.70df.2cfd, irq 92: Ext: Ethernet0/2 : address is 001d.70df.2cfe, irq 93: Ext: Ethernet0/3 : address is 001d.70df.2cff, irq 94: Ext: Management0/0 : address is 001d.70df.2d00, irq 115: Int: Not used : irq 116: Int: Not used : irq 5Licensed features for this platform:Maximum Physical Interfaces : UnlimitedMaximum VLANs : 100Inside Hosts : UnlimitedFailover : Active/ActiveVPN-DES : EnabledVPN-3DES-AES : EnabledSecurity Contexts : 2GTP/GPRS : DisabledVPN Peers : 250WebVPN Peers : 2This platform has an ASA 5510 Security Plus license.从上面的硬件和ios,其实硬件配置并不高档,比我们用的普通电脑的档次低多了,我觉得其关键在于其稳定性好、ios系统强;现在市面上也出现一些网友用自己旧PC组装的防火墙,功能和性能也不错,如M0N0、pfsense等;1.首先配置防火墙的端口一般会配置两个端口一个inside口一个outside口,asa5510有4个网络口,我们可随便使用那个口来设置inside口和outside口,关键在在于配置端口上面来确定是怎样的出口;interface Ethernet0/0speed 100duplex fullnameif outside 设置外网口security-level 0 安全级别0-100ip address 192.168.55.2 255.255.255.252!interface Ethernet0/1nameif inside 设置内网口security-level 100 安全级别最高100ip address 192.168.3.1 255.255.255.0!2.配置基本的访问策略;access-group WAN_access_in in interface outside 定义外网口访问策略群组access-group IN_access_WAN in interface inside 定义内网口访问策略群组access-list IN_access_WAN extended permit ip 192.168.9.0 255.255.255.0 any 增加内网口出去的访问策略access-list IN_access_WAN extended permit tcp 192.168.9.0 255.255.255.0 any 增加内网口出去的访问策略access-list WAN_access_in extended permit tcp host 222.66.97.193 host 202.104.151.* eq 8317 增加一般的主机访问策略,允许ip 222.66.97.193 访问ip 202.104.151.* eq 83173.配置natglobal (outside) 1 interfacenat (inside) 1 0.0.0.0 0.0.0.0static (inside,outside) 58.251.130.* 192.168.9.50 netmask 255.255.255.255 一对一NATstatic (inside,outside) 58.251.130.* 192.168.9.52 netmask 255.255.255.255static (inside,outside) 58.251.130.* 192.168.9.53 netmask 255.255.255.2554.配置默认网关也就是默认路由route outside 0.0.0.0 0.0.0.0 10.90.22.1 1。
